linux系统中firewalld防火墙管理工具firewall-config(GUI图形用户界面)
firewall-config是firewalld防火墙管理工具的GUI(图形用户界面)版本,几乎可以实现所有以命令行来执行的操作(linux就该这么学p164)。
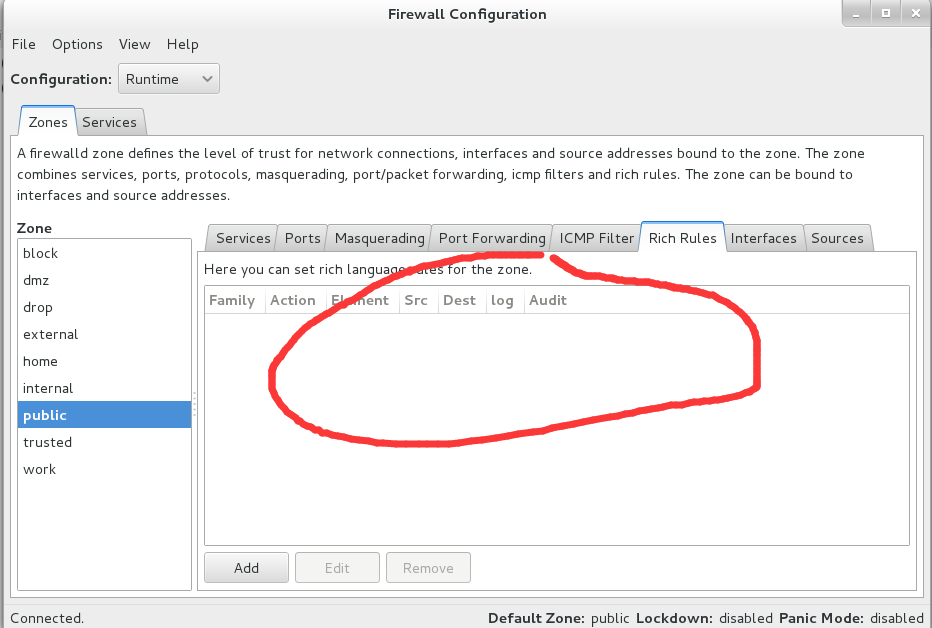
firewall-config的界面如下图(在终端直接运行firewall-config即弹出),其功能如下:
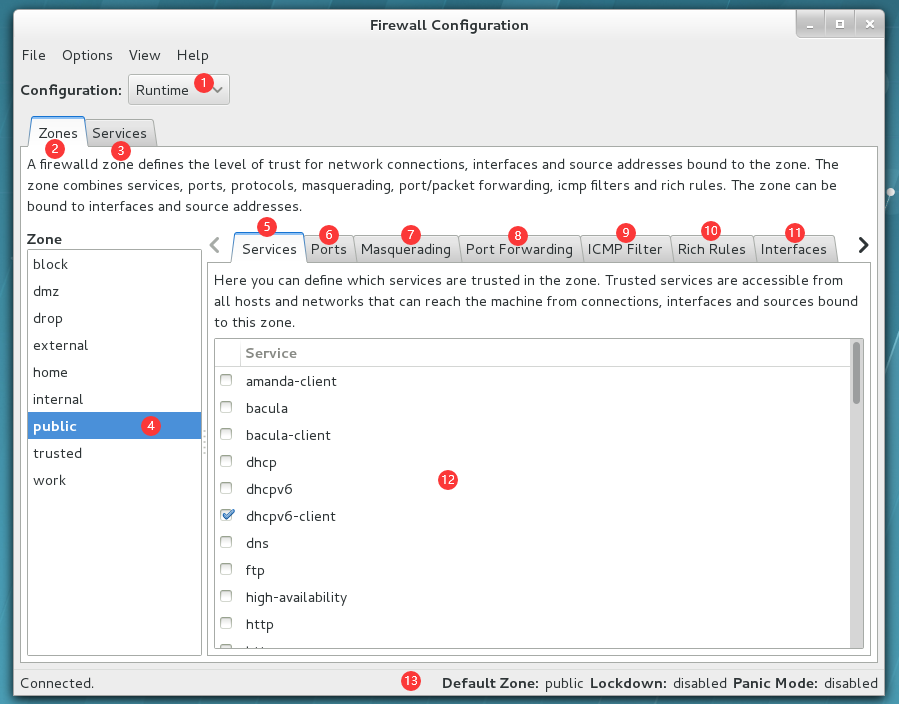
1:选择运行时(Runtime)和永久(Permanent)模式的配置
2:可选的策略集合区域的列表
3:常用的系统服务列表
4:当前正在使用的区域
5:管理当前被选中区域中的服务
6:管理当前被选中区域中的端口
7:开启或关闭SNAT(源地址转换协议)技术
8:设置端口转发策略
9:控制请求icmp服务的流量
10:管理防火墙的富规则
11:管理网卡设备
12:被选中区域的服务
13:firewall-config工具的运行状态
1、查看当前firewalld服务所使用的区域
[root@linuxprobe ~]# firewall-config

