[网络/Java EE/Web]Tomcat/Nginx中配置全局的安全响应头(header)——X-Frame-Options / X-XSS-Protection / X-Content-Options
0 序
- 特别说明:本文针对安装了Tomcat 应用服务 或/和 Nginx(代理Tomcat)的情况,可分别查阅Step1、Step2。
如只安装了其中一个组件,则跳过对应章节即可。
Step1 配置Tomcat
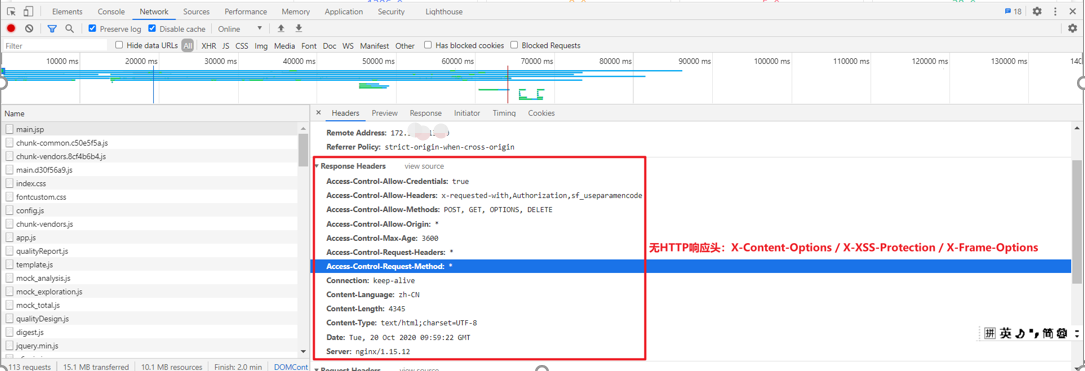
step1.1 查看是否已配置目标的HTTP网络安全头
- 方式1 – Tomcat / conf/web.xml
cat /opt/myTomcat/conf/web.xml | grep --color=auto -C 10 -i "httpHeaderSecurity"

- 方式2 查看Tomcat的任一Web HTTP网页/请求
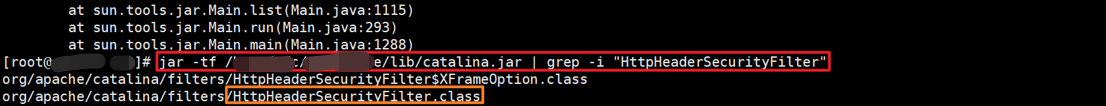
step1.2 确认Tomcat服务器中(catalina.jar)是否存在HttpHeaderSecurityFilter类
[root@hostName testUser]# jar -tf /opt/myTomcat/lib/catalina.jar | grep -i "HttpHeaderSecurityFilter"
org/apache/catalina/filters/HttpHeaderSecurityFilter$XFrameOption.class
org/apache/catalina/filters/HttpHeaderSecurityFilter.class
step1.3 利用HttpHeaderSecurityFilter为Tomcat配置全局的HTTP安全响应头
注:配置后,Tomcat会自动加载新的配置,故 无需重启Tomcat
vi /opt/myTomcat/conf/web.xml
(文件内加入如下配置)
- SAMEORIGIN 版配置
<filter>
<filter-name>httpHeaderSecurity</filter-name>
<filter-class>org.apache.catalina.filters.HttpHeaderSecurityFilter</filter-class>
<async-supported>true</async-supported>
<init-param>
<param-name>antiClickJackingEnabled</param-name> <!-- X-Frame-Options 默认(DENY) -->
<param-value>true</param-value>
</init-param>
<init-param>
<param-name>antiClickJackingOption</param-name> <!-- X-Frame-Options 默认(DENY) - org.apache.catalina.filters.HttpHeaderSecurityFilter 的内部枚举类 enum XFrameOption { DENY("DENY"),SAME_ORIGIN("SAMEORIGIN"),ALLOW_FROM("ALLOW-FROM"); } -->
