传输层安全性协议 2015年,RFC 7568 标准弃用了SSL 3.0。 其前身安全套接层 SSL是TLS前身
小结:
1)记录层、传输层、会话秘钥
SSL包含记录层(Record Layer)和传输层,记录层协议确定传输层数据的封装格式。传输层安全协议使用X.509认证,之后利用非对称加密演算来对通信方做身份认证,之后交换对称密钥作为会谈密钥(Session key)。这个会谈密钥是用来将通信两方交换的资料做加密,保证两个应用间通信的保密性和可靠性,使客户与服务器应用之间的通信不被攻击者窃听。
2)协议在传输层,与应用层不耦合
TLS协议的优势是与高层的应用层协议(如HTTP、FTP、Telnet等)无耦合。应用层协议能透明地运行在TLS协议之上,由TLS协议进行创建加密通道需要的协商和认证。应用层协议传送的数据在通过TLS协议时都会被加密,从而保证通信的私密性。
3)创建安全连接
- 当客户端连接到支持TLS协议的服务器要求创建安全连接并列出了受支持的密码包(包括加密算法、散列算法等),握手开始。
- 服务器从该列表中决定密码包,并通知客户端。
- 服务器发回其数字证书,此证书通常包含服务器的名称、受信任的证书颁发机构(CA)和服务器的公钥。
- 客户端确认其颁发的证书的有效性。
- 为了生成会话密钥用于安全连接,客户端使用服务器的公钥加密随机生成的密钥,并将其发送到服务器,只有服务器才能使用自己的私钥解密。
- 利用随机数,双方生成用于加密和解密的对称密钥。这就是TLS协议的握手,握手完毕后的连接是安全的,直到连接(被)关闭。如果上述任何一个步骤失败,TLS握手过程就会失败,并且断开所有的连接。
4)模块划分
1、密钥交换和密钥协商
2、加密密码
3、数据完整性
https://zh.wikipedia.org/wiki/傳輸層安全性協定
传输层安全性协议(英语:Transport Layer Security,缩写:TLS)及其前身安全套接层(英语:Secure Sockets Layer,缩写:SSL)是一种安全协议,目的是为互联网通信提供安全及数据完整性保障。网景公司(Netscape)在1994年推出首版网页浏览器-网景导航者时,推出HTTPS协议,以SSL进行加密,这是SSL的起源。IETF将SSL进行标准化,1999年公布TLS 1.0标准文件(RFC 2246)。随后又公布TLS 1.1(RFC 4346,2006年)、TLS 1.2(RFC 5246,2008年)和TLS 1.3(RFC 8446,2018年)。在浏览器、电子邮件、即时通信、VoIP、网络传真等应用程序中,广泛使用这个协议。许多网站,如Google、Facebook、Wikipedia等也以这个协议来创建安全连线,发送资料。目前已成为互联网上保密通信的工业标准。
SSL包含记录层(Record Layer)和传输层,记录层协议确定传输层数据的封装格式。传输层安全协议使用X.509认证,之后利用非对称加密演算来对通信方做身份认证,之后交换对称密钥作为会谈密钥(Session key)。这个会谈密钥是用来将通信两方交换的资料做加密,保证两个应用间通信的保密性和可靠性,使客户与服务器应用之间的通信不被攻击者窃听。
目录
概论[编辑]
TLS协议采用主从式架构模型,用于在两个应用程序间透过网络创建起安全的连线,防止在交换资料时受到窃听及篡改。
TLS协议的优势是与高层的应用层协议(如HTTP、FTP、Telnet等)无耦合。应用层协议能透明地运行在TLS协议之上,由TLS协议进行创建加密通道需要的协商和认证。应用层协议传送的数据在通过TLS协议时都会被加密,从而保证通信的私密性。
TLS协议是可选的,必须配置客户端和服务器才能使用。主要有两种方式实现这一目标:一个是使用统一的TLS协议端口(例如:用于HTTPS的端口443);另一个是客户端请求服务器连接到TLS时使用特定的协议机制(例如:电子邮件常用的STARTTLS)。一旦客户端和服务器都同意使用TLS协议,他们通过使用一个握手过程协商出一个有状态的连接以传输数据[1]。通过握手,客户端和服务器协商各种参数用于创建安全连接:
- 当客户端连接到支持TLS协议的服务器要求创建安全连接并列出了受支持的密码包(包括加密算法、散列算法等),握手开始。
- 服务器从该列表中决定密码包,并通知客户端。
- 服务器发回其数字证书,此证书通常包含服务器的名称、受信任的证书颁发机构(CA)和服务器的公钥。
- 客户端确认其颁发的证书的有效性。
- 为了生成会话密钥用于安全连接,客户端使用服务器的公钥加密随机生成的密钥,并将其发送到服务器,只有服务器才能使用自己的私钥解密。
- 利用随机数,双方生成用于加密和解密的对称密钥。这就是TLS协议的握手,握手完毕后的连接是安全的,直到连接(被)关闭。如果上述任何一个步骤失败,TLS握手过程就会失败,并且断开所有的连接。
| 互联网安全协议 |
|---|
| 密钥管理 |
| 应用层 |
| 域名系统 |
| 网络层 |
发展历史[编辑]
| 协议 | 发布时间 | 状态 |
|---|---|---|
| SSL 1.0 | 未公布 | 未公布 |
| SSL 2.0 | 1995年 | 已于2011年弃用[2] |
| SSL 3.0 | 1996年 | 已于2015年弃用[3] |
| TLS 1.0 | 1999年 | 于2021年弃用[4] |
| TLS 1.1 | 2006年 | 于2021年弃用[4] |
| TLS 1.2 | 2008年 | |
| TLS 1.3 | 2018年 |
安全网络编程[编辑]
早期的研究工作,为方便改造原有网络应用程序,在1993年已经有了相似的Berkeley套接字安全传输层API方法[5]。
SSL 1.0、2.0和3.0[编辑]
SSL(Secure Sockets Layer)是网景公司(Netscape)设计的主要用于Web的安全传输协议,这种协议在Web上获得了广泛的应用[6]。
基础算法由作为网景公司的首席科学家塔希尔·盖莫尔(Taher Elgamal)编写,所以他被人称为“SSL之父”。[7][8]
2014年10月,Google发布在SSL 3.0中发现设计缺陷,建议禁用此一协议。攻击者可以向TLS发送虚假错误提示,然后将安全连接强行降级到过时且不安全的SSL 3.0,然后就可以利用其中的设计漏洞窃取敏感信息。Google在自己公司相关产品中陆续禁止回溯兼容,强制使用TLS协议。Mozilla也在11月25日发布的Firefox 34中彻底禁用了SSL 3.0。微软同样发出了安全通告[9]。
- 1.0版本从未公开过,因为存在严重的安全漏洞。
- 2.0版本在1995年2月发布。2011年,RFC 6176 标准弃用了SSL 2.0。
- 3.0版本在1996年发布,是由网景工程师保罗·科切、Phil Karlton和Alan Freier完全重新设计的。2015年,RFC 7568 标准弃用了SSL 3.0。
TLS 1.0[编辑]
IETF将SSL标准化,即 RFC 2246 ,并将其称为TLS(Transport Layer Security)。
TLS 1.1[编辑]
TLS 1.1在 RFC 4346 中定义,于2006年4月发表[10],它是TLS 1.0的更新。在此版本中的差异包括:
微软、Google、苹果、Mozilla四家浏览器业者将在2020年终止支持TLS 1.0及1.1版[12]。2021年3月,RFC 8996标准弃用了TLS 1.0和TLS 1.1[4]。
TLS 1.2[编辑]
TLS 1.2在 RFC 5246 中定义,于2008年8月发表。它基于更早的TLS 1.1规范。主要区别包括:
- 增加SHA-2密码散列函数。
- 增加AEAD加密算法,如GCM模式。
- 添加TLS扩展定义和AES密码组合[11]:2。所有TLS版本在2011年3月发布的RFC 6176中删除了对SSL的兼容,这样TLS会话将永远无法协商使用的SSL 2.0以避免安全问题。
TLS 1.3[编辑]
TLS 1.3在 RFC 8446 中定义,于2018年8月发表。[13]它与TLS 1.2的主要区别包括:
- 将密钥交换算法(如ECDHE)和认证算法(如RSA)从密码包中分离出来。
- 移除MD5、SHA1密码散列函数的支持。
- 请求数字签名。
- 集成HKDF和半短暂DH提议。
- 替换使用PSK和票据的恢复。
- 支持1-RTT握手并初步支持0-RTT。
- 通过在密钥协商期间使用临时密钥来保证完善的前向安全性。
- 放弃许多不安全或过时特性的支持,包括数据压缩、重新协商、非AEAD加密算法、静态RSA和静态DH密钥交换、自定义DHE分组、点格式协商、更改密码本规范的协议、UNIX时间的Hello消息,以及长度字段AD输入到AEAD密码本。
- 较TLS 1.2速度更快,性能更好。
- 移除RC4加密算法的支持。
- 集成会话散列的使用。
- 弃用记录层版本号和冻结数以改进向后兼容性。
- 将一些安全相关的算法细节从附录移动到标准,并将ClientKeyShare降级到附录。
- 支持Ed25519和Ed448数字签名算法。
- 支持X25519密钥交换。
- 支持带Poly1305消息验证码的ChaCha20加密算法。
- 支持加密服务器名称指示(Encrypted Server Name Indication, ESNI)。[14]
网络安全服务(NSS)是由Mozilla开发并由其网络浏览器Firefox使用的加密库,自2017年2月起便默认启用TLS 1.3。[15]随后TLS 1.3被添加到2017年3月发布的Firefox 52.0中,但它由于某些用户的兼容性问题,默认情况下禁用。[16]直到Firefox 60.0才正式默认启用。[17]
Google Chrome曾在2017年短时间将TLS 1.3设为默认,然而由于类似Blue Coat Systems等不兼容组件而被取消。[18]
wolfSSL在2017年5月发布的3.11.1版本中启用了TLS 1.3。[19]作为第一款支持TLS 1.3部署,wolfSSL 3.11.1 支持 TLS 1.3 Draft 18(现已支持到Draft 28),[20]同时官方也发布了一系列关于TLS 1.2和TLS 1.3性能差距的博客。[21]
算法[编辑]
密钥交换和密钥协商[编辑]
在客户端和服务器开始交换TLS所保护的加密信息之前,他们必须安全地交换或协定加密密钥和加密数据时要使用的密码。用于密钥交换的方法包括:使用RSA算法生成公钥和私钥(在TLS 握手协议中被称为TLS_RSA)、Diffie-Hellman(在TLS握手协议中被称为TLS_DH)、临时Diffie-Hellman(在TLS握手协议中被称为TLS_DHE)、椭圆曲线迪菲-赫尔曼(在TLS握手协议中被称为TLS_ECDH)、临时椭圆曲线Diffie-Hellman(在TLS握手协议中被称为TLS_ECDHE)、匿名Diffie-Hellman(在TLS握手协议中被称为TLS_DH_anon)[22]和预共享密钥(在TLS握手协议中被称为TLS_PSK)。[23]
TLS_DH_anon和TLS_ECDH_anon的密钥协商协议不能验证服务器或用户,因为易受中间人攻击因此很少使用。只有TLS_DHE和TLS_ECDHE提供前向保密能力。
在交换过程中使用的公钥/私钥加密密钥的长度和在交换协议过程中使用的公钥证书也各不相同,因而提供的强健性的安全。2013年7月,Google宣布向其用户提供的TLS加密将不再使用1024位公钥并切换到至少2048位,以提高安全性。[24]
| 算法 | SSL 2.0 | SSL 3.0 | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 | 状态 |
|---|---|---|---|---|---|---|---|
| RSA | 是 | 是 | 是 | 是 | 是 | 否 | RFC中TLS 1.2的定义 |
| DH-RSA | 否 | 是 | 是 | 是 | 是 | 否 | |
| DHE-RSA(具有前向安全性) | 否 | 是 | 是 | 是 | 是 | 是 | |
| ECDH-RSA | 否 | 否 | 是 | 是 | 是 | 否 | |
| ECDHE-RSA(具有前向安全性) | 否 | 否 | 是 | 是 | 是 | 是 | |
| DH-DSS | 否 | 是 | 是 | 是 | 是 | 否 | |
| DHE-DSS(具有前向安全性) | 否 | 是 | 是 | 是 | 是 | 否[25] | |
| ECDH-ECDSA | 否 | 否 | 是 | 是 | 是 | 否 | |
| ECDHE-ECDSA(具有前向安全性) | 否 | 否 | 是 | 是 | 是 | 是 | |
| SRP | 否 | 否 | 是 | 是 | 是 | ||
| PSK-RSA | 否 | 否 | 是 | 是 | 是 | ||
| DHE-PSK(具有前向安全性) | 否 | 否 | 是 | 是 | 是 | 是 | |
| ECDHE-PSK(具有前向安全性) | 否 | 否 | 是 | 是 | 是 | 是 | |
| SRP | 否 | 否 | 是 | 是 | 是 | ||
| SRP-DSS | 否 | 否 | 是 | 是 | 是 | ||
| SRP-RSA | 否 | 否 | 是 | 是 | 是 | ||
| Kerberos | 否 | 否 | 是 | 是 | 是 | ||
| DH-ANON(不安全) | 否 | 是 | 是 | 是 | 是 | ||
| ECDH-ANON(不安全) | 否 | 否 | 是 | 是 | 是 | ||
| GOST R 34.10-94 / 34.10-2001[26] | 否 | 否 | 是 | 是 | 是 | 在RFC草案中提出 |
加密密码[编辑]
| 密码 | 协议版本 | 状态 | |||||||
|---|---|---|---|---|---|---|---|---|---|
| 类型 | 算法 | 长度(bits) | SSL 2.0 | SSL 3.0 [n 1][n 2][n 3][n 4] | TLS 1.0 [n 1][n 3] | TLS 1.1 [n 1] | TLS 1.2 [n 1] | TLS 1.3 | |
| 分组密码及其加密方式 | AES GCM[27][n 5] | 256, 128 | 不适用 | 不适用 | 不适用 | 不适用 | 安全 | 安全 | RFC中TLS 1.2的定义 |
| AES CCM[28][n 5] | 不适用 | 不适用 | 不适用 | 不适用 | 安全 | 安全 | |||
| AES CBC[n 6] | 不适用 | 不安全 | 依赖于后期添加的措施 | 依赖于后期添加的措施 | 依赖于后期添加的措施 | 不适用 | |||
| Camellia GCM[29][n 5] | 256, 128 | 不适用 | 不适用 | 不适用 | 不适用 | 安全 | 不适用 | ||
| Camellia CBC[30][n 6] | 不适用 | 不安全 | 依赖于后期添加的措施 | 依赖于后期添加的措施 | 依赖于后期添加的措施 | 不适用 | |||
| ARIA加密算法 GCM[31][n 5] | 256, 128 | 不适用 | 不适用 | 不适用 | 不适用 | 安全 | 不适用 | ||
| ARIA加密算法 CBC[31][n 6] | 不适用 | 不适用 | 依赖于后期添加的措施 | 依赖于后期添加的措施 | 依赖于后期添加的措施 | 不适用 | |||
| SEED加密算法 CBC[32][n 6] | 128 | 不适用 | 不安全 | 依赖于后期添加的措施 | 依赖于后期添加的措施 | 依赖于后期添加的措施 | 不适用 | ||
| 3DES EDE CBC[n 6][n 7] | 112[n 8] | 不安全 | 不安全 | 不安全 | 不安全 | 不安全 | 不适用 | ||
| GOST 28147-89 CNT[26][n 7] | 256 | 不适用 | 不适用 | 不安全 | 不安全 | 不安全 | 不适用 | 定义于RFC 4357 | |
| IDEA CBC[n 6][n 7][n 9] | 128 | 不安全 | 不安全 | 不安全 | 不安全 | 不适用 | 不适用 | 从TLS 1.2标准中移除 | |
| DES CBC[n 6][n 7][n 9] | 56 | 不安全 | 不安全 | 不安全 | 不安全 | 不适用 | 不适用 | ||
| 40[n 10] | 不安全 | 不安全 | 不安全 | 不适用 | 不适用 | 不适用 | 在TLS 1.1及之后版本禁止 | ||
| RC2 CBC[n 6][n 7] | 40[n 10] | 不安全 | 不安全 | 不安全 | 不适用 | 不适用 | 不适用 | ||
| 流加密 | ChaCha20-Poly1305[37][n 5] | 256 | 不适用 | 不适用 | 不适用 | 不适用 | 安全 | 安全 | RFC中TLS 1.2的定义 |
| RC4[n 11] | 128 | 不安全 | 不安全 | 不安全 | 不安全 | 不安全 | 不适用 | 由RFC 7465定义所有版本TLS禁止 | |
| 40[n 10] | 不安全 | 不安全 | 不安全 | 不适用 | 不适用 | 不适用 | |||
| None | Null[n 12] | – | 不安全 | 不安全 | 不安全 | 不安全 | 不安全 | 不适用 | RFC中TLS 1.2的定义 |
- 标注
- ^ 跳转至:1.0 1.1 1.2 1.3 RFC 5746 must be implemented to fix a renegotiation flaw that would otherwise break this protocol.
