CA认证过程及https实现方法
CA认证过程及https实现方法
一、CA认证过程
CA概述:Certificate Authority的缩写,通常翻译成认证权威或者认证中心,主要用途是为用户发放数字证书。CA认证的流程和公安局派出所颁发身份证的流程一样
认证中心(CA)的功能有:证书发放、证书更新、证书撤销和证书验证。
CA证书作用:身份认证,实现数据的不可否认性。
证书请求文件:CSR是Cerificate Signing Request的英文缩写,即证书请求文件,也就是证书申请者在申请数字证书时由CSP(加密服务提供者)在生成私钥的同时也生成证书请求文件,证书申请者只要把CSR文件提交给证书颁发机构后,证书颁发机构使用其根证书的私钥签名就生成了证书文件,也就是颁发给用户的证书。
1.1:证书签名过程
1、 生成请求文件
2、 CA确认申请者的身份真实性
3、 CA使用根证书的私钥加密请求文件,生成证书
4、 把证书传给申请者
1.2 用户使用CA证书确认服务器身份过程(K7 CA认证服务器 k6 是申请方)
1、请求文件发给k7CA认证中心
2、CA认证 (用CA的私钥加密k6的请求文件), 得到加密后的文件,这个文件就是k6的证书 ),CA认证中心颁发给k6加密后的数字证书
3、用户访问k6并向k6索要数字证书
4、用户拿到数字证书后,用浏览器中CA的公钥解密k6的证书,解开后得到k6的公钥和标识(主机名,国家,省,组织等信息),从而确认k6的身份。
二、搭建CA认证中心
搭建CA认证中心
1、安装CA认证软件包中心:
[root@k7 ~]# rpm -qf `which openssl`
openssl-1.0.2k-16.el7_6.1.x86_64
2、配置一个自己的CA认证中心。生成CA的根证书和私钥。
[root@k7 ~]# vim /etc/pki/tls/openssl.cnf
改:172 basicConstraints=CA:FALSE
为:172 basicConstraints=CA:TRUE #让自己成为CA认证中心
3、生成CA的公钥证书和私钥。
[root@k7 ~]# /etc/pki/tls/misc/CA -h #查看帮助
usage: /etc/pki/tls/misc/CA -newcert|-newreq|-newreq-nodes|-newca|-sign|-verify
选项 :
-newcert 新证书
-newreq 新请求
-newreq-nodes 新请求节点
-newca 新的CA证书
-sign 签证
-verify 验证
[root@k7 ~]# /etc/pki/tls/misc/CA -newca
CA certificate filename (or enter to create)
Making CA certificate ...
Generating a 2048 bit RSA private key
...............................................................+++
.......+++
writing new private key to '/etc/pki/CA/private/./cakey.pem'
Enter PEM pass phrase:
Verifying - Enter PEM pass phrase:
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:sichuan
Locality Name (eg, city) [Default City]:chengdu
Organization Name (eg, company) [Default Company Ltd]:kezibky
Organizational Unit Name (eg, section) []:IT
Common Name (eg, your name or your server's hostname) []:kezibky.com