<param-value>SAMEORIGIN</param-value>
</init-param>
<init-param>
<param-name>blockContentTypeSniffingEnabled</param-name> <!-- X-Content-Type-Options 默认: true(nosniff) -->
<param-value>true</param-value>
</init-param>
<init-param>
<param-name>xssProtectionEnabled</param-name> <!-- X-XSS-Protection 默认: true(1; mode=block) -->
<param-value>false</param-value>
</init-param>
</filter>
<filter-mapping>
<filter-name>httpHeaderSecurity</filter-name>
<url-pattern>/*</url-pattern>
<dispatcher>REQUEST</dispatcher>
</filter-mapping>
- ALLOW-FROM 版
<filter>
<filter-name>httpHeaderSecurity</filter-name>
<filter-class>org.apache.catalina.filters.HttpHeaderSecurityFilter</filter-class>
<async-supported>true</async-supported>
<init-param>
<param-name>antiClickJackingEnabled</param-name> <!-- X-Frame-Options 默认(DENY) -->
<param-value>true</param-value>
</init-param>
<init-param>
<param-name>antiClickJackingOption</param-name>
<!-- X-Frame-Options 默认(DENY) -
org.apache.catalina.filters.HttpHeaderSecurityFilter 的内部枚举类 enum XFrameOption { DENY("DENY"),SAME_ORIGIN("SAMEORIGIN"),ALLOW_FROM("ALLOW-FROM"); } -->
<param-value>ALLOW-FROM</param-value>
</init-param>
<init-param>
<param-name>antiClickJackingUri</param-name>
<!-- <param-value>http://10.xx.yy.148:18460</param-value> -->
<param-value>[http://10.xx.yy.148:18460][http://10.xx.yy.149:8085]</param-value>
</init-param>
</filter>
<filter-mapping>
