#下载签名密钥
wget https://lancelot.netknights.it/NetKnights-Release.asc
#确认指纹
gpg --import --import-options show-only --with-fingerprint NetKnights-Release.asc
#添加签名密钥
mv NetKnights-Release.asc /etc/apt/trusted.gpg.d/
#添加仓库
apt install software-properties-common -y
add-apt-repository http://lancelot.netknights.it/community/jammy/stable
#privacyIDEA安装
privacyIDEA Installation: apt update && apt install privacyidea-apache2 privacyidea-radius -y
#添加privacyIDEA web管理员
pi-manage admin add admin -e admin@localhost
#添加 privacyIDEA 本地认证用户:
/opt/privacyidea/bin/privacyidea-create-pwidresolver-user -u ljc -i 10 -p 123456.com -d 'User LJC' >> /etc/privacyidea/privacyidea_user
#其中ljc为用户名 123456.com为密码
1.2 配置radius客户端
vi /etc/freeradius/3.0/clients.conf
在# IPv6 Client前面增加
client palo_alto {
ipaddr = 192.168.0.24
secret = pasecret123
}
保存退出后重启freeradius
systemctl restart freeradius
二、privacyIDEA 配置
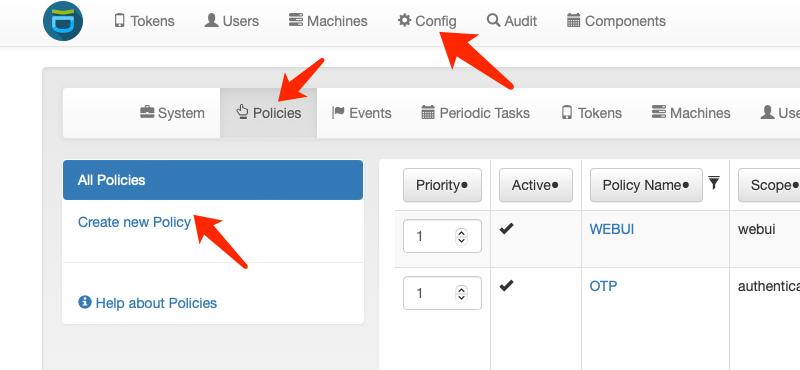
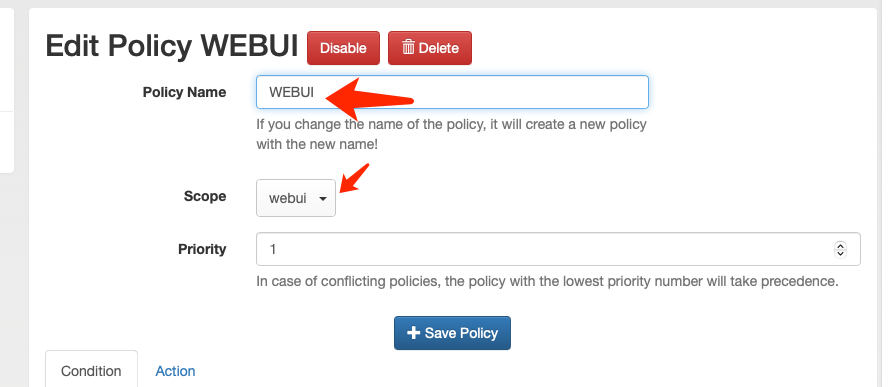
2.1隐藏web欢迎信息
![]()
![]()
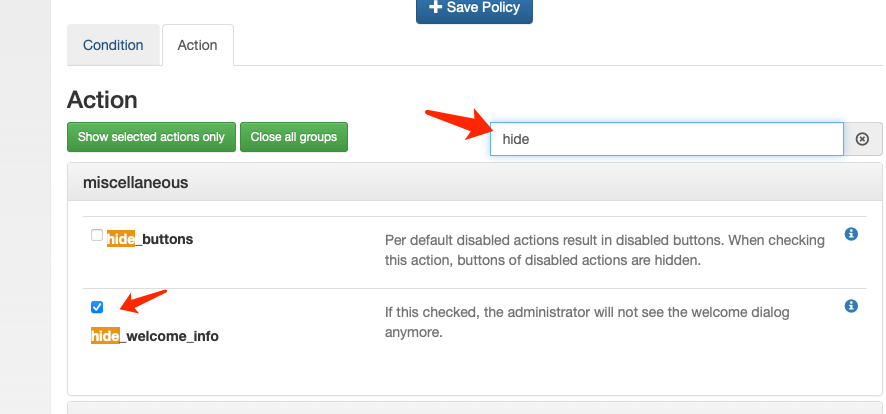