Email Address []:keizibky@163.com
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/./cakey.pem:
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number:
ca:7e:0b:7a:b3:65:5a:f3
Validity
Not Before: Sep 12 06:40:28 2019 GMT
Not After : Sep 11 06:40:28 2022 GMT
Subject:
countryName = CN
stateOrProvinceName = sichuan
organizationName = kezibky
organizationalUnitName = IT
commonName = kezibky.com
emailAddress = keizibky@163.com
X509v3 extensions:
X509v3 Subject Key Identifier:
11:13:F7:A1:F6:9E:DA:3F:52:A1:4F:D0:BC:D5:F6:B4:78:C9:FB:E7
X509v3 Authority Key Identifier:
keyid:11:13:F7:A1:F6:9E:DA:3F:52:A1:4F:D0:BC:D5:F6:B4:78:C9:FB:E7
X509v3 Basic Constraints:
CA:TRUE
Certificate is to be certified until Sep 11 06:40:28 2022 GMT (1095 days)
Write out database with 1 new entries
Data Base Updated
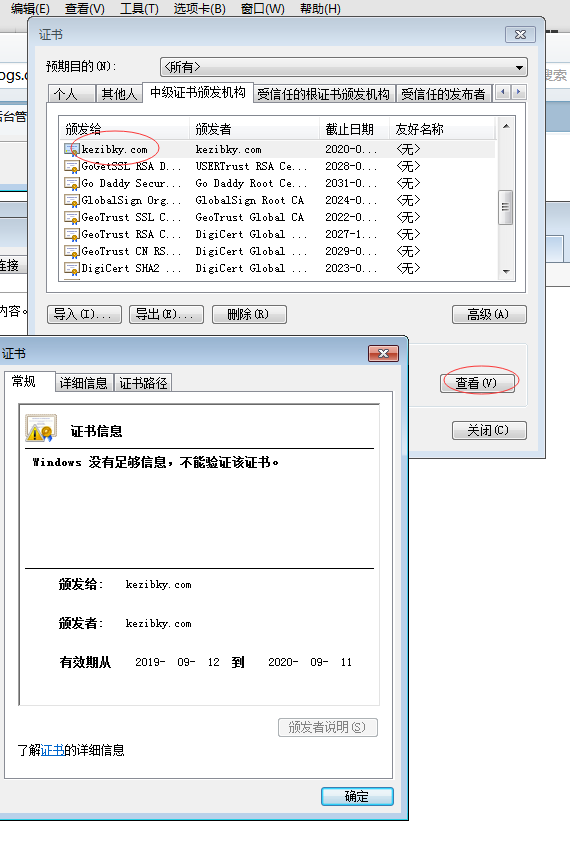
4、查看生成的CA根证书,根证书中包括CA公钥
[root@k7 ~]# vim /etc/pki/CA/cacert.pem
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
ca:7e:0b:7a:b3:65:5a:f3
Signature Algorithm: sha256WithRSAEncryption
Issuer: C=CN, ST=sichuan, O=kezibky, OU=IT, CN=kezibky.com/emailAddress=keizibky@163.com
Validity
Not Before: Sep 12 06:40:28 2019 GMT
Not After : Sep 11 06:40:28 2022 GMT
Subject: C=CN, ST=sichuan, O=kezibky, OU=IT, CN=kezibky.com/emailAddress=keizibky@163.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:be:ee:c5:e0:5e:8a:4c:8a:7e:2d:e2:d4:53:a9:
6c:b3:36:f6:f3:1f:00:cb:b6:a2:88:67:af:8c:03:
4e:56:a5:3d:79:eb:d8:0e:f1:d0:8c:d6:b8:a8:8f:
11:ae:ec:c6:fd:6a:a9:cf:bf:fc:bd:c9:6b:55:fb:
ea:88:20:e7:ca:58:e3:22:6d:4d:f5:ae:d2:6e:e9:
81:fd:16:38:d4:0b:7b:85:60:5c:0c:c9:9b:6d:2a:
8c:26:01:42:24:18:1c:46:73:4b:9d:98:58:f0:37:
cc:29:ae:db:e5:40:dc:26:d6:4c:fc:c8:ff:d4:6e:
aa:f4:21:c7:54:45:ae:5a:15:96:c8:b6:b4:b7:66:
