CentOS 7下安装Logstash ELK Stack 日志管理系统(下)
修改防火墙,对外开放tcp/5601
Success
[root@elk elk]# firewall-cmd --reload
success
[root@elk elk]# firewall-cmd --list-all
public (default, active)
interfaces: eno16777984 eno33557248
sources:
services: dhcpv6-client ssh
ports: 9200/tcp 9300/tcp 5601/tcp
masquerade: no
forward-ports:
icmp-blocks:
rich rules:
[root@elk elk]# systemctl enable kibana
Created symlink from /etc/systemd/system/multi-user.target.wants/kibana.service to /usr/lib/systemd/system/kibana.service.
[root@elk elk]# systemctl start kibana
[root@elk elk]# systemctl status kibana
● kibana.service - no description given
Loaded: loaded (/usr/lib/systemd/system/kibana.service; enabled; vendor preset: disabled)
Active: active (running) since Fri 2016-05-20 15:49:02 CST; 20s ago
Main PID: 11260 (node)
CGroup: /system.slice/kibana.service
└─11260 /opt/kibana/bin/../node/bin/node /opt/kibana/bin/../src/cli
May 20 15:49:05 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:05+00:00","tags":["status","plugin:elasticsearch...May 20 15:49:05 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:05+00:00","tags":["status","plugin:kbn_vi...lized"}
May 20 15:49:05 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:05+00:00","tags":["status","plugin:markdo...lized"}
May 20 15:49:05 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:05+00:00","tags":["status","plugin:metric...lized"}
May 20 15:49:05 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:05+00:00","tags":["status","plugin:spyMod...lized"}
May 20 15:49:05 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:05+00:00","tags":["status","plugin:status...lized"}
May 20 15:49:05 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:05+00:00","tags":["status","plugin:table_...lized"}
May 20 15:49:05 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:05+00:00","tags":["listening","info"],"pi...:5601"}
May 20 15:49:10 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:10+00:00","tags":["status","plugin:elasticsearch...May 20 15:49:14 elk.test.com kibana[11260]: {"type":"log","@timestamp":"2016-05-20T07:49:14+00:00","tags":["status","plugin:elasti...found"}
Hint: Some lines were ellipsized, use -l to show in full.
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 909/sshd
tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN 1595/master
tcp 0 0 0.0.0.0:5601 0.0.0.0:* LISTEN 11260/node
Success
[root@elk elk]# firewall-cmd --reload
success
[root@elk elk]# firewall-cmd --list-all
public (default, active)
interfaces: eno16777984 eno33557248
sources:
services: dhcpv6-client ssh
ports: 9200/tcp 9300/tcp 5601/tcp
masquerade: no
forward-ports:
icmp-blocks:
rich rules:
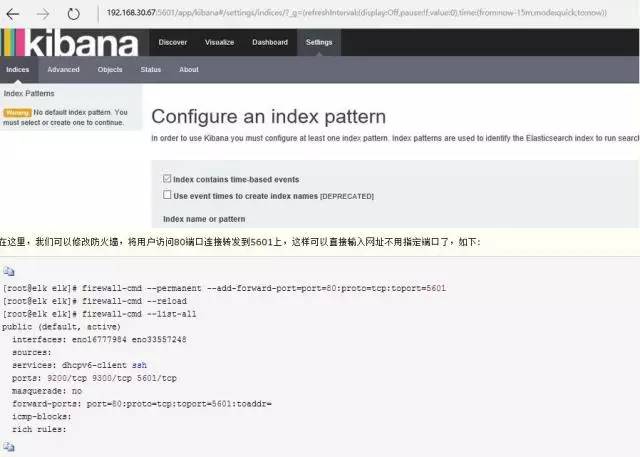
public (default, active)
interfaces: eno16777984 eno33557248
sources:
services: dhcpv6-client ssh
ports: 9200/tcp 9300/tcp 5601/tcp
masquerade: no
forward-ports: port=80:proto=tcp:toport=5601:toaddr=
icmp-blocks:
rich rules:
[root@elk tls]# openssl req -subj '/CN=elk.test.com/' -x509 -days 3650 -batch -nodes -newkey rsa:2048 -keyout private/logstash-forwarder.key -out
certs/logstash-forwarder.crt
Generating a 2048 bit RSA private key
...................................................................+++......................................................+++writing new private key to 'private/logstash-forwarder.key'-----
[root@elk elk]# /sbin/chkconfig logstash on
[root@elk conf.d]# netstat -ntlp
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 909/sshd
tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN 1595/master
tcp 0 0 0.0.0.0:5601 0.0.0.0:* LISTEN 11260/node
tcp 0 0 0.0.0.0:514 0.0.0.0:* LISTEN 618/rsyslogd
tcp6 0 0 :::5000 :::* LISTEN 12819/java
tcp6 0 0 :::3306 :::* LISTEN 1270/mysqld
tcp6 0 0 127.0.0.1:9200 :::* LISTEN 10430/java
tcp6 0 0 ::1:9200 :::* LISTEN 10430/java
tcp6 0 0 127.0.0.1:9300 :::* LISTEN 10430/java
tcp6 0 0 ::1:9300 :::* LISTEN 10430/java
tcp6 0 0 :::22 :::* LISTEN 909/sshd
tcp6 0 0 ::1:25 :::* LISTEN 1595/master
tcp6 0 0 :::514 :::* LISTEN 618/rsyslogd
success
[root@elk ~]# firewall-cmd --reload
success
[root@elk ~]# firewall-cmd --list-all
public (default, active)
interfaces: eno16777984 eno33557248
sources:
services: dhcpv6-client ssh
ports: 9200/tcp 9300/tcp 5000/tcp 5601/tcp
masquerade: no
forward-ports: port=80:proto=tcp:toport=5601:toaddr=
icmp-blocks:
rich rules:
.
