AnolisOS7.9(CentOS7)部署K8s(1.28.2)集群
一. 安装K8s集群
1. 准备工作,2台服务器
① 192.168.5.140 - 做为master节点 # 在该节点运行命令设置主机名: hostnamectl set-hostname master ② 192.168.5.141 - 做为node1节点,在该节点运行命令设置主机名: # 在该节点运行命令设置主机名: hostnamectl set-hostname node1
# 所有节点配置hosts
cat >>/etc/hosts <<EOF 192.168.5.140 master
192.168.5.141 node1 EOF
# 所有节点关闭 SELinux
# 临时关闭 setenforce 0
# 永久关闭 sed -i --follow-symlinks 's/SELINUX=enforcing/SELINUX=disabled/g' /etc/sysconfig/selinux
# 所有节点关闭 swap分区
# 临时关闭
swapoff -a
# 永久关闭
sed -ri 's/.*swap.*/#&/' /etc/fstab
# 所有节点关闭防火墙
systemctl stop firewalld
systemctl disable firewalld
# 所有节点时间同步
# 安装 ntp
yum install -y ntp
# 同步时间
ntpdate ntp.aliyun.com
# 查看时间
date
# 设置每小时的第一分钟执行一次同步
vi /etc/crontab
# 新增
1 * * * * root /usr/sbin/ntpdate ntp1.aliyun.com && /sbin/hwclock -w
2. 所有节点配置内核参数
cat > /etc/sysctl.d/Kubernetes.conf <<EOF
net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1
net.ipv4.ip_forward = 1
vm.swappiness = 0 EOF # 使配置生效 sysctl --system
# 参数解释 # 通过桥接网络接收IPv6数据包时,调用ip6tables规则处理 net.bridge.bridge-nf-call-ip6tables = 1 # 通过桥接网络接收IPv4数据包时,调用iptables规则处理 net.bridge.bridge-nf-call-iptables = 1 # 允许IPv4数据包转发,即使数据包目标不是本机 net.ipv4.ip_forward = 1 # vm.swappiness是操作系统控制物理内存交换出去的策略。它允许的值是一个百分比的值,最小为0,最大运行100,该值默认为60。vm.swappiness设置为0表示尽量少swap,100表示尽量将inactive的内存页交换出去 vm.swappiness = 0 # Kubernetes通过iptables实现服务发现和网络流量路由,pod通信。这一步很重要。没有设置的话会导致集群网络通信故障,如pod无法通信。
3. 所有节点安装、设置、开机启动ipvs
# 安装 yum -y install conntrack ipvsadm ipset jq iptables curl sysstat libseccomp wget vim net-tools git # 设置 cat > /etc/modules-load.d/ipvs.conf <<EOF ip_vs ip_vs_rr ip_vs_wrr ip_vs_sh nf_conntrack EOF # 开机启动 systemctl enable --now systemd-modules-load
# ip_vs,ip_vs_rr,ip_vs_wrr,ip_vs_sh 是IPVS相关的内核模块。它们提供了不同的负载均衡算法(round-robin,加权轮询,最短任务优先)。 # nf_conntrack 和 nf_conntrack_ipv4 是用于网络连接跟踪的内核模块,这在防火墙和NAT中非常重要。 # linux kernel 4.19版本已经将nf_conntrack_ipv4 更新为 nf_conntrack
4. 所有节点重启
reboot
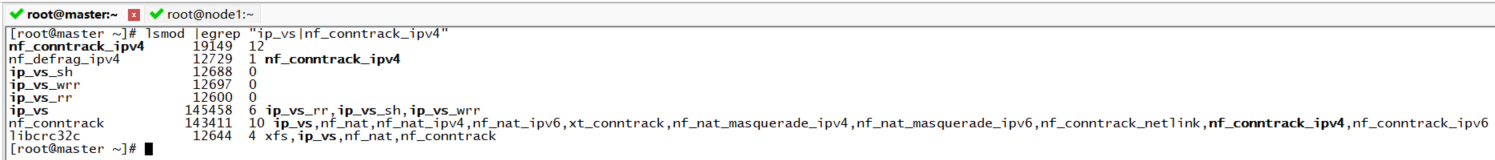
5. 所有节点检查ipvs是否加载
lsmod |egrep "ip_vs|nf_conntrack_ipv4"
6. 所有节点安装containerd
# k8s 1.24版本之后移除了dockershim组件,不再兼容docker # 安装依赖 yum -y install yum-utils device-mapper-persistent-data lvm2 # 添加docker的阿里源 yum-config-manager --add-repo http://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo
# 配置containerd cat >>/etc/modules-load.d/containerd.conf <<EOF overlay br_netfilter EOF
# 加载overlay
# Overlay 是一种联合文件系统,允许在不修改原始文件的情况下,将变更记录在一个独立的层中。这种写时复制(Copy-on-Write)技术被广泛用于 Docker 和其他容器运行时,以便创建高效的容器文件系统 modprobe overlay
# 加载br_netfilter
# br_netfilter 是一个内核模块,支持对网桥网络流量进行过滤,使用 iptables 和其他网络工具进行管理。这对于 Kubernetes 网络配置至关重要,特别是在使用 overlay 网络方案(如 flannel 和 Calico)时 modprobe br_netfilter # 安装 yum install -y containerd.io
# 配置containerd
mkdir -p /etc/containerd
containerd config default > /etc/containerd/config.toml
# 使用systemd管理cgroups
sed -i '/SystemdCgroup/s/false/true/g' /etc/containerd/config.toml
