逆向挑战赛Bob Doge 和 who is he
(拿来对比一下)
1. 这题是net程序,下载是一个安装程序,我以为会是个猛题,奈何关键函数暴露了,有点浪费。
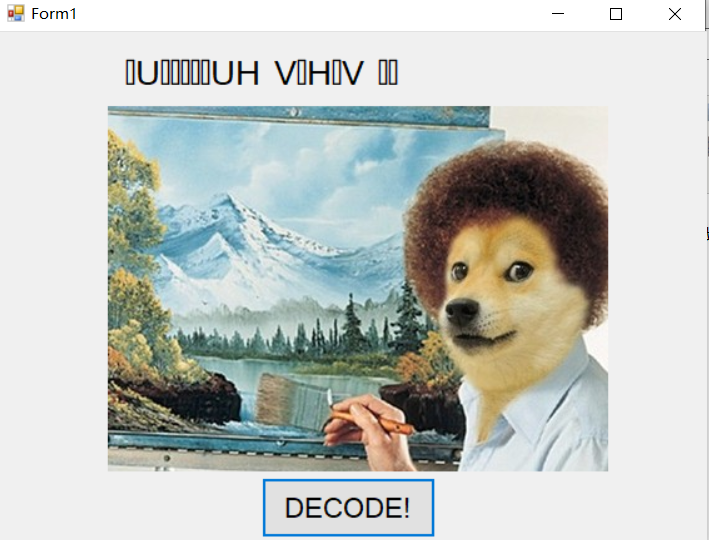
点击解密,图片不仅更换了还出现一串乱码,光看这界面真的很容易想到是什么MFC(我还想着去控件找button按钮):
dnspy挂载程序,找到关键的控件函数:
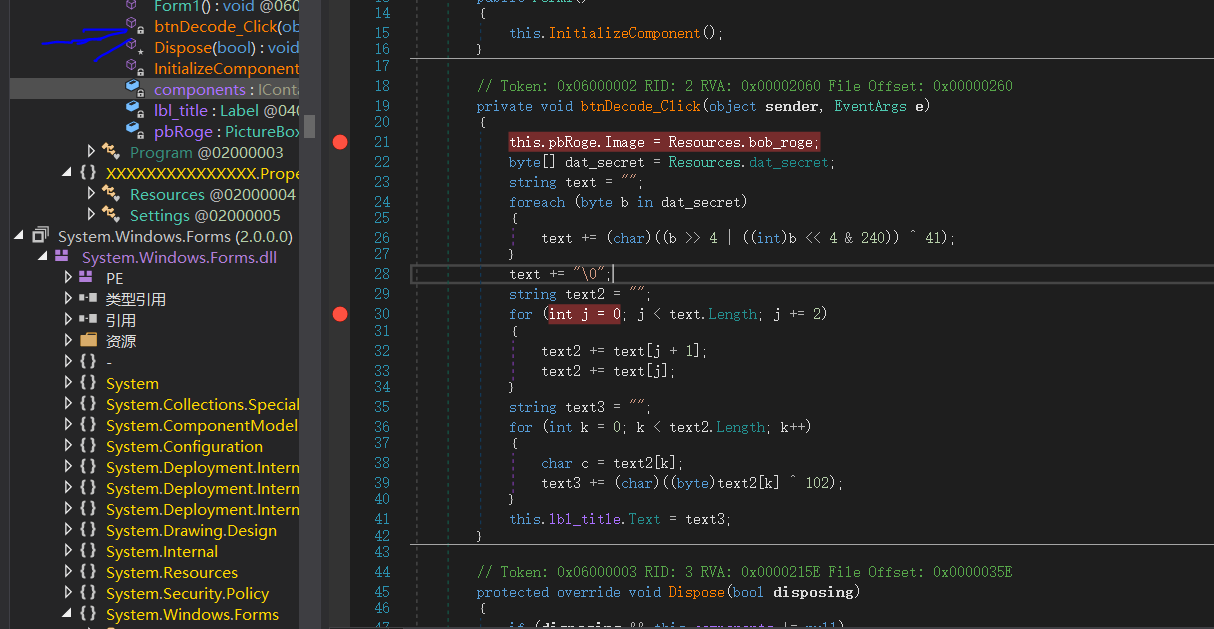
动态调试就能拿到flag:
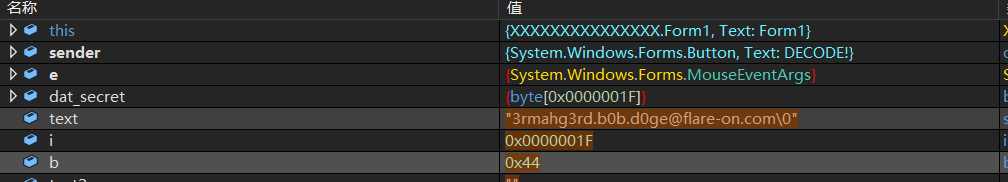
有两处text的处理,一开始我直接下断到后面的判断,得到的不对,不对,正确的是第一个循环处理,flag{3rmahg3rd.b0b.d0ge@flare-on.com}.