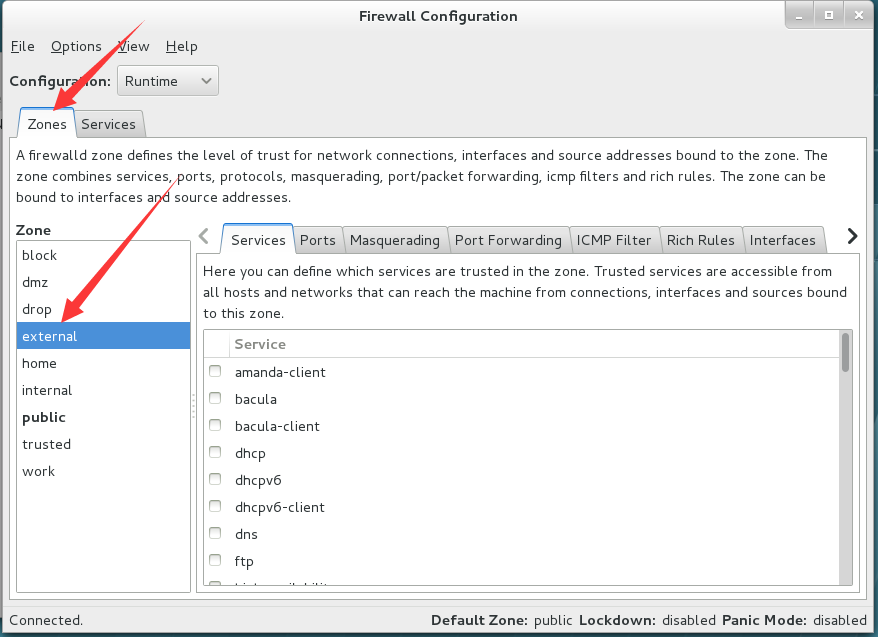
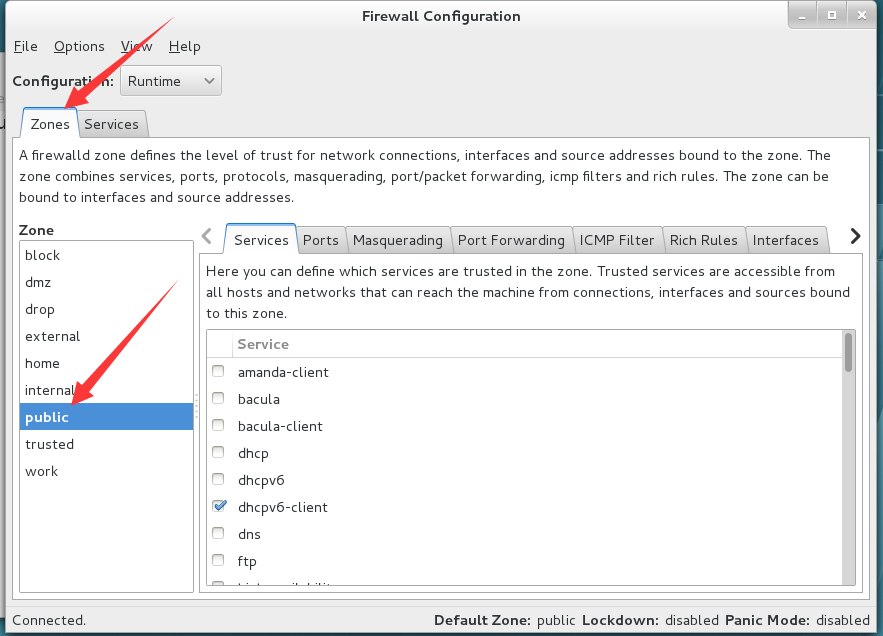
2、切换firewalld服务所使用的区域
切换至external:
切换至public:
3、把在firewalld服务中访问8080和8081端口的流量策略设置为允许,仅当前有效
查看设置前的端口列表:
[root@linuxprobe ~]# firewall-cmd --zone=public --list-ports
[root@linuxprobe ~]#
增加端口:
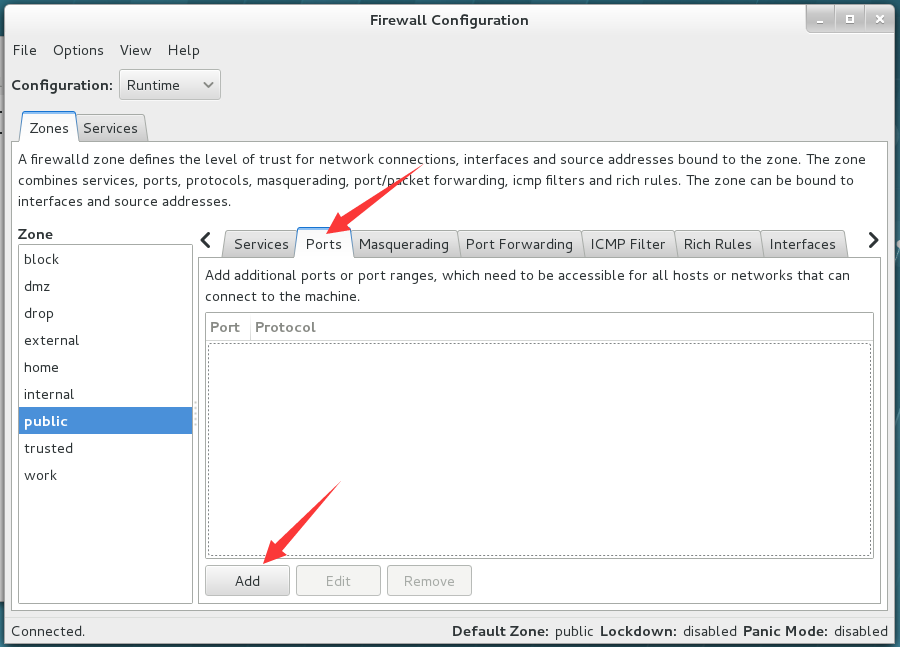
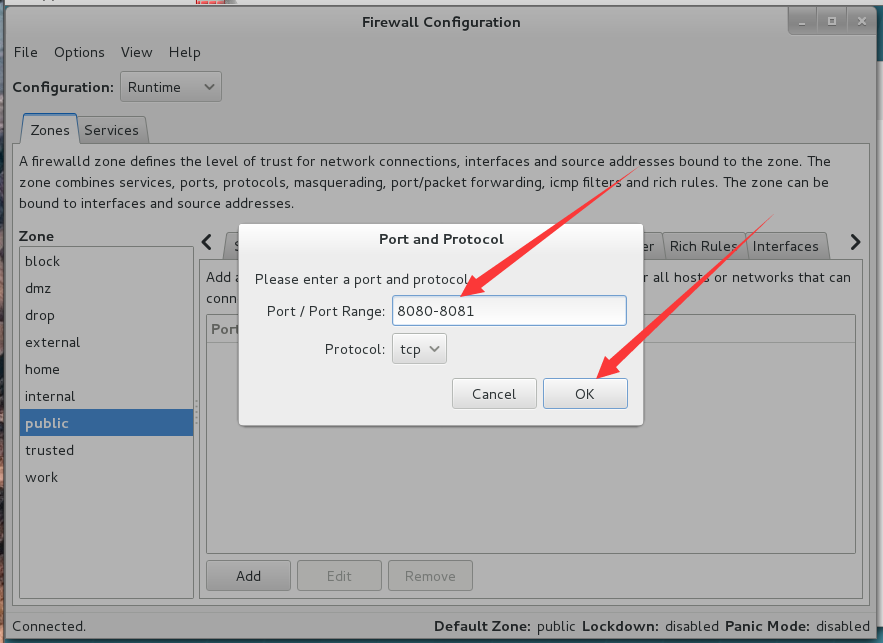
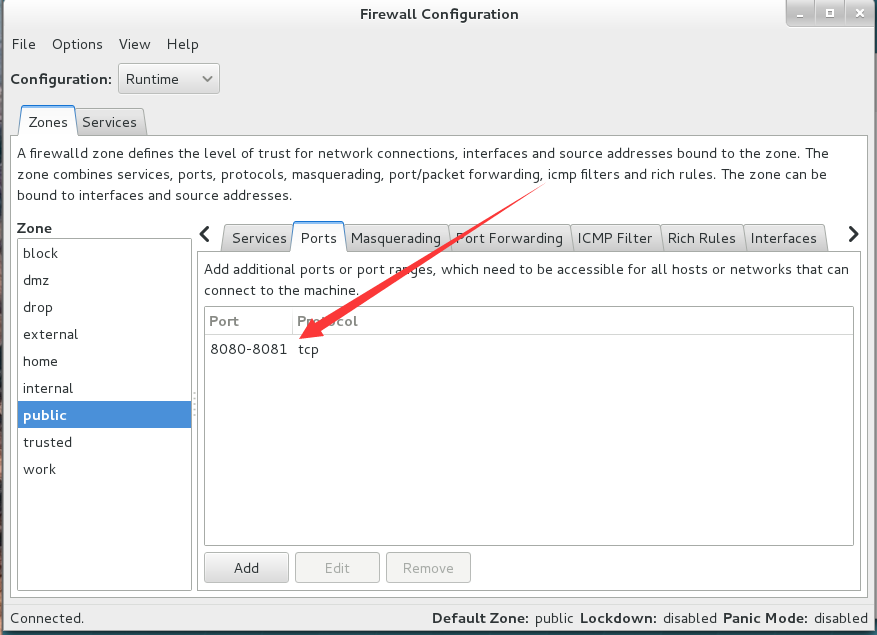
查看效果:
[root@linuxprobe ~]# firewall-cmd --zone=public --list-ports
8080-8081/tcp
4、查询public区域是否允许请求ssh和https协议的流量,并进行设置:
使用firewall-cmd命令行查询:
[root@linuxprobe ~]# firewall-cmd --zone=public --query-service=ssh
yes
[root@linuxprobe ~]# firewall-cmd --zone=public --query-service=https
no
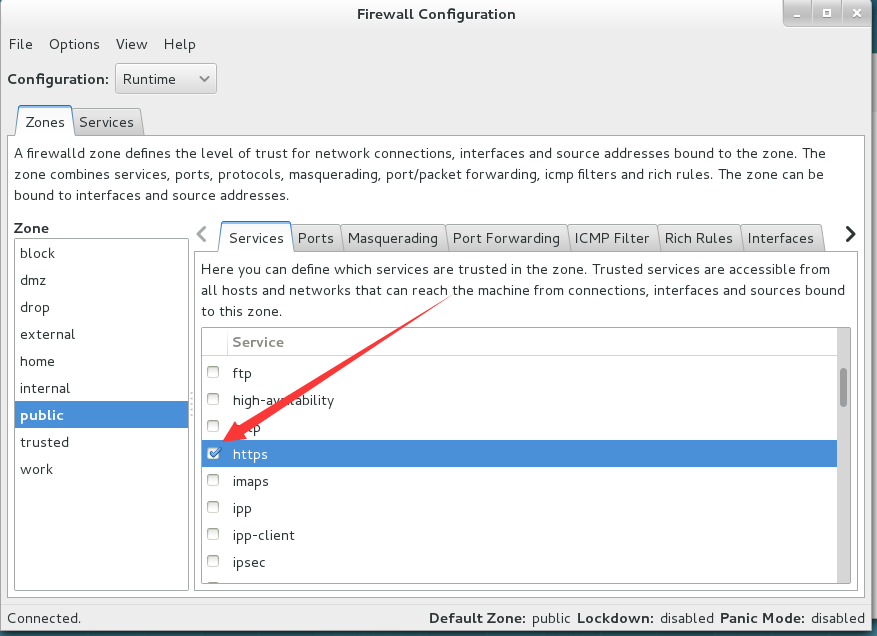
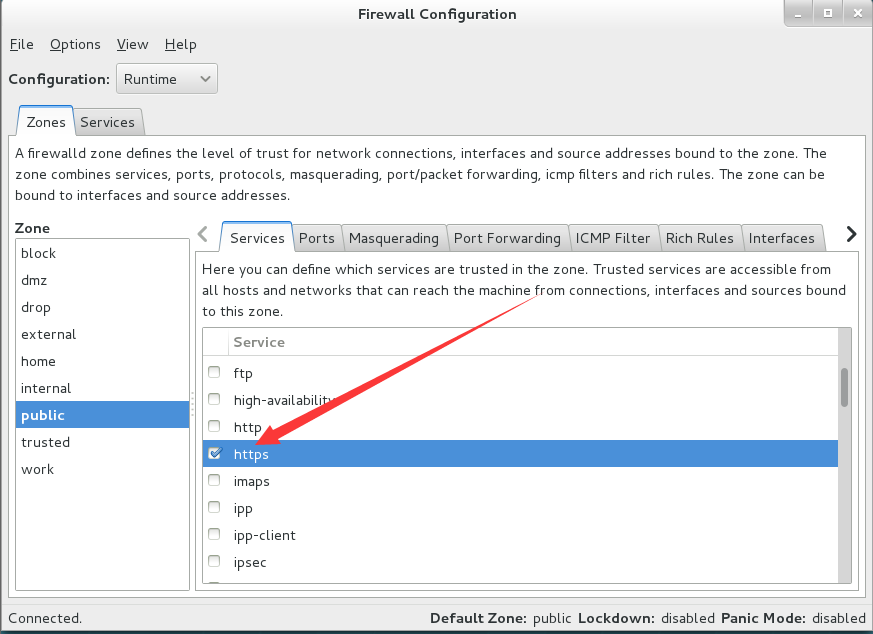
使用firewall-config图形用户界面查询:
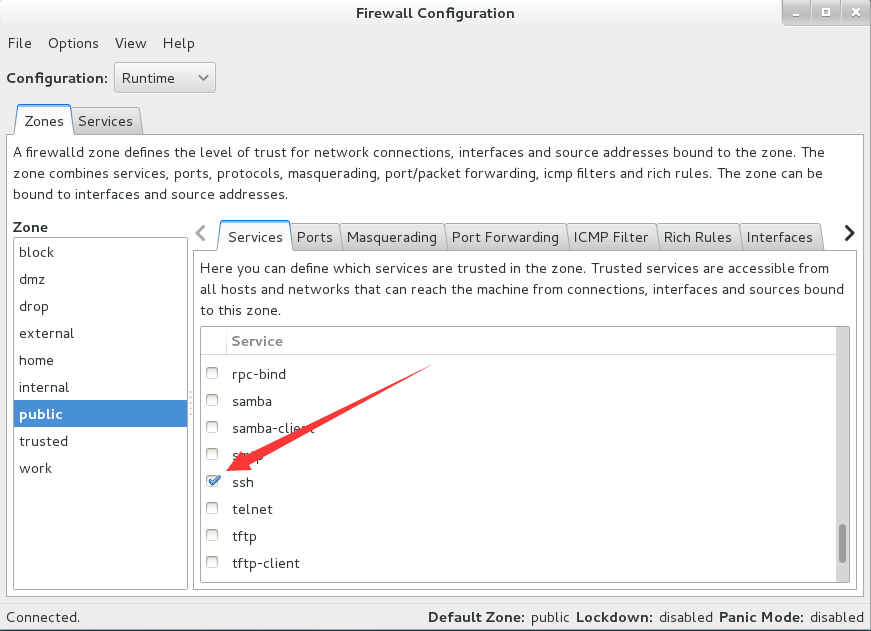
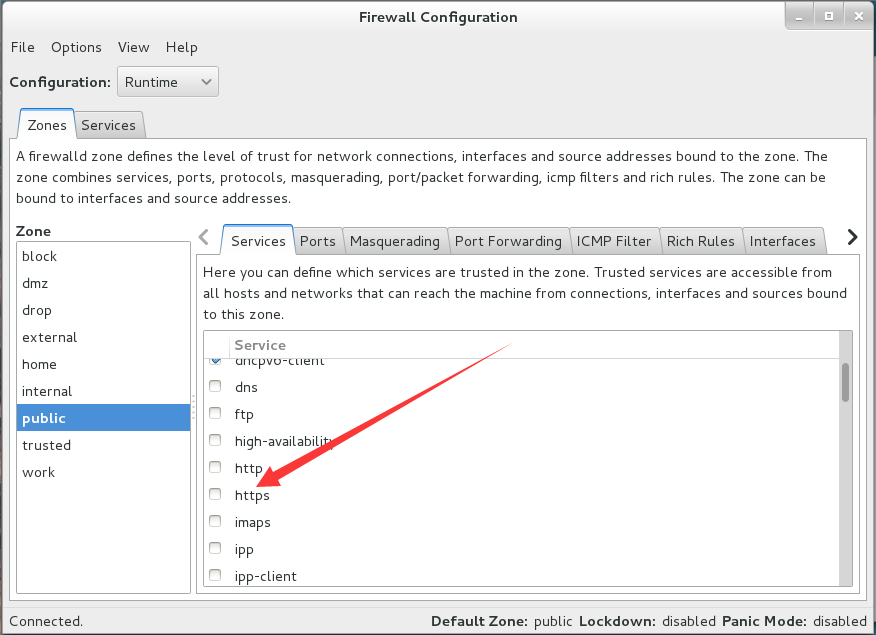
利用图形界面工具将https协议的流量在public区域设置为允许并利用命令行测试:
[root@linuxprobe ~]# firewall-cmd --zone=public --query-service=https
yes
5、把firewalld服务中请求https协议设置为永久拒绝,并立即生效:
查看当前状态:
[root@linuxprobe ~]# firewall-cmd --zone=public --query-service=https
yes
设置为永久拒绝:
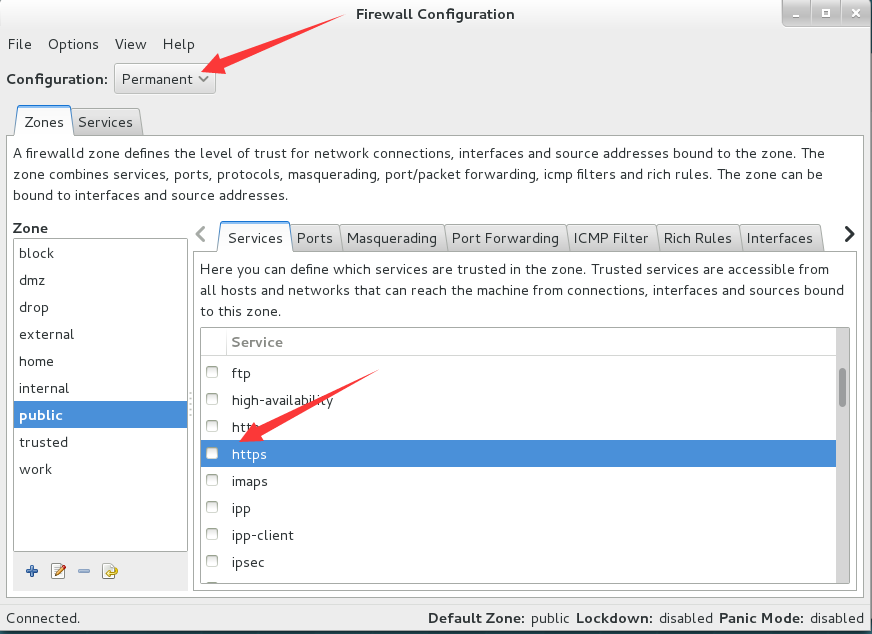
测试:
[root@linuxprobe ~]# firewall-cmd --zone=public --query-service=https
yes
立即生效:
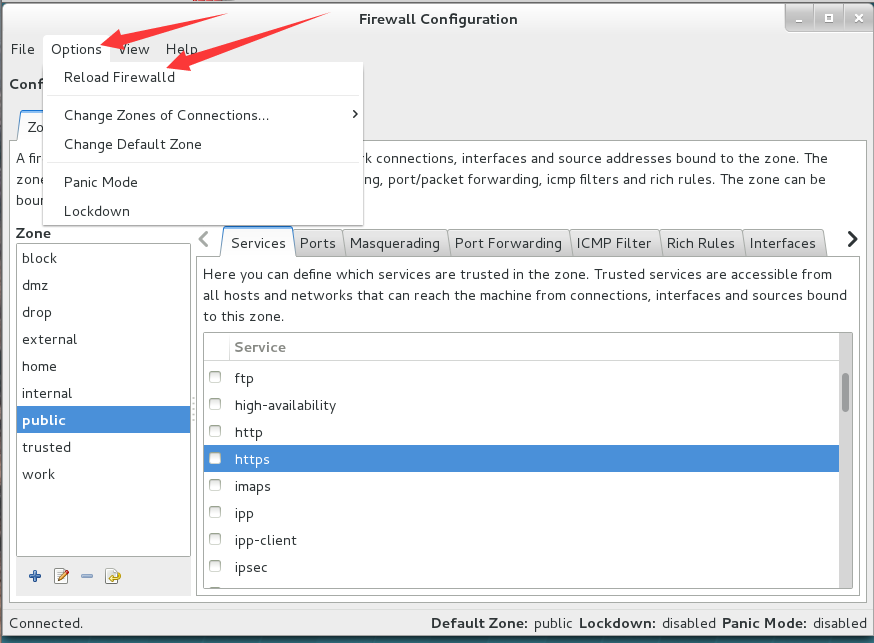
测试:
[root@linuxprobe ~]# firewall-cmd --zone=public --query-service=https
no
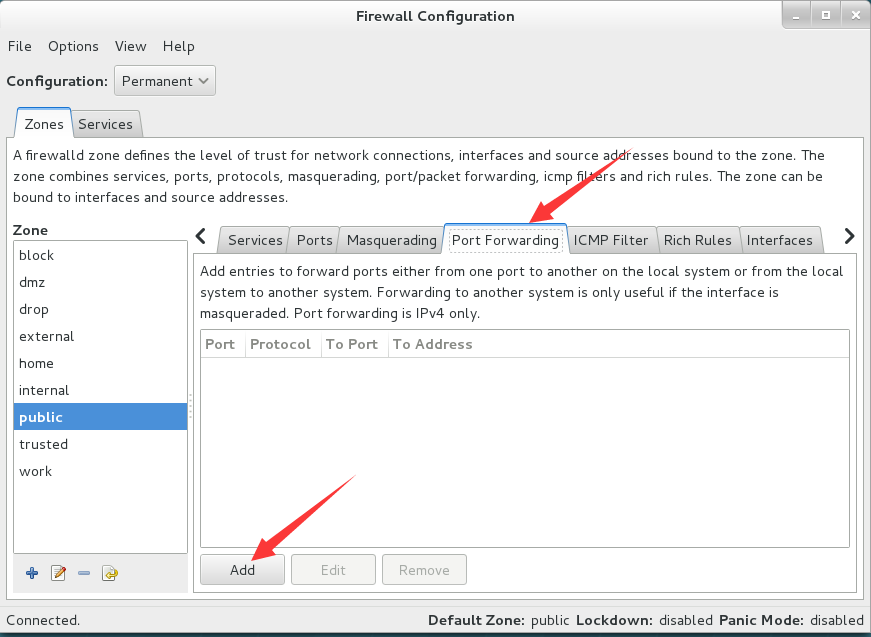
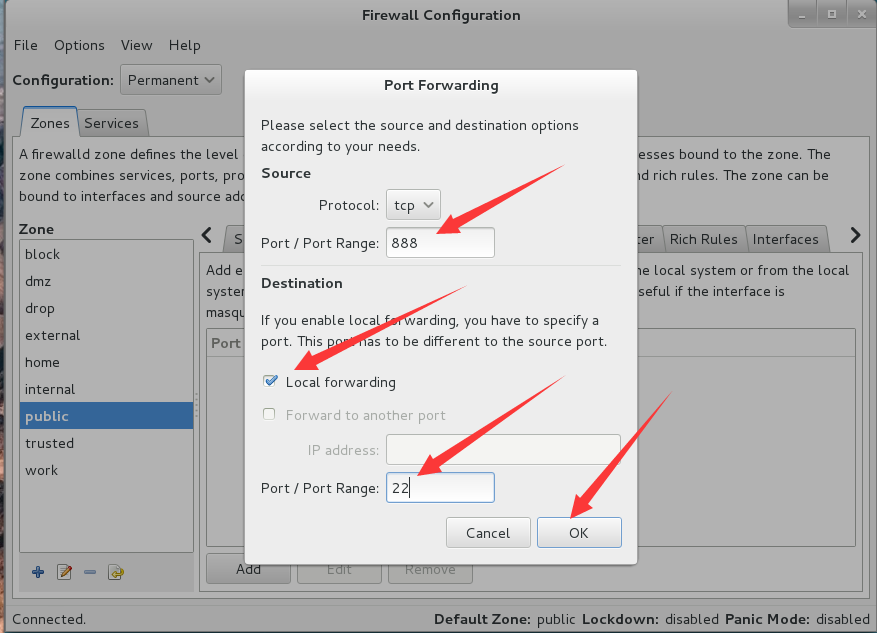
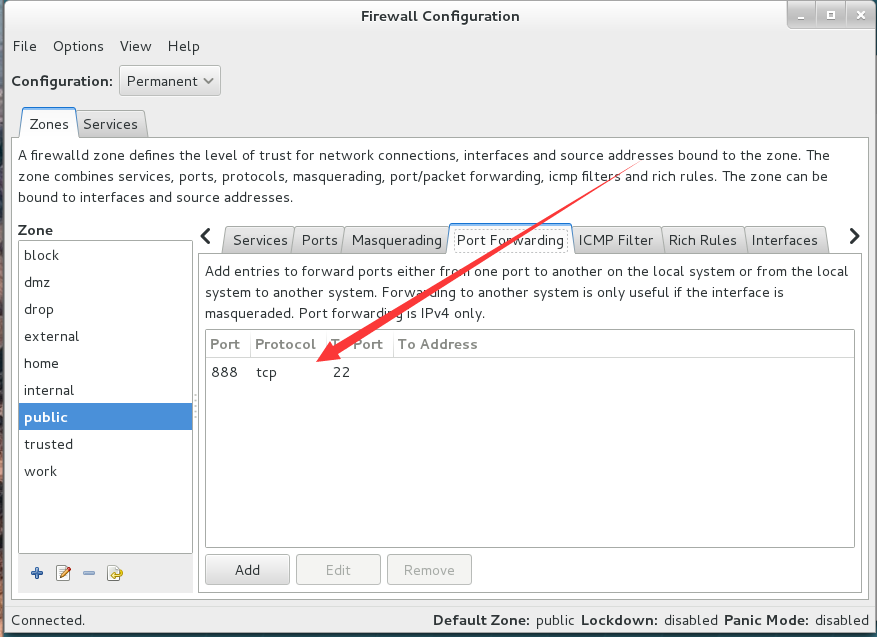
6、利用图形用户界面将原本访问本机888端口的流量转发到22端口
测试设置前效果:
[root@linuxprobe ~]# ifconfig | head -n 5 ## 查看当前主机IP
eno16777728: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.13 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::20c:29ff:feab:7b00 