- ^ If libraries implement fixes listed in RFC 5746, this violates the SSL 3.0 specification, which the IETF cannot change unlike TLS. Fortunately, most current libraries implement the fix and disregard the violation that this causes.
- ^ 跳转至:3.0 3.1 The BEAST attack breaks all block ciphers (CBC ciphers) used in SSL 3.0 and TLS 1.0 unless mitigated by the client and/or the server. See § Web browsers.
- ^ The POODLE attack breaks all block ciphers (CBC ciphers) used in SSL 3.0 unless mitigated by the client and/or the server. See § Web browsers.
- ^ 跳转至:5.0 5.1 5.2 5.3 5.4 AEAD ciphers (such as GCM and CCM) can be used in only TLS 1.2.
- ^ 跳转至:6.0 6.1 6.2 6.3 6.4 6.5 6.6 6.7 CBC ciphers can be attacked with the Lucky Thirteen attack if the library is not written carefully to eliminate timing side channels.
- ^ 跳转至:7.0 7.1 7.2 7.3 7.4 The Sweet32 attack breaks block ciphers with a block size of 64 bits.[33]
- ^ Although the key length of 3DES is 168 bits, effective security strength of 3DES is only 112 bits,[34] which is below the recommended minimum of 128 bits.[35]
- ^ 跳转至:9.0 9.1 IDEA and DES have been removed from TLS 1.2.[36]
- ^ 跳转至:10.0 10.1 10.2 40 bits strength of cipher suites were designed to operate at reduced key lengths to comply with US regulations about the export of cryptographic software containing certain strong encryption algorithms (see 美国的加密技术出口管制). These weak suites are forbidden in TLS 1.1 and later.
- ^ Use of RC4 in all versions of TLS is prohibited by RFC 7465 (because RC4 attacks weaken or break RC4 used in SSL/TLS).
- ^ Authentication only, no encryption.
数据完整性[编辑]
消息认证码(MAC)用于对数据完整性进行认证。HMAC用于CBC模式的块密码。AEAD例如GCM模式和CCM模式使用AEAD内置的消息鉴别码,不使用HMAC[38]。另外,在TLS握手过程中需要使用基于HMAC的伪随机函数(PRF),或HKDF。
| 算法 | SSL 2.0 | SSL 3.0 | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 | 状态 |
|---|---|---|---|---|---|---|---|
| HMAC-MD5 | 是 | 是 | 是 | 是 | 是 | 否 | RFC中TLS 1.2的定义 |
| HMAC-SHA1 | 否 | 是 | 是 | 是 | 是 | 否 | |
| HMAC-SHA256/384 | 否 | 否 | 否 | 否 | 是 | 否 | |
| AEAD | 否 | 否 | 否 | 否 | 是 | 是 | |
| GOST 28147-89 IMIT | 否 | 否 | 是 | 是 | 是 | 在RFC草案中提出 | |
| GOST R 34.11-94 | 否 | 否 | 是 | 是 | 是 |
过程[编辑]
TLS在互联网上为HTTP等应用程序提供身份验证、加密、完整性,其基础是公钥基础设施。这是因为公钥基础设施普遍商业运营。TLS协议的设计在某种程度上能够使主从架构应用程序通讯预防窃听、干扰和消息伪造。
TLS包含几个基本阶段:
- 对等协商支持的TLS版本,和支持的密码包。
- 基于非对称密钥的身份认证,通常是基于PKI证书的身份认证。服务器将其X.509证书发送给客户端,由客户端验证服务器的身份。如果服务器要验证客户端的证书,则客户端可能会将客户端证书发送给服务器。通常仅验证服务器,不验证客户端。
- 基于对称密钥的数据加密。客户端生成随机数作为会话密钥,并使用服务器公钥(服务器公钥在服务器证书中)加密会话密钥,最后将已加密的会话密钥发送给服务器。由服务器的私钥解密出会话密钥。最后使用此会话密钥加密数据。TLS也可以使用预共享密钥(PSK)作为对称密钥。
在第一阶段,客户端与服务器协商所用密码算法。当前广泛实现的算法选择如下:
https://en.wikipedia.org/wiki/Transport_Layer_Security
Transport Layer Security (TLS), the successor of the now-deprecated Secure Sockets Layer (SSL), is a cryptographic protocol designed to provide communications security over a computer network. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in securing HTTPS remains the most publicly visible.
The TLS protocol aims primarily to provide privacy and data integrity between two or more communicating computer applications. It runs in the application layer and is itself composed of two layers: the TLS record and the TLS handshake protocols.
TLS is a proposed Internet Engineering Task Force (IETF) standard, first defined in 1999, and the current version is TLS 1.3 defined in August 2018. TLS builds on the earlier SSL specifications (1994, 1995, 1996) developed by Netscape Communications for adding the HTTPS protocol to their Navigator web browser.
Description[edit]
Client-server applications use the TLS protocol to communicate across a network in a way designed to prevent eavesdropping and tampering.
Since applications can communicate either with or without TLS (or SSL), it is necessary for the client to request that the server sets up a TLS connection.[1] One of the main ways of achieving this is to use a different port number for TLS connections. For example, port 80 is typically used for unencrypted HTTP traffic while port 443 is the common port used for encrypted HTTPS traffic. Another mechanism is for the client to make a protocol-specific request to the server to switch the connection to TLS; for example, by making a STARTTLS request when using the mail and news protocols.
Once the client and server have agreed to use TLS, they negotiate a stateful connection by using a handshaking procedure.[2] The protocols use a handshake with an asymmetric cipher to establish not only cipher settings but also a session-specific shared key with which further communication is encrypted using a symmetric cipher. During this handshake, the client and server agree on various parameters used to establish the connection's security:
- The handshake begins when a client connects to a TLS-enabled server requesting a secure connection and the client presents a list of supported cipher suites (ciphers and hash functions).
- From this list, the server picks a cipher and hash function that it also supports and notifies the client of the decision.
- The server usually then provides identification in the form of a digital certificate. The certificate contains the server name, the trusted certificate authority (CA) that vouches for the authenticity of the certificate, and the server's public encryption key.
- The client confirms the validity of the certificate before proceeding.
- To generate the session keys used for the secure connection, the client either:
- encrypts a random number (PreMasterSecret) with the server's public key and sends the result to the server (which only the server should be able to decrypt with its private key); both parties then use the random number to generate a unique session key for subsequent encryption and decryption of data during the session
- uses Diffie–Hellman key exchange to securely generate a random and unique session key for encryption and decryption that has the additional property of forward secrecy: if the server's private key is disclosed in future, it cannot be used to decrypt the current session, even if the session is intercepted and recorded by a third party.
This concludes the handshake and begins the secured connection, which is encrypted and decrypted with the session key until the connection closes. If any one of the above steps fails, then the TLS handshake fails and the connection is not created.
TLS and SSL do not fit neatly into any single layer of the OSI model or the TCP/IP model.[3][4] TLS runs "on top of some reliable transport protocol (e.g., TCP),"[5] which would imply that it is above the transport layer. It serves encryption to higher layers, which is normally the function of the presentation layer. However, applications generally use TLS as if it were a transport layer,[3][4] even though applications using TLS must actively control initiating TLS handshakes and handling of exchanged authentication certificates.[5]
When secured by TLS, connections between a client (e.g., a web browser) and a server (e.g., wikipedia.org) should have one or more of the following properties:
- The connection is private (or secure) because a symmetric-key algorithm is used to encrypt the data transmitted. The keys for this symmetric encryption are generated uniquely for each connection and are based on a shared secret that was negotiated at the start of the session. The server and client negotiate the details of which encryption algorithm and cryptographic keys to use before the first byte of data is transmitted (see below). The negotiation of a shared secret is both secure (the negotiated secret is unavailable to eavesdroppers and cannot be obtained, even by an attacker who places themself in the middle of the connection) and reliable (no attacker can modify the communications during the negotiation without being detected).
- The identity of the communicating parties can be authenticated using public-key cryptography. This authentication is required for the server and optional for the client.[6]
- The connection is reliable because each message transmitted includes a message integrity check using a message authentication code to prevent undetected loss or alteration of the data during transmission.[7]: 3
In addition to the above, careful configuration of TLS can provide additional privacy-related properties such as forward secrecy, ensuring that any future disclosure of encryption keys cannot be used to decrypt any TLS communications recorded in the past.
TLS supports many different methods for exchanging keys, encrypting data, and authenticating message integrity. As a result, secure configuration of TLS involves many configurable parameters, and not all choices provide all of the privacy-related properties described in the list above (see the tables below § Key exchange, § Cipher security, and § Data integrity).
Attempts have been made to subvert aspects of the communications security that TLS seeks to provide, and the protocol has been revised several times to address these security threats. Developers of web browsers have repeatedly revised their products to defend against potential security weaknesses after these were discovered (see TLS/SSL support history of web browsers).
History and development[edit]
| Protocol | Published | Status |
|---|---|---|
| SSL 1.0 | Unpublished | Unpublished |
| SSL 2.0 | 1995 | Deprecated in 2011 (RFC 6176) |
| SSL 3.0 | 1996 | Deprecated in 2015 (RFC 7568) |
| TLS 1.0 | 1999 | Deprecated in 2020 (RFC 8996)[8][9][10] |
| TLS 1.1 | 2006 | Deprecated in 2020 (RFC 8996)[8][9][10] |
| TLS 1.2 | 2008 | |
| TLS 1.3 | 2018 |
Secure Data Network System[edit]
The Transport Layer Security Protocol (TLS), together with several other basic network security platforms, was developed through a joint initiative begun in August 1986, among the National Security Agency, the National Bureau of Standards, the Defense Communications Agency, and twelve communications and computer corporations who initiated a special project called the Secure Data Network System (SDNS).[11] The program was described in September 1987 at the 10th National Computer Security Conference in an extensive set of published papers. The innovative research program focused on designing the next generation of secure computer communications network and product specifications to be implemented for applications on public and private internets. It was intended to complement the rapidly emerging new OSI internet standards moving forward both in the U.S. government's GOSIP Profiles and in the huge ITU-ISO JTC1 internet effort internationally. Originally known as the SP4 protocol, it was renamed TLS and subsequently published in 1995 as international standard ITU-T X.274| ISO/IEC 10736:1995.
Secure Network Programming[edit]
Early research efforts towards transport layer security included the Secure Network Programming (SNP) application programming interface (API), which in 1993 explored the approach of having a secure transport layer API closely resembling Berkeley sockets, to facilitate retrofitting pre-existing network applications with security measures.[12]
SSL 1.0, 2.0, and 3.0[edit]
Netscape developed the original SSL protocols, and Taher Elgamal, chief scientist at Netscape Communications from 1995 to 1998, has been described as the "father of SSL".[13][14][15][16] SSL version 1.0 was never publicly released because of serious security flaws in the protocol. Version 2.0, after being released in February 1995 was quickly discovered to contain a number of security and usability flaws. It used the same cryptographic keys for message authentication and encryption. It had a weak MAC construction that used the MD5 hash function with a secret prefix, making it vulnerable to length extension attacks. And it provided no protection for either the opening handshake or an explicit message close, both of which meant man-in-the-middle attacks could go undetected. Moreover, SSL 2.0 assumed a single service and a fixed domain certificate, conflicting with the widely used feature of virtual hosting in Web servers, so most websites were effectively impaired from using SSL.
These flaws necessitated the complete redesign of the protocol to SSL version 3.0.[17][15] Released in 1996, it was produced by Paul Kocher working with Netscape engineers Phil Karlton and Alan Freier, with a reference implementation by Christopher Allen and Tim Dierks of Consensus Development. Newer versions of SSL/TLS are based on SSL 3.0. The 1996 draft of SSL 3.0 was published by IETF as a historical document in RFC 6101.
SSL 2.0 was deprecated in 2011 by RFC 6176. In 2014, SSL 3.0 was found to be vulnerable to the POODLE attack that affects all block ciphers in SSL; RC4, the only non-block cipher supported by SSL 3.0, is also feasibly broken as used in SSL 3.0.[18] SSL 3.0 was deprecated in June 2015 by RFC 7568.
TLS 1.0[edit]
TLS 1.0 was first defined in RFC 2246 in January 1999 as an upgrade of SSL Version 3.0, and written by Christopher Allen and Tim Dierks of Consensus Development. As stated in the RFC, "the differences between this protocol and SSL 3.0 are not dramatic, but they are significant enough to preclude interoperability between TLS 1.0 and SSL 3.0". Tim Dierks later wrote that these changes, and the renaming from "SSL" to "TLS", were a face-saving gesture to Microsoft, "so it wouldn't look [like] the IETF was just rubberstamping Netscape's protocol".[19]
The PCI Council suggested that organizations migrate from TLS 1.0 to TLS 1.1 or higher before June 30, 2018.[20][21] In October 2018, Apple, Google, Microsoft, and Mozilla jointly announced they would deprecate TLS 1.0 and 1.1 in March 2020.[8]
TLS 1.1[edit]
TLS 1.1 was defined in RFC 4346 in April 2006.[22] It is an update from TLS version 1.0. Significant differences in this version include:
- Added protection against cipher-block chaining (CBC) attacks.
- The implicit initialization vector (IV) was replaced with an explicit IV.
- Change in handling of padding errors.
- Support for IANA registration of parameters.[23]: 2
Support for TLS versions 1.0 and 1.1 was widely deprecated by web sites around 2020, disabling access to Firefox versions before 24 and Google Chrome before 29.[24][25][26]
TLS 1.2[edit]
TLS 1.2 was defined in RFC 5246 in August 2008. It is based on the earlier TLS 1.1 specification. Major differences include:
- The MD5–SHA-1 combination in the pseudorandom function (PRF) was replaced with SHA-256, with an option to use cipher suite specified PRFs.
- The MD5–SHA-1 combination in the finished message hash was replaced with SHA-256, with an option to use cipher suite specific hash algorithms. However, the size of the hash in the finished message must still be at least 96 bits.[27]
- The MD5–SHA-1 combination in the digitally signed element was replaced with a single hash negotiated during handshake, which defaults to SHA-1.
- Enhancement in the client's and server's ability to specify which hashes and signature algorithms they accept.
- Expansion of support for authenticated encryption ciphers, used mainly for Galois/Counter Mode (GCM) and CCM mode of Advanced Encryption Standard (AES) encryption.
- TLS Extensions definition and AES cipher suites were added.[23]: 2
All TLS versions were further refined in RFC 6176 in March 2011, removing their backward compatibility with SSL such that TLS sessions never negotiate the use of Secure Sockets Layer (SSL) version 2.0.
