mosquitto ---SSL/TLS 单向认证+双向认证
生成证书
# * Redistributions in binary form must reproduce the above copyright # notice, this list of conditions and the following disclaimer in the # documentation and/or other materials provided with the distribution. # * Neither the name of the axTLS project nor the names of its # contributors may be used to endorse or promote products derived # from this software without specific prior written permission. # # THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS # "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT # LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR # A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT OWNER OR # CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, # SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED # TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, # DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY # OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING # NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF # THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. # # # Generate the certificates and keys for testing. # PROJECT_NAME="TLS Project" # Generate the openssl configuration files. cat > ca_cert.conf << EOF [ req ] distinguished_name = req_distinguished_name prompt = no [ req_distinguished_name ] O = $PROJECT_NAME Dodgy Certificate Authority EOF cat > server_cert.conf << EOF [ req ] distinguished_name = req_distinguished_name prompt = no [ req_distinguished_name ] O = $PROJECT_NAME CN = 192.168.111.100 EOF cat > client_cert.conf << EOF [ req ] distinguished_name = req_distinguished_name prompt = no [ req_distinguished_name ] O = $PROJECT_NAME Device Certificate CN = 192.168.111.101 EOF mkdir ca mkdir server mkdir client mkdir certDER # private key generation openssl genrsa -out ca.key 1024 openssl genrsa -out server.key 1024 openssl genrsa -out client.key 1024 # cert requests openssl req -out ca.req -key ca.key -new \ -config ./ca_cert.conf openssl req -out server.req -key server.key -new \ -config ./server_cert.conf openssl req -out client.req -key client.key -new \ -config ./client_cert.conf # generate the actual certs. openssl x509 -req -in ca.req -out ca.crt \ -sha1 -days 5000 -signkey ca.key openssl x509 -req -in server.req -out server.crt \ -sha1 -CAcreateserial -days 5000 \ -CA ca.crt -CAkey ca.key openssl x509 -req -in client.req -out client.crt \ -sha1 -CAcreateserial -days 5000 \ -CA ca.crt -CAkey ca.key openssl x509 -in ca.crt -outform DER -out ca.der openssl x509 -in server.crt -outform DER -out server.der openssl x509 -in client.crt -outform DER -out client.der mv ca.crt ca.key ca/ mv server.crt server.key server/ mv client.crt client.key client/ mv ca.der server.der client.der certDER/ rm *.conf rm *.req rm *.srl
将上述代码保存为makefile.sh
做如下修改,终端执行。
-
修改 CN 域中 IP 地址为你主机/设备的 IP 地址
-
[可选]加密位数 1024 修改为你需要的加密位数
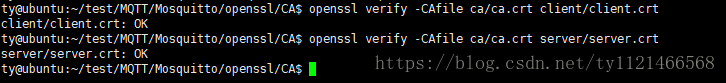
CA校验证书测试
进行如下测试,以验证证书是否可用:
$openssl verify -CAfile ca/ca.crt server/server.crt $openssl verify -CAfile ca/ca.crt client/client.crt
结果如下:
配置单/双向认证
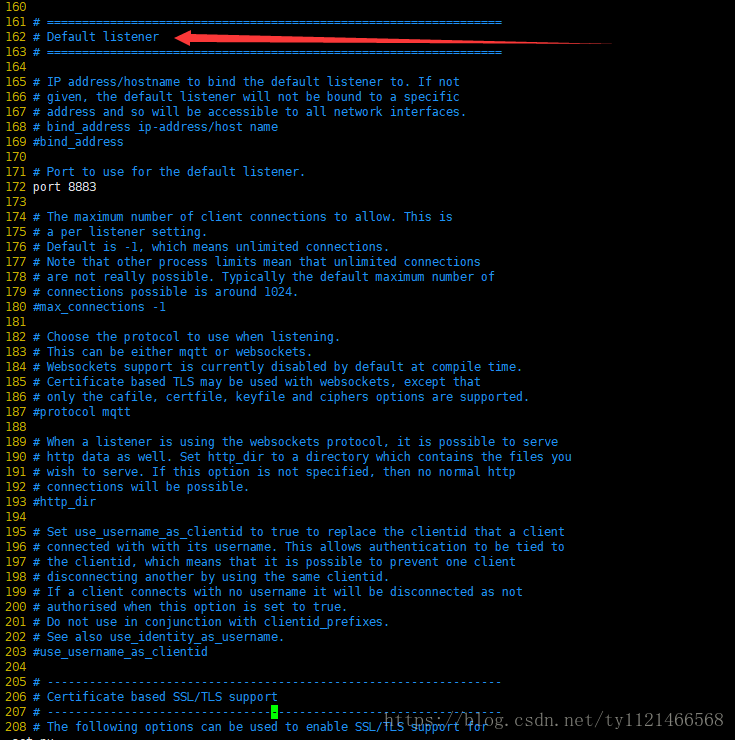
step 1.进入配置文件
sudo vim /etc/mosquitto/mosquitto.conf
step 2.找到 Default listener,在该栏下进行如下配置
再找到Certificate based SSL/TLS support字段.
即:
port 8883 cafile /etc/mosquitto/CA/ca.crt certfile /etc/mosquitto/CA/server/server.crt keyfile /etc/mosquitto/CA/server/server.key require_certificate true use_identity_as_username true
根据自己路径不同配置校验文件路径,这里是把文件放在/etc/mosquitto/CA/下
注意!!!