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:ab:7b:00 txqueuelen 1000 (Ethernet)
RX packets 553 bytes 52426 (51.1 KiB)
[root@linuxprobe ~]# ifconfig | head -n 5 ## 登录另一台主机,查看IP
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.14 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::d7fe:9dfc:42ec:c255 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:ef:86:f2 txqueuelen 1000 (Ethernet)
RX packets 2531 bytes 3395800 (3.2 MiB)
[root@linuxprobe ~]# ssh -p 888 192.168.3.13 ## 测试远程连接服务
ssh: connect to host 192.168.3.13 port 888: No route to host
利用图形用户界面设置:
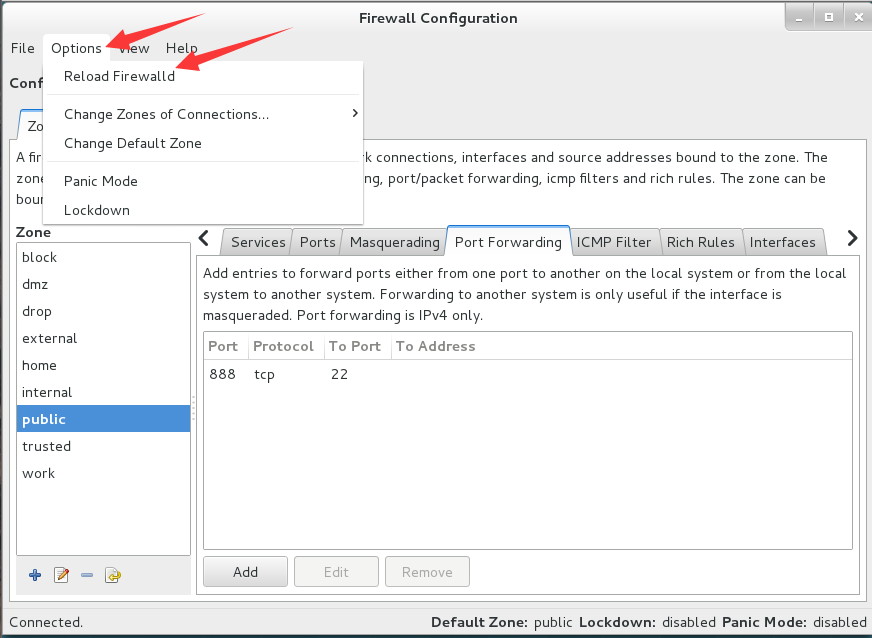
测试效果:
[root@linuxprobe ~]# ifconfig | head -n 5 ## 登录另一台主机,查看IP
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.14 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::d7fe:9dfc:42ec:c255 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:ef:86:f2 txqueuelen 1000 (Ethernet)
RX packets 2621 bytes 3403906 (3.2 MiB)
[root@linuxprobe ~]# ssh -p 888 192.168.3.13 ## 远程测试,通过
The authenticity of host '[192.168.3.13]:888 ([192.168.3.13]:888)' can't be established.