TLS 1.3[edit]
TLS 1.3 was defined in RFC 8446 in August 2018. It is based on the earlier TLS 1.2 specification. Major differences from TLS 1.2 include:[28]
- Separating key agreement and authentication algorithms from the cipher suites
- Removing support for weak and less-used named elliptic curves
- Removing support for MD5 and SHA-224 cryptographic hash functions
- Requiring digital signatures even when a previous configuration is used
- Integrating HKDF and the semi-ephemeral DH proposal
- Replacing resumption with PSK and tickets
- Supporting 1-RTT handshakes and initial support for 0-RTT
- Mandating perfect forward secrecy, by means of using ephemeral keys during the (EC)DH key agreement
- Dropping support for many insecure or obsolete features including compression, renegotiation, non-AEAD ciphers, non-PFS key exchange (among which are static RSA and static DH key exchanges), custom DHE groups, EC point format negotiation, Change Cipher Spec protocol, Hello message UNIX time, and the length field AD input to AEAD ciphers
- Prohibiting SSL or RC4 negotiation for backwards compatibility
- Integrating use of session hash
- Deprecating use of the record layer version number and freezing the number for improved backwards compatibility
- Moving some security-related algorithm details from an appendix to the specification and relegating ClientKeyShare to an appendix
- Adding the ChaCha20 stream cipher with the Poly1305 message authentication code
- Adding the Ed25519 and Ed448 digital signature algorithms
- Adding the x25519 and x448 key exchange protocols
- Adding support for sending multiple OCSP responses
- Encrypting all handshake messages after the ServerHello
Network Security Services (NSS), the cryptography library developed by Mozilla and used by its web browser Firefox, enabled TLS 1.3 by default in February 2017.[29] TLS 1.3 support was subsequently added — but due to compatibility issues for a small number of users, not automatically enabled[30] — to Firefox 52.0, which was released in March 2017. TLS 1.3 was enabled by default in May 2018 with the release of Firefox 60.0.[31]
Google Chrome set TLS 1.3 as the default version for a short time in 2017. It then removed it as the default, due to incompatible middleboxes such as Blue Coat web proxies.[32]
During the IETF 100 Hackathon which took place in Singapore in 2017, The TLS Group worked on adapting open-source applications to use TLS 1.3.[33][34] The TLS group was made up of individuals from Japan, United Kingdom, and Mauritius via the cyberstorm.mu team.[34] This work was continued in the IETF 101 Hackathon in London,[35] and the IETF 102 Hackathon in Montreal.[36]
wolfSSL enabled the use of TLS 1.3 as of version 3.11.1, released in May 2017.[37] As the first commercial TLS 1.3 implementation, wolfSSL 3.11.1 supported Draft 18 and now supports Draft 28,[38] the final version, as well as many older versions. A series of blogs were published on the performance difference between TLS 1.2 and 1.3.[39]
In September 2018, the popular OpenSSL project released version 1.1.1 of its library, in which support for TLS 1.3 was "the headline new feature".[40]
Support for TLS 1.3 was first added to SChannel with Windows 11 and Windows Server 2022.[41]
Enterprise Transport Security[edit]
The Electronic Frontier Foundation praised TLS 1.3 and expressed concern about the variant protocol Enterprise Transport Security (ETS) that intentionally disables important security measures in TLS 1.3.[42] Originally called Enterprise TLS (eTLS), ETS is a published standard known as the 'ETSI TS103523-3', "Middlebox Security Protocol, Part3: Enterprise Transport Security". It is intended for use entirely within proprietary networks such as banking systems. ETS does not support forward secrecy so as to allow third-party organizations connected to the proprietary networks to be able to use their private key to monitor network traffic for the detection of malware and to make it easier to conduct audits.[43][44] Despite the claimed benefits, the EFF warned that the loss of forward secrecy could make it easier for data to be exposed along with saying that there are better ways to analyze traffic.
Digital certificates[edit]
A digital certificate certifies the ownership of a public key by the named subject of the certificate, and indicates certain expected usages of that key. This allows others (relying parties) to rely upon signatures or on assertions made by the private key that corresponds to the certified public key. Keystores and trust stores can be in various formats, such as .pem, .crt, .pfx, and .jks.
TLS typically relies on a set of trusted third-party certificate authorities to establish the authenticity of certificates. Trust is usually anchored in a list of certificates distributed with user agent software,[45] and can be modified by the relying party.
According to Netcraft, who monitors active TLS certificates, the market-leading certificate authority (CA) has been Symantec since the beginning of their survey (or VeriSign before the authentication services business unit was purchased by Symantec). As of 2015, Symantec accounted for just under a third of all certificates and 44% of the valid certificates used by the 1 million busiest websites, as counted by Netcraft.[46] In 2017, Symantec sold its TLS/SSL business to DigiCert.[47] In an updated report, it was shown that IdenTrust, DigiCert, and Sectigo are the top 3 certificate authorities in terms of market share since May 2019.[48]
As a consequence of choosing X.509 certificates, certificate authorities and a public key infrastructure are necessary to verify the relation between a certificate and its owner, as well as to generate, sign, and administer the validity of certificates. While this can be more convenient than verifying the identities via a web of trust, the 2013 mass surveillance disclosures made it more widely known that certificate authorities are a weak point from a security standpoint, allowing man-in-the-middle attacks (MITM) if the certificate authority cooperates (or is compromised).[49][50]
Algorithms[edit]
Key exchange or key agreement[edit]
Before a client and server can begin to exchange information protected by TLS, they must securely exchange or agree upon an encryption key and a cipher to use when encrypting data (see § Cipher). Among the methods used for key exchange/agreement are: public and private keys generated with RSA (denoted TLS_RSA in the TLS handshake protocol), Diffie–Hellman (TLS_DH), ephemeral Diffie–Hellman (TLS_DHE), elliptic-curve Diffie–Hellman (TLS_ECDH), ephemeral elliptic-curve Diffie–Hellman (TLS_ECDHE), anonymous Diffie–Hellman (TLS_DH_anon),[7] pre-shared key (TLS_PSK)[51] and Secure Remote Password (TLS_SRP).[52]
The TLS_DH_anon and TLS_ECDH_anon key agreement methods do not authenticate the server or the user and hence are rarely used because those are vulnerable to man-in-the-middle attacks. Only TLS_DHE and TLS_ECDHE provide forward secrecy.
Public key certificates used during exchange/agreement also vary in the size of the public/private encryption keys used during the exchange and hence the robustness of the security provided. In July 2013, Google announced that it would no longer use 1024-bit public keys and would switch instead to 2048-bit keys to increase the security of the TLS encryption it provides to its users because the encryption strength is directly related to the key size.[53][54]
| Algorithm | SSL 2.0 | SSL 3.0 | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 | Status |
|---|---|---|---|---|---|---|---|
| RSA | Yes | Yes | Yes | Yes | Yes | No | Defined for TLS 1.2 in RFCs |
| DH-RSA | No | Yes | Yes | Yes | Yes | No | |
| DHE-RSA (forward secrecy) | No | Yes | Yes | Yes | Yes | Yes | |
| ECDH-RSA | No | No | Yes | Yes | Yes | No | |
| ECDHE-RSA (forward secrecy) | No | No | Yes | Yes | Yes | Yes | |
| DH-DSS | No | Yes | Yes | Yes | Yes | No | |
| DHE-DSS (forward secrecy) | No | Yes | Yes | Yes | Yes | No[55] | |
| ECDH-ECDSA | No | No | Yes | Yes | Yes | No | |
| ECDHE-ECDSA (forward secrecy) | No | No | Yes | Yes | Yes | Yes | |
| ECDH-EdDSA | No | No | Yes | Yes | Yes | No | |
| ECDHE-EdDSA (forward secrecy)[56] | No | No | Yes | Yes | Yes | Yes | |
| PSK | No | No | Yes | Yes | Yes | ||
| PSK-RSA | No | No | Yes | Yes | Yes | ||
| DHE-PSK (forward secrecy) | No | No | Yes | Yes | Yes | Yes | |
| ECDHE-PSK (forward secrecy) | No | No | Yes | Yes | Yes | Yes | |
| SRP | No | No | Yes | Yes | Yes | ||
| SRP-DSS | No | No | Yes | Yes | Yes | ||
| SRP-RSA | No | No | Yes | Yes | Yes | ||
| Kerberos | No | No | Yes | Yes | Yes | ||
| DH-ANON (insecure) | No | Yes | Yes | Yes | Yes | ||
| ECDH-ANON (insecure) | No | No | Yes | Yes | Yes | ||
| GOST R 34.10-94 / 34.10-2001[57] | No | No | Yes | Yes | Yes | Proposed in RFC drafts |
Cipher[edit]
| Cipher | Protocol version | Status | |||||||
|---|---|---|---|---|---|---|---|---|---|
| Type | Algorithm | Nominal strength (bits) | SSL 2.0 | SSL 3.0 [n 1][n 2][n 3][n 4] | TLS 1.0 [n 1][n 3] | TLS 1.1 [n 1] | TLS 1.2 [n 1] | TLS 1.3 | |
| Block cipher with mode of operation | AES GCM[58][n 5] | 256, 128 | N/A | N/A | N/A | N/A | Secure | Secure | Defined for TLS 1.2 in RFCs |
| AES CCM[59][n 5] | N/A | N/A | N/A | N/A | Secure | Secure | |||
| AES CBC[n 6] | N/A | Insecure | Depends on mitigations | Depends on mitigations | Depends on mitigations | N/A | |||
| Camellia GCM[60][n 5] | 256, 128 | N/A | N/A | N/A | N/A | Secure | N/A | ||
| Camellia CBC[61][n 6] | N/A | Insecure | Depends on mitigations | Depends on mitigations | Depends on mitigations | N/A | |||
| ARIA GCM[62][n 5] | 256, 128 | N/A | N/A | N/A | N/A | Secure | N/A | ||
| ARIA CBC[62][n 6] | N/A | N/A | Depends on mitigations | Depends on mitigations | Depends on mitigations | N/A | |||
| SEED CBC[63][n 6] | 128 | N/A | Insecure | Depends on mitigations | Depends on mitigations | Depends on mitigations | N/A | ||
| 3DES EDE CBC[n 6][n 7] | 112[n 8] | Insecure | Insecure | Insecure | Insecure | Insecure | N/A | ||
| SM4 GCM[67][n 5] | 128 | N/A | N/A | N/A | N/A | N/A | Secure | Defined for TLS 1.3 in RFC 8998 | |
| SM4 CCM[68][n 5] | N/A | N/A | N/A | N/A | N/A | Secure | |||
| GOST 28147-89 CNT[57][n 7] | 256 | N/A | N/A | Insecure | Insecure | Insecure | N/A | Defined in RFC 4357 | |
| IDEA CBC[n 6][n 7][n 9] | 128 | Insecure | Insecure | Insecure | Insecure | N/A | N/A | Removed from TLS 1.2 | |
| DES CBC[n 6][n 7][n 9] | 56 | Insecure | Insecure | Insecure | Insecure | N/A | N/A | ||
| 40[n 10] | Insecure | Insecure | Insecure | N/A | N/A | N/A | Forbidden in TLS 1.1 and later | ||
| RC2 CBC[n 6][n 7] | 40[n 10] | Insecure | Insecure | Insecure | N/A | N/A | N/A | ||
| Stream cipher | ChaCha20-Poly1305[70][n 5] | 256 | N/A | N/A | N/A | N/A | Secure | Secure | Defined for TLS 1.2 in RFCs |
| RC4[n 11] | 128 | Insecure | Insecure | Insecure | Insecure | Insecure | N/A | Prohibited in all versions of TLS by RFC 7465 | |
| 40[n 10] | Insecure | Insecure | Insecure | N/A | N/A | N/A | |||
| None | Null[n 12] | – | Insecure | Insecure | Insecure | Insecure | Insecure | N/A | Defined for TLS 1.2 in RFCs |
- Notes
- ^ Jump up to:a b c d RFC 5746 must be implemented to fix a renegotiation flaw that would otherwise break this protocol.
- ^ If libraries implement fixes listed in RFC 5746, this violates the SSL 3.0 specification, which the IETF cannot change unlike TLS. Most current libraries implement the fix and disregard the violation that this causes.
- ^ Jump up to:a b The BEAST attack breaks all block ciphers (CBC ciphers) used in SSL 3.0 and TLS 1.0 unless mitigated by the client and/or the server. See § Web browsers.
- ^ The POODLE attack breaks all block ciphers (CBC ciphers) used in SSL 3.0 unless mitigated by the client and/or the server. See § Web browsers.
- ^ Jump up to:a b c d e f g AEAD ciphers (such as GCM and CCM) can only be used in TLS 1.2 or later.
- ^ Jump up to:a b c d e f g h CBC ciphers can be attacked with the Lucky Thirteen attack if the library is not written carefully to eliminate timing side channels.
- ^ Jump up to:a b c d e The Sweet32 attack breaks block ciphers with a block size of 64 bits.[64]
- ^ Although the key length of 3DES is 168 bits, effective security strength of 3DES is only 112 bits,[65] which is below the recommended minimum of 128 bits.[66]
- ^ Jump up to:a b IDEA and DES have been removed from TLS 1.2.[69]
- ^ Jump up to:a b c 40-bit strength cipher suites were intentionally designed with reduced key lengths to comply with since-rescinded US regulations forbidding the export of cryptographic software containing certain strong encryption algorithms (see Export of cryptography from the United States). These weak suites are forbidden in TLS 1.1 and later.
- ^ Use of RC4 in all versions of TLS is prohibited by RFC 7465(because RC4 attacks weaken or break RC4 used in SSL/TLS).
- ^ Authentication only, no encryption.
Data integrity[edit]
A message authentication code (MAC) is used for data integrity. HMAC is used for CBC mode of block ciphers. Authenticated encryption (AEAD) such as GCM mode and CCM mode uses AEAD-integrated MAC and doesn't use HMAC.[71] HMAC-based PRF, or HKDF is used for TLS handshake.
| Algorithm | SSL 2.0 | SSL 3.0 | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 | Status |
|---|---|---|---|---|---|---|---|
| HMAC-MD5 | Yes | Yes | Yes | Yes | Yes | No | Defined for TLS 1.2 in RFCs |
| HMAC-SHA1 | No | Yes | Yes | Yes | Yes | No | |
| HMAC-SHA256/384 | No | No | No | No | Yes | No | |
| AEAD | No | No | No | No | Yes | Yes | |
| GOST 28147-89 IMIT[57] | No | No | Yes | Yes | Yes | Proposed in RFC drafts | |
| GOST R 34.11-94[57] | No | No | Yes | Yes | Yes |
Applications and adoption[edit]
In applications design, TLS is usually implemented on top of Transport Layer protocols, encrypting all of the protocol-related data of protocols such as HTTP, FTP, SMTP, NNTP and XMPP.
Historically, TLS has been used primarily with reliable transport protocols such as the Transmission Control Protocol (TCP). However, it has also been implemented with datagram-oriented transport protocols, such as the User Datagram Protocol (UDP) and the Datagram Congestion Control Protocol (DCCP), usage of which has been standardized independently using the term Datagram Transport Layer Security (DTLS).
Websites[edit]
A primary use of TLS is to secure World Wide Web traffic between a website and a web browser encoded with the HTTP protocol. This use of TLS to secure HTTP traffic constitutes the HTTPS protocol.[72]
| Protocol version | Website support[73] | Security[73][74] |
|---|---|---|
| SSL 2.0 | 0.4% | Insecure |
| SSL 3.0 | 3.0% | Insecure[75] |
| TLS 1.0 | 43.8% | Deprecated[8][9][10] |
| TLS 1.1 | 47.8% | Deprecated[8][9][10] |
| TLS 1.2 | 99.6% | Depends on cipher[n 1] and client mitigations[n 2] |
| TLS 1.3 | 49.7% | Secure |
- Notes
- ^ see § Cipher table above
- ^ see § Web browsers and § Attacks against TLS/SSL sections
Web browsers[edit]
As of April 2016, the latest versions of all major web browsers support TLS 1.0, 1.1, and 1.2, and have them enabled by default. However, not all supported Microsoft operating systems support the latest version of IE. Additionally, many Microsoft operating systems currently support multiple versions of IE, but this has changed according to Microsoft's Internet Explorer Support Lifecycle Policy FAQ, "beginning January 12, 2016, only the most current version of Internet Explorer available for a supported operating system will receive technical support and security updates." The page then goes on to list the latest supported version of IE at that date for each operating system. The next critical date would be when an operating system reaches the end of life stage, which is in Microsoft's Windows lifecycle fact sheet.