# 配置sadnbox从阿里云镜像拉取
sed -i '/sandbox_image/s/registry.k8s.io/registry.aliyuncs.com\/google_containers/g' /etc/containerd/config.toml
sed -i 's#sandbox_image = "registry.k8s.io/pause:3.6"#sandbox_image = "registry.aliyuncs.com/google_containers/pause:3.9"#' /etc/containerd/config.toml
# 设置开机启动、启动containerd
systemctl enable containerd
systemctl start containerd
7. 所有节点安装软件源
# 添加k8s安装源
cat >/etc/yum.repos.d/kubernetes.repo <<EOF
[kubernetes]
name=Kubernetes
baseurl=https://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64
enabled=1
gpgcheck=0
repo_gpgcheck=0
gpgkey=https://mirrors.aliyun.com/kubernetes/yum/doc/yum-key.gpg https://mirrors.aliyun.com/kubernetes/yum/doc/rpm-package-key.gpg
EOF
# 查看k8s可用版本
yum list kubelet --showduplicates | sort -r
8. 所有节点安装k8s
# 这里指定k8s版本为1.28.2
yum install -y kubelet-1.28.2 kubectl-1.28.2 kubeadm-1.28.2
9. 所有节点启动 kubelet、docker,并设置开机启动
systemctl enable kubelet
systemctl start kubelet
10. master节点kubeadm初始化
kubeadm init \ --kubernetes-version=1.28.2 \ --apiserver-advertise-address=192.168.5.140 \ --image-repository=registry.aliyuncs.com/google_containers \ --pod-network-cidr=10.244.0.0/16
# 如果init失败,使用下面命令重置后再init
kubeadm reset
# 解释 # 指定K8s的版本,刚才安装的 --kubernetes-version=1.28.2 \ # 指定API Server组件的地址 --apiserver-advertise-address=192.168.5.140 \ # 指定阿里的镜像仓库地址,因为管理节点和工作节点的部分组件是封装到kubeadm工具中的,等会启动的时候,它默认会从国外的源下载镜像,所以这里为了加快速度指定为国内源 --image-repository registry.aliyuncs.com/google_containers \ # pod网段,可以选择一个本机网络和service-cidr都没有用到的私网地址段 --pod-network-cidr=10.244.0.0/16
11. 看到下面的内容说明master节点初始化完成

如果关闭了窗口,可以通过下面的命令查看
kubeadm token create --print-join-command
12. 复制授权文件,以便 kubectl 可以有权限访问集群
# 如果其他节点或本地需要访问集群,需要从主节点复制这个文件过去其他节点或本地,这样其他节点或本地执行kubectl命令了 mkdir -p $HOME/.kube sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config sudo chown $(id -u):$(id -g) $HOME/.kube/config export KUBECONFIG=/etc/kubernetes/admin.conf
13. 将子节点加入集群
# 将上面的内容在所有子节点运行 kubeadm join 192.168.5.140:6443 --token 65tl4q.mbzgy903o25b75g1 --discovery-token-ca-cert-hash sha256:fa7875e9420e44f87cbf702c91f54e6fb85bd01fa77288a32fb64f28ac10978f
14. 安装flannel网络插件,使用提供的 kube-flannel.yml文件,在master节点上执行命令
kubectl apply -f kube-flannel.yml
kube-flannel.yml内容如下
---
kind: Namespace
apiVersion: v1
metadata:
name: kube-flannel
labels:
pod-security.kubernetes.io/enforce: privileged
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: flannel
rules:
- apiGroups:
- ""
resources:
- pods
verbs:
- get
- apiGroups:
- ""
resources:
- nodes
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes/status
verbs:
- patch
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: flannel
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: flannel
subjects:
- kind: ServiceAccount
name: flannel
namespace: kube-flannel
