kubernetes(七)--安全机制
一、安全机制说明
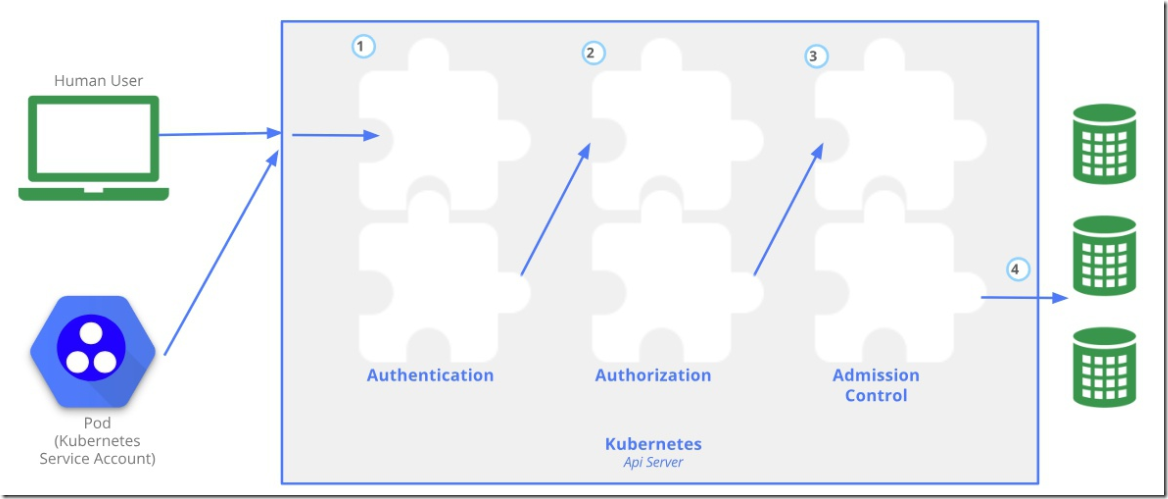
Kubernetes 作为一个分布式集群的管理工具,保证集群的安全性是其一个重要的任务。API Server 是集群内部各个组件通信的中介,也是外部控制的入口。所以 Kubernetes 的安全机制基本就是围绕保护 API Server 来设计的。Kubernetes 使用了认证(Authentication)、鉴权(Authorization)、准入控制(AdmissionControl)三步来保证API Server的安全
二、认证--Authentication
2.1、认证的方式
1)HTTP Token 认证
通过一个 Token 来识别合法用户
HTTP Token 的认证是用一个很长的特殊编码方式的并且难以被模仿的字符串 - Token 来表达客户的一种方式。Token 是一个很长的很复杂的字符串,每一个 Token 对应一个用户名存储在 API Server 能访问的文件中。当客户端发起 API 调用请求时,需要在 HTTP Header 里放入 Token
2)HTTP Base 认证
通过用户名+密码的方式认证
用户名+密码用 BASE64 算法进行编码后的字符串放在 HTTP Request 中的 HeatherAuthorization 域里发送给服务端,服务端收到后进行编码,获取用户名及密码
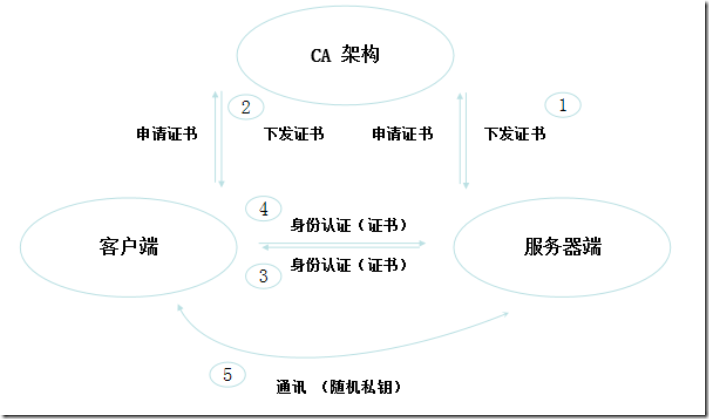
3)HTTPS 证书认证
最严格,基于 CA 根证书签名的客户端身份认证方式
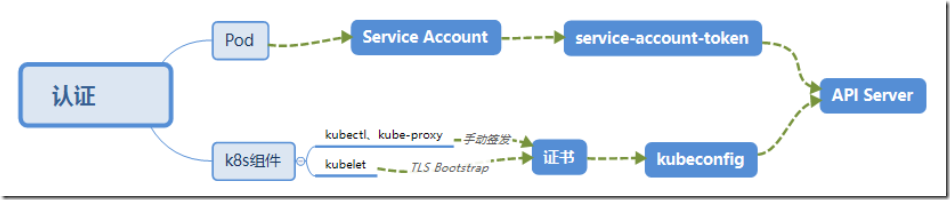
2.2、认证组件
2.2.1、两种类型
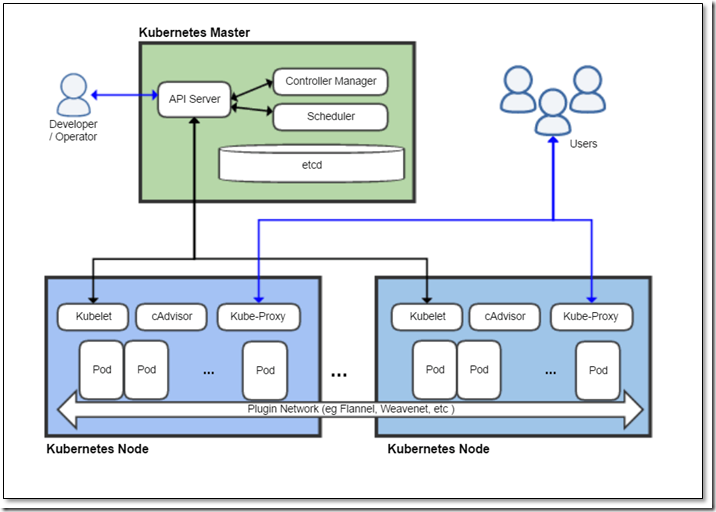
Kubenetes 组件对 API Server 的访问:kubectl、Controller Manager、Scheduler、kubelet、kube-proxy
Kubernetes 管理的 Pod 对容器的访问:Pod(dashborad 也是以 Pod 形式运行)
2.2.2、安全性说明
Controller Manager、Scheduler 与 API Server 在同一台机器,所以直接使用 API Server 的非安全端口访问,--insecure-bind-address=127.0.0.1
kubectl、kubelet、kube-proxy 访问 API Server 就都需要证书进行 HTTPS 双向认证
2.2.3、证书颁发
手动签发:通过 k8s 集群的跟 ca 进行签发 HTTPS 证书
自动签发:kubelet 首次访问 API Server 时,使用 token 做认证,通过后,Controller Manager 会为kubelet 生成一个证书,以后的访问都是用证书做认证了
2.3、kubeconfig
kubeconfig 文件包含集群参数(CA证书、API Server地址),客户端参数(上面生成的证书和私钥),集群context 信息(集群名称、用户名)。Kubenetes 组件通过启动时指定不同的 kubeconfig 文件可以切换到不同的集群
[root@k8s-master01 ~]# cd .kube/
[root@k8s-master01 .kube]# ls
cache config http-cache
[root@k8s-master01 .kube]# cat config
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUN5RENDQWJDZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBREFWTVJNd0VRWURWUVFERXdwcmRXSmwKY201bGRHVnpNQjRYRFRJd01ESXdNakEyTVRjMU4xb1hEVE13TURFek1EQTJNVGMxTjFvd0ZURVRNQkVHQTFVRQpBeE1LYTNWaVpYSnVaWFJsY3pDQ0FTSXdEUVlKS29aSWh2Y05BUUVCQlFBRGdnRVBBRENDQVFvQ2dnRUJBTmVzCkFic2VOa1hjZzFuUzVFRFh3b1Q3RS9oTU9BL3JFUTZNSDJIQkM2VkhndG5mSmVJMkRqOFZ2cVVHTnI1ZGtGN1QKdmpxbDFRVDQ1bENKWElkdWhqK1FadVJjQk13RkdKd09KODQzRkd0QWdSemVBT1RPSHE4VXREc0hNU3NuOHRTdApaVFFEbEMxK1lwUUI1a0xDM2FRWnJpZzJpMlRURXYwTjk1RWU1T2FUOUkzRjdOWGR4d25SYTNSQjZyUnRwdlhLCkhEdnVUK2JBQmdJVUd5Rk1PNkdxRU44UnN6SnhYME5ha0N4ajlzMGNaUy9VTzF4UCtOcm9GcHdVSzI0dU1SeG8KSHhCRG1KaHZ1K2gzWjFMRzRJK1gzTy9vUXpMSGZFZEtmUkRKL083MTVMRWtrNzYwMVhLYTNBQXJmQzkvQllabQo1Q3pLL29uVFRTSjZESTJlcUlVQ0F3RUFBYU1qTUNFd0RnWURWUjBQQVFIL0JBUURBZ0trTUE4R0ExVWRFd0VCCi93UUZNQU1CQWY4d0RRWUpLb1pJaHZjTkFRRUxCUUFEZ2dFQkFFVmRpc0dwOUdGcHhZT2tMd2tCT2s5S2ZhaEsKWk1KdWdvSklFdnVTS0VqOTdiUkpCSE5pVmk0aHJjN2JXUWVxVlRxYlc0MGhFQkdjUXpKeUVySmlZVzJsSTVoawp4bWtXSSs5R3JsaHBtU1NGbC93SUxTbWRCaG9jcjdZMEU5THNoTHdPUmdzYm00U1BxSmVXNHNjNml1V08wTENkCjlhSzQ2VGh3RTYxM3JWblVvb2YzQUtyUENhaDBFc1ZJZFlEemFFamFTcHBHOWVzYVVsQjV4NjFWMTR5MkFvOS8KWUNtK3h4c29QamdBMHlHS0dMWHl1cE1CN25NWEhoK0pQWVpmUUFDeU5yVWVoM0RWa2hrMVJtb0wrUm81VEdaRApoUVd5aEM3N0w2T05kTm9takdEcVRnTktob3VxMEdNNVdGSEhhdENQSmNlcW8weEIzbWF1ZDd0dE9tUT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=
server: https://10.0.0.11:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: kubernetes-admin
name: kubernetes-admin@kubernetes
current-context: kubernetes-admin@kubernetes
kind: Config
preferences: {}
users:
- name: kubernetes-admin
user:
client-certificate-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUM4akNDQWRxZ0F3SUJBZ0lJUkZmT05zRGdhUVV3RFFZSktvWklodmNOQVFFTEJRQXdGVEVUTUJFR0ExVUUKQXhNS2EzVmlaWEp1WlhSbGN6QWVGdzB5TURBeU1ESXdOakUzTlRkYUZ3MHlNVEF5TURFd05qRTNOVGhhTURReApGekFWQmdOVkJBb1REbk41YzNSbGJUcHRZWE4wWlhKek1Sa3dGd1lEVlFRREV4QnJkV0psY201bGRHVnpMV0ZrCmJXbHVNSUlCSWpBTkJna3Foa2lHOXcwQkFRRUZBQU9DQVE4QU1JSUJDZ0tDQVFFQXZ1U1BGQTVObDgvWTNoT1YKMXorL3EzcElHRUs0V0JJRnJmRDhlV2xkNldOZzMzWFV3NE5YYlkwNDIyMlhrTThuOWhlYjhsL0tPdlVZSVg4SwpMTGhnQTEzTVZsa0grU0ZwYURIdVJnRVVKVFM5UVUzbFdFNXYwWjJQd2tOdzdVVmJYNzhFZzRUWWI1YUxzTThsClJJeFNDeWhBa2tmUkd2WXJQMXZpSFhrNWtiWVY1MkZiVVlUOXRmUGZreWFkTWRVNW83YkJiU3daeVNjK1FiQmcKR3l4OEVCeng4NEZycUpydXFXeTZaQlMveFBlc3czWVVpbDJhaDJzelNVOXJPY2xucVFoODN1ZzFUMFBVczhZMwpYanVOVmtveWpQcUFjMHRkSit1cXRzVUtFdTJmU0hScDFSL3YyKzV3QTNXdUsyeTIxZWROZVI5c2ZTeWY3SWsyCjZFKzZRd0lEQVFBQm95Y3dKVEFPQmdOVkhROEJBZjhFQkFNQ0JhQXdFd1lEVlIwbEJBd3dDZ1lJS3dZQkJRVUgKQXdJd0RRWUpLb1pJaHZjTkFRRUxCUUFEZ2dFQkFKWTJDbzl4L0hOZmJQVVlwenBLOE0vaHI3SlRwODFNR0lnTQpOaWp0LzhpdGRNY0QxbTJFSkZwK3pyZDhmeGd6Zi9tWkd2ZWRWQzROVzVhZkJ6bDJEbXJnaWtlOXVwSzRqMHpyClduTFRaN003L3dBWFpjRW1lck1pYVFiRkRXVzZtaEJIK2tUckxieDYyZXFBWCsrQUNZZWU3TnQrQk5YOS8vNE4KMlNkT3pkbkw0NVl2QnFLNlAxb3VKUklBQSt6ZWdYa3hyKzBpMmVZL21ncGhmY3JreUhWY1RCcGVhU3lObkR1UwpuaGphNitNb3l5SGx3elRHTkI3L01aajlQOVVrUHRuKzR3S1pPRUxlN1NrNER6N0JMNVJVaGZ0MmZRL1I2bjczCkJRMVo1eWRQVHhIUTI5aUtabitxOXRWUjNiTUpWdVloQnhyaHhRK3o1MGhNdmxZbnpHYz0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=
client-key-data: LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFcEFJQkFBS0NBUUVBdnVTUEZBNU5sOC9ZM2hPVjF6Ky9xM3BJR0VLNFdCSUZyZkQ4ZVdsZDZXTmczM1hVCnc0TlhiWTA0MjIyWGtNOG45aGViOGwvS092VVlJWDhLTExoZ0ExM01WbGtIK1NGcGFESHVSZ0VVSlRTOVFVM2wKV0U1djBaMlB3a053N1VWYlg3OEVnNFRZYjVhTHNNOGxSSXhTQ3loQWtrZlJHdllyUDF2aUhYazVrYllWNTJGYgpVWVQ5dGZQZmt5YWRNZFU1bzdiQmJTd1p5U2MrUWJCZ0d5eDhFQnp4ODRGcnFKcnVxV3k2WkJTL3hQZXN3M1lVCmlsMmFoMnN6U1U5ck9jbG5xUWg4M3VnMVQwUFVzOFkzWGp1TlZrb3lqUHFBYzB0ZEordXF0c1VLRXUyZlNIUnAKMVIvdjIrNXdBM1d1SzJ5MjFlZE5lUjlzZlN5ZjdJazI2RSs2UXdJREFRQUJBb0lCQUJoUmk3eTFXY00yVWwxdwpSMDJGckloTzZySlVoYUdLb2ppWGs4SnYzdXZsb2lpMW5TWlBMQ3NqcTVPZ3NZZGNMSzRZTWVDOXZVaW5ncXg1CnY3VVV3LzZKeTRkUWpraDVyakQ4ODJydHBrQmJLS1VTSkY2TWw0Z3Z0Mm03Sjc3Q2NES1JaaVRQSHJlUWlUazgKR25aU0hmMlg0aW9BaGk0V0lFcFJEVXhON2p5V3FrcmxBTGFBL1ZiSnR4UWowMlVnem0rNnd4ejUrNTlka0tDRgppV1F4eVdrV3FkRjQ3L05HcUFXVFFjbStPcmYwNmt1VTArV240cDVyK1kvTWgxdFJpbjFXMnhKUlB4dFN3MTFRCkE3Nm5mTDRGZnhuYkwvOEVHWE1zd0NucUZBVzhmZDhXKzRXSlo4c0dNTkYvVDZqZ3hxVWhERGl6S3RCendTT2gKWW9iMmdLRUNnWUVBOEpWdVNVaDh0MklGUm9pMVlXWENuNnltQzdCOTNtc3RvMmpxN3JGTEJRVXRFZDRDYXRzagpCa3dNL2xWbDIzK1FZVVljYUNhSU5YdHYyUy9aNUxKM3d6SytWWXdWcm9pRDlvck5RTjJBZ3NiejZFa1d6Ly8xClBXWUsrNXVxR1dlN3djbExvK3VGSXpuZUdpYmlOU2xQMmdONHhCc0FydU8zblAvWFRlbnBRQkVDZ1lFQXl4LzkKMEhhd3BZSzRtd0h6cDZOWXpRZzY1L2hRNEppSXpGMGl1SGR0a3N2Rk1qbG93bzB1ZGxNSVBtY3NsOXJWRnN2bgpTY1BZRmFjTng5RDRjdkNsc1o2eEtxRTNYS2pUdDBjaDlPc25EWFVOVnpHaTcxVXhRT3p6dnVCbytrMXAzZUNqCnJnSzRLZXpwUHVlejJPb1BZc0lSU0JoaHlJNjlETUZpTnI0cGFSTUNnWUVBNGxSUitwTTg4UEEvOGtrdUNjREgKeFp1UVlqTFpWdU1SZmtkM3JMSVIxMWsxT3pmV29sd2hxUXptdEdYMmV2YVpCMG9EODE4OGlNUGxSemNqRDJsdQpEYTZ4TEoycTBCVVJ3R0I0RSt2TnVEb2V2NG55OGg3andhMDc2OVJYdzZxNUVlZWpSMFNNYmNWRTB1bDlxWEdCCjg2R01mVURCOWNXNHVQUmV3cWVwaldFQ2dZRUFsMWZveHpBSUFlbmFIalJnRk9HU1FvSUZVZDBrZFpOeEtjT2oKSVFwcTY5dER2RjRsL2Y4dlJSNHNvRUpEYVltMUIxMDVvUzU0aS9tQ1BRVW9lSXR4Q1Z5UjZJOWlMbm5qOVVUYwp1aDJUWldWM1lTWXNubUk5Wm9DbVErdjBpN3F1VEpFWm80ZUhMRVhHckFYN2JIMUlwVzZ2YmFZdEJUL0ZBQUgrCmFZZGFWMTBDZ1lBNnhWbXdlcHZBckNiVDZFQUE1RVVJQ2RKZTAzRFd5a3VzMnVQRU5qSmtUS3RJM3lueHl1b0gKbkVQL3FleHZqZkpMckVFcXZNemxMTVhzdTdTSElXeWdSNWRxem41Z3pvOFBwV0d3VkJ2OTM2V1o3SnRTMGdEUAprUzlkUnpWYlZKREJwZWdQdHNFQ09aQUJrTzI5QzhzY2IvUnZFdnB4YkpJdkpvTWF4b3FHWEE9PQotLS0tLUVORCBSU0EgUFJJVkFURSBLRVktLS0tLQo=2.4、ServiceAccount