25:f4:35:b7:5a:88:39:95:16:5d:77:ac:86:7d:f2:
1d:b4:ec:97:1b:21:a2:7a:35:fd:b1:23:11:b2:80:
80:49:9b:66:73:45:94:7a:bf:bb:9c:9b:bd:9f:e7:
e4:3d:77:8e:91:9b:ec:81:c2:90:98:f9:7d:e5:75:
77:51:9d:7d:96:58:52:4c:84:88:a3:92:b5:b3:4b:
dc:06:96:c1:64:12:ad:6d:df:f8:5d:71:46:14:96:
"/etc/pki/CA/cacert.pem" 81L, 4465C
5、查看根证书的私钥
[root@k7 ~]# vim /etc/pki/CA/private/cakey.pem
-----BEGIN ENCRYPTED PRIVATE KEY-----
MIIFDjBABgkqhkiG9w0BBQ0wMzAbBgkqhkiG9w0BBQwwDgQITCjptF6WslUCAggA
MBQGCCqGSIb3DQMHBAhl/0pgVa0ZGASCBMilfCLbo7qiXVpZKj6levYLA611Pa4a
Wl5DlOdZ/AdIjROvYS7Va5lYdj5jWfky0Tyz6+XNA08xNugPTmLPcmvR0GeSJPwe
NIgpzSqFPaT+d1K1FJ7abKZgPvfcIOhejX+sST9h75KTgkN8XruJHeDrFclg1z0C
804g9Nb7SElDmIfwpxDf1glngwW+hqkTcZUInI92pslIGQ8uuXbXYa+l5ZCKpfbL
A4b0avxA6D5ktEa+WPcuzn10ShQH4oPSYwteq8+l7ODXheqgrLSJJov4HyB+tk+G
三、在apache上搭建https
基于apache搭建https的整体流程如下:
(1)、在k6上安装httpd
(2)、k6生成证书请求文件,发给k7 CA认证中心进行签名,k3下发证书 给k6
(3)、把证书和httpd相结合,实现https
(4)、测试https认证效果
2、安装:httpd web服务器
[root@k6 ~]# yum install httpd -y
[root@k6 ~]# vim /etc/httpd/conf/httpd.conf
改:95 #ServerName www.example.com:80 #指定ServerName
为:95 ServerName 10.27.17.36:80
[root@k6 ~]# systemctl start httpd
[root@k6 ~]# iptables -F
3、k6生成证书请求文件,获得证书
[root@k6 ~]# openssl genrsa -h #查看帮助
生一个私钥密钥(此时还没有生成公钥):
[root@k6 ~]# openssl genrsa -des3 -out /etc/httpd/conf.d/server.key
参数:-des3 encrypt the generated key with DES in ede cbc mode (168 bit key) #加密 一下私钥
Generating RSA private key, 512 bit long modulus
.....++++++++++++
..............................++++++++++++
e is 65537 (0x10001)
Enter pass phrase for /etc/httpd/conf.d/server.key:123456 #输入保护私钥的密码,保护私 钥时,使用的加密算法是 -des3
Verifying - Enter pass phrase for /etc/httpd/conf.d/server.key: 123456
注: 有私钥可以推出来公钥,但是公钥不可以推出私钥。公钥由私钥生成
4、使用私钥生成证书请求文件