也可以直接按照它的思路写keygen,就是找硬编码的字符串有点麻烦,附上前辈的脚本:http://www.mottoin.com/getUserView/6218.html
using System; using System.Collections.Generic; using System.Linq; using System.Text; namespace flare_on_1 { class Program { //private void btnDecode_Click(object sender, EventArgs e) static void btnDecode_Click() { //this.pbRoge.Image = Resources.bob_roge; //byte[] buffer = Resources.dat_secret; byte[] buffer = { 0xA1, 0xB5, 0x44, 0x84, 0x14, 0xE4, 0xA1, 0xB5, 0xD4, 0x70, 0xB4, 0x91, 0xB4, 0x70, 0xD4, 0x91, 0xE4, 0xC4, 0x96, 0xF4, 0x54, 0x84, 0xB5, 0xC4, 0x40, 0x64, 0x74, 0x70, 0xA4, 0x64, 0x44 }; string str = ""; for (int i = 0; i < buffer.Length; i++) { byte num2 = buffer[i]; str = str + ((char)(((num2 >> 4) | ((num2 << 4) & 240)) ^ 0x29)); } str = str + ""; } static void Main(string[] args) { btnDecode_Click(); } } }
2. who is he 就有点头大, 拿到题目打开就是NBA大使的恶搞视频:
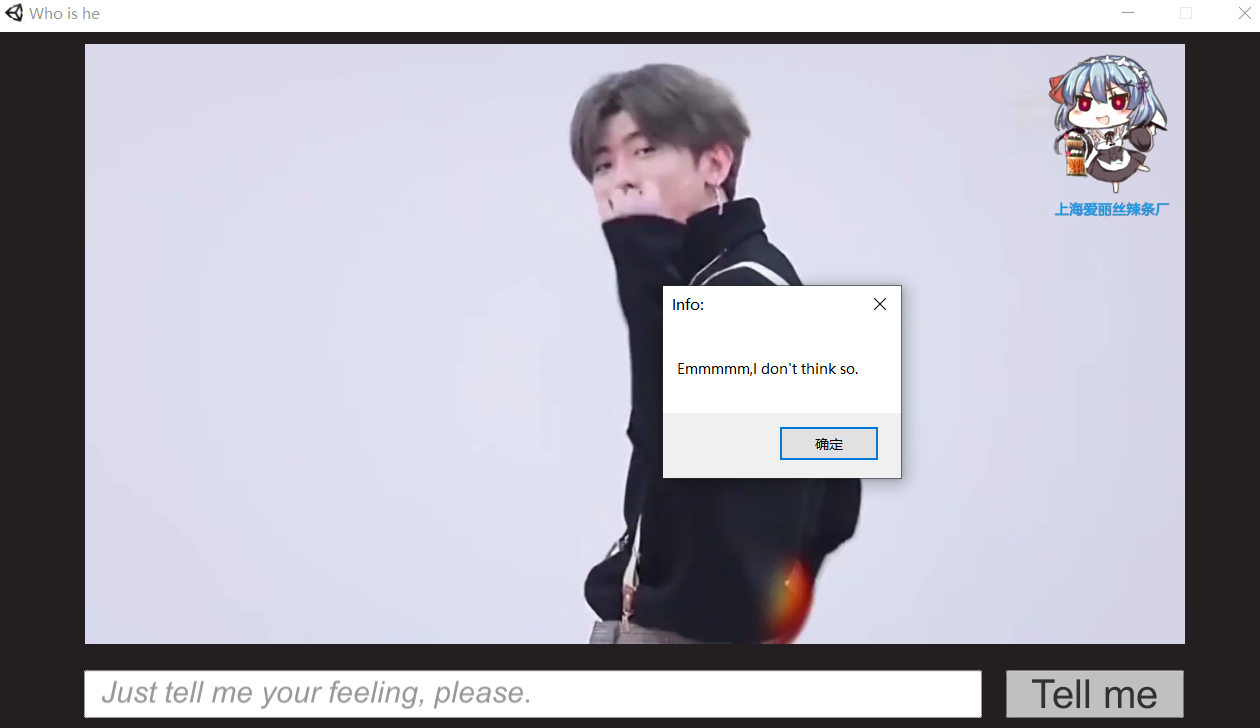
点击弹出提示错误对话框。
然后查壳也没发现有什么net混淆之类的,就是正常的程序,找到资源下反汇编dll,打开也有很明显的加密方式:
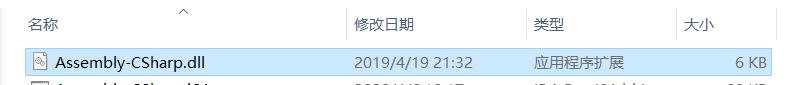