搜索hide,勾选hide_welcome_info隐藏web界面欢迎信息
![]()
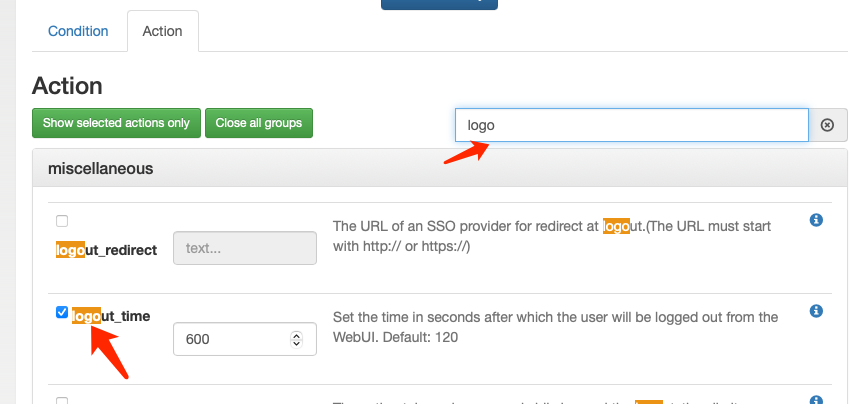
修改web超时时间
![]()
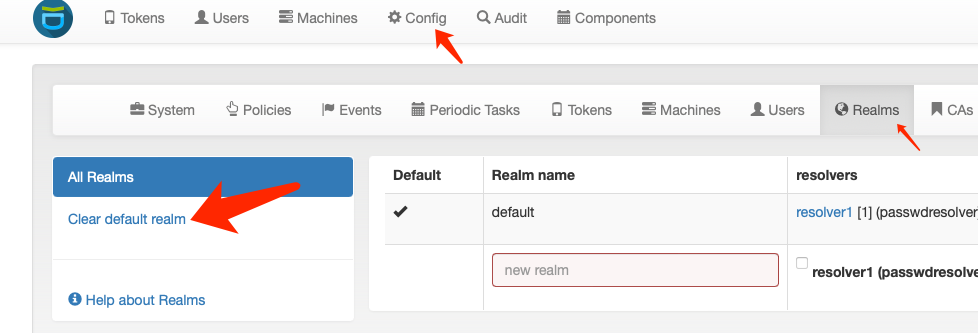
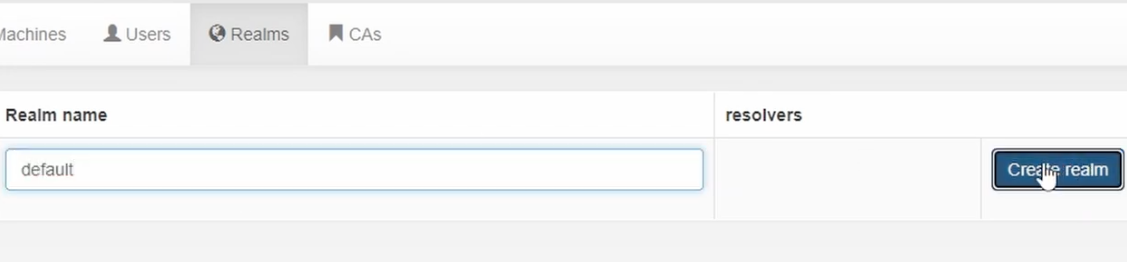
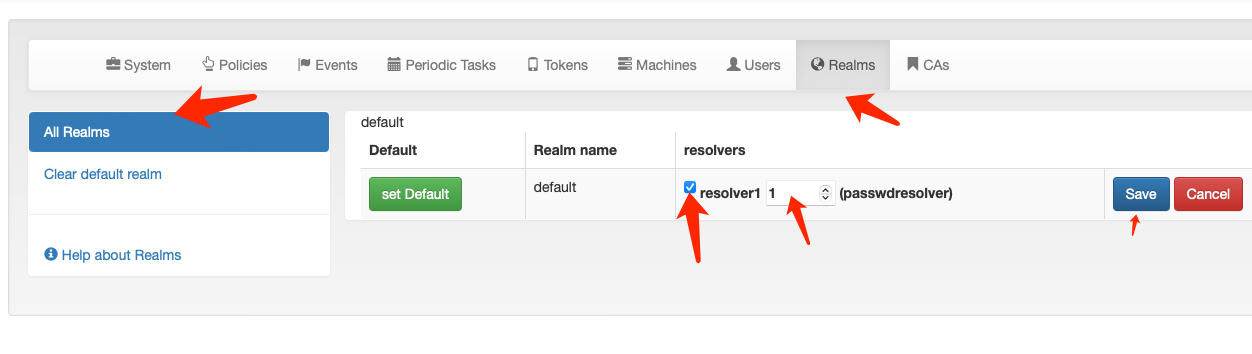
2.2创建认证域
![]()
![]()
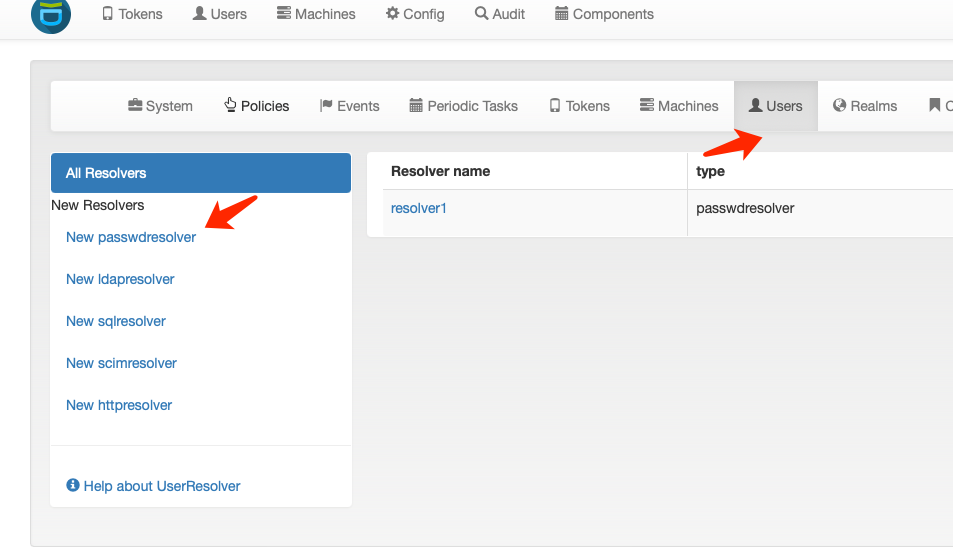
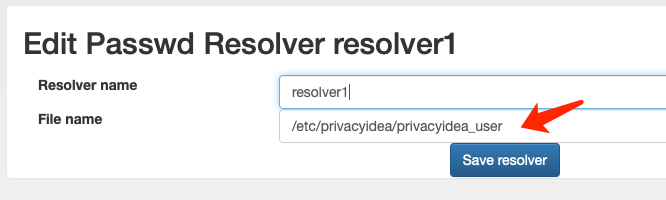
2.3创建认证数据库
![]()
File name 选择第一步安装privacyIDEA时创建的本地密码数据库文件 /etc/privacyidea/privacyidea_user
![]()
返回认证域选择刚刚创建的本地密码数据库并设置优先级
![]()
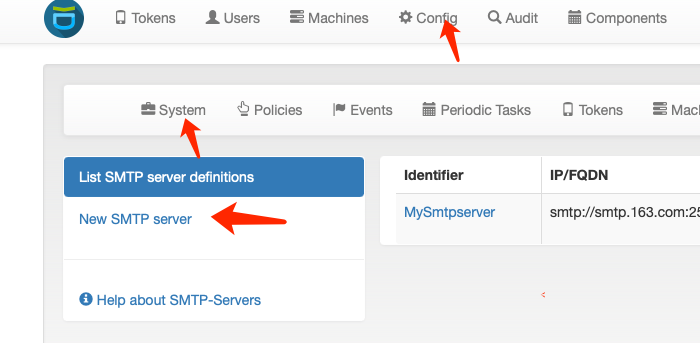
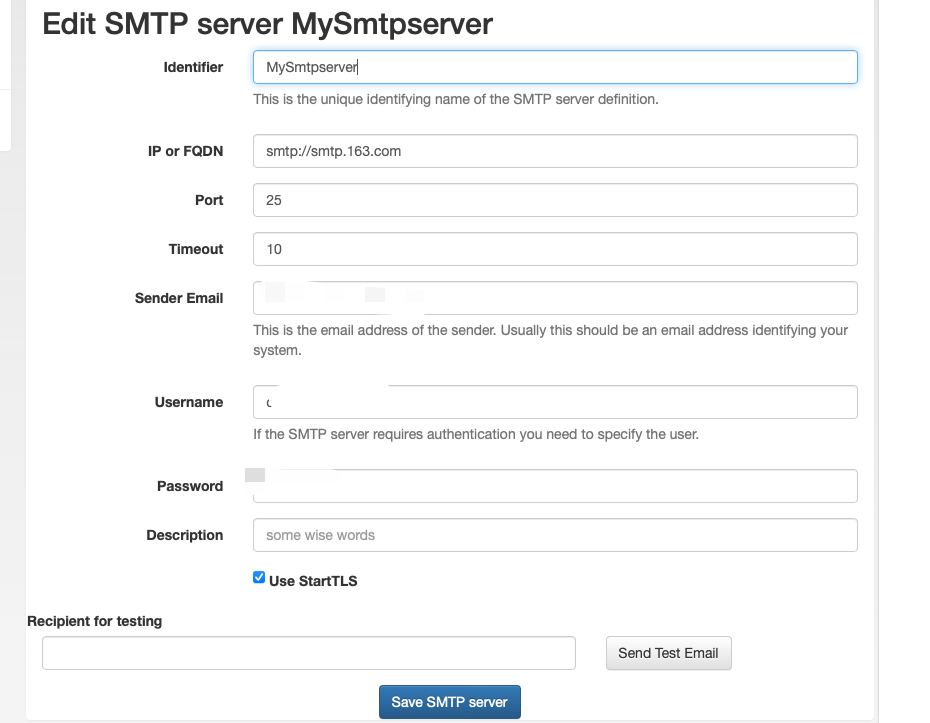
