最详细解决https访问不安全问题,windows自建CA并签发证书
本博客适用于测试使用,因为生成的证书需导入客户端电脑,如需商用请购买证书
1|01.windows电脑下载openSSL软件
官方下载地址: https://www.openssl.org/source/
备用下载地址: http://slproweb.com/products/Win32OpenSSL.html
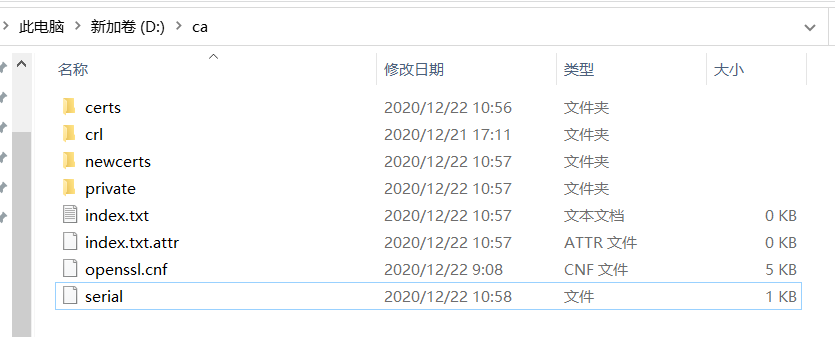
2|02.找个目录新建如下文件夹及文件
1 2 3 4 5 6 7 8 9 | ca├── certs 证书目录├── crl 证书吊销目录├── index.txt CA 签发证书列表├── index.txt.attr CA 签发证书列表配置├── newcerts CA 签发的证书备份├── openssl.cnf openssl 配置文件,-config 参数用├── private 私钥目录└── serial CA 下一次签发证书时使用的序列号 |
附: openssl.cnf 文件(需要修改dir和alt_names)
打开serial文件写入数字"00",后期每生成pem,数字会增加1