根据单向认证和双向认证需要,可能需修改的字段有:
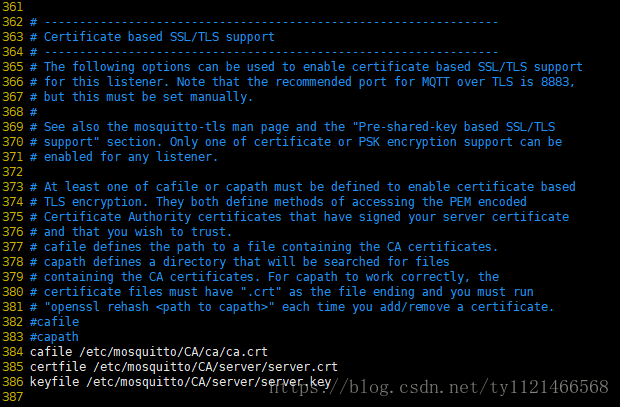
a) port 8883 // MQTT服务器将选择此端口 listen
b) cafile /etc/mosquitto/CA/ca.crt
双向认证必须配置为你的CA证书
单向认证(通常认为是client校验server证书,下同)可选配置
单向认证中,server 和 client 端 ca 配置必须保持一致。即 server 若配置 ca.crt ,则 client 必须配置 ca.crt, server 不配置ca.crt ,client 也不可配置 ca.crt
路径必须为绝对路径!!!
c) certfile /etc/mosquitto/CA/server/server.crt
单项认证和双向认证都必须配置为你的server证书
d) keyfile /etc/mosquitto/CA/server/server.key
单项认证和双向认证都必须配置为你的server私钥
e) require_certificate true
单向认证需设置为 false,注释此行,默认也是 false
双向认证必须配置为true
f) use_identity_as_username true
单向认证设置为 false,注释此行,默认也是 false
双向认证通常设置为true
从上面可以看出,双向和单项认证的区别是,除了需要单向SSL认证需要的CA的证书,服务器端的公钥和私钥的证书之外,还需要开启下面的两个开关。
require_certificate true use_identity_as_username true
重启服务
mosquitto -c /etc/mosquitto/mosquitto.conf
如果提示端口被占用,先ps出mosquitto,再kill掉
ps -aux | grep "mosquitto" kill -9 XXXXX
单双向切换
单向认证只需要注释两行即可:
#require_certificate true #use_identity_as_username true
如下:
port 8883 cafile /etc/mosquitto/CA/ca/ca.crt certfile /etc/mosquitto/CA/server/server.crt keyfile /etc/mosquitto/CA/server/server.key
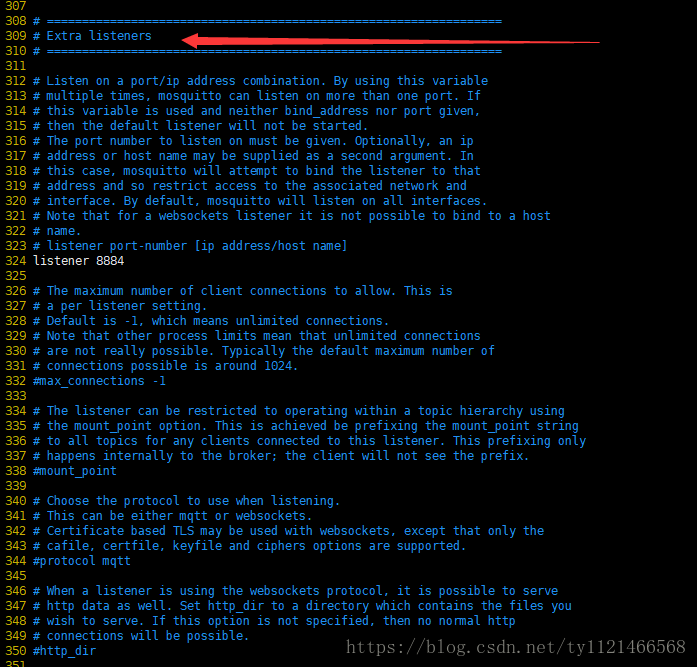
同时打开单双向认证
step 1.
在先将/etc/mosquitto/mosquitto.conf 文件按上面配置默认打开双向认证,再找到 Extra listener字段
进行如下配置,打开另一个端口用作单向认证
step 2.
再在该字段下找到Certificate based SSL/TLS support字段
step 3.重启服务
mosquitto -c /etc/mosquitto/mosquitto.conf
验证
step 1.进入到CA证书目录下:
step 2.双向:
终端一:订阅
mosquitto_sub -h 10.30.11.47 -p 8883 -t "mqtt/server/topic" --cafile ./ca/ca.crt --cert ./client/client.pem --key ./client/client.key &
终端二:发布
mosquitto_pub -h 10.30.11.47 -p 8883 -t "mqtt/server/topic" -m "hello,world!" --cafile ./ca/ca.crt --cert ./server/server.pem --key ./server/server.key
step 3. 单向
终端一:订阅
mosquitto_sub -h 10.30.11.47 -p 8884 -t "mqtt/server/topic" --cafile ./ca/ca.crt &
终端二:发布
mosquitto_pub -h 10.30.11.47 -p 8884 -t "mqtt/server/topic" -m " hello,world!" --cafile ./ca/ca.crt


 浙公网安备 33010602011771号
浙公网安备 33010602011771号