<filter-name>httpHeaderSecurity</filter-name>
<url-pattern>/*</url-pattern>
<dispatcher>REQUEST</dispatcher>
</filter-mapping>
【备注】
配置http的响应头信息:属性名 X-Frame-Options / X-XSS-Protection / X-Content-Options
- https://blog.csdn.net/liangpingguo/article/details/86703284
- https://blog.csdn.net/li_wen_jin/article/details/88353763
1.此配置将即时生效,Tomcat会实时加载,故 配置完成后,无需重启
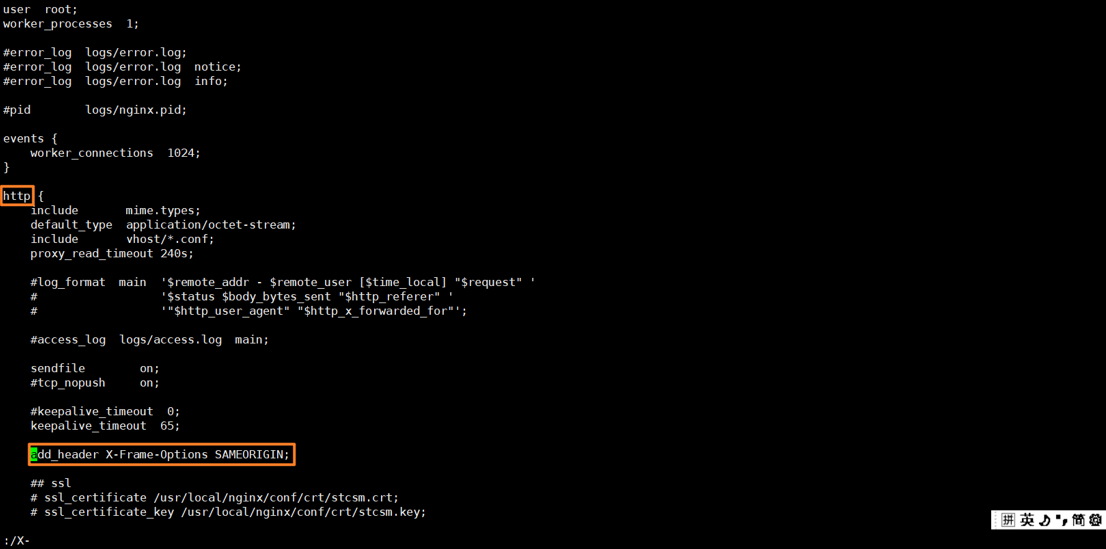
Step2 配置Nginx
step2.1 配置Nginx的HTTP安全头
# vi /usr/local/nginx/conf/nginx.conf
在http(或server)模块内添加如下内容:
add_header X-Frame-Options "SAMEORIGIN"; #或 add_header X-Frame-Options SAMEORIGIN;
add_header X-XSS-Protection "1; mode=block";
add_header X-Content-Type-Options "nosniff"; # 禁止嗅探文件类型
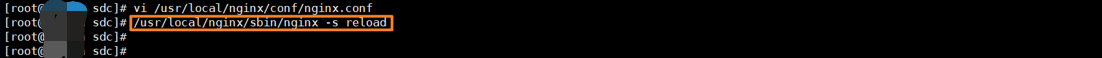
step2.2 添加后,重载nginx配置
注:重载(reload)操作不会使Nginx停止服务。
# /usr/local/nginx/sbin/nginx -s reload
Step3 验证配置是否生效
(验证方式同step1.1)

4 header配置详解
此3个header配置可避免以下3种(低危)安全漏洞:
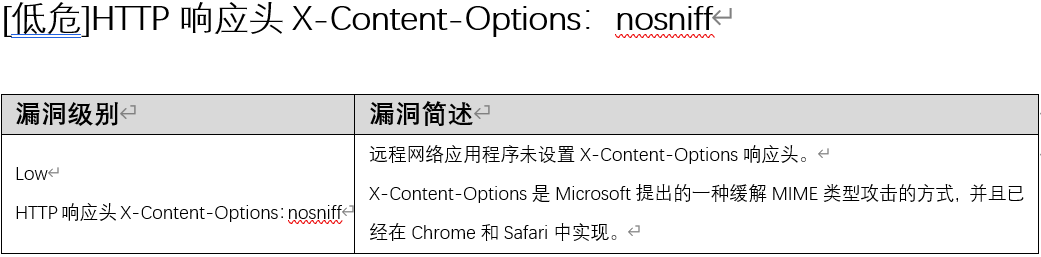
- [低危]HTTP响应头 X-Content-Options:nosniff
- [低危]HTTP响应头使用 X-XSS-Protection

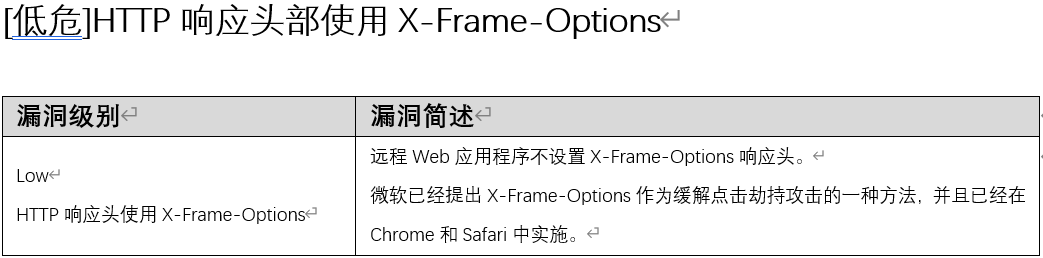
- [低危]HTTP响应头使用 X-Frame-Options
4-1 X-Content-Options
远程网络应用程序不设置X-Content-Options响应头。
X-Content-Options是Microsoft提出的一种缓解MIME类型攻击的方式,并且已经在Chrome和Safari中实现。
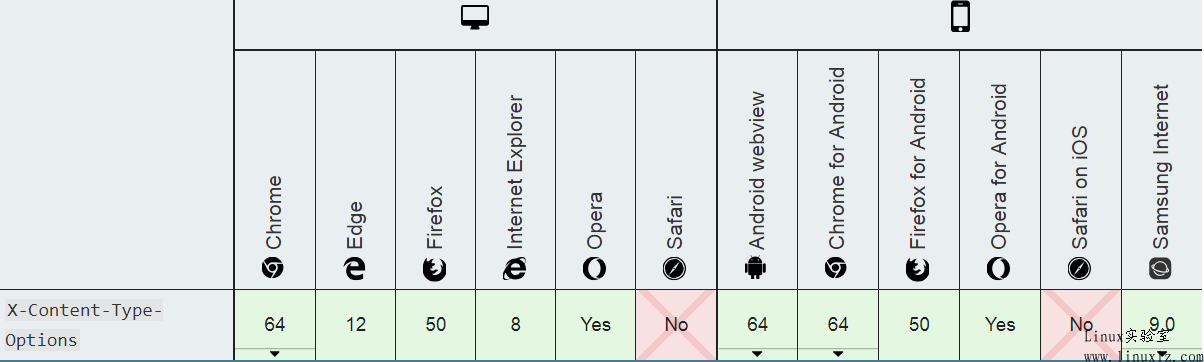
X-Content-Type-Options的浏览器兼容性
4-2 X-Frame-Options
可以配置的参数值有3个:
1.DENY:浏览器拒绝当前页面加载任何Frame页面。 [Tomcat中org.apache.catalina.filters.HttpHeaderSecurityFilter(catalina.jar)的默认值]
2.SAMEORIGIN:页面只能加载入同源域名下的页面。[一般配置此值即可]