签发步骤
打开cmd命令工具或者powerSher进入到ca文件夹
3|03.生成 CA
3|1生成私钥
1 | openssl ecparam -genkey -name secp256r1 |openssl ec -out private/ca.key.pem |
使用 ECC 算法生成 256 位 CA 私钥
生成自签署证书,类型由 openssl.cnf 中配置的扩展字段指定为 CA 证书类型
1 | openssl req -config openssl.cnf -key private/ca.key.pem -new -x509 -days 7300 -sha256 -extensions v3_ca -out certs/ca.cert.pem |
需要输入各项信息。由于是 CA 根证书, Common Name 字段不需要为域名。这里使用的 zhihuRootCA
生成后即可将 certs/ca.cert.pem 安装于客户端操作系统/浏览器中作为受信任的跟证书颁发机构,由此 CA 签署的证书均会被客户端信任
生成服务器密钥
生成私钥
与 CA 私钥生成方法相同
3|2生成证书请求文件
填写证书相关信息,这里 Common Name 字段需要为证书域名。需要提前在 openssl.cnf 中编辑好 subjectAltName 以保证证书扩展字段中 DNS 可选域名正确。
3|3使用 CA 签发服务器证书
1 | openssl ca -config openssl.cnf -extensions server_cert -days 1095 -md sha256 -in certs/stf.csr.pem -out certs/stf.cert.pem |
需要提前在 openssl.cnf 中编辑好 subjectAltName 以保证证书扩展字段中 DNS 可选域名正确。
以上输入的两次国家组织等信息 尽量相同
至此:已经生成pem文件
因为nginx和tomcat不支持pem证书,所以需要转为jks证书
执行如下的openssl指令,将stf.cert.pem和stf.key.pem(证书和证书的密钥文件)导出到PKCS12格式的证书文件(p12证书):
把ca/private/stf.key.pem文件复制一份到ca\certs下 cmd命令进入到ca\certs下执行命令
此时文件夹下已经有了.p12文件
4|04.将.p12转为jks文件
5|0证书的使用
ca.cert.pem:打开浏览器 > 设置 > 安全 > 管理证书
导入ca.cert.pem(打开文件所在路径,后缀选择*.*) 证书存储选择"受信任的根证书颁发机构"
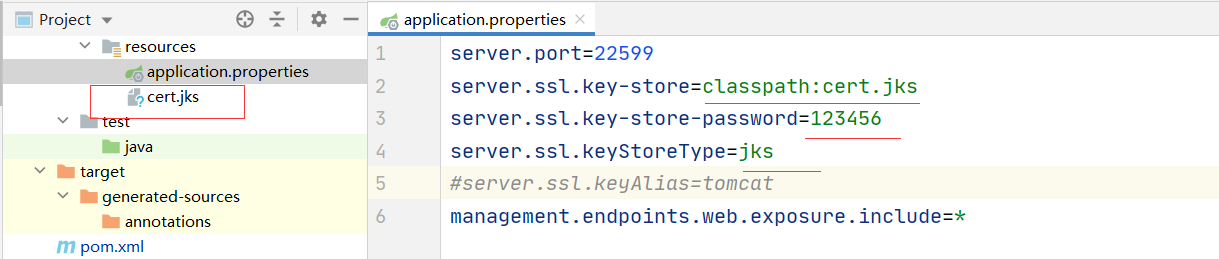
cert.jks:导入Java项目 配置properties
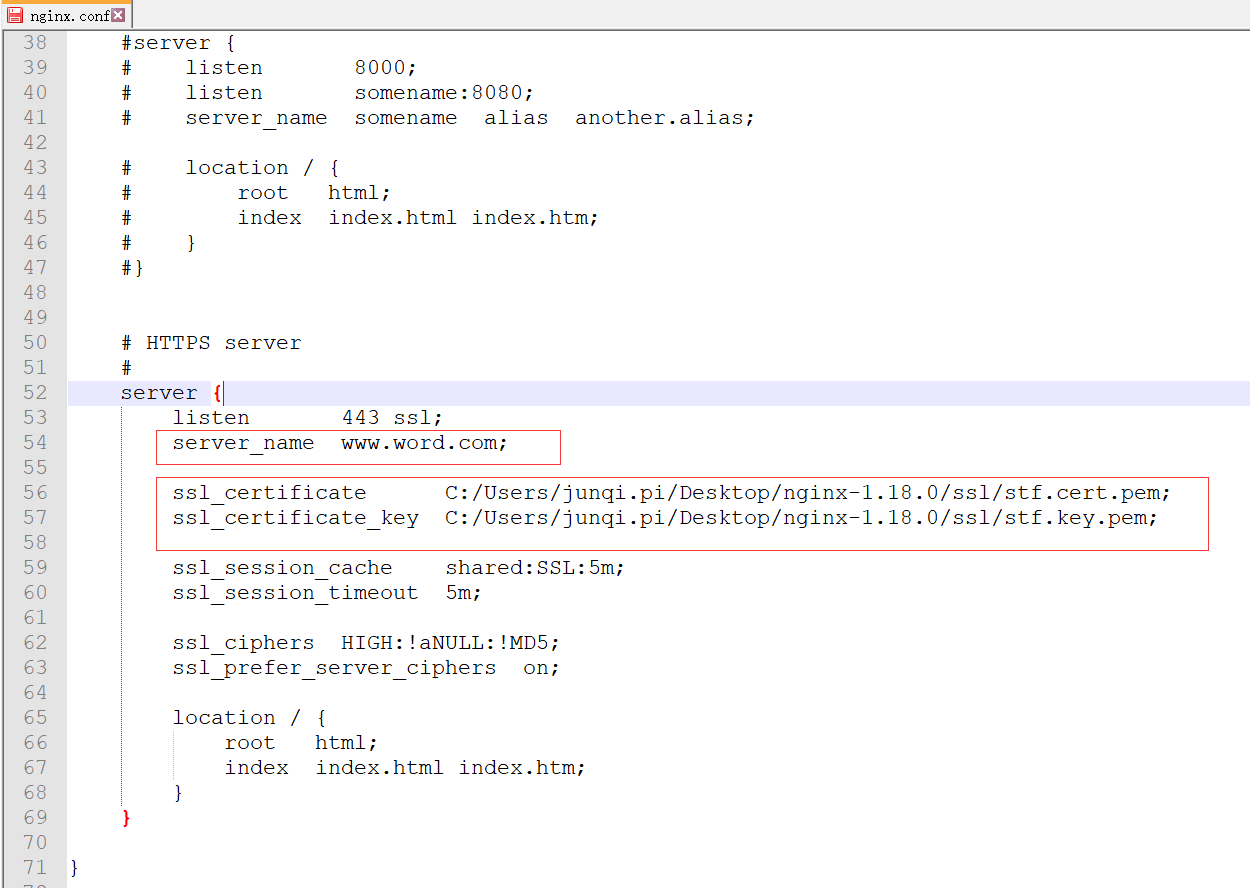
stf.cert.pem和stf.key.pem:将文件放到放到nginx的ssl目录下
重启项目,浏览器,nginx(之前启动过nginx的杀掉进程,重新启动)
__EOF__

本文链接:https://www.cnblogs.com/pijunqi/p/14168493.html
关于博主:评论和私信会在第一时间回复。或者直接私信我。
版权声明:本博客所有文章除特别声明外,均采用 BY-NC-SA 许可协议。转载请注明出处!
声援博主:如果您觉得文章对您有帮助,可以点击文章右下角【推荐】一下。您的鼓励是博主的最大动力!
本文来自博客园,作者:皮军旗,转载请注明原文链接:https://www.cnblogs.com/pijunqi/p/14168493.html




【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· AI与.NET技术实操系列:向量存储与相似性搜索在 .NET 中的实现
· 基于Microsoft.Extensions.AI核心库实现RAG应用
· Linux系列:如何用heaptrack跟踪.NET程序的非托管内存泄露
· 开发者必知的日志记录最佳实践
· SQL Server 2025 AI相关能力初探
· 震惊!C++程序真的从main开始吗?99%的程序员都答错了
· winform 绘制太阳,地球,月球 运作规律
· 【硬核科普】Trae如何「偷看」你的代码?零基础破解AI编程运行原理
· 上周热点回顾(3.3-3.9)
· 超详细:普通电脑也行Windows部署deepseek R1训练数据并当服务器共享给他人