OSPF综合实验(下)
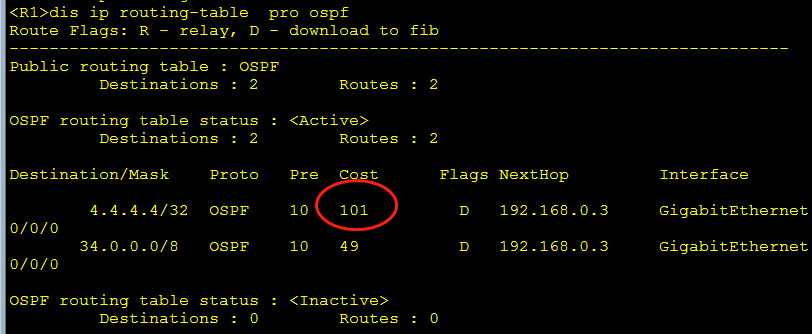
验证R1到R4的开销:
R3:
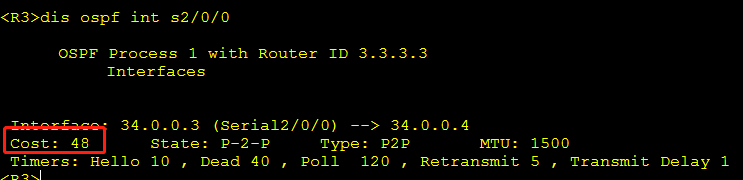
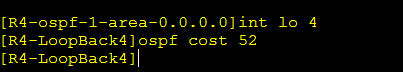
R4:修改R4回环口开销52,则从1到4开销为:1+48+52=101
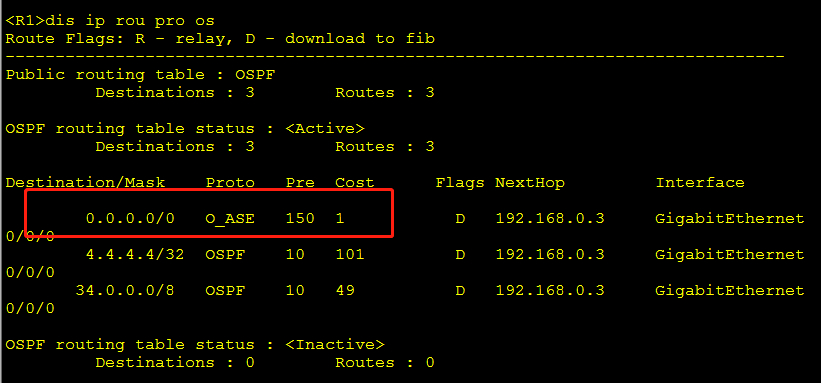
R1:查看开销是不是101
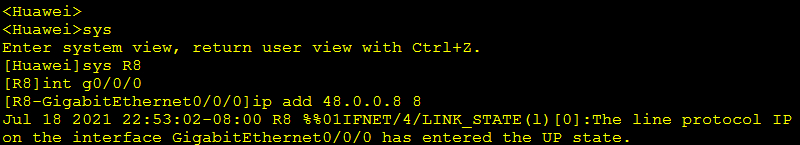
配制运营商R8:
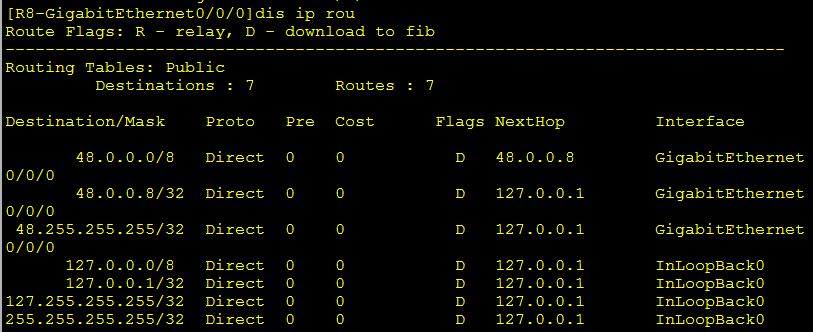
查看R8路由:
配置R8到area 0缺省路由
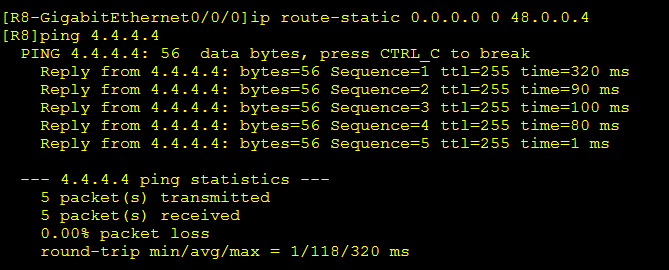
area 0访问运营商R8:
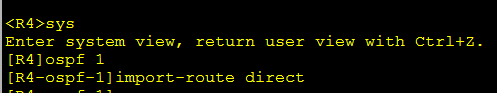
方法一:R4引入48路由---直连(ASBR)
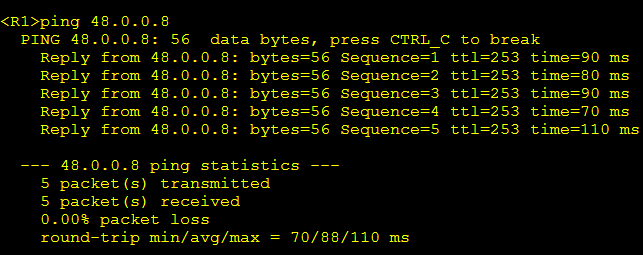
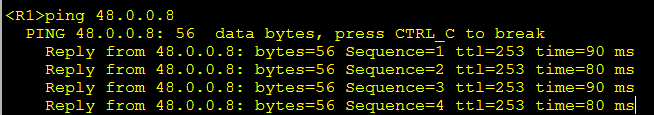
成功后area 0里的R1可访问R8
方法二:R4给大家发缺省路由