Mitigations against known attacks are not enough yet:
- Mitigations against POODLE attack: some browsers already prevent fallback to SSL 3.0; however, this mitigation needs to be supported by not only clients but also servers. Disabling SSL 3.0 itself, implementation of "anti-POODLE record splitting", or denying CBC ciphers in SSL 3.0 is required.
- Google Chrome: complete (TLS_FALLBACK_SCSV is implemented since version 33, fallback to SSL 3.0 is disabled since version 39, SSL 3.0 itself is disabled by default since version 40. Support of SSL 3.0 itself was dropped since version 44.)
- Mozilla Firefox: complete (support of SSL 3.0 itself is dropped since version 39. SSL 3.0 itself is disabled by default and fallback to SSL 3.0 are disabled since version 34, TLS_FALLBACK_SCSV is implemented since version 35. In ESR, SSL 3.0 itself is disabled by default and TLS_FALLBACK_SCSV is implemented since ESR 31.3.)
- Internet Explorer: partial (only in version 11, SSL 3.0 is disabled by default since April 2015. Version 10 and older are still vulnerable against POODLE.)
- Opera: complete (TLS_FALLBACK_SCSV is implemented since version 20, "anti-POODLE record splitting", which is effective only with client-side implementation, is implemented since version 25, SSL 3.0 itself is disabled by default since version 27. Support of SSL 3.0 itself will be dropped since version 31.)
- Safari: complete (only on OS X 10.8 and later and iOS 8, CBC ciphers during fallback to SSL 3.0 is denied, but this means it will use RC4, which is not recommended as well. Support of SSL 3.0 itself is dropped on OS X 10.11 and later and iOS 9.)
- Mitigation against RC4 attacks:
- Google Chrome disabled RC4 except as a fallback since version 43. RC4 is disabled since Chrome 48.
- Firefox disabled RC4 except as a fallback since version 36. Firefox 44 disabled RC4 by default.
- Opera disabled RC4 except as a fallback since version 30. RC4 is disabled since Opera 35.
- Internet Explorer for Windows 7 / Server 2008 R2 and for Windows 8 / Server 2012 have set the priority of RC4 to lowest and can also disable RC4 except as a fallback through registry settings. Internet Explorer 11 Mobile 11 for Windows Phone 8.1 disable RC4 except as a fallback if no other enabled algorithm works. Edge and IE 11 disable RC4 completely in August 2016.
- Mitigation against FREAK attack:
- The Android Browser included with Android 4.0 and older is still vulnerable to the FREAK attack.
- Internet Explorer 11 Mobile is still vulnerable to the FREAK attack.
- Google Chrome, Internet Explorer (desktop), Safari (desktop & mobile), and Opera (mobile) have FREAK mitigations in place.
- Mozilla Firefox on all platforms and Google Chrome on Windows were not affected by FREAK.
| Browser | Version | Platforms | SSL protocols | TLS protocols | Certificate support | Vulnerabilities fixed[n 1] | Protocol selection by user [n 2] | ||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV [n 3][76] | SHA-2 [77] | ECDSA [78] | BEAST[n 4] | CRIME[n 5] | POODLE (SSLv3)[n 6] | RC4[n 7] | FREAK[79][80] | Logjam | |||||
| Google Chrome (Chrome for Android) [n 8] [n 9] |
1–9 | Windows (7+) macOS (10.11+) Linux Android (5.0+) iOS (12.2+) Chrome OS |
Disabled by default | Enabled by default | Yes | No | No | No | Yes (only desktop) |
needs SHA-2 compatible OS[77] | needs ECC compatible OS[78] | Not affected [85] |
Vulnerable (HTTPS) |
Vulnerable | Vulnerable | Vulnerable (except Windows) |
Vulnerable | Yes[n 10] | |
| 10–20 | No[86] | Enabled by default | Yes | No | No | No | Yes (only desktop) |
needs SHA-2 compatible OS[77] | needs ECC compatible OS[78] | Not affected | Vulnerable (HTTPS/SPDY) |
Vulnerable | Vulnerable | Vulnerable (except Windows) |
Vulnerable | Yes[n 10] | |||
| 21 | No | Enabled by default | Yes | No | No | No | Yes (only desktop) |
needs SHA-2 compatible OS[77] | needs ECC compatible OS[78] | Not affected | Mitigated [87] |
Vulnerable | Vulnerable | Vulnerable (except Windows) |
Vulnerable | Yes[n 10] | |||
| 22–29 | No | Enabled by default | Yes | Yes[88] | No[88][89][90][91] | No | Yes (only desktop) |
needs SHA-2 compatible OS[77] | needs ECC compatible OS[78] | Not affected | Mitigated | Vulnerable | Vulnerable | Vulnerable (except Windows) |
Vulnerable | Temporary [n 11] |
|||
| 30–32 | No | Enabled by default | Yes | Yes | Yes[89][90][91] | No | Yes (only desktop) |
needs SHA-2 compatible OS[77] | needs ECC compatible OS[78] | Not affected | Mitigated | Vulnerable | Vulnerable | Vulnerable (except Windows) |
Vulnerable | Temporary [n 11] |
|||
| 33–37 | No | Enabled by default | Yes | Yes | Yes | No | Yes (only desktop) |
needs SHA-2 compatible OS[77] | needs ECC compatible OS[78] | Not affected | Mitigated | Partly mitigated [n 12] |
Lowest priority [94][95][96] |
Vulnerable (except Windows) |
Vulnerable | Temporary [n 11] |
|||
| 38, 39 | No | Enabled by default | Yes | Yes | Yes | No | Yes (only desktop) |
Yes | needs ECC compatible OS[78] | Not affected | Mitigated | Partly mitigated | Lowest priority | Vulnerable (except Windows) |
Vulnerable | Temporary [n 11] |
|||
| 40 | No | Disabled by default[93][97] | Yes | Yes | Yes | No | Yes (only desktop) |
Yes | needs ECC compatible OS[78] | Not affected | Mitigated | Mitigated [n 13] |
Lowest priority | Vulnerable (except Windows) |
Vulnerable | Yes[n 14] | |||
| 41, 42 | No | Disabled by default | Yes | Yes | Yes | No | Yes (only desktop) |
Yes | needs ECC compatible OS[78] | Not affected | Mitigated | Mitigated | Lowest priority | Mitigated | Vulnerable | Yes[n 14] | |||
| 43 | No | Disabled by default | Yes | Yes | Yes | No | Yes (only desktop) |
Yes | needs ECC compatible OS[78] | Not affected | Mitigated | Mitigated | Only as fallback [n 15][98] |
Mitigated | Vulnerable | Yes[n 14] | |||
| 44–47 | No | No[99] | Yes | Yes | Yes | No | Yes (only desktop) |
Yes | needs ECC compatible OS[78] | Not affected | Mitigated | Not affected | Only as fallback [n 15] |
Mitigated | Mitigated[100] | Temporary [n 11] |
|||
| 48, 49 | No | No | Yes | Yes | Yes | No | Yes (only desktop) |
Yes | needs ECC compatible OS[78] | Not affected | Mitigated | Not affected | Disabled by default[n 16][101][102] | Mitigated | Mitigated | Temporary [n 11] |
|||
| 50–53 | No | No | Yes | Yes | Yes | No | Yes (only desktop) |
Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16][101][102] | Mitigated | Mitigated | Temporary [n 11] |
|||
| 54–66 | No | No | Yes | Yes | Yes | Disabled by default (draft version) |
Yes (only desktop) |
Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16][101][102] | Mitigated | Mitigated | Temporary [n 11] |
|||
| 67–69 | No | No | Yes | Yes | Yes | Yes (draft version) |
Yes (only desktop) |
Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16][101][102] | Mitigated | Mitigated | Temporary [n 11] |
|||
| 70–83 | No | No | Yes | Yes | Yes | Yes | Yes (only desktop) |
Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16][101][102] | Mitigated | Mitigated | Temporary [n 11] |
|||
| 84–90 | No | No | Warn by default | Warn by default | Yes | Yes | Yes (only desktop) |
Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16][101][102] | Mitigated | Mitigated | Temporary [n 11] |
|||
| 91–95 | No | No | No[103] | No[103] | Yes | Yes | Yes (only desktop) |
Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16][101][102] | Mitigated | Mitigated | Temporary [n 11] |
|||
| ESC 96 | 96 | ||||||||||||||||||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Microsoft Edge (Chromium-based) OS-independent |
79–83 | Windows (7+) macOS (10.12+) Linux Android (4.4+) iOS (11.0+) |
No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default | Mitigated | Mitigated | Yes[n 10] | |
| 84–90 | No | No | Warn by default | Warn by default | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default | Mitigated | Mitigated | Yes[n 10] | |||
| 91-95 | No | No | No[104] | No[104] | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default | Mitigated | Mitigated | Yes[n 10] | |||
| ESC 96 | 96 | ||||||||||||||||||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Mozilla Firefox (Firefox for mobile) [n 17] |
1.0, 1.5 | Windows (7+) macOS (10.12+) Linux Android (5.0+) iOS (11.4+) ESR only for: Windows (7+) macOS (10.12+) Linux |
Enabled by default [105] |
Enabled by default [105] |
Yes[105] | No | No | No | No | Yes[77] | No | Not affected [106] |
Not affected | Vulnerable | Vulnerable | Not affected | Vulnerable | Yes[n 10] | |
| 2 | Disabled by default [105][107] |
Enabled by default | Yes | No | No | No | No | Yes | Yes[78] | Not affected | Not affected | Vulnerable | Vulnerable | Not affected | Vulnerable | Yes[n 10] | |||
| 3–7 | Disabled by default | Enabled by default | Yes | No | No | No | Yes | Yes | Yes | Not affected | Not affected | Vulnerable | Vulnerable | Not affected | Vulnerable | Yes[n 10] | |||
| 8–10 ESR 10 |
No[107] | Enabled by default | Yes | No | No | No | Yes | Yes | Yes | Not affected | Not affected | Vulnerable | Vulnerable | Not affected | Vulnerable | Yes[n 10] | |||
| 11–14 | No | Enabled by default | Yes | No | No | No | Yes | Yes | Yes | Not affected | Vulnerable (SPDY)[87] |
Vulnerable | Vulnerable | Not affected | Vulnerable | Yes[n 10] | |||
| 15–22 ESR 17.0–17.0.10 |
No | Enabled by default | Yes | No | No | No | Yes | Yes | Yes | Not affected | Mitigated | Vulnerable | Vulnerable | Not affected | Vulnerable | Yes[n 10] | |||
| ESR 17.0.11 | No | Enabled by default | Yes | No | No | No | Yes | Yes | Yes | Not affected | Mitigated | Vulnerable | Lowest priority [108][109] |
Not affected | Vulnerable | Yes[n 10] | |||
| 23 | No | Enabled by default | Yes | Disabled by default [110] |
No | No | Yes | Yes | Yes | Not affected | Mitigated | Vulnerable | Vulnerable | Not affected | Vulnerable | Yes[n 18] | |||
| 24, 25.0.0 ESR 24.0–24.1.0 |
No | Enabled by default | Yes | Disabled by default | Disabled by default [111] |
No | Yes | Yes | Yes | Not affected | Mitigated | Vulnerable | Vulnerable | Not affected | Vulnerable | Yes[n 18] | |||
| 25.0.1, 26 ESR 24.1.1 |
No | Enabled by default | Yes | Disabled by default | Disabled by default | No | Yes | Yes | Yes | Not affected | Mitigated | Vulnerable | Lowest priority [108][109] |
Not affected | Vulnerable | Yes[n 18] | |||
| 27–33 ESR 31.0–31.2 |
No | Enabled by default | Yes | Yes[112][113] | Yes[114][113] | No | Yes | Yes | Yes | Not affected | Mitigated | Vulnerable | Lowest priority | Not affected | Vulnerable | Yes[n 18] | |||
| 34, 35 ESR 31.3–31.7 |
No | Disabled by default [115][116] |
Yes | Yes | Yes | No | Yes | Yes | Yes | Not affected | Mitigated | Mitigated [n 19] |
Lowest priority | Not affected | Vulnerable | Yes[n 18] | |||
| ESR 31.8 | No | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Not affected | Mitigated | Mitigated | Lowest priority | Not affected | Mitigated[119] | Yes[n 18] | |||
| 36–38 ESR 38.0 |
No | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Not affected | Mitigated | Mitigated | Only as fallback [n 15][120] |
Not affected | Vulnerable | Yes[n 18] | |||
| ESR 38.1–38.8 | No | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Not affected | Mitigated | Mitigated | Only as fallback [n 15] |
Not affected | Mitigated[119] | Yes[n 18] | |||
| 39–43 | No | No[121] | Yes | Yes | Yes | No | Yes | Yes | Yes | Not affected | Mitigated | Not affected | Only as fallback [n 15] |
Not affected | Mitigated[119] | Yes[n 18] | |||
| 44–48 ESR 45 |
No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16][122][123][124][125] | Not affected | Mitigated | Yes[n 18] | |||
| 49–59 ESR 52 |
No | No | Yes | Yes | Yes | Disabled by default (draft version)[126] |
Yes | Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16] | Not affected | Mitigated | Yes[n 18] | |||
| 60–62 ESR 60 |
No | No | Yes | Yes | Yes | Yes (draft version) |
Yes | Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16] | Not affected | Mitigated | Yes[n 18] | |||
| 63–77 ESR 68 |
No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16] | Not affected | Mitigated | Yes[n 18] | |||
| 78–94 ESR 78.0 ESR 91.0–91.3 |
No | No | Disabled by default[127] | Disabled by default[127] | Yes | Yes | Yes | Yes | Yes | Not affected | Mitigated | Not affected | Disabled by default[n 16] | Not affected | Mitigated | Yes[n 18] | |||
| ESR 91.4 | 95 | ||||||||||||||||||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Microsoft Internet Explorer (1–10) [n 20] |
1.x | Windows 3.1, 95, NT,[n 21][n 22] Mac OS 7, 8 |
No SSL/TLS support | ||||||||||||||||
| 2 | Yes | No | No | No | No | No | No | No | No | No SSL 3.0 or TLS support | Vulnerable | Vulnerable | Vulnerable | N/A | |||||
| 3 | Yes | Yes[130] | No | No | No | No | No | No | No | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | Unknown | |||
| 4, 5, 6 | Windows 3.1, 95, 98, NT, 2000[n 21][n 22] Mac OS 7.1, 8, X, Solaris, HP-UX |
Enabled by default | Enabled by default | Disabled by default [130] |
No | No | No | No | No | No | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | Yes[n 10] | ||
| 6 | Windows XP[n 22] | Enabled by default | Enabled by default | Disabled by default | No | No | No | No | Yes (since SP3) [n 23][131] |
No | Mitigated | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | Yes[n 10] | ||
| 7, 8 | Disabled by default [132] |
Enabled by default | Yes[132] | No | No | No | Yes | Yes (since SP3) [n 23][131] |
No | Mitigated | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | Yes[n 10] | |||
| 6 | Server 2003[n 22] | Enabled by default | Enabled by default | Disabled by default | No | No | No | No | Yes (KB938397+KB968730) [n 23][131] |
No | Mitigated | Not affected | Vulnerable | Vulnerable | Mitigated [135] |
Mitigated [136] |
Yes[n 10] | ||
| 7, 8 | Disabled by default [132] |
Enabled by default | Yes[132] | No | No | No | Yes | Yes (KB938397+KB968730) [n 23][131] |
No | Mitigated | Not affected | Vulnerable | Vulnerable | Mitigated [135] |
Mitigated [136] |
Yes[n 10] | |||
| 7, 8, 9 | Windows Vista | Disabled by default | Enabled by default | Yes | No | No | No | Yes | Yes | Yes[78] | Mitigated | Not affected | Vulnerable | Vulnerable | Mitigated [135] |
Mitigated [136] |
Yes[n 10] | ||
| 7, 8, 9 | Server 2008 | Disabled by default | Enabled by default | Yes | Disabled by default[137] (KB4019276) |
Disabled by default[137] (KB4019276) |
No | Yes | Yes | Yes[78] | Mitigated | Not affected | Vulnerable | Vulnerable | Mitigated [135] |
Mitigated [136] |
Yes[n 10] | ||
| 8, 9, 10 | Windows 7 / 8 Server 2008 R2 / 2012 |
Disabled by default | Enabled by default | Yes | Disabled by default [138] |
Disabled by default [138] |
No | Yes | Yes | Yes | Mitigated | Not affected | Vulnerable | Lowest priority [139][n 24] |
Mitigated [135] |
Mitigated [136] |
Yes[n 10] | ||
| Internet Explorer 11 [n 20] |
11 | Windows 7 Server 2008 R2 |
Disabled by default | Disabled by default [n 25] |
Yes | Yes[141] | Yes[141] | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated [n 25] |
Disabled by default[145] | Mitigated [135] |
Mitigated [136] |
Yes[n 10] | |
| 11[146] | Windows 8.1 | Disabled by default | Disabled by default [n 25] |
Yes | Yes[141] | Yes[141] | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated [n 25] |
Disabled by default[n 16] | Mitigated [135] |
Mitigated [136] |
Yes[n 10] | ||
| Server 2012 Server 2012 R2 |
