Kubernetes学习之路(十九)之Kubernetes dashboard认证访问
Dashboard:https://github.com/kubernetes/dashboard
一、Dashboard部署
由于需要用到k8s.gcr.io/kubernetes-dashboard-amd64:v1.10.0,这里有2种方式进行pull 镜像。docker search该镜像名称,直接pull,再重新进行tag;另外一种方式是通过谷歌容器镜像拉取。
[root@k8s-node01 ~]# docker pull siriuszg/kubernetes-dashboard-amd64 [root@k8s-node01 ~]# docker tag siriuszg/kubernetes-dashboard-amd64:latest k8s.gcr.io/kubernetes-dashboard-amd64:v1.10.0 或者是 [root@k8s-node01 ~]# docker pull mirrorgooglecontainers/kubernetes-dashboard-amd64:v1.10.0
再看其部署的过程:
[root@k8s-master ~]# kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/master/src/deploy/recommended/kubernetes-dashboard.yaml secret/kubernetes-dashboard-certs created serviceaccount/kubernetes-dashboard created role.rbac.authorization.k8s.io/kubernetes-dashboard-minimal created rolebinding.rbac.authorization.k8s.io/kubernetes-dashboard-minimal created deployment.apps/kubernetes-dashboard created service/kubernetes-dashboard created [root@k8s-master ~]# kubectl get pods -n kube-system NAME READY STATUS RESTARTS AGE coredns-78fcdf6894-nmcmz 1/1 Running 1 54d coredns-78fcdf6894-p5pfm 1/1 Running 1 54d etcd-k8s-master 1/1 Running 2 54d kube-apiserver-k8s-master 1/1 Running 9 54d kube-controller-manager-k8s-master 1/1 Running 5 54d kube-flannel-ds-n5c86 1/1 Running 1 54d kube-flannel-ds-nrcw2 1/1 Running 1 52d kube-flannel-ds-pgpr7 1/1 Running 5 54d kube-proxy-glzth 1/1 Running 1 52d kube-proxy-rxlt7 1/1 Running 2 54d kube-proxy-vxckf 1/1 Running 4 54d kube-scheduler-k8s-master 1/1 Running 3 54d kubernetes-dashboard-767dc7d4d-n4clq 1/1 Running 0 3s [root@k8s-master ~]# kubectl get svc -n kube-system NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE kube-dns ClusterIP 10.96.0.10 <none> 53/UDP,53/TCP 54d kubernetes-dashboard ClusterIP 10.105.204.4 <none> 443/TCP 30m [root@k8s-master ~]# kubectl patch svc kubernetes-dashboard -p '{"spec":{"type":"NodePort"}}' -n kube-system #以打补丁方式修改dasboard的访问方式 service/kubernetes-dashboard patched [root@k8s-master ~]# kubectl get svc -n kube-system NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE kube-dns ClusterIP 10.96.0.10 <none> 53/UDP,53/TCP 54d kubernetes-dashboard NodePort 10.105.204.4 <none> 443:32645/TCP 31m
浏览器访问:https://192.168.56.12:32645,如图:这里需要注意的是谷歌浏览器会禁止不安全证书访问,建议使用火狐浏览器,并且需要在高级选项中添加信任
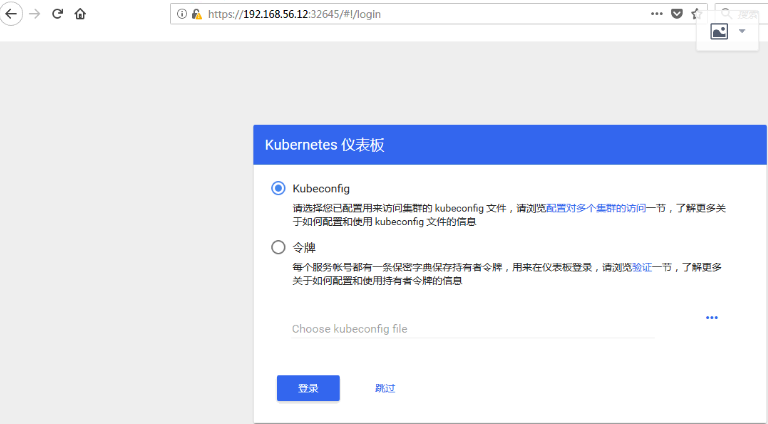
在k8s中 dashboard可以有两种访问方式:kubeconfig(HTTPS)和token(http)
1、token认证
(1)创建dashboard专用证书