2.4 设置邮件发送服务器
![]()
填写邮件服务器的相关信息,并保存。填写完毕可点击Send Test Email测试配置是否正确
![]()
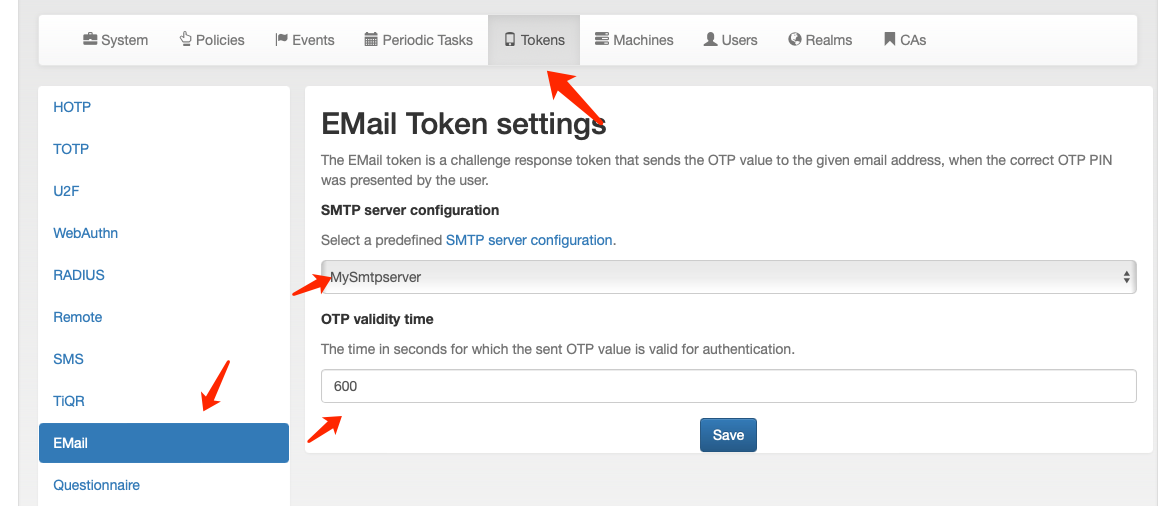
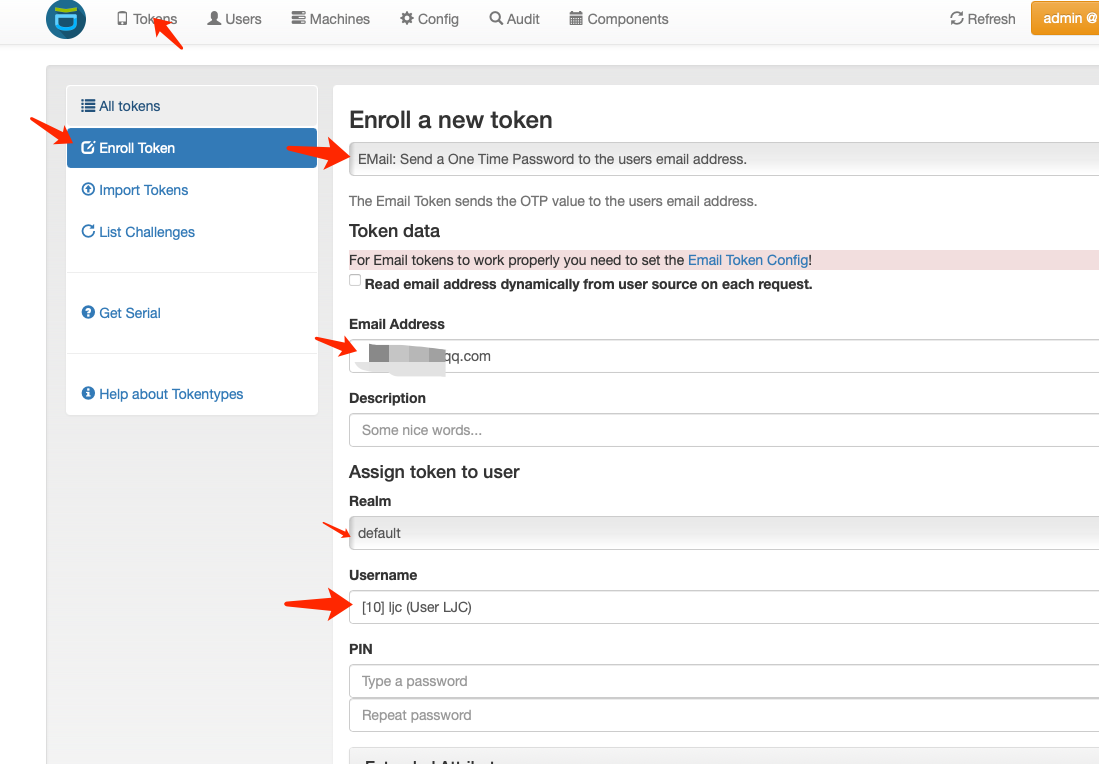
2.5 设置用户邮件Email Token及超时时间
设置全局超时时间设备为10分钟
![]()
设置单个用户的邮箱
![]()
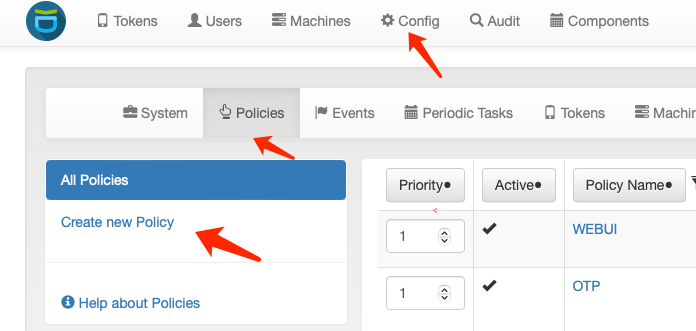
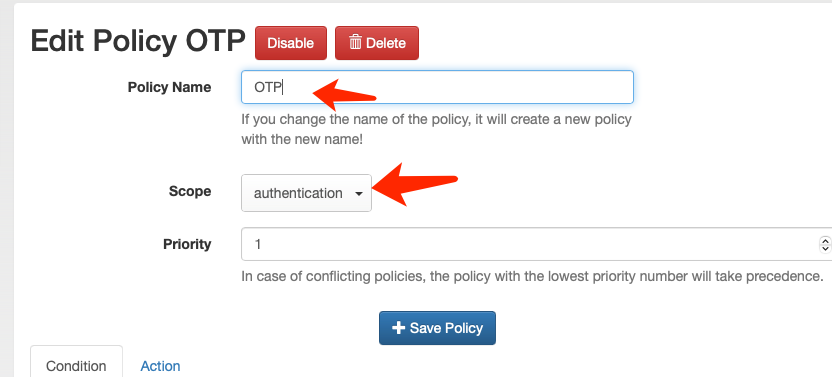
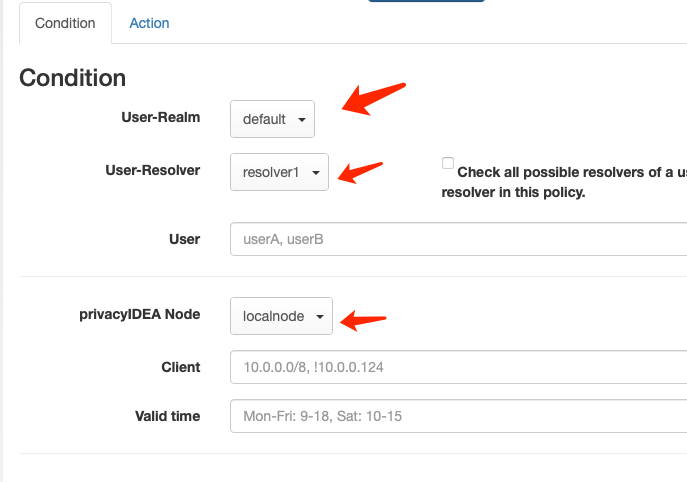
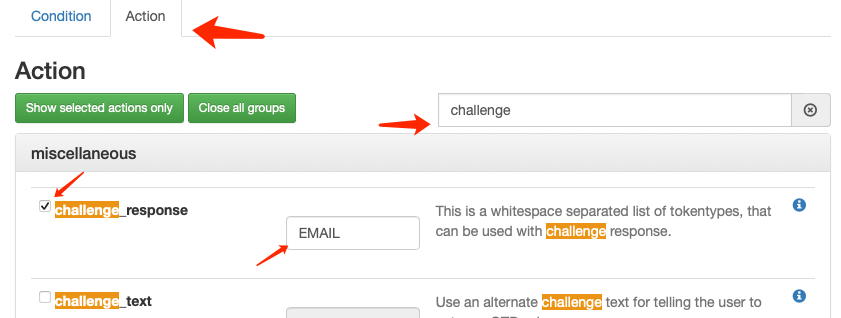
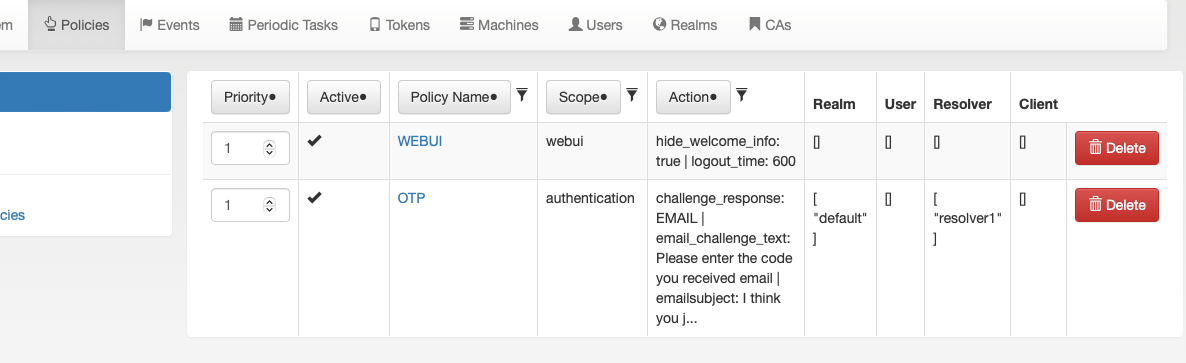
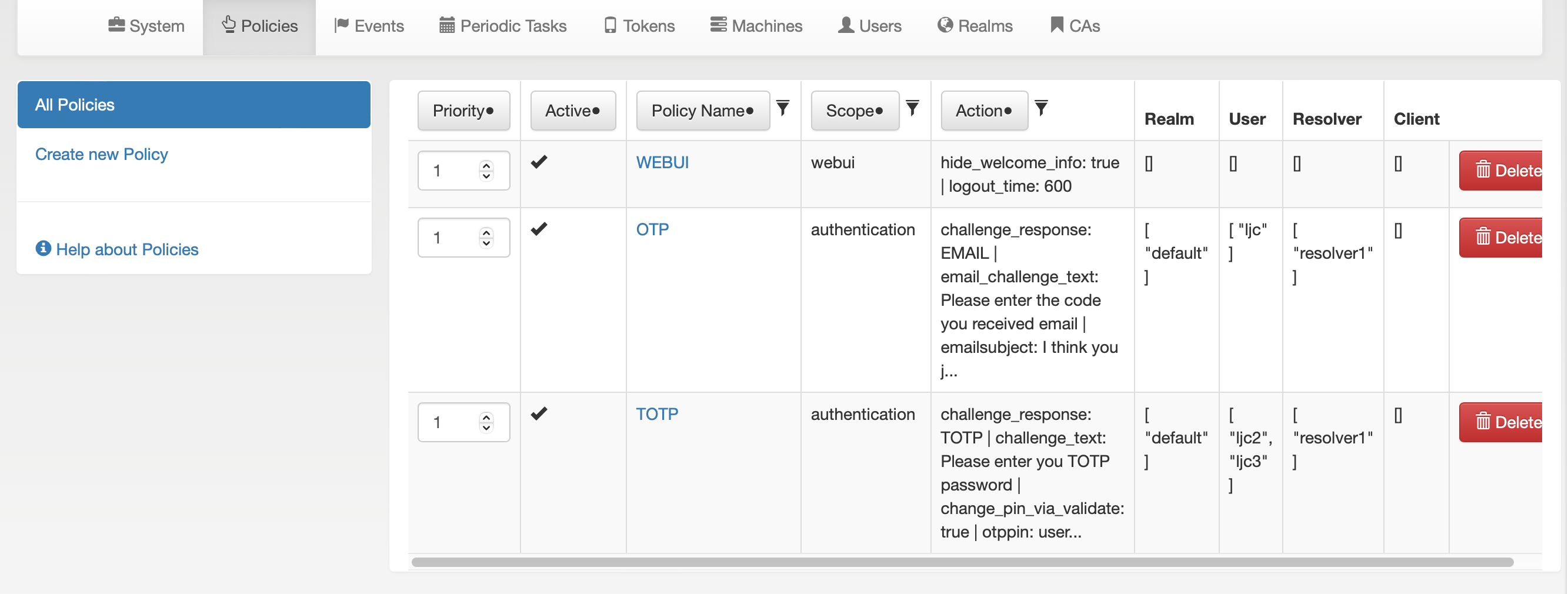
2.6 设置认证策略
![]()
![]()
![]()
![]()
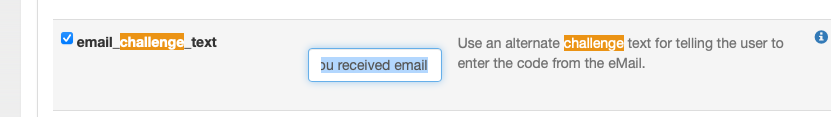