[root@k6 ~]# openssl req -new -key /etc/httpd/conf.d/server.key -out /server.csr #注意后期添加的国家,省,组织等信息要和CA保持一致
Enter pass phrase for /etc/httpd/conf.d/server.key:123456 #输入私钥的密码
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:sichuan
Locality Name (eg, city) [Default City]:chengdu
Organization Name (eg, company) [Default Company Ltd]:kezibky
Organizational Unit Name (eg, section) []:IT
Common Name (eg, your name or your server's hostname) []:kezibky.cn
#这里要求输入的CommonName必须与通过浏览器访问您网站的 URL 完全相同,否则用户会发 现您服务器证书的通用名与站点的名字不匹配,用户就会怀疑您的证书的真实性。可以使域名也可以 使IP地址。
Email Address []:kezibky@163.com
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []: #不输密码直接回车
An optional company name []:
注:证书请求文件中有k6的公钥。 这个公钥是在生成证书请求文件时,通过指定的私钥 /etc/httpd/conf.d/server.key生成的。
常识: 通过私钥可以生成公钥的,通过公钥不可以推出来私钥。
5、将证书请求文件发给CA服务器:
[root@k6 ~]# scp /server.csr 10.27.17.36/tmp/
6、CA签名
[root@k7 ~]# openssl ca -h
[root@k7 ~]# openssl ca -keyfile /etc/pki/CA/private/cakey.pem -cert /etc/pki/CA/cacert.pem -in /tmp/server.csr -out /server.crt
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/cakey.pem:
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number:
ca:7e:0b:7a:b3:65:5a:f4
Validity
Not Before: Sep 12 07:28:18 2019 GMT
Not After : Sep 11 07:28:18 2020 GMT
Subject:
countryName = CN
stateOrProvinceName = sichuan
organizationName = kezibky
organizationalUnitName = It
commonName = kezibky.com
emailAddress = kezibky@163.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:TRUE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
21:A0:46:0A:00:96:74:3D:62:12:30:66:19:E1:66:9B:39:4E:74:6D
X509v3 Authority Key Identifier:
keyid:11:13:F7:A1:F6:9E:DA:3F:52:A1:4F:D0:BC:D5:F6:B4:78:C9:FB:E7
Certificate is to be certified until Sep 11 07:28:18 2020 GMT (365 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