Pod中的容器访问API Server。因为Pod的创建、销毁是动态的,所以要为它手动生成证书就不可行了。Kubenetes使用了Service Account解决Pod 访问API Server的认证问题
2.5、Secret 与 SA 的关系
Kubernetes 设计了一种资源对象叫做 Secret,分为两类,一种是用于 ServiceAccount 的 service-account-token,另一种是用于保存用户自定义保密信息的 Opaque。ServiceAccount 中用到包含三个部分:Token、ca.crt、namespace
- token是使用 API Server 私钥签名的 JWT。用于访问API Server时,Server端认证
- ca.crt,根证书。用于Client端验证API Server发送的证书
- namespace, 标识这个service-account-token的作用域名空间
[root@k8s-master01 ~]# kubectl get secret --all-namespaces [root@k8s-master01 ~]# kubectl describe secret default-token-5gm9r --namespace=kube-system
默认情况下,每个 namespace 都会有一个 ServiceAccount,如果 Pod 在创建时没有指定 ServiceAccount,就会使用 Pod 所属的 namespace 的 ServiceAccount
2.6、总结
三、鉴权--Authorization
上面认证过程,只是确认通信的双方都确认了对方是可信的,可以相互通信。而鉴权是确定请求方有哪些资源的权限。API Server 目前支持以下几种授权策略(通过 API Server 的启动参数 “--authorization-mode” 设置)
- AlwaysDeny:表示拒绝所有的请求,一般用于测试
- AlwaysAllow:允许接收所有请求,如果集群不需要授权流程,则可以采用该策略
- ABAC(Attribute-Based Access Control):基于属性的访问控制,表示使用用户配置的授权规则对用户请求进行匹配和控制
- Webbook:通过调用外部 REST 服务对用户进行授权
- RBAC(Role-Based Access Control):基于角色的访问控制,现行默认规则(常用)
3.1、RBAC 授权模式
RBAC(Role-Based Access Control)基于角色的访问控制,在 Kubernetes 1.5 中引入,现行版本成为默认标准。相对其它访问控制方式,拥有以下优势:
- 对集群中的资源和非资源均拥有完整的覆盖
- 整个 RBAC 完全由几个 API 对象完成,同其它 API 对象一样,可以用 kubectl 或 API 进行操作
- 可以在运行时进行调整,无需重启 API Server
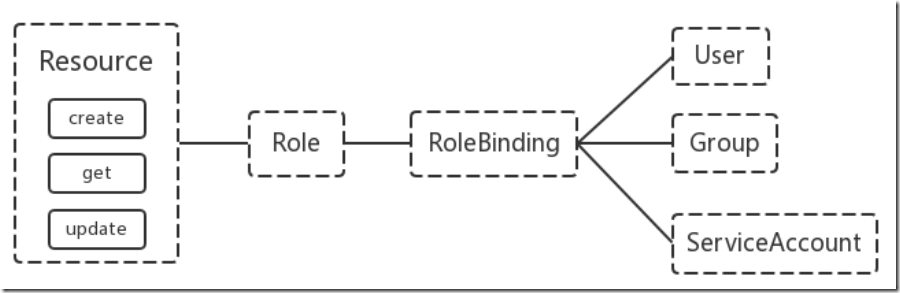
3.2、RBAC 的 API 资源对象说明
RBAC 引入了 4 个新的顶级资源对象:Role、ClusterRole、RoleBinding、ClusterRoleBinding,4 种对象类型均可以通过 kubectl 与 API 操作
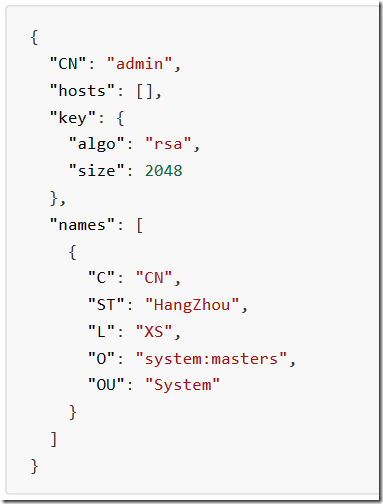
需要注意的是 Kubenetes 并不会提供用户管理,那么 User、Group、ServiceAccount 指定的用户又是从哪里来的呢? Kubenetes 组件(kubectl、kube-proxy)或是其他自定义的用户在向 CA 申请证书时,需要提供一个证书请求文件
API Server会把客户端证书的CN字段作为User,把names.O字段作为Group
kubelet 使用 TLS Bootstaping 认证时,API Server 可以使用 Bootstrap Tokens 或者 Token authenticationfile 验证=token,无论哪一种,Kubenetes 都会为 token 绑定一个默认的 User 和 Group
Pod使用 ServiceAccount 认证时,service-account-token 中的 JWT 会保存 User 信息
有了用户信息,再创建一对角色/角色绑定(集群角色/集群角色绑定)资源对象,就可以完成权限绑定了
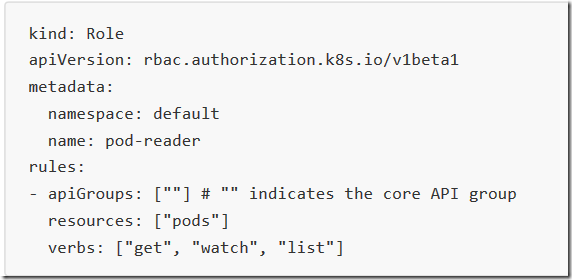
3.3、Role and ClusterRole
在 RBAC API 中,Role 表示一组规则权限,权限只会增加(累加权限),不存在一个资源一开始就有很多权限而通过RBAC 对其进行减少的操作;Role 可以定义在一个 namespace 中,如果想要跨 namespace 则可以创建ClusterRole
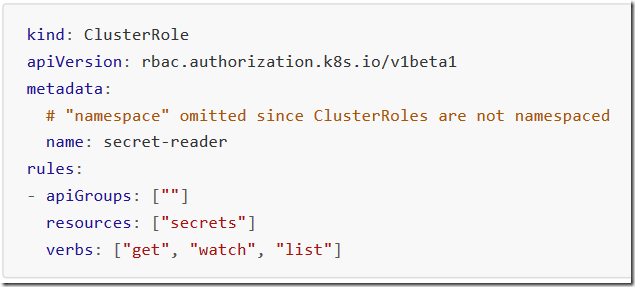
ClusterRole 具有与 Role 相同的权限角色控制能力,不同的是 ClusterRole 是集群级别的,ClusterRole 可以用于:
- 集群级别的资源控制( 例如 node 访问权限 )
- 非资源型 endpoints( 例如/healthz访问 )
- 所有命名空间资源控制(例如 pods )
3.4、RoleBinding and ClusterRoleBinding
RoloBinding 可以将角色中定义的权限授予用户或用户组,RoleBinding 包含一组权限列表(subjects),权限列表中包含有不同形式的待授予权限资源类型(users, groups, or service accounts);RoloBinding 同样包含对被Bind 的 Role 引用;RoleBinding 适用于某个命名空间内授权,而 ClusterRoleBinding 适用于集群范围内的授权
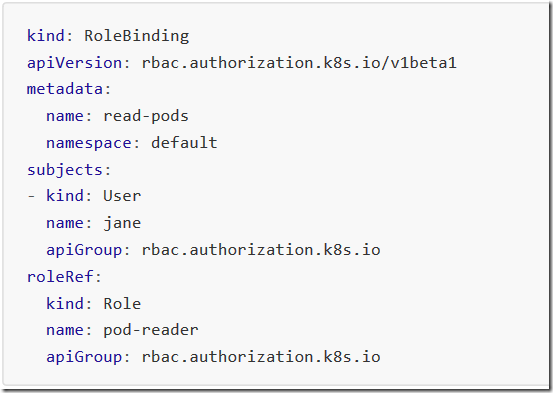
示例:将 default 命名空间的pod-reader Role 授予 jane 用户,此后 jane 用户在 default 命名空间中将具有pod-reader的权限
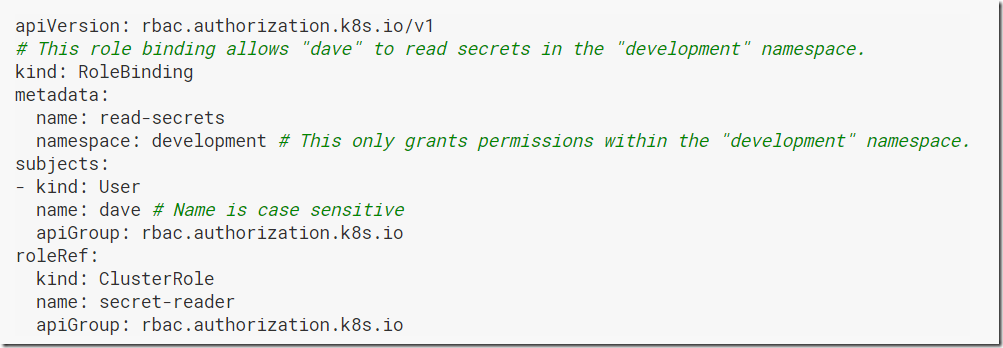