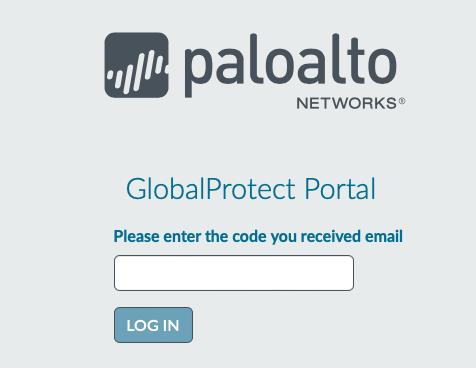
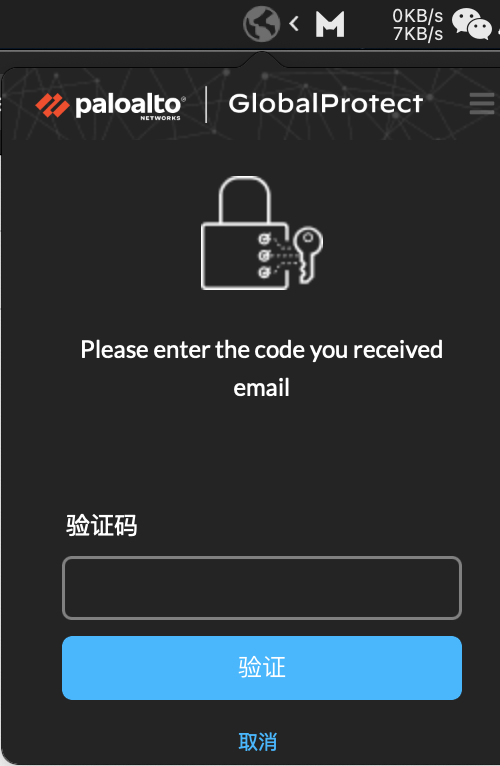
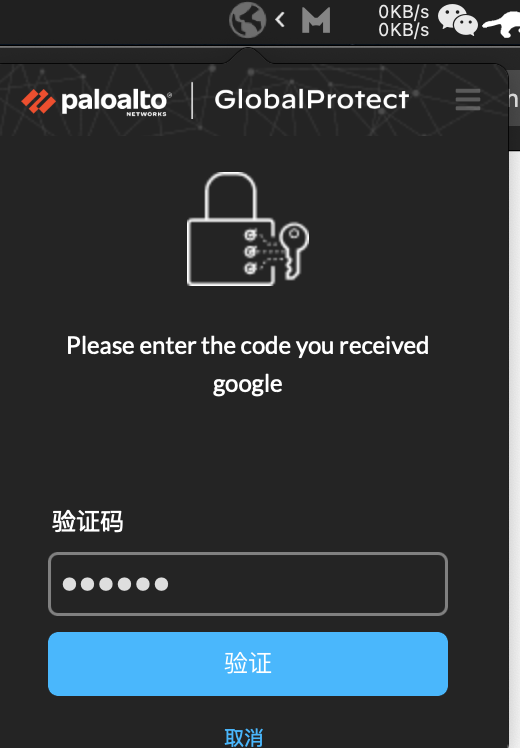
输入:Please enter the code you received email
这段文字会出现输入验证码的界面
![]()
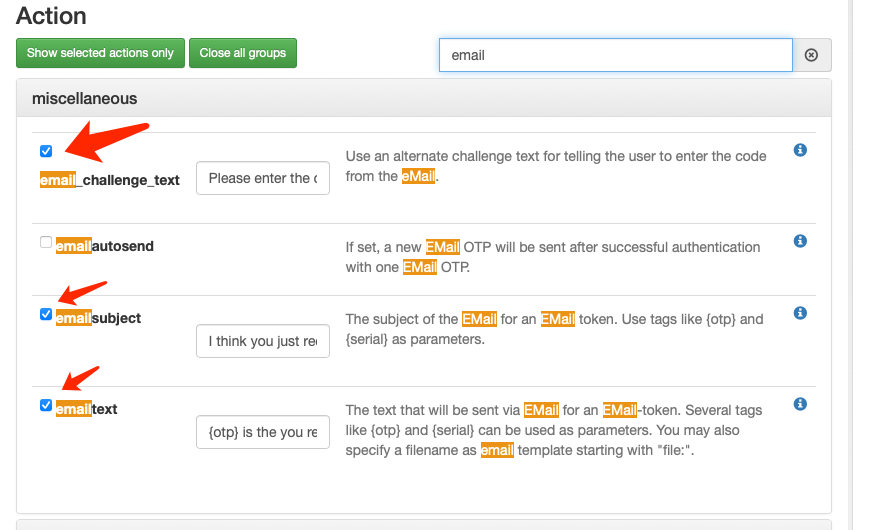
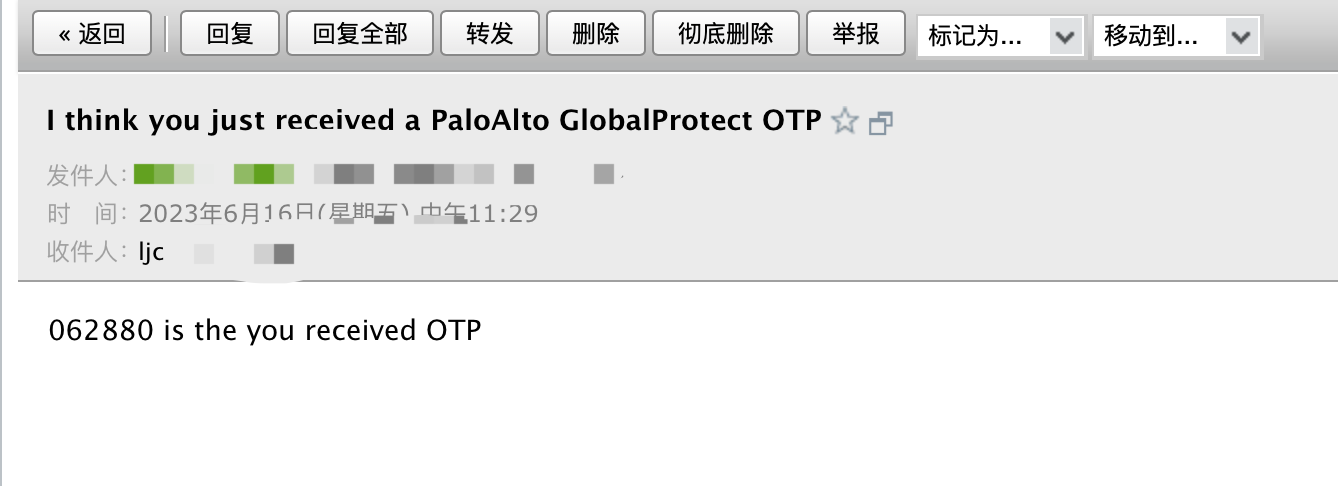
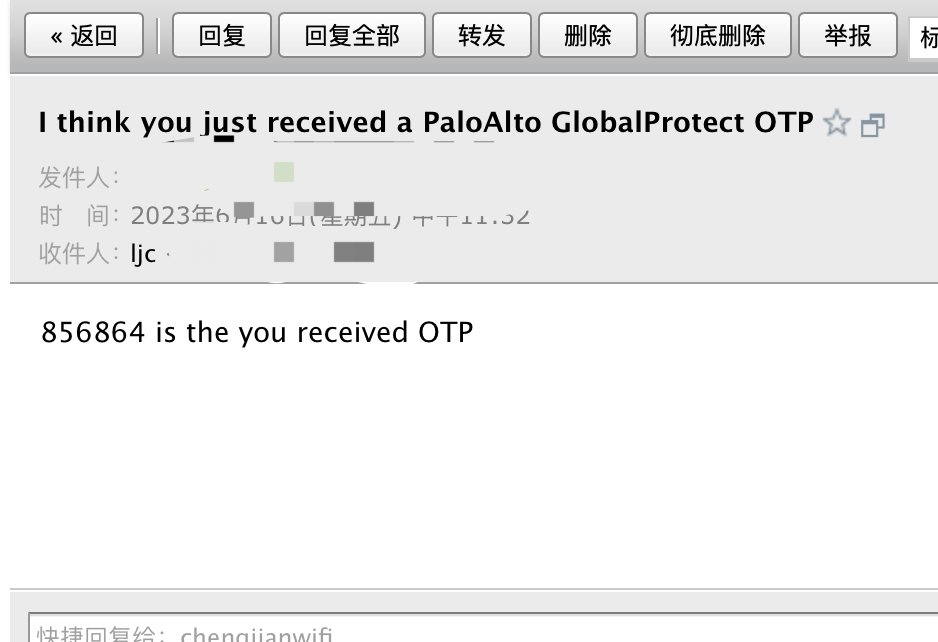
email_challenge_text: Please enter the code you received email
emailsubject(邮件标题): I think you just received a PaloAlto GlobalProtect OTP
emailtext(邮件内容): {otp} is the you received OTP