|||||||||||||||||||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Microsoft Edge (12–18) (EdgeHTML-based) Client only Internet Explorer 11 [n 20] |
11 | 12–13 | Windows 10 1507–1511 |
Disabled by default | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] |
| 11 | 14–18 (client only) |
Windows 10 1607–2004 Windows Server (SAC) 1709–2004 |
No[147] | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | |
| Internet Explorer 11 [n 20] |
11 | Windows 10 20H2 Windows Server (SAC) 20H2 |
No | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | |
| 11 | Windows 10 21H1 |
No | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | ||
| 11 | Windows 10 21H2 |
No | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | ||
| 11 | Windows 11 | No | Disabled by default | Yes | Yes | Yes | Yes[148] | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | ||
| Internet Explorer 11 [n 20] LTSC Versions |
11 | Windows 10 LTSB 2015 (1507) |
Disabled by default | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | |
| 11 | Windows 10 LTSB 2016 (1607) |
No[147] | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | ||
| 11 | Windows Server 2016 (LTSB / 1607) |
No[147] | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | ||
| 11 | Windows 10 LTSC 2019 (1809) Windows Server 2019 (LTSC / 1809) |
No | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | ||
| 11 | Windows 10 LTSC 2021 (21H2) |
No | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | ||
| 11 | Windows Server 2022 (LTSC) |
No | Disabled by default | Yes | Yes | Yes | Yes[148] | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | Yes[n 10] | ||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Microsoft Internet Explorer Mobile [n 20] |
7, 9 | Windows Phone 7, 7.5, 7.8 | Disabled by default [132] |
Enabled by default | Yes | No [citation needed] |
No [citation needed] |
No | No [citation needed] |
Yes | Yes[149] | Unknown | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | Only with 3rd party tools[n 26] | |
| 10 | Windows Phone 8 | Disabled by default | Enabled by default | Yes | Disabled by default [151] |
Disabled by default [151] |
No | No [citation needed] |
Yes | Yes[152] | Mitigated | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | Only with 3rd party tools[n 26] | ||
| 11 | Windows Phone 8.1 | Disabled by default | Enabled by default | Yes | Yes[153] | Yes[153] | No | No [citation needed] |
Yes | Yes | Mitigated | Not affected | Vulnerable | Only as fallback [n 15][154][155] |
Vulnerable | Vulnerable | Only with 3rd party tools[n 26] | ||
| Microsoft Edge (13–15) (EdgeHTML-based) [n 27] |
13 | Windows 10 Mobile 1511 |
Disabled by default | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | No | |
| 14, 15 | Windows 10 Mobile 1607–1709 |
No[147] | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Apple Safari [n 28] |
1 | Mac OS X 10.2, 10.3 | No[160] | Yes | Yes | No | No | No | No | No | No | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | |
| 2–5 | Mac OS X 10.4, 10.5, Win XP | No | Yes | Yes | No | No | No | since v3.2 | No | No | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 3–5 | Vista, Win 7 | No | Yes | Yes | No | No | No | since v3.2 | No | Yes[149] | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 4–6 | Mac OS X 10.6, 10.7 | No | Yes | Yes | No | No | No | Yes | Yes[77] | Yes[78] | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 6 | OS X 10.8 | No | Yes | Yes | No | No | No | Yes | Yes | Yes[78] | Mitigated [n 29] |
Not affected | Mitigated [n 30] |
Vulnerable [n 30] |
Mitigated [166] |
Vulnerable | No | ||
| 7, 9 | OS X 10.9 | No | Yes | Yes | Yes[167] | Yes[167] | No | Yes | Yes | Yes | Mitigated [162] |
Not affected | Mitigated [n 30] |
Vulnerable [n 30] |
Mitigated [166] |
Vulnerable | No | ||
| 8–10 | OS X 10.10 | No | Yes | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated [n 30] |
Lowest priority [168][n 30] |
Mitigated [166] |
Mitigated [169] |
No | ||
| 9–11 | OS X 10.11 | No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Lowest priority | Mitigated | Mitigated | No | ||
| 10–13 | macOS 10.12, 10.13 | No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| 12–14 | macOS 10.14 | No | No | Yes | Yes | Yes | Yes (since macOS 10.14.4)[170] | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| 13, 14 | 15 | macOS 10.15 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | |
| 14 | 15 | macOS 11 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | |
| 15 | macOS 12 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Apple Safari (mobile) [n 31] |
3 | iPhone OS 1, 2 | No[174] | Yes | Yes | No | No | No | No | No | No | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | |
| 4, 5 | iPhone OS 3, iOS 4 | No | Yes | Yes | No | No | No | Yes[175] | Yes | since iOS 4[149] | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 5, 6 | iOS 5, 6 | No | Yes | Yes | Yes[171] | Yes[171] | No | Yes | Yes | Yes | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 7 | iOS 7 | No | Yes | Yes | Yes | Yes | No | Yes | Yes | Yes[176] | Mitigated [177] |
Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 8 | iOS 8 | No | Yes | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated [n 30] |
Lowest priority [178][n 30] |
Mitigated [179] |
Mitigated [180] |
No | ||
| 9 | iOS 9 | No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Lowest priority | Mitigated | Mitigated | No | ||
| 10, 11 | iOS 10, 11 | No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| 12 | iOS 12 | No | No | Yes | Yes | Yes | Yes (since iOS 12.2)[170] | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| 13, 14 | iOS 13, 14 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| iPadOS 13, 14 | |||||||||||||||||||
| 15 | iOS 15 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| iPadOS 15 | |||||||||||||||||||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV [n 3] | SHA-2 | ECDSA | BEAST[n 4] | CRIME[n 5] | POODLE (SSLv3)[n 6] | RC4[n 7] | FREAK[79][80] | Logjam | Protocol selection by user | |
| Google Android OS [181] |
Android 1.0–4.0.4 | No | Enabled by default | Yes | No | No | No | Unknown | Yes[77] | since 3.0[149][78] | Unknown | Unknown | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| Android 4.1–4.4.4 | No | Enabled by default | Yes | Disabled by default[182] | Disabled by default[182] | No | Unknown | Yes | Yes | Unknown | Unknown | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | |||
| Android 5.0–5.0.2 | No | Enabled by default | Yes | Yes[182][183] | Yes[182][183] | No | Unknown | Yes | Yes | Unknown | Unknown | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | |||
| Android 5.1–5.1.1 | No | Disabled by default [citation needed] |
Yes | Yes | Yes | No | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Only as fallback [n 15] |
Mitigated | Mitigated | No | |||
| Android 6.0–7.1.2 | No | Disabled by default [citation needed] |
Yes | Yes | Yes | No | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 8.0–8.1 | No | No [184] |
Yes | Yes | Yes | No | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 9 | No | No | Yes | Yes | Yes | No | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 10 | No | No | Yes | Yes | Yes | Yes | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 11 | No | No | Yes | Yes | Yes | Yes | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 12 | No | No | Unknown | Unknown | Yes | Yes | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Color or Note | Significance | |
|---|---|---|
| Browser version | Platform | |
| Browser version | Operating system | Future release; under development |
| Browser version | Operating system | Current latest release |
| Browser version | Operating system | Former release; still supported |
| Browser version | Operating system | Former release; long-term support still active, but will end in less than 12 months |
| Browser version | Operating system | Former release; no longer supported |
| n/a | Operating system | Mixed / Unspecified |
| Operating system (Version+) | Minimum required operating system version (for supported versions of the browser) | |
| No longer supported for this operating system | ||
- Notes
- ^ Does the browser have mitigations or is not vulnerable for the known attacks. Note actual security depends on other factors such as negotiated cipher, encryption strength, etc. (see § Cipher table).
- ^ Whether a user or administrator can choose the protocols to be used or not. If yes, several attacks such as BEAST (vulnerable in SSL 3.0 and TLS 1.0) or POODLE (vulnerable in SSL 3.0) can be avoided.
- ^ Jump up to:a b Whether EV SSL and DV SSL (normal SSL) can be distinguished by indicators (green lock icon, green address bar, etc.) or not.
- ^ Jump up to:a b e.g. 1/n-1 record splitting.
- ^ Jump up to:a b e.g. Disabling header compression in HTTPS/SPDY.
- ^ Jump up to:a b
- Complete mitigations; disabling SSL 3.0 itself, "anti-POODLE record splitting". "Anti-POODLE record splitting" is effective only with client-side implementation and valid according to the SSL 3.0 specification, however, it may also cause compatibility issues due to problems in server-side implementations.
- Partial mitigations; disabling fallback to SSL 3.0, TLS_FALLBACK_SCSV, disabling cipher suites with CBC mode of operation. If the server also supports TLS_FALLBACK_SCSV, the POODLE attack will fail against this combination of server and browser, but connections where the server does not support TLS_FALLBACK_SCSV and does support SSL 3.0 will still be vulnerable. If disabling cipher suites with CBC mode of operation in SSL 3.0, only cipher suites with RC4 are available, RC4 attacks become easier.
- When disabling SSL 3.0 manually, POODLE attack will fail.
- ^ Jump up to:a b
- Complete mitigation; disabling cipher suites with RC4.
- Partial mitigations to keeping compatibility with old systems; setting the priority of RC4 to lower.
- ^ Google Chrome (and Chromium) supports TLS 1.0, and TLS 1.1 from version 22 (it was added, then dropped from version 21). TLS 1.2 support has been added, then dropped from Chrome 29.[81][82][83]
- ^ Uses the TLS implementation provided by BoringSSL for Android, OS X, and Windows[84] or by NSS for Linux. Google is switching the TLS library used in Chrome to BoringSSL from NSS completely.
- ^ Jump up to:a b c d e f g h i j k l m n o p q r s t u v w x y z aa ab ac ad ae af agah ai configure enabling/disabling of each protocols via setting/option (menu name is dependent on browsers)
- ^ Jump up to:a b c d e f g h i j k l configure the maximum and the minimum version of enabling protocols with command-line option
- ^ TLS_FALLBACK_SCSV is implemented.[92] Fallback to SSL 3.0 is disabled since version 39.[93]
- ^ In addition to TLS_FALLBACK_SCSV and disabling a fallback to SSL 3.0, SSL 3.0 itself is disabled by default.[93]
- ^ Jump up to:a b c configure the minimum version of enabling protocols via chrome://flags[97] (the maximum version can be configured with command-line option)
- ^ Jump up to:a b c d e f g Only when no cipher suites with other than RC4 is available, cipher suites with RC4 will be used as a fallback.
- ^ Jump up to:a b c d e f g h i j k l m n o p q r s t u v w x y z aa ab ac ad ae af agah ai aj All RC4 cipher suites are disabled by default.
- ^ Uses the TLS implementation provided by NSS. As of Firefox 22, Firefox supports only TLS 1.0 despite the bundled NSS supporting TLS 1.1. Since Firefox 23, TLS 1.1 can be enabled, but was not enabled by default due to issues. Firefox 24 has TLS 1.2 support disabled by default. TLS 1.1 and TLS 1.2 have been enabled by default in Firefox 27 release.
- ^ Jump up to:a b c d e f g h i j k l m n configure the maximum and the minimum version of enabling protocols via about:config
- ^ SSL 3.0 itself is disabled by default.[115] In addition, fallback to SSL 3.0 is disabled since version 34,[117] and TLS_FALLBACK_SCSV is implemented since 35.0 and ESR 31.3.[115][118]
- ^ Jump up to:a b c d e f IE uses the TLS implementation of the Microsoft Windows operating system provided by the SChannel security support provider. TLS 1.1 and 1.2 are disabled by default until IE11.[128][129]
- ^ Jump up to:a b Windows NT 3.1 supports IE 1–2, Windows NT 3.5 supports IE 1–3, Windows NT 3.51 and Windows NT 4.0 supports IE 1–6
- ^ Jump up to:a b c d Windows XP as well as Server 2003 and older support only weak ciphers like 3DES and RC4 out of the box.[133] The weak ciphers of these SChannel version are not only used for IE, but also for other Microsoft products running on this OS, like Office or Windows Update. Only Windows Server 2003 can get a manual update to support AES ciphers by KB948963[134]
- ^ Jump up to:a b c d MS13-095 or MS14-049 for Windows Server 2003, Windows XP x64 and Windows XP SP3 (32-bit)
- ^ RC4 can be disabled except as a fallback (Only when no cipher suites with other than RC4 is available, cipher suites with RC4 will be used as a fallback.)[140]
- ^ Jump up to:a b c d Fallback to SSL 3.0 is sites blocked by default in Internet Explorer 11 for Protected Mode.[142][143] SSL 3.0 is disabled by default in Internet Explorer 11 since April 2015.[144]
- ^ Jump up to:a b c Could be disabled via registry editing but need 3rd Party tools to do this.[150]
- ^ Edge (formerly known as Project Spartan) is based on a fork of the Internet Explorer 11 rendering engine.
- ^ Safari uses the operating system implementation on Mac OS X, Windows (XP, Vista, 7)[156] with unknown version,[157] Safari 5 is the last version available for Windows. OS X 10.8 on have SecureTransport support for TLS 1.1 and 1.2[158] Qualys SSL report simulates Safari 5.1.9 connecting with TLS 1.0 not 1.1 or 1.2[159]
- ^ In September 2013, Apple implemented BEAST mitigation in OS X 10.8 (Mountain Lion), but it was not turned on by default, resulting in Safari still being theoretically vulnerable to the BEAST attack on that platform.[161][162] BEAST mitigation has been enabled by default from OS X 10.8.5 updated in February 2014.[163]
- ^ Jump up to:a b c d e f g h Because Apple removed support for all CBC protocols in SSL 3.0 to mitigate POODLE,[164][165] this leaves only RC4, which is also completely broken by the RC4 attacks in SSL 3.0.
- ^ Mobile Safari and third-party software utilizing the system UIWebView library use the iOS operating system implementation, which supports TLS 1.2 as of iOS 5.0.[171][172][173]
Libraries[edit]
Most SSL and TLS programming libraries are free and open source software.
- BoringSSL, a fork of OpenSSL for Chrome/Chromium and Android as well as other Google applications.
- Botan, a BSD-licensed cryptographic library written in C++.
- BSAFE Micro Edition Suite: a multi-platform implementation of TLS written in C using a FIPS-validated cryptographic module
- BSAFE SSL-J: a TLS library providing both a proprietary API and JSSE API, using FIPS-validated cryptographic module
- cryptlib: a portable open source cryptography library (includes TLS/SSL implementation)
- Delphi programmers may use a library called Indy which utilizes OpenSSL or alternatively ICS which supports TLS 1.3 now.
- GnuTLS: a free implementation (LGPL licensed)
- Java Secure Socket Extension: a Java implementation included in the Java Runtime Environment supported TLS 1.1 and 1.2 starting with Java 7. (TLS 1.1/1.2 were initially disabled by default for client on Java 7, but were enabled in January 2017.[185]) Java 11 supports TLS 1.3.[186][187]
- LibreSSL: a fork of OpenSSL by OpenBSD project.