├── es-01│ ├── elasticsearch.yml
│ └── logging.yml
└── scripts
----http:
port: 9200network:
host: elk.test.com
node:
name: elk.test.com
path:
data: /etc/elasticsearch/data/es-01
[root@elk elk]# scp filebeat-1.2.3-x86_64.rpm root@nginx.test.com:/root/elk
[root@elk elk]# scp /etc/pki/tls/certs/logstash-forwarder.crt rsyslog.test.com:/root/elk
[root@elk elk]# scp /etc/pki/tls/certs/logstash-forwarder.crt nginx.test.com:/root/elk
#拷贝证书到本机指定目录中
[root@rsyslog elk]# cp logstash-forwarder.crt /etc/pki/tls/certs/.
[root@rsyslog elk]# cd /etc/filebeat/[root@rsyslog filebeat]# tree
.
├── conf.d
│ ├── authlogs.yml
│ └── syslogs.yml
├── filebeat.template.json
└── filebeat.yml1 directory, 4 files
Starting filebeat: [ OK ]
[root@rsyslog filebeat]# chkconfig filebeat on
[root@rsyslog filebeat]# netstat -altp
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 localhost:25151 *:* LISTEN 6230/python2
tcp 0 0 *:ssh *:* LISTEN 5509/sshd
tcp 0 0 localhost:ipp *:* LISTEN 1053/cupsd
tcp 0 0 localhost:smtp *:* LISTEN 1188/master
tcp 0 0 rsyslog.test.com:51155 elk.test.com:commplex-main ESTABLISHED 7443/filebeat
tcp 0 52 rsyslog.test.com:ssh 192.168.30.65:10580 ESTABLISHED 7164/sshd
tcp 0 0 *:ssh *:* LISTEN 5509/sshd
tcp 0 0 localhost:ipp *:* LISTEN 1053/cupsd
tcp 0 0 localhost:smtp *:* LISTEN 1188/master
[root@nginx elk]# cp logstash-forwarder.crt /etc/pki/tls/certs/.
[root@nginx elk]# cd /etc/filebeat/[root@nginx filebeat]# tree
.
├── conf.d
│ ├── nginx.yml
│ └── syslogs.yml
├── filebeat.template.json
└── filebeat.yml1 directory, 4 files
Starting filebeat: [ OK ]
[root@nginx filebeat]# chkconfig filebeat on
[root@nginx filebeat]# netstat -aulpt
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 *:ssh *:* LISTEN 1076/sshd
tcp 0 0 localhost:smtp *:* LISTEN 1155/master
tcp 0 0 *:http *:* LISTEN 1446/nginx
tcp 0 52 nginx.test.com:ssh 192.168.30.65:11690 ESTABLISHED 1313/sshd
tcp 0 0 nginx.test.com:49500 elk.test.com:commplex-main ESTABLISHED 1515/filebeat
tcp 0 0 nginx.test.com:ssh 192.168.30.65:6215 ESTABLISHED 1196/sshd
tcp 0 0 nginx.test.com:ssh 192.168.30.65:6216 ESTABLISHED 1200/sshd
tcp 0 0 *:ssh *:* LISTEN 1076/sshd