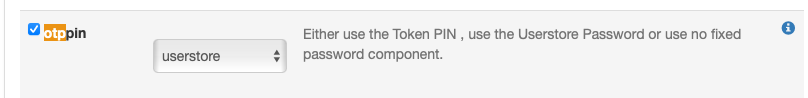
![]()
![]()
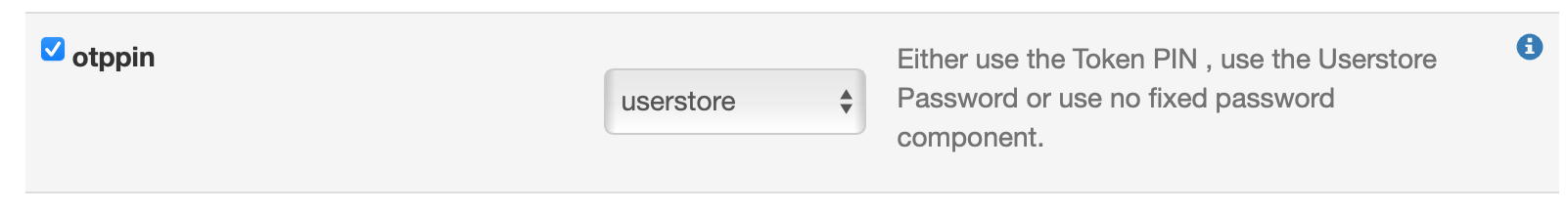
!!!若不选otppin则默认只输入otp作为密码,不需要输入用户密码
保存后的策略
![]()
三、Palo Alto 配置
具体GlobalProtect的配置可参考另一篇博文,这里不再叙述 https://www.cnblogs.com/id404/p/17465413.html
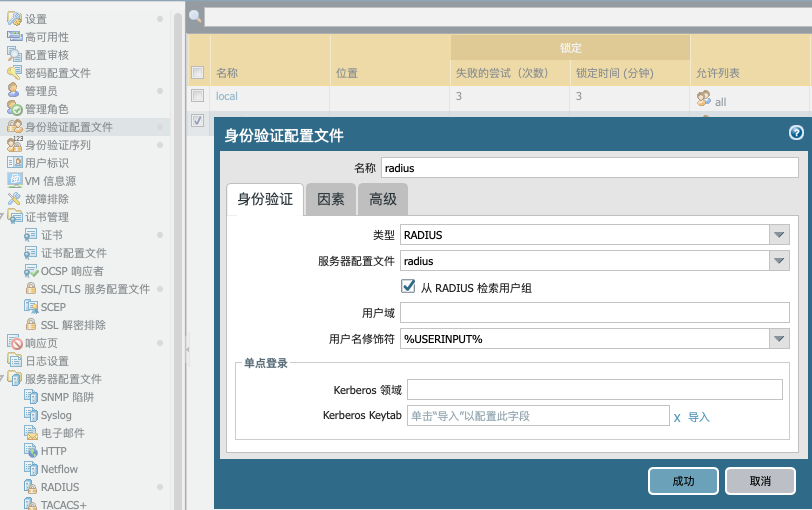
3.1 radius配置
确认radius的服务路由,设备默认从管理口发送radius请求,若需要从其它接口发送radius请求
![]()
![]()
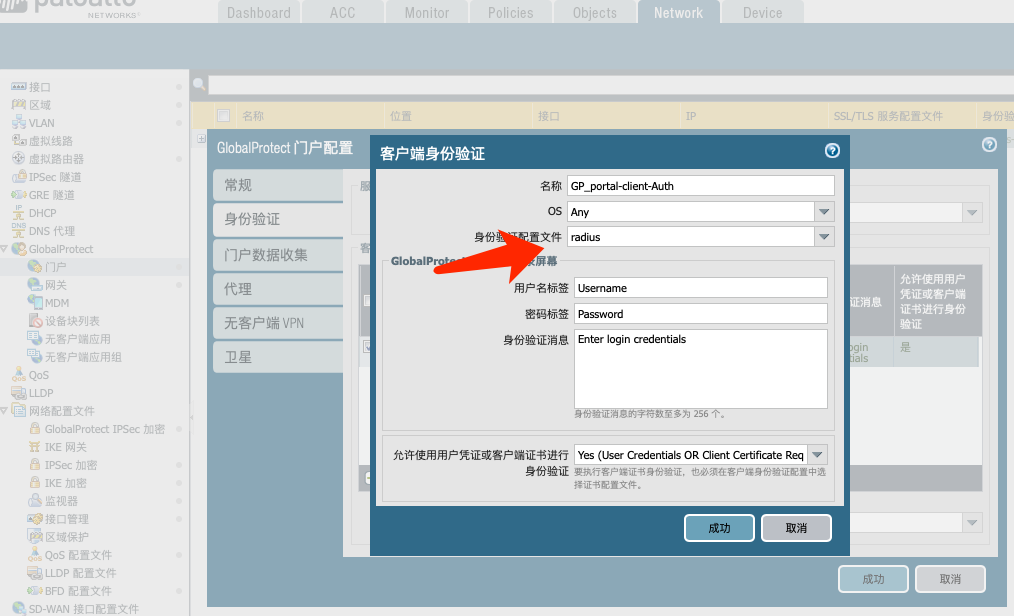
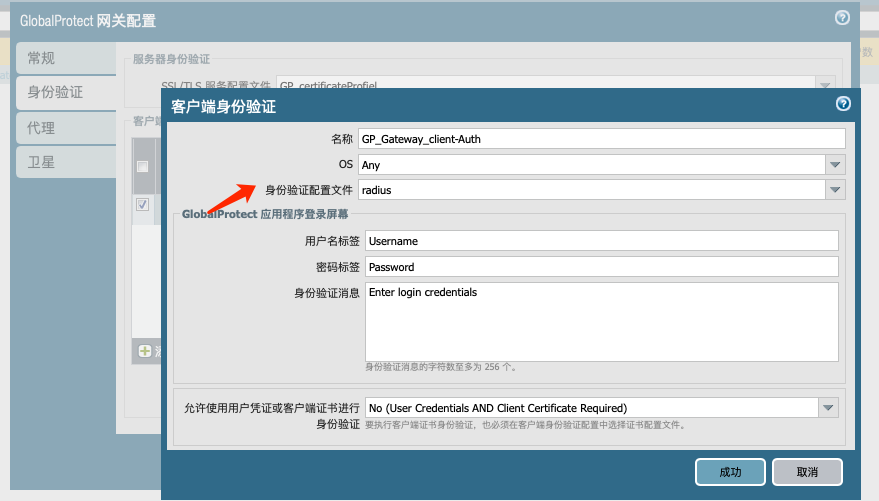
门户将身份验证配置文件改为 radius
![]()
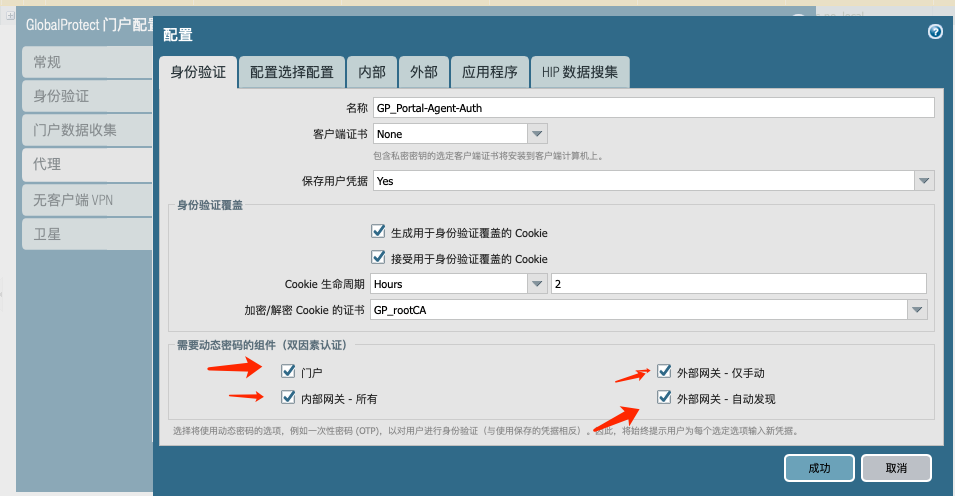
代理将双因素认证选上
![]()
网关将身份验证配置文件改为 radius