[root@k8s-master pki]# (umask 077;openssl genrsa -out dashboard.key 2048) Generating RSA private key, 2048 bit long modulus .....................................................................................................+++ ..........................+++ e is 65537 (0x10001)
(2)证书签署请求
[root@k8s-master pki]# openssl req -new -key dashboard.key -out dashboard.csr -subj "/O=magedu/CN=dashboard" [root@k8s-master pki]# openssl x509 -req -in dashboard.csr -CA ca.crt -CAkey ca.key -CAcreateserial -out dashboard.crt -days 365 Signature ok subject=/O=magedu/CN=dashboard Getting CA Private Key
(3)定义令牌方式仅能访问default名称空间
[root@k8s-master pki]# kubectl create secret generic dashboard-cert -n kube-system --from-file=./dashboard.crt --from-file=dashboard.key=./dashboard.key #secret创建 secret/dashboard-cert created [root@k8s-master pki]# kubectl get secret -n kube-system |grep dashboard dashboard-cert Opaque 2 1m kubernetes-dashboard-certs Opaque 0 3h kubernetes-dashboard-key-holder Opaque 2 3h kubernetes-dashboard-token-jpbgw kubernetes.io/service-account-token 3 3h [root@k8s-master pki]# kubectl create serviceaccount def-ns-admin -n default #创建serviceaccount serviceaccount/def-ns-admin created [root@k8s-master pki]# kubectl create rolebinding def-ns-admin --clusterrole=admin --serviceaccount=default:def-ns-admin #service account账户绑定到集群角色admin rolebinding.rbac.authorization.k8s.io/def-ns-admin created [root@k8s-master pki]# kubectl describe secret def-ns-admin-token-k9fz9 #查看def-ns-admin这个serviceaccount的token Name: def-ns-admin-token-k9fz9 Namespace: default Labels: <none> Annotations: kubernetes.io/service-account.name=def-ns-admin kubernetes.io/service-account.uid=56ed901c-d042-11e8-801a-000c2972dc1f Type: kubernetes.io/service-account-token Data ==== ca.crt: 1025 bytes namespace: 7 bytes token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1rOWZ6OSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI1NmVkOTAxYy1kMDQyLTExZTgtODAxYS0wMDBjMjk3MmRjMWYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.QfB5RR19nBv4-kFYyzW5-2n5Ksg-kON8lU18-COLBNfObQTDHs926m4k9f_5bto4YGncYi7sV_3oEec8ouW1FRjJWfY677L1IqIlwcuqc-g0DUo21zkjY_s3Lv3JSb_AfXUbZ7VTeWOhvwonqfK8uriGO1-XET-RBk1CE4Go1sL7X5qDgPjNO1g85D9IbIZG64VygplT6yZNc-b7tLNn_O49STthy6J0jdNk8lYxjy6UJohoTicy2XkZMHp8bNPBj9RqGqMSnnJxny5WO3vHxYAodKx7h6w-PtuON84lICnhiJ06RzsWjZfdeaQYg4gCZmd2J6Hdq0_K32n3l3kFLg
将该token复制后,填入验证,要知道的是,该token认证仅可以查看default名称空间的内容,如下图:

2、kubeconfig认证
(1)配置def-ns-admin的集群信息
[root@k8s-master pki]# kubectl config set-cluster kubernetes --certificate-authority=./ca.crt --server="https://192.168.56.11:6443" --embed-certs=true --kubeconfig=/root/def-ns-admin.conf Cluster "kubernetes" set.