加密算法:
private string Decrypt(string str) { string result; try { byte[] bytes = Encoding.Unicode.GetBytes(TestClick.encryptKey); byte[] array = Convert.FromBase64String(str); DESCryptoServiceProvider descryptoServiceProvider = new DESCryptoServiceProvider(); MemoryStream memoryStream = new MemoryStream(); CryptoStream cryptoStream = new CryptoStream(memoryStream, descryptoServiceProvider.CreateDecryptor(bytes, bytes), CryptoStreamMode.Write); cryptoStream.Write(array, 0, array.Length); cryptoStream.FlushFinalBlock(); byte[] bytes2 = memoryStream.ToArray(); cryptoStream.Close(); memoryStream.Close(); result = Encoding.Unicode.GetString(bytes2); } catch { result = str; } return result; }
DES的加解密,输入是base64编码,key和iv相同。
照着写脚本解密:(注意Convert.FromBase64String函数是base64编码转换为8位无符号数组):参考 https://xz.aliyun.com/u/12624
import base64 from Crypto.Cipher import DES key = b"1x002x003x004x00"#高高低低 des_new = DES.new(key, mode = DES.MODE_CBC, iv = key) cipher = b"1Tsy0ZGotyMinSpxqYzVBWnfMdUcqCMLu0MA+22Jnp+MNwLHvYuFToxRQr0c+ONZc6Q7L0EAmzbycqobZHh4H23U4WDTNmmXwusW4E+SZjygsntGkO2sGA==" cipher = base64.b64decode(cipher) plain = des_new.decrypt(cipher)[0:-8].decode("utf-16")## print(plain)
解出flag : He_P1ay_Basketball_Very_We11!Hahahahaha! 不对
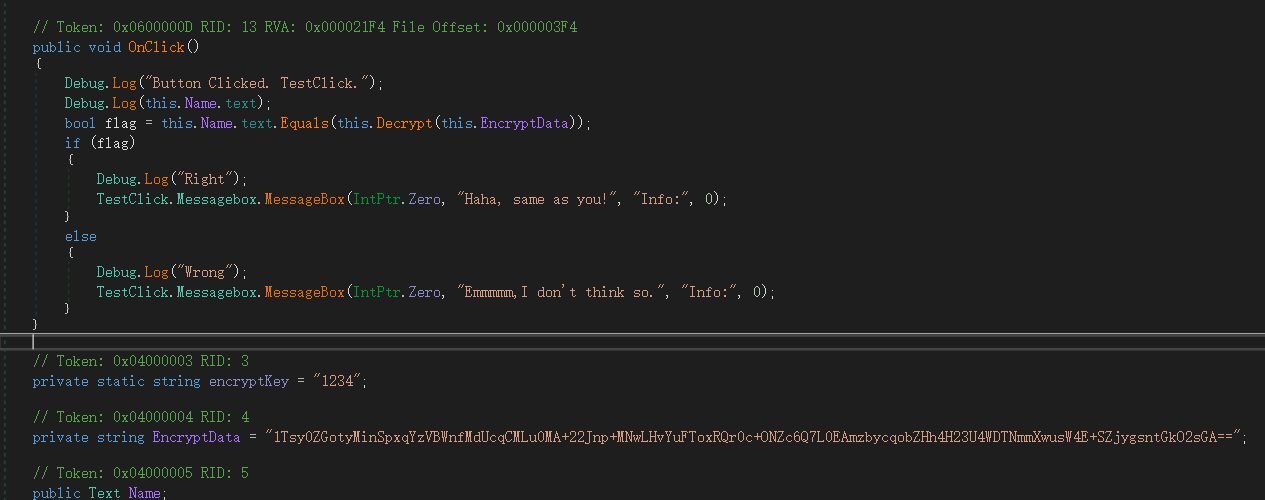
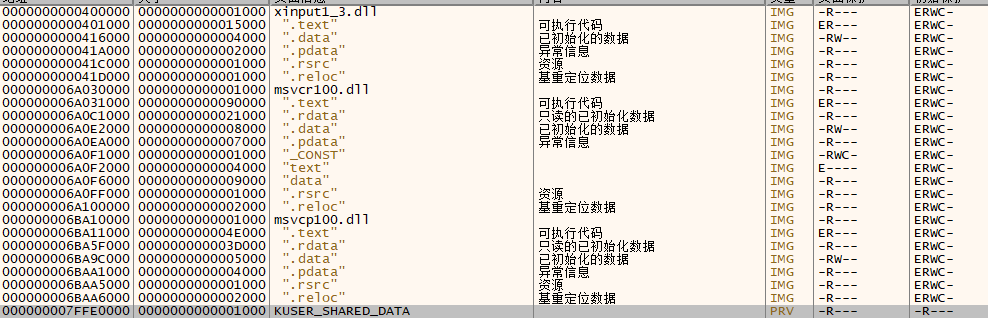
然后动态调试全部F9发现并没有调用这个dll:
同时挂载程序之后,内存字符串有多个Emmmmm, I dont think so.(winhex查找内存)
在程序运行起来之后可以找到另一个base64字符串:xZWDZaKEhWNMCbiGYPBIlY3+arozO9zonwrYLiVL4njSez2RYM2WwsGnsnjCDnHs7N43aFvNE54noSadP9F8eEpvTs5QPG+KL0TDE/40nbU= key: test
解密之后得到:
She_P1ay_Black_Hole_Very_Wel1!LOL!XD!
题目链接:https://buuoj.cn/files/7d2ae493291c929abd049c3c3ece3170/attachment.zip?token=eyJ1c2VyX2lkIjo1NTY4LCJ0ZWFtX2lkIjpudWxsLCJmaWxlX2lkIjoxMTU2fQ.XowQxg.hkyZVR_3HIFLcf-BRG3pkyUDHuw
https://buuoj.cn/files/7414474a334c9d80bb9ffb24b3a453bc/attachment.7z?token=eyJ1c2VyX2lkIjo1NTY4LCJ0ZWFtX2lkIjpudWxsLCJmaWxlX2lkIjo2MjR9.XowZ9w.x1XB5lMiEULlgT150woQOkZY_9o


 浙公网安备 33010602011771号
浙公网安备 33010602011771号