![]()
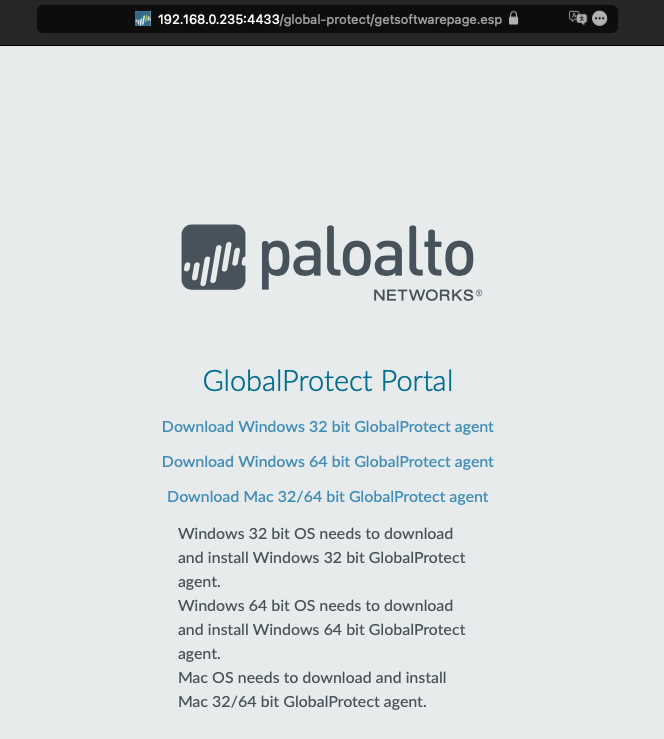
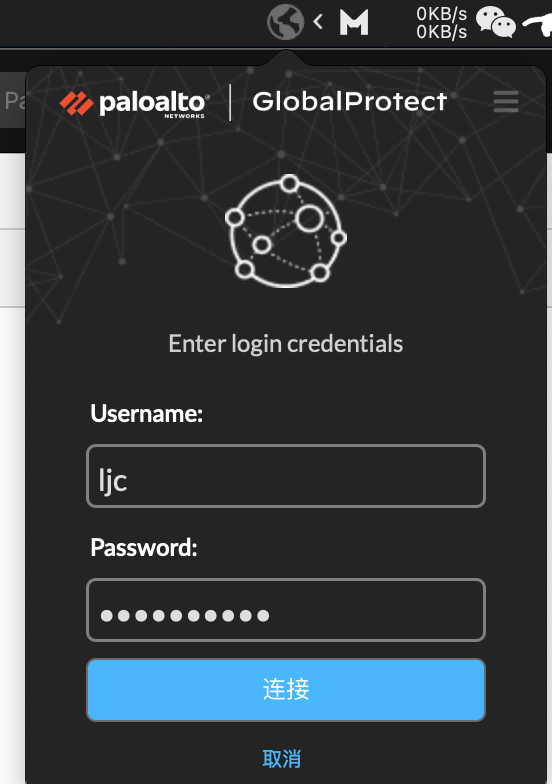
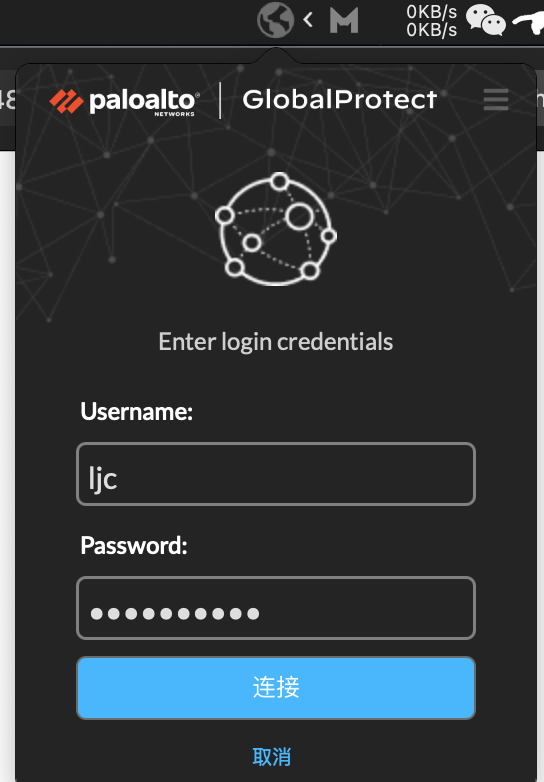
三、客户端登陆
3.1 门户登陆
![]()
![]()
![]()
登陆成功
![]()
客户端登陆
![]()
![]()
![]()
![]()
PA上可以看到用户成功连接
![]()
四、TOTP二步验证
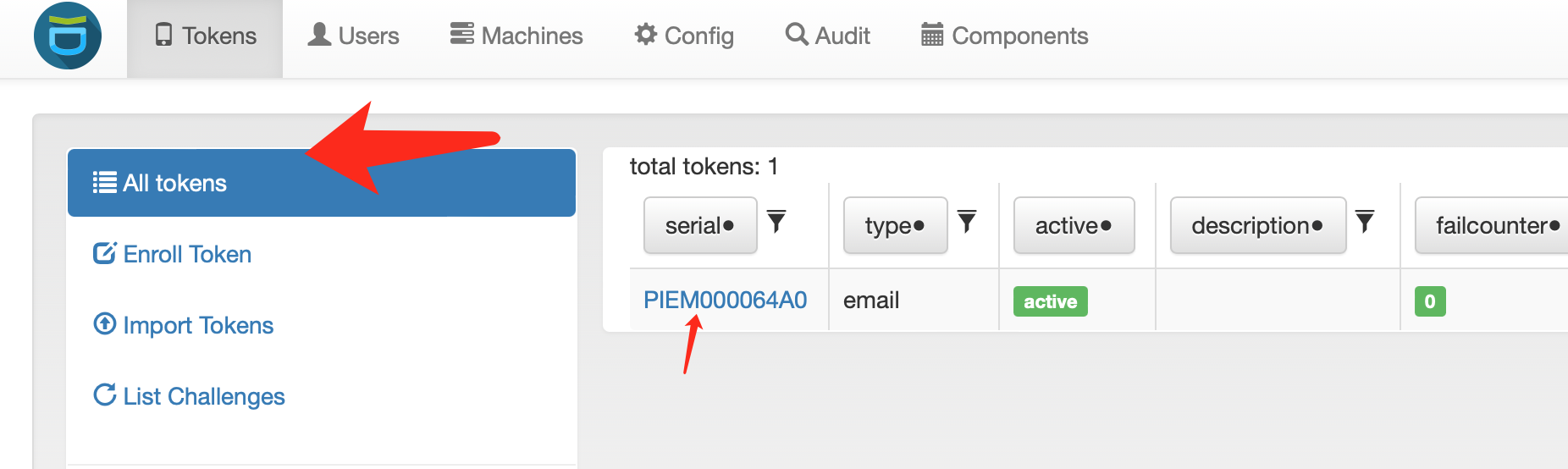
4.1 privicyIDEA配置-用户token
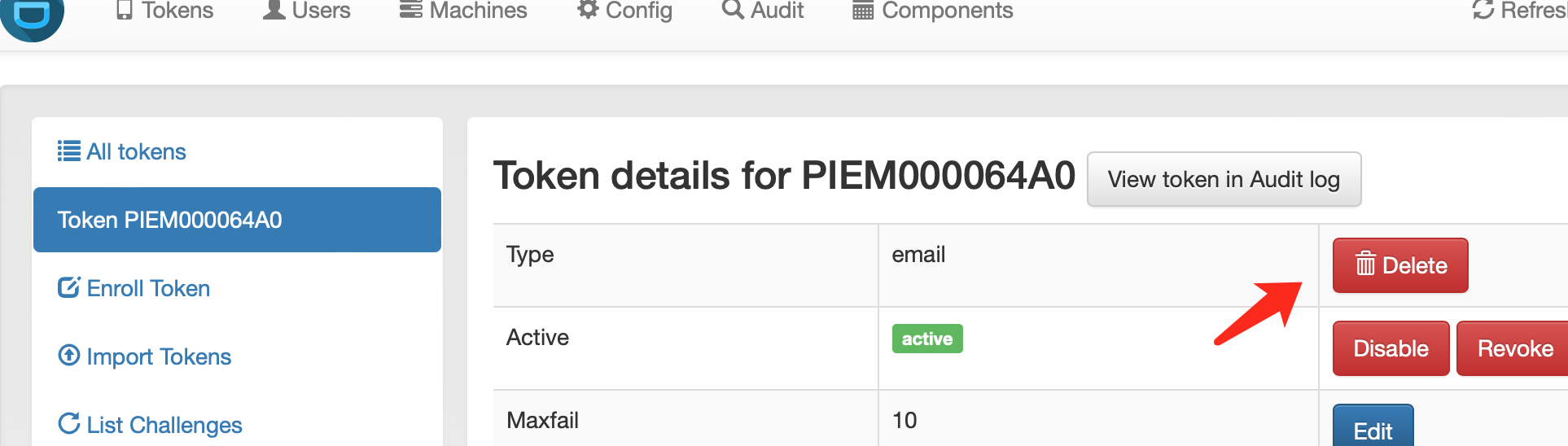
删除并新建用户token
删除之前针对用户建立的EMAIL token
![]()
![]()
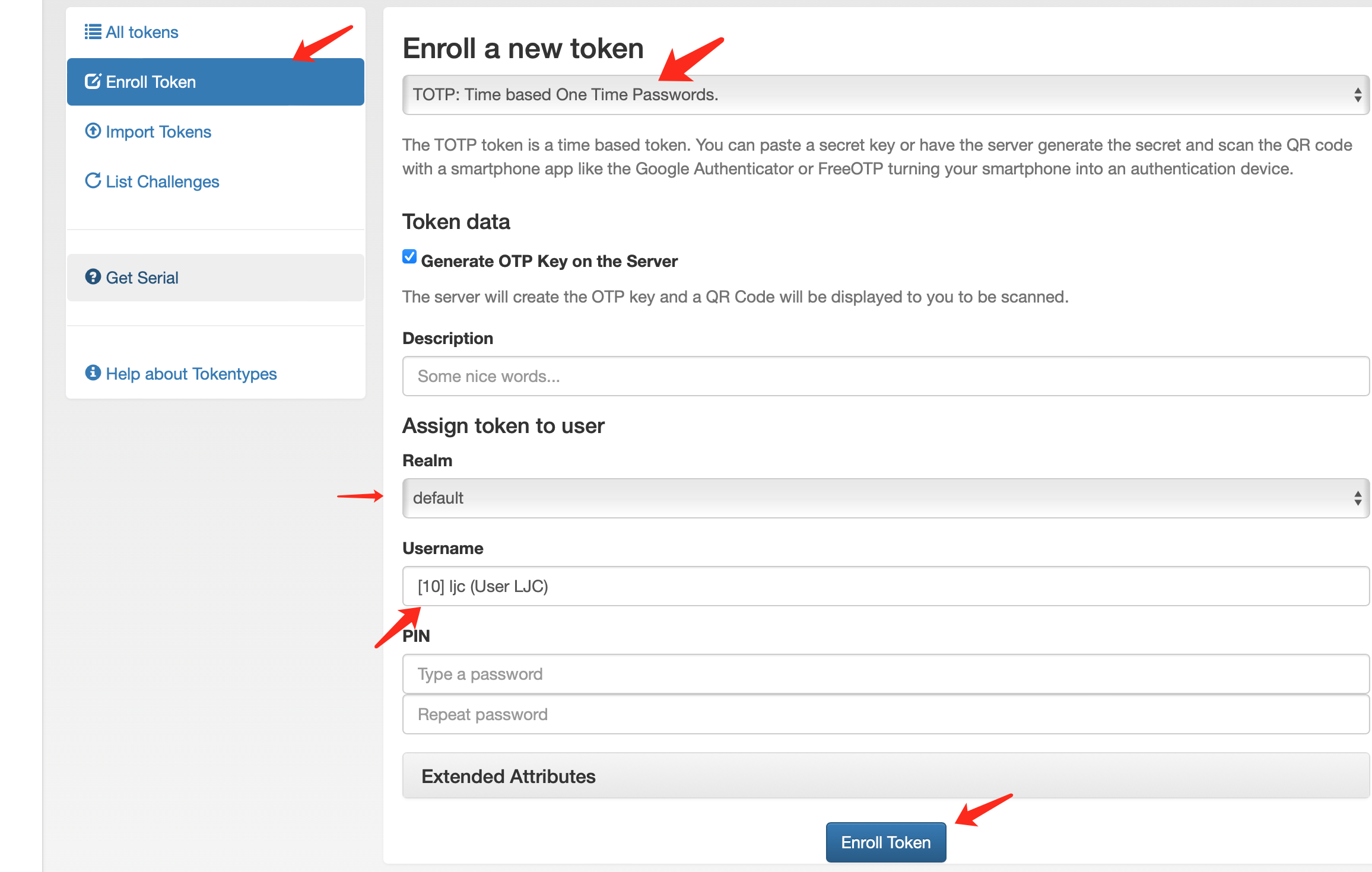
新建用户TOTP token
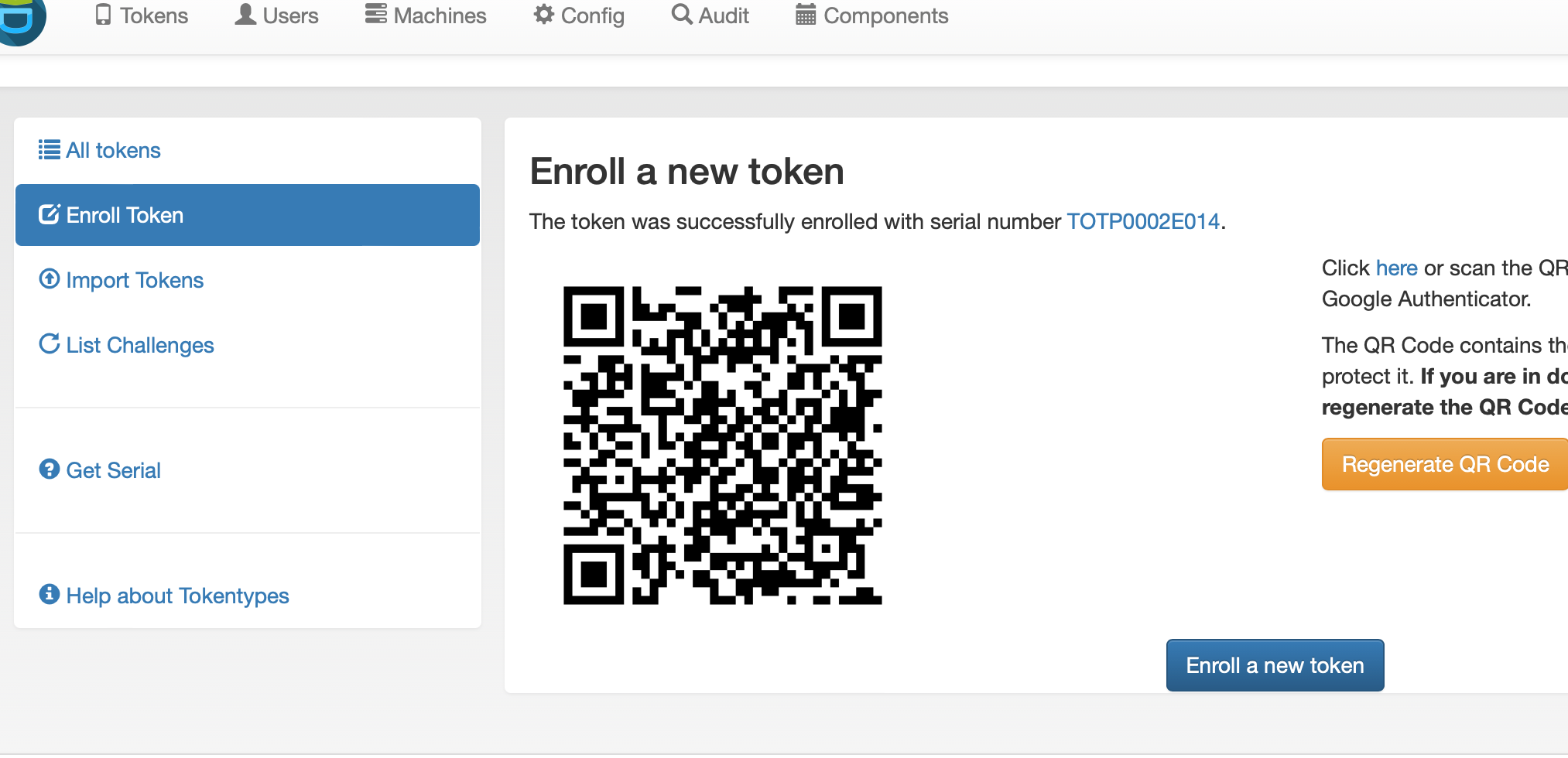
![]()
![]()
用google authentior或其它TOTP二步验证工具扫描二维码