RoleBinding 同样可以引用 ClusterRole 来对当前 namespace 内用户、用户组或 ServiceAccount 进行授权,这种操作允许集群管理员在整个集群内定义一些通用的 ClusterRole,然后在不同的 namespace 中使用RoleBinding 来引用
例如,以下 RoleBinding 引用了一个 ClusterRole,这个 ClusterRole 具有整个集群内对 secrets 的访问权限;但是其授权用户dave只能访问 development 空间中的 secrets(因为 RoleBinding 定义在 development 命名空间)
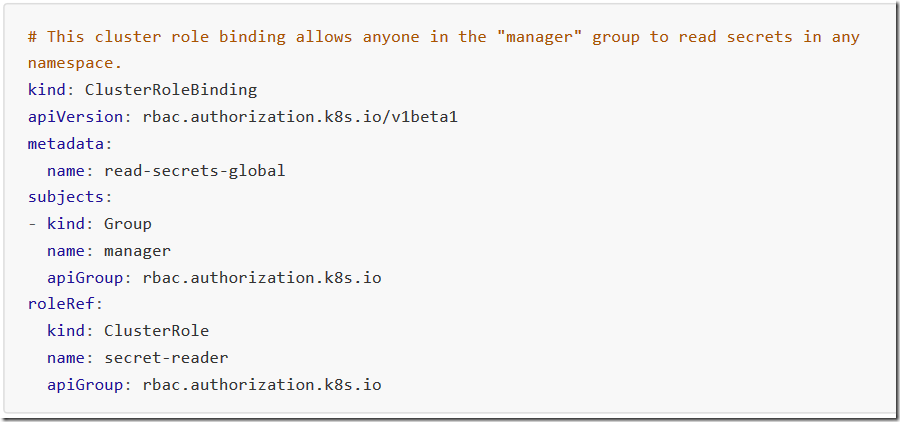
使用 ClusterRoleBinding 可以对整个集群中的所有命名空间资源权限进行授权;以下 ClusterRoleBinding 样例展示了授权 manager 组内所有用户在全部命名空间中对 secrets 进行访问
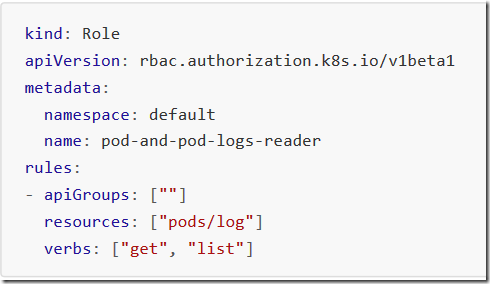
3.5、Resources
Kubernetes 集群内一些资源一般以其名称字符串来表示,这些字符串一般会在 API 的 URL 地址中出现;同时某些资源也会包含子资源,例如 logs 资源就属于 pods 的子资源,API 中 URL 样例如下
GET /api/v1/namespaces/{namespace}/pods/{name}/log如果要在 RBAC 授权模型中控制这些子资源的访问权限,可以通过 / 分隔符来实现,以下是一个定义 pods 资资源logs 访问权限的 Role 定义样例
3.6、to Subjects
RoleBinding 和 ClusterRoleBinding 可以将 Role 绑定到 Subjects;Subjects 可以是 groups、users 或者service accounts
Subjects 中 Users 使用字符串表示,它可以是一个普通的名字字符串,如 “alice”;也可以是 email 格式的邮箱地址,如 “linux@163.com”;甚至是一组字符串形式的数字 ID 。但是 Users 的前缀 system: 是系统保留的,集群管理员应该确保普通用户不会使用这个前缀格式
Groups 书写格式与 Users 相同,都为一个字符串,并且没有特定的格式要求;同样 system: 前缀为系统保留
3.7、实践:创建一个用户只能管理 dev 空间
1)linux服务器创建用户
[root@k8s-master01 ~]# useradd devuser [root@k8s-master01 ~]# echo "123456"|passwd --stdin devuser Changing password for user devuser. passwd: all authentication tokens updated successfully. [root@k8s-master01 ~]# su - devuser [devuser@k8s-master01 ~]$ kubectl get pod The connection to the server localhost:8080 was refused - did you specify the right host or port?
2)下载证书生成工具
[root@k8s-master01 k8s]# mkdir Authorization [root@k8s-master01 k8s]# cd Authorization [root@k8s-master01 Authorization]# pwd /root/k8s/Authorization [root@k8s-master01 Authorization]# wget https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 [root@k8s-master01 Authorization]# wget https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 [root@k8s-master01 Authorization]# wget https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 [root@k8s-master01 Authorization]# chmod +x ./* [root@k8s-master01 Authorization]# ls cfssl-certinfo_linux-amd64 cfssljson_linux-amd64 cfssl_linux-amd64 [root@k8s-master01 Authorization]# cp cfssl_linux-amd64 /usr/local/bin/cfssl [root@k8s-master01 Authorization]# cp cfssljson_linux-amd64 /usr/local/bin/cfssljson [root@k8s-master01 Authorization]# cp cfssl-certinfo_linux-amd64 /usr/local/bin/cfssl-certinfo
3)创建证书请求文件
[root@k8s-master01 k8s]# pwd
/root/k8s
[root@k8s-master01 k8s]# mkdir cert
[root@k8s-master01 k8s]# cd cert/
[root@k8s-master01 cert]# vim devuser-csr.json
{
"CN": "devuser",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
4 )创建证书
[root@k8s-master01 pki]# cfssl gencert -ca=ca.crt -ca-key=ca.key -profile=kubernetes /root/k8s/cert/devuser-csr.json | cfssljson -bare devuser
2020/02/06 10:22:57 [INFO] generate received request
2020/02/06 10:22:57 [INFO] received CSR
2020/02/06 10:22:57 [INFO] generating key: rsa-2048
2020/02/06 10:22:57 [INFO] encoded CSR
2020/02/06 10:22:57 [INFO] signed certificate with serial number 240797140666079034092581066556520895112609035699
2020/02/06 10:22:57 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for
websites. For more information see the Baseline Requirements for the Issuance and Management
of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org);
specifically, section 10.2.3 ("Information Requirements").