- MatrixSSL: a dual licensed implementation
- mbed TLS (previously PolarSSL): A tiny SSL library implementation for embedded devices that is designed for ease of use
- Network Security Services: FIPS 140 validated open source library
- OpenSSL: a free implementation (BSD license with some extensions)
- SChannel: an implementation of SSL and TLS Microsoft Windows as part of its package.
- Secure Transport: an implementation of SSL and TLS used in OS X and iOS as part of their packages.
- wolfSSL (previously CyaSSL): Embedded SSL/TLS Library with a strong focus on speed and size.
| Implementation | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 |
|---|---|---|---|---|---|---|
| Botan | No | No[188] | Yes | Yes | Yes | |
| BSAFE Micro Edition Suite | No | Disabled by default | Yes | Yes | Yes | In development |
| BSAFE SSL-J | No | Disabled by default | Yes | Yes | Yes | Yes |
| cryptlib | No | Disabled by default at compile time | Yes | Yes | Yes | |
| GnuTLS | No[a] | Disabled by default[189] | Yes | Yes | Yes | Yes[190] |
| Java Secure Socket Extension | No[a] | Disabled by default[191] | Yes | Yes | Yes | Yes |
| LibreSSL | No[192] | No[193] | Yes | Yes | Yes | As of version 3.2.2 [194][195] |
| MatrixSSL | No | Disabled by default at compile time[196] | Yes | Yes | Yes | yes (draft version) |
| mbed TLS (previously PolarSSL) | No | Disabled by default[197] | Yes | Yes | Yes | |
| Network Security Services | No[b] | Disabled by default[198] | Yes | Yes[199] | Yes[200] | Yes[201] |
| OpenSSL | No[202] | Enabled by default | Yes | Yes[203] | Yes[203] | Yes[204] |
| SChannel XP / 2003[205] | Disabled by default by MSIE 7 | Enabled by default | Enabled by default by MSIE 7 | No | No | No |
| SChannel Vista[206] | Disabled by default | Enabled by default | Yes | No | No | No |
| SChannel 2008[206] | Disabled by default | Enabled by default | Yes | Disabled by default (KB4019276)[137] | Disabled by default (KB4019276)[137] | No |
| SChannel 7 / 2008 R2[207] | Disabled by default | Disabled by default in MSIE 11 | Yes | Enabled by default by MSIE 11 | Enabled by default by MSIE 11 | No |
| SChannel 8 / 2012[207] | Disabled by default | Enabled by default | Yes | Disabled by default | Disabled by default | No |
| SChannel 8.1 / 2012 R2, 10 v1507 & v1511[207] | Disabled by default | Disabled by default in MSIE 11 | Yes | Yes | Yes | No |
| SChannel 10 v1607 / 2016[147] | No | Disabled by default | Yes | Yes | Yes | No |
| SChannel 10 v1903[208] | No | Disabled by default | Yes | Yes | Yes | No |
| SChannel 10 v21H1[209] | No | Disabled by default | Yes | Yes | Yes | No |
| Secure Transport OS X 10.2–10.8 / iOS 1–4 | Yes | Yes | Yes | No | No | |
| Secure Transport OS X 10.9–10.10 / iOS 5–8 | No[c] | Yes | Yes | Yes[c] | Yes[c] | |
| Secure Transport OS X 10.11 / iOS 9 | No | No[c] | Yes | Yes | Yes | |
| Seed7 TLS/SSL Library | No | Yes | Yes | Yes | Yes | |
| wolfSSL (previously CyaSSL) | No | Disabled by default[210] | Yes | Yes | Yes | Yes[211] |
| Implementation | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 |
- ^
SSL 2.0 client hello is supported even though SSL 2.0 is not supported or is disabled because of the backward compatibilities.
- ^
Server-side implementation of the SSL/TLS protocol still supports processing of received v2-compatible client hello messages.[212]
- ^
Secure Transport: SSL 2.0 was discontinued in OS X 10.8. SSL 3.0 was discontinued in OS X 10.11 and iOS 9. TLS 1.1 and 1.2 are available on iOS 5.0 and later, and OS X 10.9 and later.[213]
A paper presented at the 2012 ACM conference on computer and communications security[215] showed that few applications used some of these SSL libraries correctly, leading to vulnerabilities. According to the authors
"the root cause of most of these vulnerabilities is the terrible design of the APIs to the underlying SSL libraries. Instead of expressing high-level security properties of network tunnels such as confidentiality and authentication, these APIs expose low-level details of the SSL protocol to application developers. As a consequence, developers often use SSL APIs incorrectly, misinterpreting and misunderstanding their manifold parameters, options, side effects, and return values."
Other uses[edit]
The Simple Mail Transfer Protocol (SMTP) can also be protected by TLS. These applications use public key certificates to verify the identity of endpoints.
TLS can also be used for tunnelling an entire network stack to create a VPN, which is the case with OpenVPN and OpenConnect. Many vendors have by now married TLS's encryption and authentication capabilities with authorization. There has also been substantial development since the late 1990s in creating client technology outside of Web-browsers, in order to enable support for client/server applications. Compared to traditional IPsec VPN technologies, TLS has some inherent advantages in firewall and NAT traversal that make it easier to administer for large remote-access populations.
TLS is also a standard method for protecting Session Initiation Protocol (SIP) application signaling. TLS can be used for providing authentication and encryption of the SIP signalling associated with VoIP and other SIP-based applications.[216]
Security[edit]
Attacks against TLS/SSL[edit]
Significant attacks against TLS/SSL are listed below.
In February 2015, IETF issued an informational RFC[217] summarizing the various known attacks against TLS/SSL.
Renegotiation attack[edit]
A vulnerability of the renegotiation procedure was discovered in August 2009 that can lead to plaintext injection attacks against SSL 3.0 and all current versions of TLS.[218] For example, it allows an attacker who can hijack an https connection to splice their own requests into the beginning of the conversation the client has with the web server. The attacker can't actually decrypt the client–server communication, so it is different from a typical man-in-the-middle attack. A short-term fix is for web servers to stop allowing renegotiation, which typically will not require other changes unless client certificate authentication is used. To fix the vulnerability, a renegotiation indication extension was proposed for TLS. It will require the client and server to include and verify information about previous handshakes in any renegotiation handshakes.[219] This extension has become a proposed standard and has been assigned the number RFC 5746. The RFC has been implemented by several libraries.[220][221][222]
Downgrade attacks: FREAK attack and Logjam attack[edit]
A protocol downgrade attack (also called a version rollback attack) tricks a web server into negotiating connections with previous versions of TLS (such as SSLv2) that have long since been abandoned as insecure.
Previous modifications to the original protocols, like False Start[223] (adopted and enabled by Google Chrome[224]) or Snap Start, reportedly introduced limited TLS protocol downgrade attacks[225] or allowed modifications to the cipher suite list sent by the client to the server. In doing so, an attacker might succeed in influencing the cipher suite selection in an attempt to downgrade the cipher suite negotiated to use either a weaker symmetric encryption algorithm or a weaker key exchange.[226] A paper presented at an ACM conference on computer and communications security in 2012 demonstrated that the False Start extension was at risk: in certain circumstances it could allow an attacker to recover the encryption keys offline and to access the encrypted data.[227]
Encryption downgrade attacks can force servers and clients to negotiate a connection using cryptographically weak keys. In 2014, a man-in-the-middle attack called FREAK was discovered affecting the OpenSSL stack, the default Android web browser, and some Safari browsers.[228] The attack involved tricking servers into negotiating a TLS connection using cryptographically weak 512 bit encryption keys.
Logjam is a security exploit discovered in May 2015 that exploits the option of using legacy "export-grade" 512-bit Diffie–Hellman groups dating back to the 1990s.[229] It forces susceptible servers to downgrade to cryptographically weak 512-bit Diffie–Hellman groups. An attacker can then deduce the keys the client and server determine using the Diffie–Hellman key exchange.
Cross-protocol attacks: DROWN[edit]
The DROWN attack is an exploit that attacks servers supporting contemporary SSL/TLS protocol suites by exploiting their support for the obsolete, insecure, SSLv2 protocol to leverage an attack on connections using up-to-date protocols that would otherwise be secure.[230][231] DROWN exploits a vulnerability in the protocols used and the configuration of the server, rather than any specific implementation error. Full details of DROWN were announced in March 2016, together with a patch for the exploit. At that time, more than 81,000 of the top 1 million most popular websites were among the TLS protected websites that were vulnerable to the DROWN attack.[231]
BEAST attack[edit]
On September 23, 2011 researchers Thai Duong and Juliano Rizzo demonstrated a proof of concept called BEAST (Browser Exploit Against SSL/TLS)[232] using a Java applet to violate same origin policy constraints, for a long-known cipher block chaining (CBC) vulnerability in TLS 1.0:[233][234] an attacker observing 2 consecutive ciphertext blocks C0, C1 can test if the plaintext block P1 is equal to x by choosing the next plaintext block P2 = x 






RC4 as a stream cipher is immune to BEAST attack. Therefore, RC4 was widely used as a way to mitigate BEAST attack on the server side. However, in 2013, researchers found more weaknesses in RC4. Thereafter enabling RC4 on server side was no longer recommended.[236]
Chrome and Firefox themselves are not vulnerable to BEAST attack,[85][106] however, Mozilla updated their NSS libraries to mitigate BEAST-like attacks. NSS is used by Mozilla Firefox and Google Chrome to implement SSL. Some web servers that have a broken implementation of the SSL specification may stop working as a result.[237]
Microsoft released Security Bulletin MS12-006 on January 10, 2012, which fixed the BEAST vulnerability by changing the way that the Windows Secure Channel (SChannel) component transmits encrypted network packets from the server end.[238] Users of Internet Explorer (prior to version 11) that run on older versions of Windows (Windows 7, Windows 8 and Windows Server 2008 R2) can restrict use of TLS to 1.1 or higher.
Apple fixed BEAST vulnerability by implementing 1/n-1 split and turning it on by default in OS X Mavericks, released on October 22, 2013.[239]
CRIME and BREACH attacks[edit]
The authors of the BEAST attack are also the creators of the later CRIME attack, which can allow an attacker to recover the content of web cookies when data compression is used along with TLS.[240][241] When used to recover the content of secret authentication cookies, it allows an attacker to perform session hijacking on an authenticated web session.
While the CRIME attack was presented as a general attack that could work effectively against a large number of protocols, including but not limited to TLS, and application-layer protocols such as SPDY or HTTP, only exploits against TLS and SPDY were demonstrated and largely mitigated in browsers and servers. The CRIME exploit against HTTP compression has not been mitigated at all, even though the authors of CRIME have warned that this vulnerability might be even more widespread than SPDY and TLS compression combined. In 2013 a new instance of the CRIME attack against HTTP compression, dubbed BREACH, was announced. Based on the CRIME attack a BREACH attack can extract login tokens, email addresses or other sensitive information from TLS encrypted web traffic in as little as 30 seconds (depending on the number of bytes to be extracted), provided the attacker tricks the victim into visiting a malicious web link or is able to inject content into valid pages the user is visiting (ex: a wireless network under the control of the attacker).[242] All versions of TLS and SSL are at risk from BREACH regardless of the encryption algorithm or cipher used.[243] Unlike previous instances of CRIME, which can be successfully defended against by turning off TLS compression or SPDY header compression, BREACH exploits HTTP compression which cannot realistically be turned off, as virtually all web servers rely upon it to improve data transmission speeds for users.[242] This is a known limitation of TLS as it is susceptible to chosen-plaintext attack against the application-layer data it was meant to protect.
Timing attacks on padding[edit]
Earlier TLS versions were vulnerable against the padding oracle attack discovered in 2002. A novel variant, called the Lucky Thirteen attack, was published in 2013.
Some experts[66] also recommended avoiding Triple-DES CBC. Since the last supported ciphers developed to support any program using Windows XP's SSL/TLS library like Internet Explorer on Windows XP are RC4 and Triple-DES, and since RC4 is now deprecated (see discussion of RC4 attacks), this makes it difficult to support any version of SSL for any program using this library on XP.
A fix was released as the Encrypt-then-MAC extension to the TLS specification, released as RFC 7366.[244] The Lucky Thirteen attack can be mitigated in TLS 1.2 by using only AES_GCM ciphers; AES_CBC remains vulnerable.[citation needed]
POODLE attack[edit]
On October 14, 2014, Google researchers published a vulnerability in the design of SSL 3.0, which makes CBC mode of operation with SSL 3.0 vulnerable to a padding attack (CVE-2014-3566). They named this attack POODLE (Padding Oracle On Downgraded Legacy Encryption). On average, attackers only need to make 256 SSL 3.0 requests to reveal one byte of encrypted messages.[75]
Although this vulnerability only exists in SSL 3.0 and most clients and servers support TLS 1.0 and above, all major browsers voluntarily downgrade to SSL 3.0 if the handshakes with newer versions of TLS fail unless they provide the option for a user or administrator to disable SSL 3.0 and the user or administrator does so[citation needed]. Therefore, the man-in-the-middle can first conduct a version rollback attack and then exploit this vulnerability.[75]
On December 8, 2014, a variant of POODLE was announced that impacts TLS implementations that do not properly enforce padding byte requirements.[245]
RC4 attacks[edit]
Despite the existence of attacks on RC4 that broke its security, cipher suites in SSL and TLS that were based on RC4 were still considered secure prior to 2013 based on the way in which they were used in SSL and TLS. In 2011, the RC4 suite was actually recommended as a work around for the BEAST attack.[246] New forms of attack disclosed in March 2013 conclusively demonstrated the feasibility of breaking RC4 in TLS, suggesting it was not a good workaround for BEAST.[74] An attack scenario was proposed by AlFardan, Bernstein, Paterson, Poettering and Schuldt that used newly discovered statistical biases in the RC4 key table[247] to recover parts of the plaintext with a large number of TLS encryptions.[248][249] An attack on RC4 in TLS and SSL that requires 13 × 220 encryptions to break RC4 was unveiled on 8 July 2013 and later described as "feasible" in the accompanying presentation at a USENIX Security Symposium in August 2013.[250][251] In July 2015, subsequent improvements in the attack make it increasingly practical to defeat the security of RC4-encrypted TLS.[252]
As many modern browsers have been designed to defeat BEAST attacks (except Safari for Mac OS X 10.7 or earlier, for iOS 6 or earlier, and for Windows; see § Web browsers), RC4 is no longer a good choice for TLS 1.0. The CBC ciphers which were affected by the BEAST attack in the past have become a more popular choice for protection.[66] Mozilla and Microsoft recommend disabling RC4 where possible.[253][254] RFC 7465 prohibits the use of RC4 cipher suites in all versions of TLS.
On September 1, 2015, Microsoft, Google and Mozilla announced that RC4 cipher suites would be disabled by default in their browsers (Microsoft Edge, Internet Explorer 11 on Windows 7/8.1/10, Firefox, and Chrome) in early 2016.[255][256][257]
Truncation attack[edit]
A TLS (logout) truncation attack blocks a victim's account logout requests so that the user unknowingly remains logged into a web service. When the request to sign out is sent, the attacker injects an unencrypted TCP FIN message (no more data from sender) to close the connection. The server therefore doesn't receive the logout request and is unaware of the abnormal termination.[258]
Published in July 2013,[259][260] the attack causes web services such as Gmail and Hotmail to display a page that informs the user that they have successfully signed-out, while ensuring that the user's browser maintains authorization with the service, allowing an attacker with subsequent access to the browser to access and take over control of the user's logged-in account. The attack does not rely on installing malware on the victim's computer; attackers need only place themselves between the victim and the web server (e.g., by setting up a rogue wireless hotspot).[258] This vulnerability also requires access to the victim's computer. Another possibility is when using FTP the data connection can have a false FIN in the data stream, and if the protocol rules for exchanging close_notify alerts is not adhered to a file can be truncated.