ECDSA key fingerprint is SHA256:K5A4gXWj7saZdeIJ7CpMozT2rSvDBbcA2iJEoqtCx+c.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '[192.168.3.13]:888' (ECDSA) to the list of known hosts.
root@192.168.3.13's password:
Last login: Sat Oct 31 18:00:24 2020 from 192.168.3.4
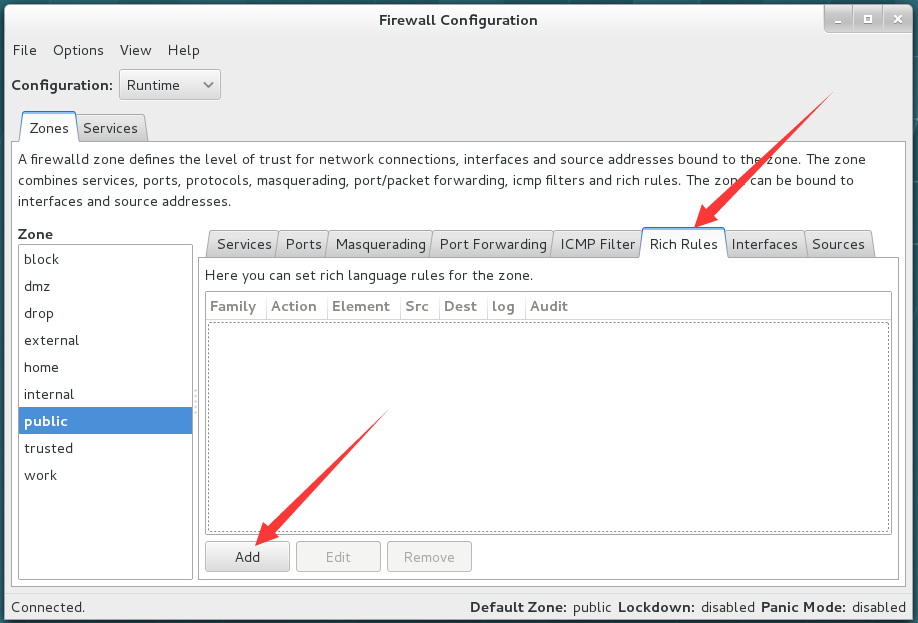
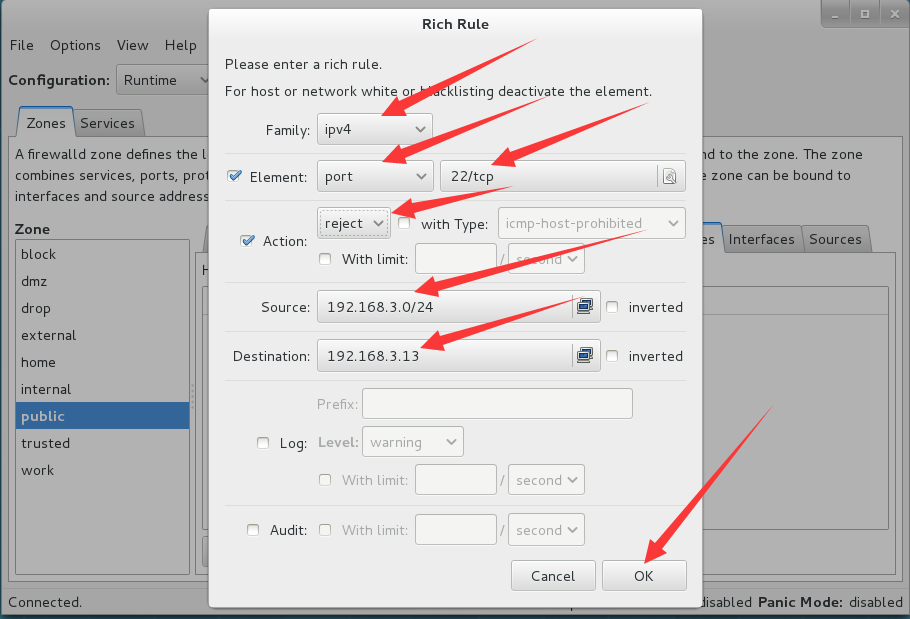
7、利用图形用户界面的富规则设置拒绝192.168.3.0/24所有用户访问本机22端口(ssh服务)
测试设置前效果:
[root@linuxprobe ~]# ifconfig | head -n 5 ## 查看本机IP
eno16777728: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.13 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::20c:29ff:feab:7b00 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:ab:7b:00 txqueuelen 1000 (Ethernet)
RX packets 792 bytes 76004 (74.2 KiB)
[root@linuxprobe ~]# ifconfig | head -n 5 ## 登录另一主机,查看IP
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.14 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::d7fe:9dfc:42ec:c255 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:ef:86:f2 txqueuelen 1000 (Ethernet)
RX packets 3139 bytes 3459666 (3.2 MiB)
[root@linuxprobe ~]# ssh 192.168.3.13 ## 测试远程控制,通过
root@192.168.3.13's password:
Last login: Sat Oct 31 18:44:29 2020 from 192.168.3.4
[root@linuxprobe ~]# ifconfig | head -n 5 ## 登录另一主机,查看IP
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.8 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::54f8:bbf7:7760:3745 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:8d:79:f8 txqueuelen 1000 (Ethernet)
RX packets 73 bytes 12740 (12.4 KiB)
[root@linuxprobe ~]# ssh 192.168.3.13 ## 测试远程控制,通过
root@192.168.3.13's password:
Last login: Sat Oct 31 18:44:40 2020 from 192.168.3.14
使用图形用户界面设置:
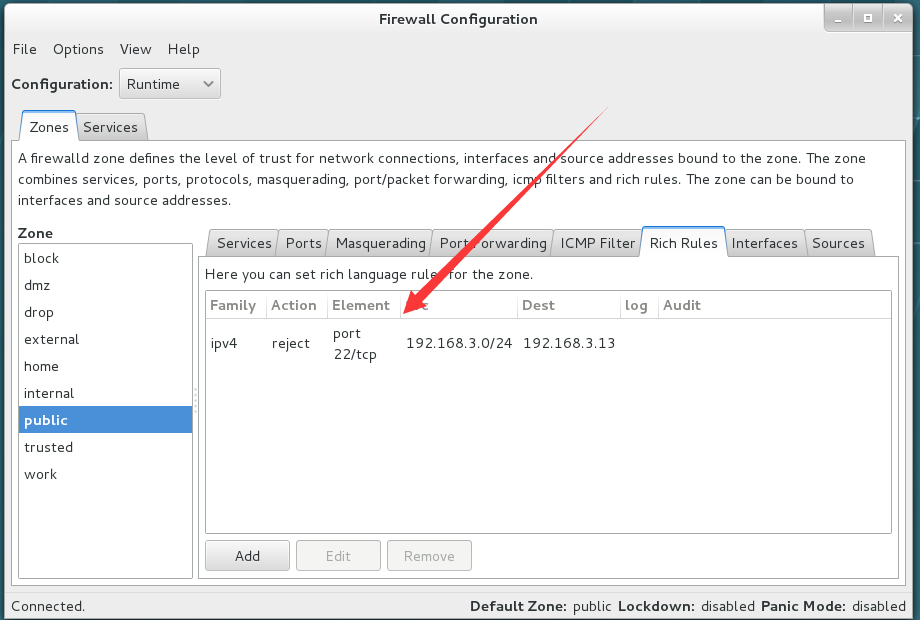
测试设置效果:
[root@linuxprobe ~]# ifconfig | head -n 5 ## 登录另一台主机,查看IP
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.14 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::d7fe:9dfc:42ec:c255 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:ef:86:f2 txqueuelen 1000 (Ethernet)