[root@k8s-master01 pki]# ls devuser*
devuser.csr devuser-key.pem devuser.pem5)设置集群参数
[root@k8s-master01 cert]# export KUBE_APISERVER="https://10.0.0.11:6443"
[root@k8s-master01 cert]# kubectl config set-cluster kubernetes --certificate-authority=/etc/kubernetes/pki/ca.crt --embed-certs=true --server=${KUBE_APISERVER} --kubeconfig=devuser.kubeconfig
Cluster "kubernetes" set.
[root@k8s-master01 cert]# cat devuser.kubeconfig
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUN5RENDQWJDZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBREFWTVJNd0VRWURWUVFERXdwcmRXSmwKY201bGRHVnpNQjRYRFRJd01ESXdNakEyTVRjMU4xb1hEVE13TURFek1EQTJNVGMxTjFvd0ZURVRNQkVHQTFVRQpBeE1LYTNWaVpYSnVaWFJsY3pDQ0FTSXdEUVlKS29aSWh2Y05BUUVCQlFBRGdnRVBBRENDQVFvQ2dnRUJBTmVzCkFic2VOa1hjZzFuUzVFRFh3b1Q3RS9oTU9BL3JFUTZNSDJIQkM2VkhndG5mSmVJMkRqOFZ2cVVHTnI1ZGtGN1QKdmpxbDFRVDQ1bENKWElkdWhqK1FadVJjQk13RkdKd09KODQzRkd0QWdSemVBT1RPSHE4VXREc0hNU3NuOHRTdApaVFFEbEMxK1lwUUI1a0xDM2FRWnJpZzJpMlRURXYwTjk1RWU1T2FUOUkzRjdOWGR4d25SYTNSQjZyUnRwdlhLCkhEdnVUK2JBQmdJVUd5Rk1PNkdxRU44UnN6SnhYME5ha0N4ajlzMGNaUy9VTzF4UCtOcm9GcHdVSzI0dU1SeG8KSHhCRG1KaHZ1K2gzWjFMRzRJK1gzTy9vUXpMSGZFZEtmUkRKL083MTVMRWtrNzYwMVhLYTNBQXJmQzkvQllabQo1Q3pLL29uVFRTSjZESTJlcUlVQ0F3RUFBYU1qTUNFd0RnWURWUjBQQVFIL0JBUURBZ0trTUE4R0ExVWRFd0VCCi93UUZNQU1CQWY4d0RRWUpLb1pJaHZjTkFRRUxCUUFEZ2dFQkFFVmRpc0dwOUdGcHhZT2tMd2tCT2s5S2ZhaEsKWk1KdWdvSklFdnVTS0VqOTdiUkpCSE5pVmk0aHJjN2JXUWVxVlRxYlc0MGhFQkdjUXpKeUVySmlZVzJsSTVoawp4bWtXSSs5R3JsaHBtU1NGbC93SUxTbWRCaG9jcjdZMEU5THNoTHdPUmdzYm00U1BxSmVXNHNjNml1V08wTENkCjlhSzQ2VGh3RTYxM3JWblVvb2YzQUtyUENhaDBFc1ZJZFlEemFFamFTcHBHOWVzYVVsQjV4NjFWMTR5MkFvOS8KWUNtK3h4c29QamdBMHlHS0dMWHl1cE1CN25NWEhoK0pQWVpmUUFDeU5yVWVoM0RWa2hrMVJtb0wrUm81VEdaRApoUVd5aEM3N0w2T05kTm9takdEcVRnTktob3VxMEdNNVdGSEhhdENQSmNlcW8weEIzbWF1ZDd0dE9tUT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=
server: https://10.0.0.11:6443
name: kubernetes
contexts: []
current-context: ""
kind: Config
preferences: {}
users: []6)设置客户端认证参数
[root@k8s-master01 cert]# kubectl config set-credentials devuser --client-certificate=/etc/kubernetes/pki/devuser.pem --client-key=/etc/kubernetes/pki/devuser-key.pem --embed-certs=true --kubeconfig=devuser.kubeconfig
User "devuser" set.
[root@k8s-master01 cert]# cat devuser.kubeconfig
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUN5RENDQWJDZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBREFWTVJNd0VRWURWUVFERXdwcmRXSmwKY201bGRHVnpNQjRYRFRJd01ESXdNakEyTVRjMU4xb1hEVE13TURFek1EQTJNVGMxTjFvd0ZURVRNQkVHQTFVRQpBeE1LYTNWaVpYSnVaWFJsY3pDQ0FTSXdEUVlKS29aSWh2Y05BUUVCQlFBRGdnRVBBRENDQVFvQ2dnRUJBTmVzCkFic2VOa1hjZzFuUzVFRFh3b1Q3RS9oTU9BL3JFUTZNSDJIQkM2VkhndG5mSmVJMkRqOFZ2cVVHTnI1ZGtGN1QKdmpxbDFRVDQ1bENKWElkdWhqK1FadVJjQk13RkdKd09KODQzRkd0QWdSemVBT1RPSHE4VXREc0hNU3NuOHRTdApaVFFEbEMxK1lwUUI1a0xDM2FRWnJpZzJpMlRURXYwTjk1RWU1T2FUOUkzRjdOWGR4d25SYTNSQjZyUnRwdlhLCkhEdnVUK2JBQmdJVUd5Rk1PNkdxRU44UnN6SnhYME5ha0N4ajlzMGNaUy9VTzF4UCtOcm9GcHdVSzI0dU1SeG8KSHhCRG1KaHZ1K2gzWjFMRzRJK1gzTy9vUXpMSGZFZEtmUkRKL083MTVMRWtrNzYwMVhLYTNBQXJmQzkvQllabQo1Q3pLL29uVFRTSjZESTJlcUlVQ0F3RUFBYU1qTUNFd0RnWURWUjBQQVFIL0JBUURBZ0trTUE4R0ExVWRFd0VCCi93UUZNQU1CQWY4d0RRWUpLb1pJaHZjTkFRRUxCUUFEZ2dFQkFFVmRpc0dwOUdGcHhZT2tMd2tCT2s5S2ZhaEsKWk1KdWdvSklFdnVTS0VqOTdiUkpCSE5pVmk0aHJjN2JXUWVxVlRxYlc0MGhFQkdjUXpKeUVySmlZVzJsSTVoawp4bWtXSSs5R3JsaHBtU1NGbC93SUxTbWRCaG9jcjdZMEU5THNoTHdPUmdzYm00U1BxSmVXNHNjNml1V08wTENkCjlhSzQ2VGh3RTYxM3JWblVvb2YzQUtyUENhaDBFc1ZJZFlEemFFamFTcHBHOWVzYVVsQjV4NjFWMTR5MkFvOS8KWUNtK3h4c29QamdBMHlHS0dMWHl1cE1CN25NWEhoK0pQWVpmUUFDeU5yVWVoM0RWa2hrMVJtb0wrUm81VEdaRApoUVd5aEM3N0w2T05kTm9takdEcVRnTktob3VxMEdNNVdGSEhhdENQSmNlcW8weEIzbWF1ZDd0dE9tUT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=
server: https://10.0.0.11:6443
name: kubernetes
contexts: []
current-context: ""
kind: Config
preferences: {}
users:
- name: devuser
user:
client-certificate-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURZekNDQWt1Z0F3SUJBZ0lVS2kyM25GNHFzMGJyRTBxbm43WUNqNCs4ZGJNd0RRWUpLb1pJaHZjTkFRRUwKQlFBd0ZURVRNQkVHQTFVRUF4TUthM1ZpWlhKdVpYUmxjekFlRncweU1EQXlNRFl3TWpFNE1EQmFGdzB5TVRBeQpNRFV3TWpFNE1EQmFNR0l4Q3pBSkJnTlZCQVlUQWtOT01SQXdEZ1lEVlFRSUV3ZENaV2xLYVc1bk1SQXdEZ1lEClZRUUhFd2RDWldsS2FXNW5NUXd3Q2dZRFZRUUtFd05yT0hNeER6QU5CZ05WQkFzVEJsTjVjM1JsYlRFUU1BNEcKQTFVRUF4TUhaR1YyZFhObGNqQ0NBU0l3RFFZSktvWklodmNOQVFFQkJRQURnZ0VQQURDQ0FRb0NnZ0VCQUwwRgp5NWMxQ2FmY3orcGlLSnovcXpBZGJ5TnVSa1daMWptVXZsMTNGRjZRbXkxUklPSDRtdlc0UXRibmlTZ3ljOTJ4ClAxVmVUdlZSWUZZbkVtVjRqdC81VTZZRE11RVlYNWlQUVh4dlBRbktlSnVVMmtjUWhDY3RaRkUvaGNocUtwUjEKclFYZ3ZPUTVpaHNWdGY2eTlJclM1eXVoWmZsRUpITG5lczFORzM0bFlxRjJvV1NqQzArN051bzZ2ZEtwaEpsTworajEwMmRQM0c0VSt0MzZXc3lra2lFMmRhVkxHN2hLWjBtNWZzcUdxQmpOdDFFUXdtd0YwZWZLUlAzVHRZY2M4CkF5dkxObDYyM2hGTDg3RE5PbVRjU3FPR2duRTB1dW1jQ3Zqa1poaFF5YTNsMkh5dDQyRkhLczdkSHlFTlhMVEMKUFJYQVkyMTVSNE9PdG5LM01CY0NBd0VBQWFOZU1Gd3dEZ1lEVlIwUEFRSC9CQVFEQWdXZ01CMEdBMVVkSlFRVwpNQlFHQ0NzR0FRVUZCd01CQmdnckJnRUZCUWNEQWpBTUJnTlZIUk1CQWY4RUFqQUFNQjBHQTFVZERnUVdCQlRBCjlINTR4UEZGSEFnclVhTzNURXp0akZaWnZUQU5CZ2txaGtpRzl3MEJBUXNGQUFPQ0FRRUFDUnRKa0dYaGplQ0kKMllKcWZCZTAzdDN4NytJalgrQk1abDc5UENuQnVTWUZZaERGQVIxWUpsU2w0cnZidTc2VlpFalRmL0tySHBOZQpjZEk5R3loUlZjT2QyNkpMd3lReGxzTEl2M3ZXb2lNZGQ1TnIxSXp3T2Y0dzZDazNybk1VK3VadDd3enRSUU02CmpKY1hVUktOVXhhay9xc21uRkFWNHVKQkRVeUNvZUZqcFJnMGQ0dEVHelk4eWRLN3RJZmQvbU8zWUZWSWNiOW4KTGg4cGZpSWVMY1lpbWJ5eEpZeTRaTHVNdnE4c21WYmJaQTZGZkh4NnVLSm41aWJ2T2N1cUxuOGJCUllZTFdUUgpma1A0OHdJNTdvUC9CWnlxVGhNMDRqZ05nVlFmU0NNZWdlK0lINjAvMDhuSzFnZzJEQ215TzdHdVlVTzluZ0hKCm5jdFp0WGpmVFE9PQotLS0tLUVORCBDRVJUSUZJQ0FURS0tLS0tCg==
client-key-data: LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFcEFJQkFBS0NBUUVBdlFYTGx6VUpwOXpQNm1Jb25QK3JNQjF2STI1R1JabldPWlMrWFhjVVhwQ2JMVkVnCjRmaWE5YmhDMXVlSktESnozYkUvVlY1TzlWRmdWaWNTWlhpTzMvbFRwZ015NFJoZm1JOUJmRzg5Q2NwNG01VGEKUnhDRUp5MWtVVCtGeUdvcWxIV3RCZUM4NURtS0d4VzEvckwwaXRMbks2RmwrVVFrY3VkNnpVMGJmaVZpb1hhaApaS01MVDdzMjZqcTkwcW1FbVU3NlBYVFowL2NiaFQ2M2ZwYXpLU1NJVFoxcFVzYnVFcG5TYmwreW9hb0dNMjNVClJEQ2JBWFI1OHBFL2RPMWh4endESzhzMlhyYmVFVXZ6c00wNlpOeEtvNGFDY1RTNjZad0srT1JtR0ZESnJlWFkKZkszallVY3F6dDBmSVExY3RNSTlGY0JqYlhsSGc0NjJjcmN3RndJREFRQUJBb0lCQUMxUkZsNUorT2FscWJNbgpsVlVPZHB3eWNsS3NQV3l5VlFtNC8ycXBBZGtxRWduclNWYmpvME1GeWdCN3dnWkJFa1kwR0ZyL0lTN3ZNNGwwCkZKVC9Na0hBSkszSVZvcGdyWXFGemMxblhkcmJEODg5QUpmSS9lWG1uQVplbEZSWUg1MDRHU012bmhtWk1lTU0KY1hWK3NlSVdiaFdudkNybWkxYUE2SkFQekdlUlpXYkd0YUprdVl3YUlJWlhXY1hydUJldWdkSW1MSTlXUDFnMwpjMXg2aXVZUGhnUkI3ZStoeGtPL0NraUZVcmdGMnJaM1dObUtrZ0hJb29uV1ZxV2lSMklpNFpkSVZrQnFBbCs0Cnd5Z2V4S21CRVNNdVpVSDVieCtTK0tGWTZEazgyVjBHSnhTZ1pJL2NDam12YW01NGEvN1AwOTBBNlpKSFNpVlgKWXdHcGdRRUNnWUVBNUdwbFE1bEF1UGowWWdUSVpDR1NaczNqNCtFQUlaekN1OU52VXE1Wm9XOUVLYU4vR0dZUQpqcTRoQkpQeEhoNzArbnN1YnhrTnNXV2lnQkhuV3ZjaFJrd2wvazl0cWgvV0JyMHp3ZE5iRGRQeks3dWJCN3BYCkpNUHd1VlUwQVI2Vm0zVXo4UklDMGZGMEQ2Zm1ZL0FTeEE2VzcvK3QwQlFYcllHVGRxejRxdE1DZ1lFQTA5bUsKNkZXa21vbU5SZ2Q0Rlc5T2FtSDlzODhIeFd2Umw4UzYzd09oRGhFSjRrQ3JVS04yYUNxREFOTm1VTVlXUFUrdApLR21sbDR6SmtFSEIza3puQWR4cThhb21sUGR4dlo5QTBOK0FDeEFKQXpRTXRlS3U1NWpjZE1NMU1SQVJiV2lyCmxKbitGRXpoelJ5anc1RmpmQjJpWk54aHVBNEc4Rm9TRGRVdWt5MENnWUFCZDZHQTVxb2d4aENqMUk0SS9xSTMKSU5sMjdFb1k3UzNmRVFPbEQxT3FFdEhvUnBHWmNZWm50RHlvRDk4N3AwMUJrcXNBc2JPQjBUcFRBa3B2TGlrNwpqMStyRzQyRHkwS1B0b1Z2bUZEOGJNRWlKY2xnS2xWRytpOUFzWWhzL1dwT25sa2dFbEtNVUxYREovdjE1bVBvCmVJT0Z0U25EclcxZGd2aVVpWlhyV3dLQmdRRFJ0MkF3WVYvQ2IvcS9ZWE41M0tjRzN4eVVuSlUzMVdVMTFkV2MKSWU2VWl6OTZqOFJIM3BtL3dwM08rbmNsN1FKbERYUUFOcDFycWo1N0pPMXpVRE82L3VXTGVJSWJJOTJmOW4vbQpoZW91aVdBeW9Kc1lqMS9QK3QzNlpLaEtlbnFXRVhFUmVXUXgybTRKYTVtZVoxWFJyMUJzZ2xIbUwxU2xLTFVJCnBvb2x2UUtCZ1FDZnltODg2VE5oYVQxRWhnYmtWVHdqMUNZQlNVM2Y3REpmVTN2UzlqYkFaekhvRXFkMkwxOGcKWjFDMlVURklaS2pHaXI2N3NXZ3ZVdG1jVDVRWTVtWmswSllLTC9INjQ0YTVMVjg3QThkUUo2dE5wczhyNlE2ZApKOGFjRVFCOURrQmFHekF6U1ZuK0RiTWQvSzdjcGlXdk1pT2tUNU5FMjdMQVplNFhWR3lid1E9PQotLS0tLUVORCBSU0EgUFJJVkFURSBLRVktLS0tLQo=7)设置上下文参数
#创建dev的namespace
[root@k8s-master01 cert]# kubectl create namespace dev
namespace/dev created
#设置上下文参数
[root@k8s-master01 cert]# kubectl config set-context kubernetes --cluster=kubernetes --user=devuser --namespace=dev --kubeconfig=devuser.kubeconfig
Context "kubernetes" created.