7、将证书复制到k6
[root@k7 /]# scp server.crt 10.27.17.36:/
四、使用证书实现https
.4.1 SSL四次握手实现安全传输数据
1、SSL概述:(Secure Socket Layer)安全套接字层,通过一种机制在互联网上提供密钥传输。其主要目标是保证两个应用间通信数据的保密性和可靠性,可在服务器端和用户端同时支持的一种加密算法。目前主流版本SSLV2、SSLV3(常用)。
注:SSL作用,可以让你在一个不安全的公网环境中,安全传输你的密钥。
SSL四次握手安全传输流程如下:
C(client客户端) ------------------------------> S(server服务端)
(1)、 客户端请求一个安全的会话,协商加密算法
C <------------------------------------------------- S
(2)、服务端将自己的证书传给客户端
C -------------------------------------------------> S
(3)、客户端用浏览中存放CA的根证书检测k6证书,确认k6是我要访问的网站。
客户端使用CA根证书中的公钥解密k6的证书,从而得到k6的公钥;
然后客户端生成一把对称的加密密钥,用k6的公钥加密这个对称加密的密钥发给k6。 后期使用对称密钥加密数据
C <------------------------------------------------> S
(4)、k6使用私钥解密,得到对称加密的密钥。从而,使用对称加密密钥来进行安全快速传输数据。这里使用对称加密数据,是因为对称加密和解密速度快
总结SSL四次握手流程整体分两个过程:
过程1: 确认身份;过程2:生成一把对称加密密钥,传输数据。
4.2 在k6上配置HTTPS web服务器
1、安装SSL模块
[root@k6 ~]# yum install mod_ssl -y
2、配置apache加载证书文件
[root@k6 ~]# cp /server.crt /etc/httpd/conf.d/ #复制证书
[root@k6 ~]# ls /etc/httpd/conf.d/server.key #查看私钥
/etc/httpd/conf.d/server.key
[root@k6 ~]# vim /etc/httpd/conf.d/ssl.conf
改:100 SSLCertificateFile /etc/pki/tls/certs/localhost.crt
为:100 SSLCertificateFile /etc/httpd/conf.d/server.crt
改:107 SSLCertificateKeyFile /etc/pki/tls/private/localhost.key
为:107 SSLCertificateKeyFile /etc/httpd/conf.d/server.key
3、启动服务:
[root@k6 ~]# systemctl restart httpd
Enter SSL pass phrase for k6.cn:443 (RSA) : 123456 #httpd私钥密码
4、测试https,查看端口
[root@k6 ~]# netstat -antup | grep 443
tcp 0 0 :::443 :::* LISTEN 5138/httpd
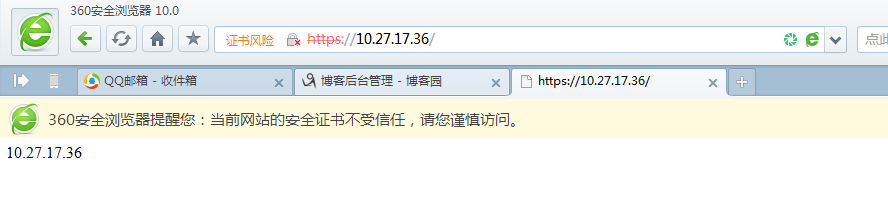
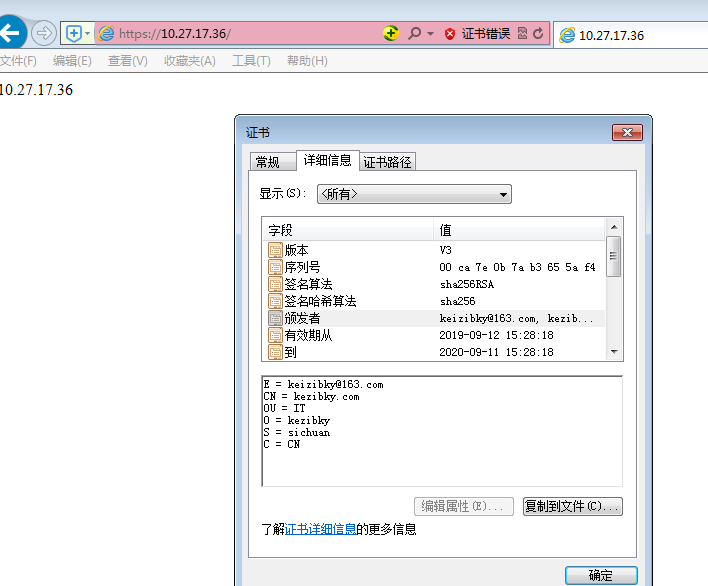
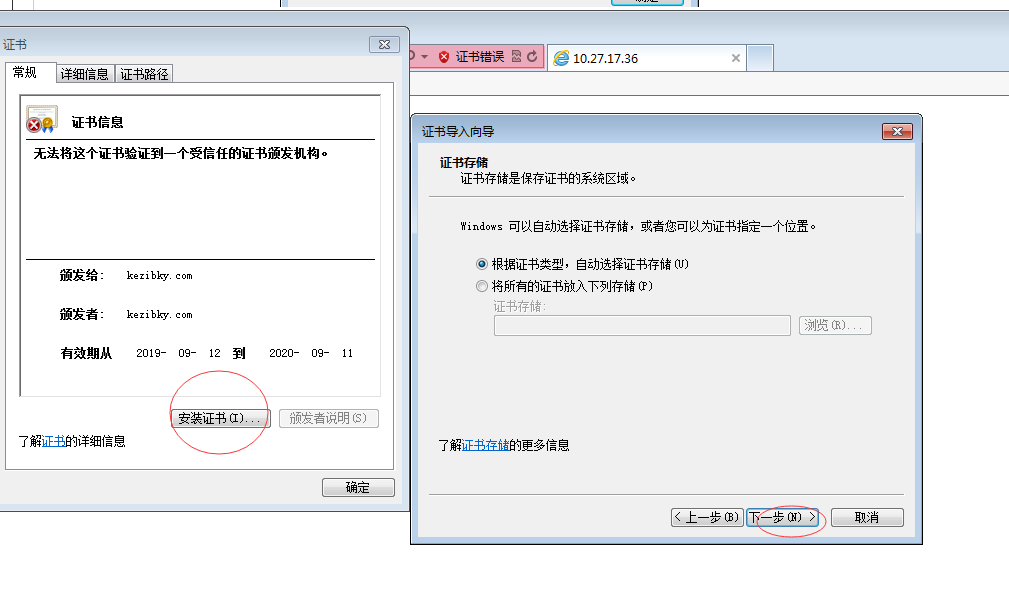
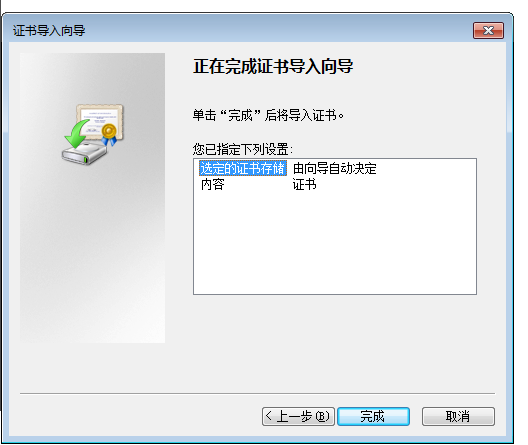
5、通过浏览器测试https效果
访问:https://10.27.17.36/


 浙公网安备 33010602011771号
浙公网安备 33010602011771号