(2)使用token写入集群验证
[root@k8s-master ~]# kubectl config set-credentials -h #认证的方式可以通过crt和key文件,也可以使用token进行配置,这里使用tonken Usage: kubectl config set-credentials NAME [--client-certificate=path/to/certfile] [--client-key=path/to/keyfile] [--token=bearer_token] [--username=basic_user] [--password=basic_password] [--auth-provider=provider_name] [--auth-provider-arg=key=value] [options] [root@k8s-master pki]# kubectl describe secret def-ns-admin-token-k9fz9 Name: def-ns-admin-token-k9fz9 Namespace: default Labels: <none> Annotations: kubernetes.io/service-account.name=def-ns-admin kubernetes.io/service-account.uid=56ed901c-d042-11e8-801a-000c2972dc1f Type: kubernetes.io/service-account-token Data ==== ca.crt: 1025 bytes namespace: 7 bytes token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1rOWZ6OSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI1NmVkOTAxYy1kMDQyLTExZTgtODAxYS0wMDBjMjk3MmRjMWYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.QfB5RR19nBv4-kFYyzW5-2n5Ksg-kON8lU18-COLBNfObQTDHs926m4k9f_5bto4YGncYi7sV_3oEec8ouW1FRjJWfY677L1IqIlwcuqc-g0DUo21zkjY_s3Lv3JSb_AfXUbZ7VTeWOhvwonqfK8uriGO1-XET-RBk1CE4Go1sL7X5qDgPjNO1g85D9IbIZG64VygplT6yZNc-b7tLNn_O49STthy6J0jdNk8lYxjy6UJohoTicy2XkZMHp8bNPBj9RqGqMSnnJxny5WO3vHxYAodKx7h6w-PtuON84lICnhiJ06RzsWjZfdeaQYg4gCZmd2J6Hdq0_K32n3l3kFLg 这里的token是base64编码,此处需要进行解码操作 [root@k8s-master ~]# kubectl get secret def-ns-admin-token-k9fz9 -o jsonpath={.data.token} |base64 -d eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1rOWZ6OSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI1NmVkOTAxYy1kMDQyLTExZTgtODAxYS0wMDBjMjk3MmRjMWYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.QfB5RR19nBv4-kFYyzW5-2n5Ksg-kON8lU18-COLBNfObQTDHs926m4k9f_5bto4YGncYi7sV_3oEec8ouW1FRjJWfY677L1IqIlwcuqc-g0DUo21zkjY_s3Lv3JSb_AfXUbZ7VTeWOhvwonqfK8uriGO1-XET-RBk1CE4Go1sL7X5qDgPjNO1g85D9IbIZG64VygplT6yZNc-b7tLNn_O49STthy6J0jdNk8lYxjy6UJohoTicy2XkZMHp8bNPBj9RqGqMSnnJxny5WO3vHxYAodKx7h6w-PtuON84lICnhiJ06RzsWjZfdeaQYg4gCZmd2J6Hdq0_K32n3l3kFLg 配置token信息 [root@k8s-master ~]# kubectl config set-credentials def-ns-admin --token=eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1rOWZ6OSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI1NmVkOTAxYy1kMDQyLTExZTgtODAxYS0wMDBjMjk3MmRjMWYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.QfB5RR19nBv4-kFYyzW5-2n5Ksg-kON8lU18-COLBNfObQTDHs926m4k9f_5bto4YGncYi7sV_3oEec8ouW1FRjJWfY677L1IqIlwcuqc-g0DUo21zkjY_s3Lv3JSb_AfXUbZ7VTeWOhvwonqfK8uriGO1-XET-RBk1CE4Go1sL7X5qDgPjNO1g85D9IbIZG64VygplT6yZNc-b7tLNn_O49STthy6J0jdNk8lYxjy6UJohoTicy2XkZMHp8bNPBj9RqGqMSnnJxny5WO3vHxYAodKx7h6w-PtuON84lICnhiJ06RzsWjZfdeaQYg4gCZmd2J6Hdq0_K32n3l3kFLg --kubeconfig=/root/def-ns-admin.conf User "def-ns-admin" set.