[root@k8s-master01 cert]# cat devuser.kubeconfig
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUN5RENDQWJDZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBREFWTVJNd0VRWURWUVFERXdwcmRXSmwKY201bGRHVnpNQjRYRFRJd01ESXdNakEyTVRjMU4xb1hEVE13TURFek1EQTJNVGMxTjFvd0ZURVRNQkVHQTFVRQpBeE1LYTNWaVpYSnVaWFJsY3pDQ0FTSXdEUVlKS29aSWh2Y05BUUVCQlFBRGdnRVBBRENDQVFvQ2dnRUJBTmVzCkFic2VOa1hjZzFuUzVFRFh3b1Q3RS9oTU9BL3JFUTZNSDJIQkM2VkhndG5mSmVJMkRqOFZ2cVVHTnI1ZGtGN1QKdmpxbDFRVDQ1bENKWElkdWhqK1FadVJjQk13RkdKd09KODQzRkd0QWdSemVBT1RPSHE4VXREc0hNU3NuOHRTdApaVFFEbEMxK1lwUUI1a0xDM2FRWnJpZzJpMlRURXYwTjk1RWU1T2FUOUkzRjdOWGR4d25SYTNSQjZyUnRwdlhLCkhEdnVUK2JBQmdJVUd5Rk1PNkdxRU44UnN6SnhYME5ha0N4ajlzMGNaUy9VTzF4UCtOcm9GcHdVSzI0dU1SeG8KSHhCRG1KaHZ1K2gzWjFMRzRJK1gzTy9vUXpMSGZFZEtmUkRKL083MTVMRWtrNzYwMVhLYTNBQXJmQzkvQllabQo1Q3pLL29uVFRTSjZESTJlcUlVQ0F3RUFBYU1qTUNFd0RnWURWUjBQQVFIL0JBUURBZ0trTUE4R0ExVWRFd0VCCi93UUZNQU1CQWY4d0RRWUpLb1pJaHZjTkFRRUxCUUFEZ2dFQkFFVmRpc0dwOUdGcHhZT2tMd2tCT2s5S2ZhaEsKWk1KdWdvSklFdnVTS0VqOTdiUkpCSE5pVmk0aHJjN2JXUWVxVlRxYlc0MGhFQkdjUXpKeUVySmlZVzJsSTVoawp4bWtXSSs5R3JsaHBtU1NGbC93SUxTbWRCaG9jcjdZMEU5THNoTHdPUmdzYm00U1BxSmVXNHNjNml1V08wTENkCjlhSzQ2VGh3RTYxM3JWblVvb2YzQUtyUENhaDBFc1ZJZFlEemFFamFTcHBHOWVzYVVsQjV4NjFWMTR5MkFvOS8KWUNtK3h4c29QamdBMHlHS0dMWHl1cE1CN25NWEhoK0pQWVpmUUFDeU5yVWVoM0RWa2hrMVJtb0wrUm81VEdaRApoUVd5aEM3N0w2T05kTm9takdEcVRnTktob3VxMEdNNVdGSEhhdENQSmNlcW8weEIzbWF1ZDd0dE9tUT0KLS0tLS1FTkQgQ0VSVElGSUNBVEUtLS0tLQo=
server: https://10.0.0.11:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
namespace: dev
user: devuser
name: kubernetes
current-context: ""
kind: Config
preferences: {}
users:
- name: devuser
user:
client-certificate-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURZekNDQWt1Z0F3SUJBZ0lVS2kyM25GNHFzMGJyRTBxbm43WUNqNCs4ZGJNd0RRWUpLb1pJaHZjTkFRRUwKQlFBd0ZURVRNQkVHQTFVRUF4TUthM1ZpWlhKdVpYUmxjekFlRncweU1EQXlNRFl3TWpFNE1EQmFGdzB5TVRBeQpNRFV3TWpFNE1EQmFNR0l4Q3pBSkJnTlZCQVlUQWtOT01SQXdEZ1lEVlFRSUV3ZENaV2xLYVc1bk1SQXdEZ1lEClZRUUhFd2RDWldsS2FXNW5NUXd3Q2dZRFZRUUtFd05yT0hNeER6QU5CZ05WQkFzVEJsTjVjM1JsYlRFUU1BNEcKQTFVRUF4TUhaR1YyZFhObGNqQ0NBU0l3RFFZSktvWklodmNOQVFFQkJRQURnZ0VQQURDQ0FRb0NnZ0VCQUwwRgp5NWMxQ2FmY3orcGlLSnovcXpBZGJ5TnVSa1daMWptVXZsMTNGRjZRbXkxUklPSDRtdlc0UXRibmlTZ3ljOTJ4ClAxVmVUdlZSWUZZbkVtVjRqdC81VTZZRE11RVlYNWlQUVh4dlBRbktlSnVVMmtjUWhDY3RaRkUvaGNocUtwUjEKclFYZ3ZPUTVpaHNWdGY2eTlJclM1eXVoWmZsRUpITG5lczFORzM0bFlxRjJvV1NqQzArN051bzZ2ZEtwaEpsTworajEwMmRQM0c0VSt0MzZXc3lra2lFMmRhVkxHN2hLWjBtNWZzcUdxQmpOdDFFUXdtd0YwZWZLUlAzVHRZY2M4CkF5dkxObDYyM2hGTDg3RE5PbVRjU3FPR2duRTB1dW1jQ3Zqa1poaFF5YTNsMkh5dDQyRkhLczdkSHlFTlhMVEMKUFJYQVkyMTVSNE9PdG5LM01CY0NBd0VBQWFOZU1Gd3dEZ1lEVlIwUEFRSC9CQVFEQWdXZ01CMEdBMVVkSlFRVwpNQlFHQ0NzR0FRVUZCd01CQmdnckJnRUZCUWNEQWpBTUJnTlZIUk1CQWY4RUFqQUFNQjBHQTFVZERnUVdCQlRBCjlINTR4UEZGSEFnclVhTzNURXp0akZaWnZUQU5CZ2txaGtpRzl3MEJBUXNGQUFPQ0FRRUFDUnRKa0dYaGplQ0kKMllKcWZCZTAzdDN4NytJalgrQk1abDc5UENuQnVTWUZZaERGQVIxWUpsU2w0cnZidTc2VlpFalRmL0tySHBOZQpjZEk5R3loUlZjT2QyNkpMd3lReGxzTEl2M3ZXb2lNZGQ1TnIxSXp3T2Y0dzZDazNybk1VK3VadDd3enRSUU02CmpKY1hVUktOVXhhay9xc21uRkFWNHVKQkRVeUNvZUZqcFJnMGQ0dEVHelk4eWRLN3RJZmQvbU8zWUZWSWNiOW4KTGg4cGZpSWVMY1lpbWJ5eEpZeTRaTHVNdnE4c21WYmJaQTZGZkh4NnVLSm41aWJ2T2N1cUxuOGJCUllZTFdUUgpma1A0OHdJNTdvUC9CWnlxVGhNMDRqZ05nVlFmU0NNZWdlK0lINjAvMDhuSzFnZzJEQ215TzdHdVlVTzluZ0hKCm5jdFp0WGpmVFE9PQotLS0tLUVORCBDRVJUSUZJQ0FURS0tLS0tCg==
client-key-data: LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFcEFJQkFBS0NBUUVBdlFYTGx6VUpwOXpQNm1Jb25QK3JNQjF2STI1R1JabldPWlMrWFhjVVhwQ2JMVkVnCjRmaWE5YmhDMXVlSktESnozYkUvVlY1TzlWRmdWaWNTWlhpTzMvbFRwZ015NFJoZm1JOUJmRzg5Q2NwNG01VGEKUnhDRUp5MWtVVCtGeUdvcWxIV3RCZUM4NURtS0d4VzEvckwwaXRMbks2RmwrVVFrY3VkNnpVMGJmaVZpb1hhaApaS01MVDdzMjZqcTkwcW1FbVU3NlBYVFowL2NiaFQ2M2ZwYXpLU1NJVFoxcFVzYnVFcG5TYmwreW9hb0dNMjNVClJEQ2JBWFI1OHBFL2RPMWh4endESzhzMlhyYmVFVXZ6c00wNlpOeEtvNGFDY1RTNjZad0srT1JtR0ZESnJlWFkKZkszallVY3F6dDBmSVExY3RNSTlGY0JqYlhsSGc0NjJjcmN3RndJREFRQUJBb0lCQUMxUkZsNUorT2FscWJNbgpsVlVPZHB3eWNsS3NQV3l5VlFtNC8ycXBBZGtxRWduclNWYmpvME1GeWdCN3dnWkJFa1kwR0