![]()
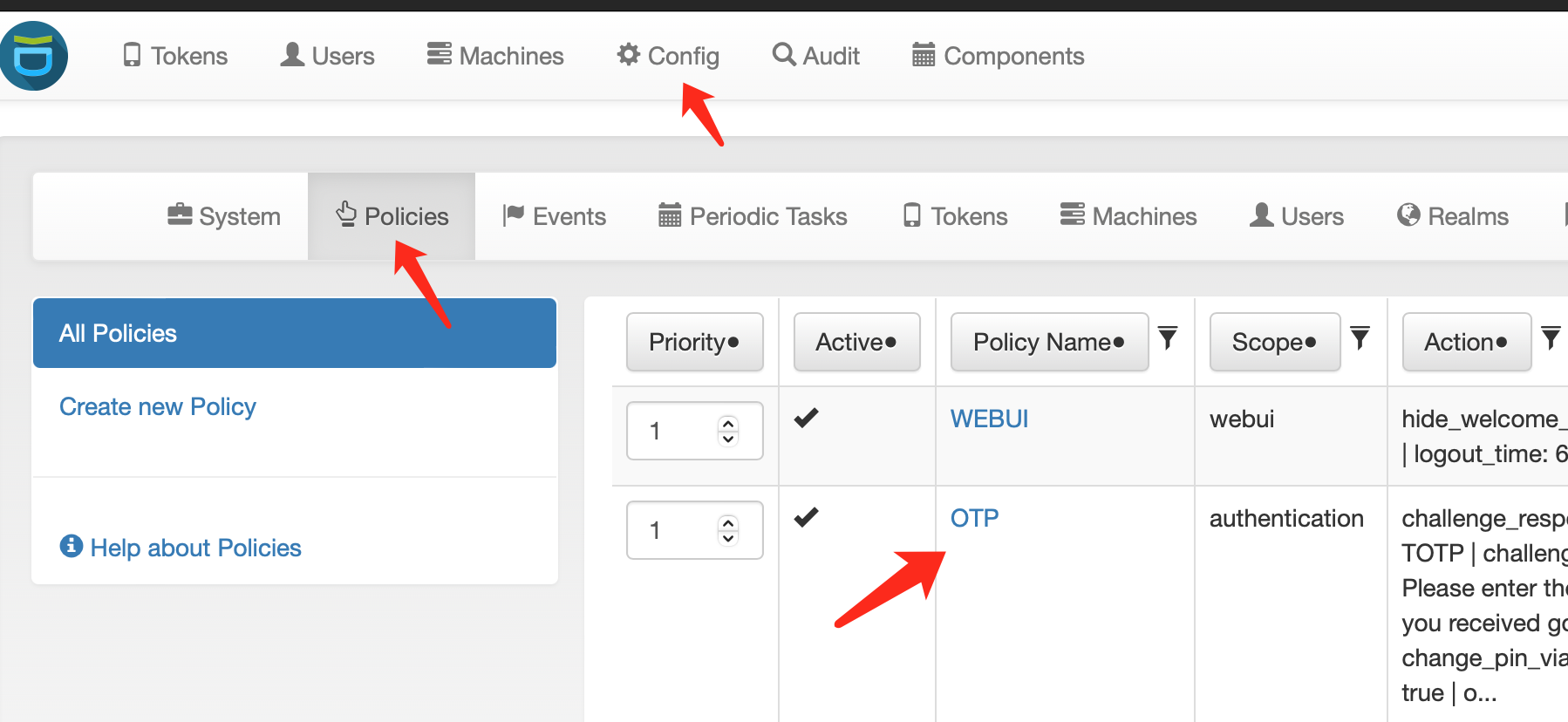
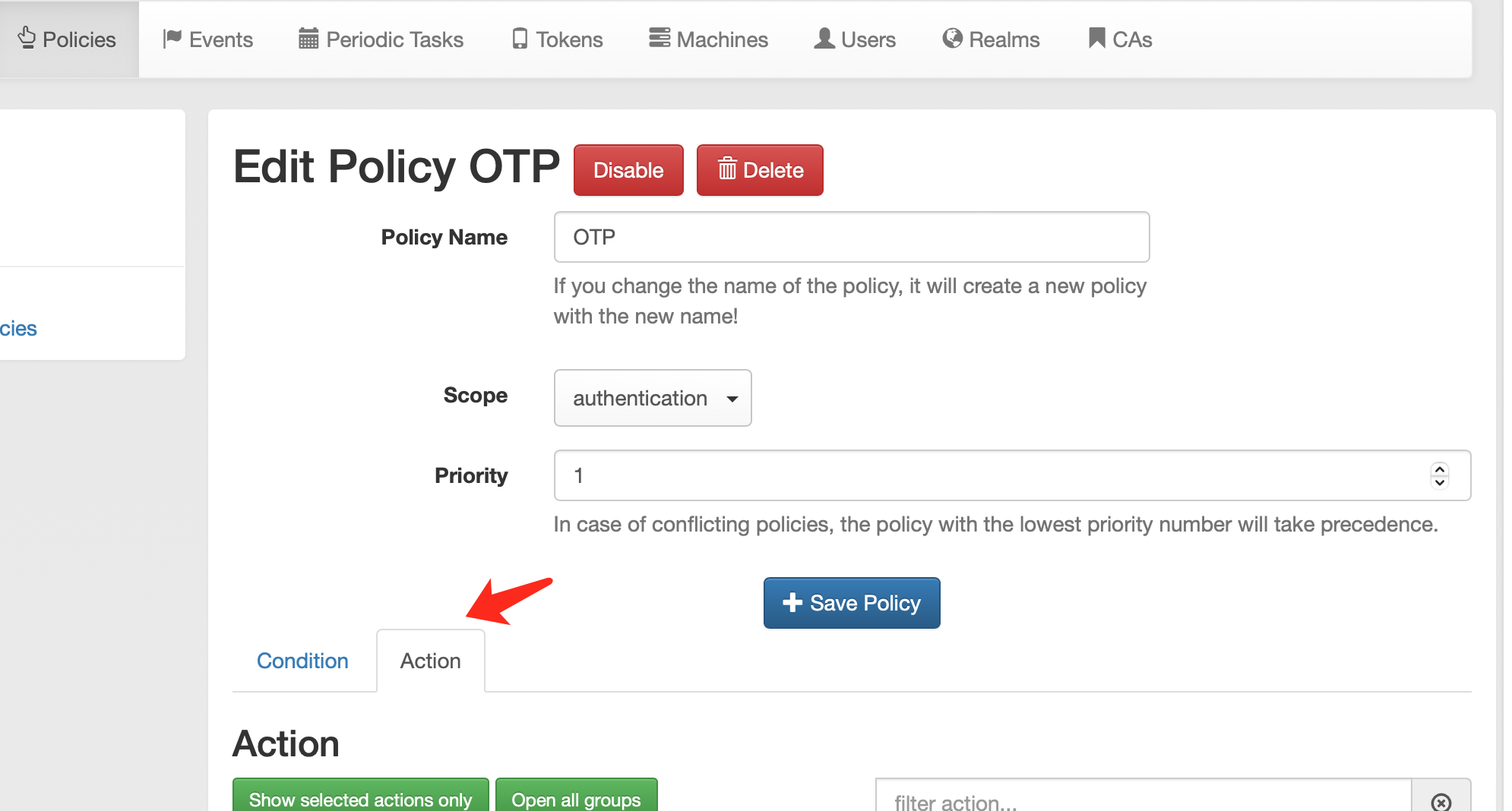
4.2 privicyIDEA配置-认证策略
![]()
![]()
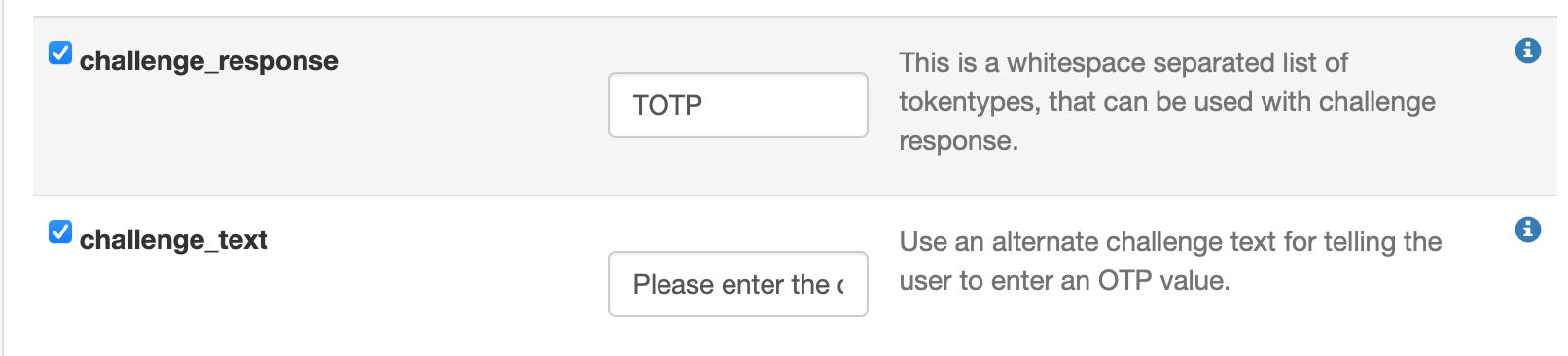
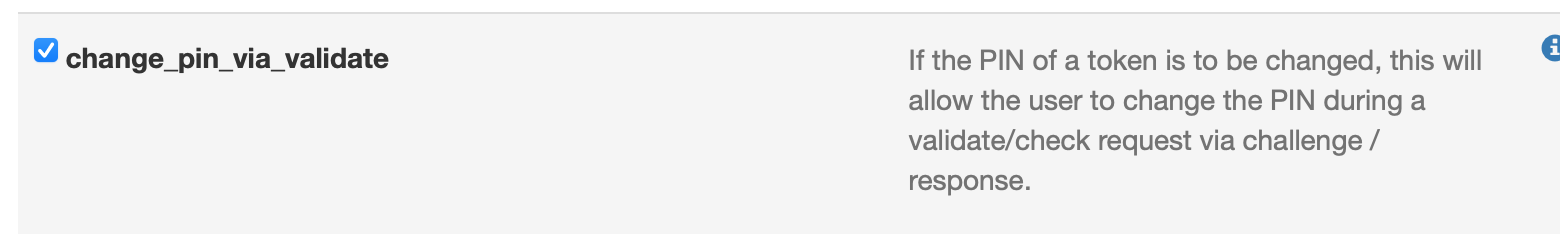
取消前面步骤配置的Email选项,只选择以下四项
challenge_response填写 TOTP
challenge_text 内容随意,主要用于提醒用户输入二步验证密码
![]()
![]()
![]()
4.3 用户登陆
![]()
![]()
登陆成功
![]()
客户端登陆
![]()
![]()
![]()
五、多种认证方式
比如用户1 使用邮件二次认证 用户2、3使用TOTP二次认证,用户4直接密码认证不做二次认证,可创建多条策略policy,针对不同用户做不同认证
![]()












 浙公网安备 33010602011771号
浙公网安备 33010602011771号