3.ALLOW-FROM uri:只能被嵌入到指定域名的框架中。
5 补充问题
(现暂时没空)
- X-Frame-Options / X-XSS-Protection / X-Content-Options 三者的配置的值的意义
- 3个header涉及的安全漏洞
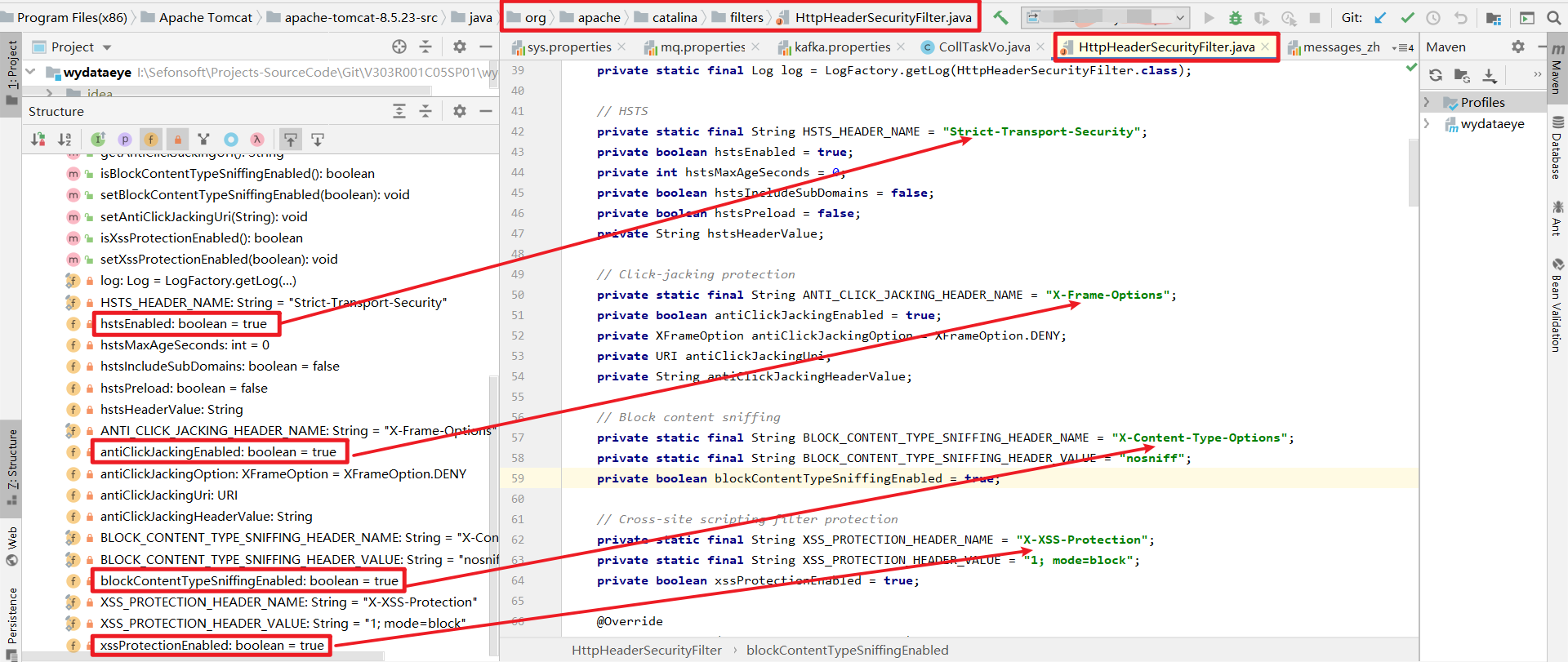
- 讲解 org.apache.catalina.filters.HttpHeaderSecurityFilter 源码
org.apache.catalina.filters.HttpHeaderSecurityFilter
[来源]
Tomcat(任何版本): /lib/catalina.jar:org.apache.catalina.filters.HttpHeaderSecurityFilter.class
Tomcat(source版): /java/org/apache/catalina/filters/HttpHeaderSecurityFilter.java
[重要的内置属性]
private static final String HSTS_HEADER_NAME = "Strict-Transport-Security"; //HSTS ,严格的传输安全
private static final String ANTI_CLICK_JACKING_HEADER_NAME = "X-Frame-Options"; //Click-jacking protection ,拒绝 frame
private static final String BLOCK_CONTENT_TYPE_SNIFFING_HEADER_NAME = "X-Content-Type-Options"; //Block content sniffing ,阻止内容嗅探
private static final String XSS_PROTECTION_HEADER_NAME = "X-XSS-Protection"; //Cross-site scripting filter protection , 跨站脚本过滤器保护
- 3个header的浏览器兼容性
- Java Web中 配置header的其它方法?
可参见该博文: Tomcat 配置“X-Frame-Options头” - CSDN
X 参考与推荐文献

本文作者:
千千寰宇
本文链接: https://www.cnblogs.com/johnnyzen
关于博文:评论和私信会在第一时间回复,或直接私信我。
版权声明:本博客所有文章除特别声明外,均采用 BY-NC-SA 许可协议。转载请注明出处!
日常交流:大数据与软件开发-QQ交流群: 774386015 【入群二维码】参见左下角。您的支持、鼓励是博主技术写作的重要动力!
本文链接: https://www.cnblogs.com/johnnyzen
关于博文:评论和私信会在第一时间回复,或直接私信我。
版权声明:本博客所有文章除特别声明外,均采用 BY-NC-SA 许可协议。转载请注明出处!
日常交流:大数据与软件开发-QQ交流群: 774386015 【入群二维码】参见左下角。您的支持、鼓励是博主技术写作的重要动力!


 浙公网安备 33010602011771号
浙公网安备 33010602011771号