(3)配置上下文和当前上下文
[root@k8s-master ~]# kubectl config set-context def-ns-admin@kubernetes --cluster=kubernetes --user=def-ns-admin --kubeconfig=/root/def-ns-admin.conf Context "def-ns-admin@kubernetes" created.
[root@k8s-master ~]# kubectl config use-context def-ns-admin@kubernetes --kubeconfig=/root/def-ns-admin.conf Switched to context "def-ns-admin@kubernetes". [root@k8s-master ~]# kubectl config view --kubeconfig=/root/def-ns-admin.conf apiVersion: v1 clusters: - cluster: certificate-authority-data: REDACTED server: https://192.168.56.11:6443 name: kubernetes contexts: - context: cluster: kubernetes user: def-ns-admin name: def-ns-admin@kubernetes current-context: def-ns-admin@kubernetes kind: Config preferences: {} users: - name: def-ns-admin user: token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJkZWZhdWx0Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZWNyZXQubmFtZSI6ImRlZi1ucy1hZG1pbi10b2tlbi1rOWZ6OSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZWYtbnMtYWRtaW4iLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiI1NmVkOTAxYy1kMDQyLTExZTgtODAxYS0wMDBjMjk3MmRjMWYiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6ZGVmYXVsdDpkZWYtbnMtYWRtaW4ifQ.QfB5RR19nBv4-kFYyzW5-2n5Ksg-kON8lU18-COLBNfObQTDHs926m4k9f_5bto4YGncYi7sV_3oEec8ouW1FRjJWfY677L1IqIlwcuqc-g0DUo21zkjY_s3Lv3JSb_AfXUbZ7VTeWOhvwonqfK8uriGO1-XET-RBk1CE4Go1sL7X5qDgPjNO1g85D9IbIZG64VygplT6yZNc-b7tLNn_O49STthy6J0jdNk8lYxjy6UJohoTicy2XkZMHp8bNPBj9RqGqMSnnJxny5WO3vHxYAodKx7h6w-PtuON84lICnhiJ06RzsWjZfdeaQYg4gCZmd2J6Hdq0_K32n3l3kFLg
将/root/def-ns-admin.conf文件发送到宿主机,浏览器访问时选择Kubeconfig认证,载入该配置文件,点击登陆,即可实现访问,如图:

二、总结
1、部署dashboard:
kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/master/src/deploy/recommended/kubernetes-dashboard.yaml
2、将Service改为Node Port方式进行访问:
kubectl patch svc kubernetes-dashboard -p '{"spec":{"type":"NodePort"}}' -n kube-system
3、访问认证:
认证时的账号必须为ServiceAccount:其作用是被dashboard pod拿来由kubenetes进行认证;认证方式有2种:
token:
- (1)创建ServiceAccount,根据其管理目标,使用rolebinding或clusterbinding绑定至合理的role或clusterrole;
- (2)获取此ServiceAccount的secret,查看secret的详细信息,其中就有token;
- (3)复制token到认证页面即可登录。
kubeconfig:把ServiceAccount的token封装为kubeconfig文件
- (1)创建ServiceAccount,根据其管理目标,使用rolebinding或clusterbinding绑定至合理的role或clusterrole;
- (2)kubectl get secret |awk '/^ServiceAccount/{print $1}'
- KUBE_TOKEN=$(kubectl get secret SERVICEACCOUNT_SECRET_NAME -o jsonpath={.data.token} | base64 -d)
- (3)生成kubeconfig文件
kubectl config set-cluster kubectl config set-credentials NAME --token=$KUBE_TOKEN kubectl config set-context kubectl config use-context
Don't forget the beginner's mind


 浙公网安备 33010602011771号
浙公网安备 33010602011771号