Unholy PAC attack[edit]
This attack, discovered in mid-2016, exploits weaknesses in the Web Proxy Autodiscovery Protocol (WPAD) to expose the URL that a web user is attempting to reach via a TLS-enabled web link.[261] Disclosure of a URL can violate a user's privacy, not only because of the website accessed, but also because URLs are sometimes used to authenticate users. Document sharing services, such as those offered by Google and Dropbox, also work by sending a user a security token that's included in the URL. An attacker who obtains such URLs may be able to gain full access to a victim's account or data.
The exploit works against almost all browsers and operating systems.
Sweet32 attack[edit]
The Sweet32 attack breaks all 64-bit block ciphers used in CBC mode as used in TLS by exploiting a birthday attack and either a man-in-the-middle attack or injection of a malicious JavaScript into a web page. The purpose of the man-in-the-middle attack or the JavaScript injection is to allow the attacker to capture enough traffic to mount a birthday attack.[262]
Implementation errors: Heartbleed bug, BERserk attack, Cloudflare bug[edit]
The Heartbleed bug is a serious vulnerability specific to the implementation of SSL/TLS in the popular OpenSSL cryptographic software library, affecting versions 1.0.1 to 1.0.1f. This weakness, reported in April 2014, allows attackers to steal private keys from servers that should normally be protected.[263] The Heartbleed bug allows anyone on the Internet to read the memory of the systems protected by the vulnerable versions of the OpenSSL software. This compromises the secret private keys associated with the public certificates used to identify the service providers and to encrypt the traffic, the names and passwords of the users and the actual content. This allows attackers to eavesdrop on communications, steal data directly from the services and users and to impersonate services and users.[264] The vulnerability is caused by a buffer over-read bug in the OpenSSL software, rather than a defect in the SSL or TLS protocol specification.
In September 2014, a variant of Daniel Bleichenbacher's PKCS#1 v1.5 RSA Signature Forgery vulnerability[265] was announced by Intel Security Advanced Threat Research. This attack, dubbed BERserk, is a result of incomplete ASN.1 length decoding of public key signatures in some SSL implementations, and allows a man-in-the-middle attack by forging a public key signature.[266]
In February 2015, after media reported the hidden pre-installation of Superfish adware on some Lenovo notebooks,[267] a researcher found a trusted root certificate on affected Lenovo machines to be insecure, as the keys could easily be accessed using the company name, Komodia, as a passphrase.[268] The Komodia library was designed to intercept client-side TLS/SSL traffic for parental control and surveillance, but it was also used in numerous adware programs, including Superfish, that were often surreptitiously installed unbeknownst to the computer user. In turn, these potentially unwanted programs installed the corrupt root certificate, allowing attackers to completely control web traffic and confirm false websites as authentic.
In May 2016, it was reported that dozens of Danish HTTPS-protected websites belonging to Visa Inc. were vulnerable to attacks allowing hackers to inject malicious code and forged content into the browsers of visitors.[269] The attacks worked because the TLS implementation used on the affected servers incorrectly reused random numbers (nonces) that are intended to be used only once, ensuring that each TLS handshake is unique.[269]
In February 2017, an implementation error caused by a single mistyped character in code used to parse HTML created a buffer overflow error on Cloudflare servers. Similar in its effects to the Heartbleed bug discovered in 2014, this overflow error, widely known as Cloudbleed, allowed unauthorized third parties to read data in the memory of programs running on the servers—data that should otherwise have been protected by TLS.[270]
Survey of websites vulnerable to attacks[edit]
As of July 2021, the Trustworthy Internet Movement estimated the ratio of websites that are vulnerable to TLS attacks.[73]
| Attacks | Security | |||
|---|---|---|---|---|
| Insecure | Depends | Secure | Other | |
| Renegotiation attack | 0.1% support insecure renegotiation |
<0.1% support both |
99.2% support secure renegotiation |
0.7% no support |
| RC4 attacks | 0.4% support RC4 suites used with modern browsers |
6.5% support some RC4 suites |
93.1% no support |
N/A |
| TLS Compression (CRIME attack) | >0.0% vulnerable |
N/A | N/A | N/A |
| Heartbleed | >0.0% vulnerable |
N/A | N/A | N/A |
| ChangeCipherSpec injection attack | 0.1% vulnerable and exploitable |
0.2% vulnerable, not exploitable |
98.5% not vulnerable |
1.2% unknown |
| POODLE attack against TLS (Original POODLE against SSL 3.0 is not included) |
0.1% vulnerable and exploitable |
0.1% vulnerable, not exploitable |
99.8% not vulnerable |
0.2% unknown |
| Protocol downgrade | 6.6% Downgrade defence not supported |
N/A | 72.3% Downgrade defence supported |
21.0% unknown |
Forward secrecy[edit]
Forward secrecy is a property of cryptographic systems which ensures that a session key derived from a set of public and private keys will not be compromised if one of the private keys is compromised in the future.[271] Without forward secrecy, if the server's private key is compromised, not only will all future TLS-encrypted sessions using that server certificate be compromised, but also any past sessions that used it as well (provided of course that these past sessions were intercepted and stored at the time of transmission).[272] An implementation of TLS can provide forward secrecy by requiring the use of ephemeral Diffie–Hellman key exchange to establish session keys, and some notable TLS implementations do so exclusively: e.g., Gmail and other Google HTTPS services that use OpenSSL.[273] However, many clients and servers supporting TLS (including browsers and web servers) are not configured to implement such restrictions.[274][275] In practice, unless a web service uses Diffie–Hellman key exchange to implement forward secrecy, all of the encrypted web traffic to and from that service can be decrypted by a third party if it obtains the server's master (private) key; e.g., by means of a court order.[276]
Even where Diffie–Hellman key exchange is implemented, server-side session management mechanisms can impact forward secrecy. The use of TLS session tickets (a TLS extension) causes the session to be protected by AES128-CBC-SHA256 regardless of any other negotiated TLS parameters, including forward secrecy ciphersuites, and the long-lived TLS session ticket keys defeat the attempt to implement forward secrecy.[277][278][279] Stanford University research in 2014 also found that of 473,802 TLS servers surveyed, 82.9% of the servers deploying ephemeral Diffie–Hellman (DHE) key exchange to support forward secrecy were using weak Diffie–Hellman parameters. These weak parameter choices could potentially compromise the effectiveness of the forward secrecy that the servers sought to provide.[280]
Since late 2011, Google has provided forward secrecy with TLS by default to users of its Gmail service, along with Google Docs and encrypted search, among other services.[281] Since November 2013, Twitter has provided forward secrecy with TLS to users of its service.[282] As of August 2019, about 80% of TLS-enabled websites are configured to use cipher suites that provide forward secrecy to most web browsers.[73]
TLS interception[edit]
TLS interception (or HTTPS interception if applied particularly to that protocol) is the practice of intercepting an encrypted data stream in order to decrypt it, read and possibly manipulate it, and then re-encrypt it and send the data on its way again. This is done by way of a "transparent proxy": the interception software terminates the incoming TLS connection, inspects the HTTP plaintext, and then creates a new TLS connection to the destination.[283]
TLS / HTTPS interception is used as an information security measure by network operators in order to be able to scan for and protect against the intrusion of malicious content into the network, such as computer viruses and other malware.[283] Such content could otherwise not be detected as long as it is protected by encryption, which is increasingly the case as a result of the routine use of HTTPS and other secure protocols.
A significant drawback of TLS / HTTPS interception is that it introduces new security risks of its own. One notable limitation is that it provides a point where network traffic is available unencrypted thus giving attackers an incentive to attack this point in particular in order to gain access to otherwise secure content. The interception also allows the network operator, or persons who gain access to its interception system, to perform man-in-the-middle attacks against network users. A 2017 study found that "HTTPS interception has become startlingly widespread, and that interception products as a class have a dramatically negative impact on connection security".[283]
Protocol details[edit]
The TLS protocol exchanges records, which encapsulate the data to be exchanged in a specific format (see below). Each record can be compressed, padded, appended with a message authentication code (MAC), or encrypted, all depending on the state of the connection. Each record has a content type field that designates the type of data encapsulated, a length field and a TLS version field. The data encapsulated may be control or procedural messages of the TLS itself, or simply the application data needed to be transferred by TLS. The specifications (cipher suite, keys etc.) required to exchange application data by TLS, are agreed upon in the "TLS handshake" between the client requesting the data and the server responding to requests. The protocol therefore defines both the structure of payloads transferred in TLS and the procedure to establish and monitor the transfer.
TLS handshake[edit]
When the connection starts, the record encapsulates a "control" protocol – the handshake messaging protocol (content type 22). This protocol is used to exchange all the information required by both sides for the exchange of the actual application data by TLS. It defines the format of messages and the order of their exchange. These may vary according to the demands of the client and server – i.e., there are several possible procedures to set up the connection. This initial exchange results in a successful TLS connection (both parties ready to transfer application data with TLS) or an alert message (as specified below).
Basic TLS handshake[edit]
A typical connection example follows, illustrating a handshake where the server (but not the client) is authenticated by its certificate:
- Negotiation phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested cipher suites and suggested compression methods. If the client is attempting to perform a resumed handshake, it may send a session ID. If the client can use Application-Layer Protocol Negotiation, it may include a list of supported application protocols, such as HTTP/2.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, cipher suite and compression method from the choices offered by the client. To confirm or allow resumed handshakes the server may send a session ID. The chosen protocol version should be the highest that both the client and server support. For example, if the client supports TLS version 1.1 and the server supports version 1.2, version 1.1 should be selected; version 1.2 should not be selected.
- The server sends its Certificate message (depending on the selected cipher suite, this may be omitted by the server).[284]
- The server sends its ServerKeyExchange message (depending on the selected cipher suite, this may be omitted by the server). This message is sent for all DHE, ECDHE and DH_anon cipher suites.[7]
- The server sends a ServerHelloDone message, indicating it is done with handshake negotiation.
- The client responds with a ClientKeyExchange message, which may contain a PreMasterSecret, public key, or nothing. (Again, this depends on the selected cipher.) This PreMasterSecret is encrypted using the public key of the server certificate.
- The client and server then use the random numbers and PreMasterSecret to compute a common secret, called the "master secret". All other key data (session keys such as IV, symmetric encryption key, MAC key[285]) for this connection is derived from this master secret (and the client- and server-generated random values), which is passed through a carefully designed pseudorandom function.
- The client now sends a ChangeCipherSpec record, essentially telling the server, "Everything I tell you from now on will be authenticated (and encrypted if encryption parameters were present in the server certificate)." The ChangeCipherSpec is itself a record-level protocol with content type of 20.
- The client sends an authenticated and encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The server will attempt to decrypt the client's Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the server sends a ChangeCipherSpec, telling the client, "Everything I tell you from now on will be authenticated (and encrypted, if encryption was negotiated)."
- The server sends its authenticated and encrypted Finished message.
- The client performs the same decryption and verification procedure as the server did in the previous step.
- Application phase: at this point, the "handshake" is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be authenticated and optionally encrypted exactly like in their Finished message. Otherwise, the content type will return 25 and the client will not authenticate.
Client-authenticated TLS handshake[edit]
The following full example shows a client being authenticated (in addition to the server as in the example above; see mutual authentication) via TLS using certificates exchanged between both peers.
- Negotiation Phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested cipher suites and compression methods.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, cipher suite and compression method from the choices offered by the client. The server may also send a session id as part of the message to perform a resumed handshake.
- The server sends its Certificate message (depending on the selected cipher suite, this may be omitted by the server).[284]
- The server sends its ServerKeyExchange message (depending on the selected cipher suite, this may be omitted by the server). This message is sent for all DHE, ECDHE and DH_anon ciphersuites.[7]
- The server sends a CertificateRequest message, to request a certificate from the client.
- The server sends a ServerHelloDone message, indicating it is done with handshake negotiation.
- The client responds with a Certificate message, which contains the client's certificate.
- The client sends a ClientKeyExchange message, which may contain a PreMasterSecret, public key, or nothing. (Again, this depends on the selected cipher.) This PreMasterSecret is encrypted using the public key of the server certificate.
- The client sends a CertificateVerify message, which is a signature over the previous handshake messages using the client's certificate's private key. This signature can be verified by using the client's certificate's public key. This lets the server know that the client has access to the private key of the certificate and thus owns the certificate.
- The client and server then use the random numbers and PreMasterSecret to compute a common secret, called the "master secret". All other key data ("session keys") for this connection is derived from this master secret (and the client- and server-generated random values), which is passed through a carefully designed pseudorandom function.
- The client now sends a ChangeCipherSpec record, essentially telling the server, "Everything I tell you from now on will be authenticated (and encrypted if encryption was negotiated). " The ChangeCipherSpec is itself a record-level protocol and has type 20 and not 22.
- Finally, the client sends an encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The server will attempt to decrypt the client's Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the server sends a ChangeCipherSpec, telling the client, "Everything I tell you from now on will be authenticated (and encrypted if encryption was negotiated). "
- The server sends its own encrypted Finished message.
- The client performs the same decryption and verification procedure as the server did in the previous step.
- Application phase: at this point, the "handshake" is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be encrypted exactly like in their Finished message.
Resumed TLS handshake[edit]
Public key operations (e.g., RSA) are relatively expensive in terms of computational power. TLS provides a secure shortcut in the handshake mechanism to avoid these operations: resumed sessions. Resumed sessions are implemented using session IDs or session tickets.
Apart from the performance benefit, resumed sessions can also be used for single sign-on, as it guarantees that both the original session and any resumed session originate from the same client. This is of particular importance for the FTP over TLS/SSL protocol, which would otherwise suffer from a man-in-the-middle attack in which an attacker could intercept the contents of the secondary data connections.[286]
TLS 1.3 handshake[edit]
The TLS 1.3 handshake was condensed to only one round trip compared to the two round trips required in previous versions of TLS/SSL.
First the client sends a clientHello message to the server that contains a list of supported ciphers in order of the client's preference and makes a guess on what key algorithm will be used so that it can send a secret key to share if needed. By making a guess at what key algorithm will be used, the server eliminates a round trip. After receiving the clientHello, the server sends a serverHello with its key, a certificate, the chosen cipher suite and the finished message.
After the client receives the server's finished message, it now is coordinated with the server on which cipher suite to use.[287]
Session IDs[edit]
In an ordinary full handshake, the server sends a session id as part of the ServerHello message. The client associates this session id with the server's IP address and TCP port, so that when the client connects again to that server, it can use the session id to shortcut the handshake. In the server, the session id maps to the cryptographic parameters previously negotiated, specifically the "master secret". Both sides must have the same "master secret" or the resumed handshake will fail (this prevents an eavesdropper from using a session id). The random data in the ClientHello and ServerHello messages virtually guarantee that the generated connection keys will be different from in the previous connection. In the RFCs, this type of handshake is called an abbreviated handshake. It is also described in the literature as a restart handshake.
- Negotiation phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested cipher suites and compression methods. Included in the message is the session id from the previous TLS connection.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, cipher suite and compression method from the choices offered by the client. If the server recognizes the session id sent by the client, it responds with the same session id. The client uses this to recognize that a resumed handshake is being performed. If the server does not recognize the session id sent by the client, it sends a different value for its session id. This tells the client that a resumed handshake will not be performed. At this point, both the client and server have the "master secret" and random data to generate the key data to be used for this connection.
- The server now sends a ChangeCipherSpec record, essentially telling the client, "Everything I tell you from now on will be encrypted." The ChangeCipherSpec is itself a record-level protocol and has type 20 and not 22.
- Finally, the server sends an encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The client will attempt to decrypt the server's Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the client sends a ChangeCipherSpec, telling the server, "Everything I tell you from now on will be encrypted. "
- The client sends its own encrypted Finished message.
- The server performs the same decryption and verification procedure as the client did in the previous step.
- Application phase: at this point, the "handshake" is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be encrypted exactly like in their Finished message.
Session tickets[edit]
RFC 5077 extends TLS via use of session tickets, instead of session IDs. It defines a way to resume a TLS session without requiring that session-specific state is stored at the TLS server.
When using session tickets, the TLS server stores its session-specific state in a session ticket and sends the session ticket to the TLS client for storing. The client resumes a TLS session by sending the session ticket to the server, and the server resumes the TLS session according to the session-specific state in the ticket. The session ticket is encrypted and authenticated by the server, and the server verifies its validity before using its contents.