验证:
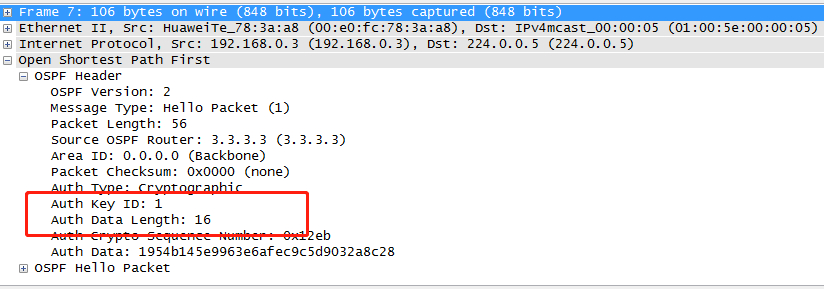
MD5认证:
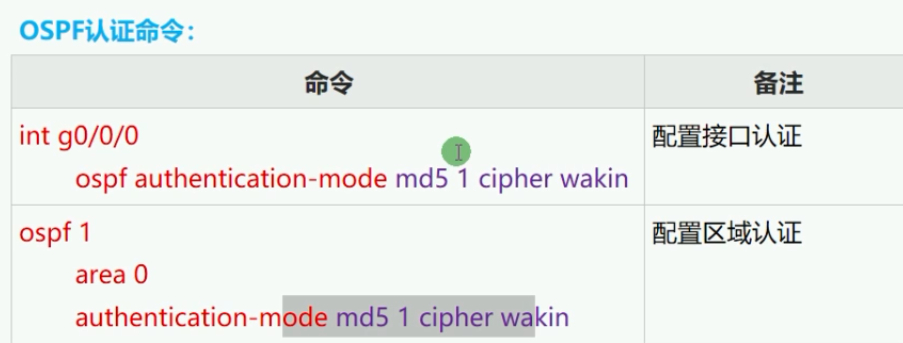
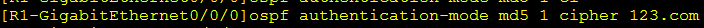
在R1 R2 R3 R6配置ospf认证:

抓包显示认证配置成功:



 浙公网安备 33010602011771号
浙公网安备 33010602011771号