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: flannel
namespace: kube-flannel
---
kind: ConfigMap
apiVersion: v1
metadata:
name: kube-flannel-cfg
namespace: kube-flannel
labels:
tier: node
app: flannel
data:
cni-conf.json: |
{
"name": "cbr0",
"cniVersion": "0.3.1",
"plugins": [
{
"type": "flannel",
"delegate": {
"hairpinMode": true,
"isDefaultGateway": true
}
},
{
"type": "portmap",
"capabilities": {
"portMappings": true
}
}
]
}
net-conf.json: |
{
"Network": "10.244.0.0/16",
"Backend": {
"Type": "vxlan"
}
}
---
apiVersion: apps/v1
kind: DaemonSet
metadata:
name: kube-flannel-ds
namespace: kube-flannel
labels:
tier: node
app: flannel
spec:
selector:
matchLabels:
app: flannel
template:
metadata:
labels:
tier: node
app: flannel
spec:
affinity:
nodeAffinity:
requiredDuringSchedulingIgnoredDuringExecution:
nodeSelectorTerms:
- matchExpressions:
- key: kubernetes.io/os
operator: In
values:
- linux
hostNetwork: true
priorityClassName: system-node-critical
tolerations:
- operator: Exists
effect: NoSchedule
serviceAccountName: flannel
initContainers:
- name: install-cni-plugin
#image: flannelcni/flannel-cni-plugin:v1.1.0 for ppc64le and mips64le (dockerhub limitations may apply)
image: docker.io/rancher/mirrored-flannelcni-flannel-cni-plugin:v1.1.0
command:
- cp
args:
- -f
- /flannel
- /opt/cni/bin/flannel
volumeMounts:
- name: cni-plugin
mountPath: /opt/cni/bin
- name: install-cni
#image: flannelcni/flannel:v0.20.1 for ppc64le and mips64le (dockerhub limitations may apply)
image: docker.io/rancher/mirrored-flannelcni-flannel:v0.20.1
command:
- cp
args:
- -f
- /etc/kube-flannel/cni-conf.json
- /etc/cni/net.d/10-flannel.conflist
volumeMounts:
- name: cni
mountPath: /etc/cni/net.d
- name: flannel-cfg
mountPath: /etc/kube-flannel/
containers:
- name: kube-flannel
#image: flannelcni/flannel:v0.20.1 for ppc64le and mips64le (dockerhub limitations may apply)
image: docker.io/rancher/mirrored-flannelcni-flannel:v0.20.1
command:
- /opt/bin/flanneld
args:
- --ip-masq
- --kube-subnet-mgr
resources:
requests:
cpu: "100m"
memory: "50Mi"
limits:
cpu: "100m"
memory: "50Mi"
securityContext:
privileged: false
capabilities:
add: ["NET_ADMIN", "NET_RAW"]
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: EVENT_QUEUE_DEPTH
value: "5000"
volumeMounts:
- name: run
mountPath: /run/flannel
- name: flannel-cfg
mountPath: /etc/kube-flannel/
- name: xtables-lock
mountPath: /run/xtables.lock
volumes:
- name: run
hostPath:
path: /run/flannel
- name: cni-plugin
hostPath:
path: /opt/cni/bin
- name: cni
hostPath:
path: /etc/cni/net.d
- name: flannel-cfg
configMap:
name: kube-flannel-cfg
- name: xtables-lock
hostPath:
path: /run/xtables.lock
type: FileOrCreate
15. 查看节点状态和pod就绪状态
kubectl get node kubectl get pods -A kubectl get pods -n kube-system



 浙公网安备 33010602011771号
浙公网安备 33010602011771号