One particular weakness of this method with OpenSSL is that it always limits encryption and authentication security of the transmitted TLS session ticket to AES128-CBC-SHA256, no matter what other TLS parameters were negotiated for the actual TLS session.[278] This means that the state information (the TLS session ticket) is not as well protected as the TLS session itself. Of particular concern is OpenSSL's storage of the keys in an application-wide context (SSL_CTX), i.e. for the life of the application, and not allowing for re-keying of the AES128-CBC-SHA256 TLS session tickets without resetting the application-wide OpenSSL context (which is uncommon, error-prone and often requires manual administrative intervention).[279][277]
TLS record[edit]
This is the general format of all TLS records.
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
Content type | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |
| Bytes 5..(m−1) |
Protocol message(s) | |||
| Bytes m..(p−1) |
MAC (optional) | |||
| Bytes p..(q−1) |
Padding (block ciphers only) | |||
- Content type
- This field identifies the Record Layer Protocol Type contained in this record.
| Hex | Dec | Type |
|---|---|---|
| 0x14 | 20 | ChangeCipherSpec |
| 0x15 | 21 | Alert |
| 0x16 | 22 | Handshake |
| 0x17 | 23 | Application |
| 0x18 | 24 | Heartbeat |
- Legacy version
- This field identifies the major and minor version of TLS prior to TLS 1.3 for the contained message. For a ClientHello message, this need not be the highest version supported by the client. For TLS 1.3 and later, this must to be set 0x0303 and application must send supported versions in an extra message extension block.
| Major version | Minor version | Version type |
|---|---|---|
| 3 | 0 | SSL 3.0 |
| 3 | 1 | TLS 1.0 |
| 3 | 2 | TLS 1.1 |
| 3 | 3 | TLS 1.2 |
| 3 | 4 | TLS 1.3 |
- Length
- The length of "protocol message(s)", "MAC" and "padding" fields combined (i.e. q−5), not to exceed 214 bytes (16 KiB).
- Protocol message(s)
- One or more messages identified by the Protocol field. Note that this field may be encrypted depending on the state of the connection.
- MAC and padding
- A message authentication code computed over the "protocol message(s)" field, with additional key material included. Note that this field may be encrypted, or not included entirely, depending on the state of the connection.
- No "MAC" or "padding" fields can be present at end of TLS records before all cipher algorithms and parameters have been negotiated and handshaked and then confirmed by sending a CipherStateChange record (see below) for signalling that these parameters will take effect in all further records sent by the same peer.
Handshake protocol[edit]
Most messages exchanged during the setup of the TLS session are based on this record, unless an error or warning occurs and needs to be signaled by an Alert protocol record (see below), or the encryption mode of the session is modified by another record (see ChangeCipherSpec protocol below).
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
22 | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |
| Bytes 5..8 |
Message type | Handshake message data length | ||
| (bits 23..16) | (bits 15..8) | (bits 7..0) | ||
| Bytes 9..(n−1) |
Handshake message data | |||
| Bytes n..(n+3) |
Message type | Handshake message data length | ||
| (bits 23..16) | (bits 15..8) | (bits 7..0) | ||
| Bytes (n+4).. |
Handshake message data | |||
- Message type
- This field identifies the handshake message type.
| Code | Description |
|---|---|
| 0 | HelloRequest |
| 1 | ClientHello |
| 2 | ServerHello |
| 4 | NewSessionTicket |
| 8 | EncryptedExtensions (TLS 1.3 only) |
| 11 | Certificate |
| 12 | ServerKeyExchange |
| 13 | CertificateRequest |
| 14 | ServerHelloDone |
| 15 | CertificateVerify |
| 16 | ClientKeyExchange |
| 20 | Finished |
- Handshake message data length
- This is a 3-byte field indicating the length of the handshake data, not including the header.
Note that multiple handshake messages may be combined within one record.
Alert protocol[edit]
This record should normally not be sent during normal handshaking or application exchanges. However, this message can be sent at any time during the handshake and up to the closure of the session. If this is used to signal a fatal error, the session will be closed immediately after sending this record, so this record is used to give a reason for this closure. If the alert level is flagged as a warning, the remote can decide to close the session if it decides that the session is not reliable enough for its needs (before doing so, the remote may also send its own signal).
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
21 | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | 0 | 2 | |
| Bytes 5..6 |
Level | Description | N/A | |
| Bytes 7..(p−1) |
MAC (optional) | |||
| Bytes p..(q−1) |
Padding (block ciphers only) | |||
- Level
- This field identifies the level of alert. If the level is fatal, the sender should close the session immediately. Otherwise, the recipient may decide to terminate the session itself, by sending its own fatal alert and closing the session itself immediately after sending it. The use of Alert records is optional, however if it is missing before the session closure, the session may be resumed automatically (with its handshakes).
- Normal closure of a session after termination of the transported application should preferably be alerted with at least the Close notify Alert type (with a simple warning level) to prevent such automatic resume of a new session. Signalling explicitly the normal closure of a secure session before effectively closing its transport layer is useful to prevent or detect attacks (like attempts to truncate the securely transported data, if it intrinsically does not have a predetermined length or duration that the recipient of the secured data may expect).
| Code | Level type | Connection state |
|---|---|---|
| 1 | warning | connection or security may be unstable. |
| 2 | fatal | connection or security may be compromised, or an unrecoverable error has occurred. |
- Description
- This field identifies which type of alert is being sent.
| Code | Description | Level types | Note |
|---|---|---|---|
| 0 | Close notify | warning/fatal | |
| 10 | Unexpected message | fatal | |
| 20 | Bad record MAC | fatal | Possibly a bad SSL implementation, or payload has been tampered with e.g. FTP firewall rule on FTPS server. |
| 21 | Decryption failed | fatal | TLS only, reserved |
| 22 | Record overflow | fatal | TLS only |
| 30 | Decompression failure | fatal | |
| 40 | Handshake failure | fatal | |
| 41 | No certificate | warning/fatal | SSL 3.0 only, reserved |
| 42 | Bad certificate | warning/fatal | |
| 43 | Unsupported certificate | warning/fatal | e.g. certificate has only server authentication usage enabled and is presented as a client certificate |
| 44 | Certificate revoked | warning/fatal | |
| 45 | Certificate expired | warning/fatal | Check server certificate expire also check no certificate in the chain presented has expired |
| 46 | Certificate unknown | warning/fatal | |
| 47 | Illegal parameter | fatal | |
| 48 | Unknown CA (Certificate authority) | fatal | TLS only |
| 49 | Access denied | fatal | TLS only – e.g. no client certificate has been presented (TLS: Blank certificate message or SSLv3: No Certificate alert), but server is configured to require one. |
| 50 | Decode error | fatal | TLS only |
| 51 | Decrypt error | warning/fatal | TLS only |
| 60 | Export restriction | fatal | TLS only, reserved |
| 70 | Protocol version | fatal | TLS only |
| 71 | Insufficient security | fatal | TLS only |
| 80 | Internal error | fatal | TLS only |
| 86 | Inappropriate fallback | fatal | TLS only |
| 90 | User canceled | fatal | TLS only |
| 100 | No renegotiation | warning | TLS only |
| 110 | Unsupported extension | warning | TLS only |
| 111 | Certificate unobtainable | warning | TLS only |
| 112 | Unrecognized name | warning/fatal | TLS only; client's Server Name Indicator specified a hostname not supported by the server |
| 113 | Bad certificate status response | fatal | TLS only |
| 114 | Bad certificate hash value | fatal | TLS only |
| 115 | Unknown PSK identity (used in TLS-PSK and TLS-SRP) | fatal | TLS only |
ChangeCipherSpec protocol[edit]
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
20 | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | 0 | 1 | |
| Byte 5 |
CCS protocol type | N/A | ||
- CCS protocol type
- Currently only 1.
Application protocol[edit]
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
23 | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |
| Bytes 5..(m−1) |
Application data | |||
| Bytes m..(p−1) |
MAC (optional) | |||
| Bytes p..(q−1) |
Padding (block ciphers only) | |||
- Length
- Length of application data (excluding the protocol header and including the MAC and padding trailers)
- MAC
- 32 bytes for the SHA-256-based HMAC, 20 bytes for the SHA-1-based HMAC, 16 bytes for the MD5-based HMAC.
- Padding
- Variable length; last byte contains the padding length.
Support for name-based virtual servers[edit]
From the application protocol point of view, TLS belongs to a lower layer, although the TCP/IP model is too coarse to show it. This means that the TLS handshake is usually (except in the STARTTLS case) performed before the application protocol can start. In the name-based virtual server feature being provided by the application layer, all co-hosted virtual servers share the same certificate because the server has to select and send a certificate immediately after the ClientHello message. This is a big problem in hosting environments because it means either sharing the same certificate among all customers or using a different IP address for each of them.
There are two known workarounds provided by X.509:
- If all virtual servers belong to the same domain, a wildcard certificate can be used.[288] Besides the loose host name selection that might be a problem or not, there is no common agreement about how to match wildcard certificates. Different rules are applied depending on the application protocol or software used.[289]
- Add every virtual host name in the subjectAltName extension. The major problem being that the certificate needs to be reissued whenever a new virtual server is added.
To provide the server name, RFC 4366 Transport Layer Security (TLS) Extensions allow clients to include a Server Name Indication extension (SNI) in the extended ClientHello message. This extension hints to the server immediately which name the client wishes to connect to, so the server can select the appropriate certificate to send to the clients.
RFC 2817 also documents a method to implement name-based virtual hosting by upgrading HTTP to TLS via an HTTP/1.1 Upgrade header. Normally this is to securely implement HTTP over TLS within the main "http" URI scheme (which avoids forking the URI space and reduces the number of used ports), however, few implementations currently support this.[citation needed]
Standards[edit]
Primary standards[edit]
The current approved version of TLS is version 1.3, which is specified in:
The current standard replaces these former versions, which are now considered obsolete:
- RFC 2246: "The TLS Protocol Version 1.0".
- RFC 4346: "The Transport Layer Security (TLS) Protocol Version 1.1".
- RFC 5246: "The Transport Layer Security (TLS) Protocol Version 1.2".
As well as the never standardized SSL 2.0 and 3.0, which are considered obsolete:
- Internet Draft (1995), SSL Version 2.0
- RFC 6101: "The Secure Sockets Layer (SSL) Protocol Version 3.0".
Extensions[edit]
Other RFCs subsequently extended TLS.
Extensions to TLS 1.0 include:
- RFC 2595: "Using TLS with IMAP, POP3 and ACAP". Specifies an extension to the IMAP, POP3 and ACAP services that allow the server and client to use transport-layer security to provide private, authenticated communication over the Internet.
- RFC 2712: "Addition of Kerberos Cipher Suites to Transport Layer Security (TLS)". The 40-bit cipher suites defined in this memo appear only for the purpose of documenting the fact that those cipher suite codes have already been assigned.
- RFC 2817: "Upgrading to TLS Within HTTP/1.1", explains how to use the Upgrade mechanism in HTTP/1.1 to initiate Transport Layer Security (TLS) over an existing TCP connection. This allows unsecured and secured HTTP traffic to share the same well known port (in this case, http: at 80 rather than https: at 443).
- RFC 2818: "HTTP Over TLS", distinguishes secured traffic from insecure traffic by the use of a different 'server port'.
- RFC 3207: "SMTP Service Extension for Secure SMTP over Transport Layer Security". Specifies an extension to the SMTP service that allows an SMTP server and client to use transport-layer security to provide private, authenticated communication over the Internet.
- RFC 3268: "AES Ciphersuites for TLS". Adds Advanced Encryption Standard (AES) cipher suites to the previously existing symmetric ciphers.
- RFC 3546: "Transport Layer Security (TLS) Extensions", adds a mechanism for negotiating protocol extensions during session initialisation and defines some extensions. Made obsolete by RFC 4366.
- RFC 3749: "Transport Layer Security Protocol Compression Methods", specifies the framework for compression methods and the DEFLATE compression method.
- RFC 3943: "Transport Layer Security (TLS) Protocol Compression Using Lempel-Ziv-Stac (LZS)".
- RFC 4132: "Addition of Camellia Cipher Suites to Transport Layer Security (TLS)".
- RFC 4162: "Addition of SEED Cipher Suites to Transport Layer Security (TLS)".
- RFC 4217: "Securing FTP with TLS".
- RFC 4279: "Pre-Shared Key Ciphersuites for Transport Layer Security (TLS)", adds three sets of new cipher suites for the TLS protocol to support authentication based on pre-shared keys.
Extensions to TLS 1.1 include:
- RFC 4347: "Datagram Transport Layer Security" specifies a TLS variant that works over datagram protocols (such as UDP).
- RFC 4366: "Transport Layer Security (TLS) Extensions" describes both a set of specific extensions and a generic extension mechanism.
- RFC 4492: "Elliptic Curve Cryptography (ECC) Cipher Suites for Transport Layer Security (TLS)".
- RFC 4680: "TLS Handshake Message for Supplemental Data".
- RFC 4681: "TLS User Mapping Extension".
- RFC 4785: "Pre-Shared Key (PSK) Ciphersuites with NULL Encryption for Transport Layer Security (TLS)".
- RFC 5054: "Using the Secure Remote Password (SRP) Protocol for TLS Authentication". Defines the TLS-SRP ciphersuites.
- RFC 5077: "Transport Layer Security (TLS) Session Resumption without Server-Side State".
- RFC 5081: "Using OpenPGP Keys for Transport Layer Security (TLS) Authentication", obsoleted by RFC 6091.
Extensions to TLS 1.2 include:
- RFC 5288: "AES Galois Counter Mode (GCM) Cipher Suites for TLS".
- RFC 5289: "TLS Elliptic Curve Cipher Suites with SHA-256/384 and AES Galois Counter Mode (GCM)".
- RFC 5746: "Transport Layer Security (TLS) Renegotiation Indication Extension".
- RFC 5878: "Transport Layer Security (TLS) Authorization Extensions".
- RFC 5932: "Camellia Cipher Suites for TLS"
- RFC 6066: "Transport Layer Security (TLS) Extensions: Extension Definitions", includes Server Name Indication and OCSP stapling.
- RFC 6091: "Using OpenPGP Keys for Transport Layer Security (TLS) Authentication".
- RFC 6176: "Prohibiting Secure Sockets Layer (SSL) Version 2.0".
- RFC 6209: "Addition of the ARIA Cipher Suites to Transport Layer Security (TLS)".
- RFC 6347: "Datagram Transport Layer Security Version 1.2".
- RFC 6367: "Addition of the Camellia Cipher Suites to Transport Layer Security (TLS)".
- RFC 6460: "Suite B Profile for Transport Layer Security (TLS)".
- RFC 6655: "AES-CCM Cipher Suites for Transport Layer Security (TLS)".
- RFC 7027: "Elliptic Curve Cryptography (ECC) Brainpool Curves for Transport Layer Security (TLS)".
- RFC 7251: "AES-CCM Elliptic Curve Cryptography (ECC) Cipher Suites for TLS".
- RFC 7301: "Transport Layer Security (TLS) Application-Layer Protocol Negotiation Extension".
- RFC 7366: "Encrypt-then-MAC for Transport Layer Security (TLS) and Datagram Transport Layer Security (DTLS)".
- RFC 7465: "Prohibiting RC4 Cipher Suites".
- RFC 7507: "TLS Fallback Signaling Cipher Suite Value (SCSV) for Preventing Protocol Downgrade Attacks".
- RFC 7568: "Deprecating Secure Sockets Layer Version 3.0".
- RFC 7627: "Transport Layer Security (TLS) Session Hash and Extended Master Secret Extension".
- RFC 7685: "A Transport Layer Security (TLS) ClientHello Padding Extension".
Encapsulations of TLS include:
Informational RFCs[edit]


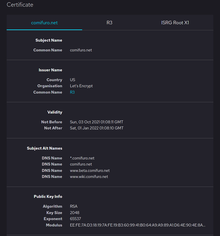


 浙公网安备 33010602011771号
浙公网安备 33010602011771号