ZyL0lTN3ZNNGwwCkZKVC9Na0hBSkszSVZvcGdyWXFGemMxblhkcmJEODg5QUpmSS9lWG1uQVplbEZSWUg1MDRHU012bmhtWk1lTU0KY1hWK3NlSVdiaFdudkNybWkxYUE2SkFQekdlUlpXYkd0YUprdVl3YUlJWlhXY1hydUJldWdkSW1MSTlXUDFnMwpjMXg2aXVZUGhnUkI3ZStoeGtPL0NraUZVcmdGMnJaM1dObUtrZ0hJb29uV1ZxV2lSMklpNFpkSVZrQnFBbCs0Cnd5Z2V4S21CRVNNdVpVSDVieCtTK0tGWTZEazgyVjBHSnhTZ1pJL2NDam12YW01NGEvN1AwOTBBNlpKSFNpVlgKWXdHcGdRRUNnWUVBNUdwbFE1bEF1UGowWWdUSVpDR1NaczNqNCtFQUlaekN1OU52VXE1Wm9XOUVLYU4vR0dZUQpqcTRoQkpQeEhoNzArbnN1YnhrTnNXV2lnQkhuV3ZjaFJrd2wvazl0cWgvV0JyMHp3ZE5iRGRQeks3dWJCN3BYCkpNUHd1VlUwQVI2Vm0zVXo4UklDMGZGMEQ2Zm1ZL0FTeEE2VzcvK3QwQlFYcllHVGRxejRxdE1DZ1lFQTA5bUsKNkZXa21vbU5SZ2Q0Rlc5T2FtSDlzODhIeFd2Umw4UzYzd09oRGhFSjRrQ3JVS04yYUNxREFOTm1VTVlXUFUrdApLR21sbDR6SmtFSEIza3puQWR4cThhb21sUGR4dlo5QTBOK0FDeEFKQXpRTXRlS3U1NWpjZE1NMU1SQVJiV2lyCmxKbitGRXpoelJ5anc1RmpmQjJpWk54aHVBNEc4Rm9TRGRVdWt5MENnWUFCZDZHQTVxb2d4aENqMUk0SS9xSTMKSU5sMjdFb1k3UzNmRVFPbEQxT3FFdEhvUnBHWmNZWm50RHlvRDk4N3AwMUJrcXNBc2JPQjBUcFRBa3B2TGlrNwpqMStyRzQyRHkwS1B0b1Z2bUZEOGJNRWlKY2xnS2xWRytpOUFzWWhzL1dwT25sa2dFbEtNVUxYREovdjE1bVBvCmVJT0Z0U25EclcxZGd2aVVpWlhyV3dLQmdRRFJ0MkF3WVYvQ2IvcS9ZWE41M0tjRzN4eVVuSlUzMVdVMTFkV2MKSWU2VWl6OTZqOFJIM3BtL3dwM08rbmNsN1FKbERYUUFOcDFycWo1N0pPMXpVRE82L3VXTGVJSWJJOTJmOW4vbQpoZW91aVdBeW9Kc1lqMS9QK3QzNlpLaEtlbnFXRVhFUmVXUXgybTRKYTVtZVoxWFJyMUJzZ2xIbUwxU2xLTFVJCnBvb2x2UUtCZ1FDZnltODg2VE5oYVQxRWhnYmtWVHdqMUNZQlNVM2Y3REpmVTN2UzlqYkFaekhvRXFkMkwxOGcKWjFDMlVURklaS2pHaXI2N3NXZ3ZVdG1jVDVRWTVtWmswSllLTC9INjQ0YTVMVjg3QThkUUo2dE5wczhyNlE2ZApKOGFjRVFCOURrQmFHekF6U1ZuK0RiTWQvSzdjcGlXdk1pT2tUNU5FMjdMQVplNFhWR3lid1E9PQotLS0tLUVORCBSU0EgUFJJVkFURSBLRVktLS0tLQo=8)创建rolebinding角色绑定
#创建角色绑定
[root@k8s-master01 cert]# kubectl create rolebinding devuser-admin-binding --clusterrole=admin --user=devuser --namespace=dev
rolebinding.rbac.authorization.k8s.io/devuser-admin-binding created
#将配置文件拷贝置devuser用户家目录并授权
[root@k8s-master01 cert]# mkdir /home/devuser/.kube
[root@k8s-master01 cert]# cp devuser.kubeconfig /home/devuser/.kube
[root@k8s-master01 cert]# chown devuser:devuser /home/devuser/.kube/devuser.kubeconfig
#重命名
[root@k8s-master01 cert]# cp /home/devuser/.kube/{devuser.kubeconfig,config}
[root@k8s-master01 cert]# ls /home/devuser/.kube/
config devuser.kubeconfig
[root@k8s-master01 cert]# chown -R devuser:devuser /home/devuser/.kube #特别注意要授权,报错error: open /home/devuser/.kube/config.lock: permission denied9)devuser用户切换上下文
[devuser@k8s-master01 ~]$ cd .kube/ [devuser@k8s-master01 .kube]$ kubectl config use-context kubernetes --kubeconfig=config Switched to context "kubernetes". [devuser@k8s-master01 .kube]$ kubectl get pod No resources found.
10)测试
[devuser@k8s-master01 ~]$ kubectl run nginx --image=hub.dianchou.com/library/myapp:v1 kubectl run --generator=deployment/apps.v1 is DEPRECATED and will be removed in a future version. Use kubectl run --generator=run-pod/v1 or kubectl create instead. deployment.apps/nginx created [devuser@k8s-master01 ~]$ kubectl get pod NAME READY STATUS RESTARTS AGE nginx-7f5f6bd68c-xj4lb 1/1 Running 0 11s [root@k8s-master01 ~]# kubectl get pod --all-namespaces -o wide|grep nginx dev nginx-7f5f6bd68c-xj4lb 1/1 Running 0 90s 10.244.1.238 k8s-node01 <none> <none> ingress-nginx nginx-ingress-controller-5876d56d4c-d7gb8 1/1 Running 0 18h 10.244.2.174 k8s-node02 <none> <none> [devuser@k8s-master01 ~]$ kubectl get pod -n default Error from server (Forbidden): pods is forbidden: User "devuser" cannot list resource "pods" in API group "" in the namespace "default"
四、准入控制
准入控制是API Server的插件集合,通过添加不同的插件,实现额外的准入控制规则。甚至于API Server的一些主要的功能都需要通过 Admission Controllers 实现,比如 ServiceAccount
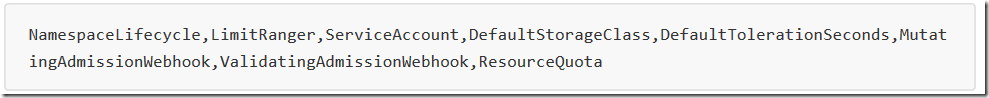
官方文档上有一份针对不同版本的准入控制器推荐列表,其中最新的 1.14 的推荐列表是:
列举几个插件的功能:
- NamespaceLifecycle:防止在不存在的 namespace 上创建对象,防止删除系统预置 namespace,删除namespace 时,连带删除它的所有资源对象。
- LimitRanger:确保请求的资源不会超过资源所在 Namespace 的 LimitRange 的限制。
- ServiceAccount:实现了自动化添加 ServiceAccount。
- ResourceQuota:确保请求的资源不会超过资源的 ResourceQuota 限制。
-------------------------------------------
个性签名:独学而无友,则孤陋而寡闻。做一个灵魂有趣的人!