RX packets 3372 bytes 3485851 (3.3 MiB)
[root@linuxprobe ~]# ssh 192.168.3.13 ## 测试远程连接
ssh: connect to host 192.168.3.13 port 22: No route to host
[root@linuxprobe ~]# ifconfig |head -n 5 ## 登录另一台主机,查看IP
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.8 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::54f8:bbf7:7760:3745 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:8d:79:f8 txqueuelen 1000 (Ethernet)
RX packets 299 bytes 35971 (35.1 KiB)
[root@linuxprobe ~]# ssh 192.168.3.13 ## 测试远程连接
ssh: connect to host 192.168.3.13 port 22: No route to host
删除该设置进行测试:
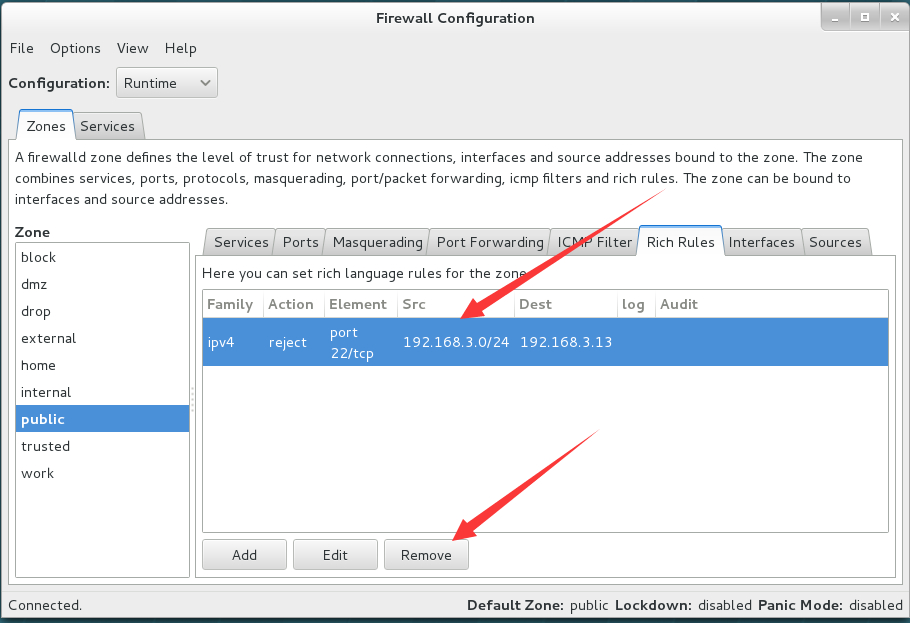
测试:
[root@linuxprobe ~]# ifconfig | head -n 5 ## 登录另一主机,查看IP
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.14 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::d7fe:9dfc:42ec:c255 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:ef:86:f2 txqueuelen 1000 (Ethernet)
RX packets 427 bytes 61356 (59.9 KiB)
[root@linuxprobe ~]# ssh 192.168.3.13 ## 远程测试,通过
root@192.168.3.13's password:
Last login: Sat Oct 31 19:13:11 2020 from 192.168.3.14
[root@linuxprobe ~]# ifconfig | head -n 5 ## 登录另一主机,查看IP
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.3.8 netmask 255.255.255.0 broadcast 192.168.3.255
inet6 fe80::54f8:bbf7:7760:3745 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:8d:79:f8 txqueuelen 1000 (Ethernet)
RX packets 594 bytes 68784 (67.1 KiB)
[root@linuxprobe ~]# ssh 192.168.3.13 ## 远程测试,通过
root@192.168.3.13's password:
Last login: Sat Oct 31 19:13:41 2020 from 192.168.3.14






【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· 基于Microsoft.Extensions.AI核心库实现RAG应用
· Linux系列:如何用heaptrack跟踪.NET程序的非托管内存泄露
· 开发者必知的日志记录最佳实践
· SQL Server 2025 AI相关能力初探
· Linux系列:如何用 C#调用 C方法造成内存泄露
· 震惊!C++程序真的从main开始吗?99%的程序员都答错了
· 【硬核科普】Trae如何「偷看」你的代码?零基础破解AI编程运行原理
· 单元测试从入门到精通
· 上周热点回顾(3.3-3.9)
· winform 绘制太阳,地球,月球 运作规律