靶机渗透练习59-digitalworld.local:snakeoil
靶机描述
靶机地址:https://www.vulnhub.com/entry/digitalworldlocal-snakeoil,738/
Description
Recently, Good Tech Inc. has decided to change their application development process. However, their applications look broken and too basic. Is this an application full of snakeoil, or are they insecure too? This goes beyond PEN-200, and some web application development expertise could be helpful.
If you MUST have hints for this machine: SNAKEOIL is (#1): a hint by itself, (#2): full of disallowed methods, (#3): a single file full of problems.
一、搭建靶机环境
攻击机Kali:
IP地址:192.168.9.7
靶机:
IP地址:192.168.9.55
注:靶机与Kali的IP地址只需要在同一局域网即可(同一个网段,即两虚拟机处于同一网络模式)
该靶机环境搭建如下
- 将下载好的靶机环境,导入 VritualBox,设置为 Host-Only 模式
- 将 VMware 中桥接模式网卡设置为 VritualBox 的 Host-only
二、实战
2.1网络扫描
2.1.1 启动靶机和Kali后进行扫描
方法一、arp-scan -I eth0 -l (指定网卡扫)
arp-scan -I eth0 -l
⬢ snakeoil arp-scan -I eth0 -l
Interface: eth0, type: EN10MB, MAC: 00:50:56:27:27:36, IPv4: 192.168.9.7
Starting arp-scan 1.9.7 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.9.2 08:00:27:02:10:5c PCS Systemtechnik GmbH
192.168.9.55 08:00:27:be:c3:35 PCS Systemtechnik GmbH
2 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.7: 256 hosts scanned in 1.937 seconds (132.16 hosts/sec). 2 responded
⬢ snakeoil
方法二、masscan 扫描的网段 -p 扫描端口号
masscan 192.168.184.0/24 -p 80,22
方法三、netdiscover -i 网卡-r 网段
netdiscover -i eth0 -r 192.168.184.0/24
方法四、等你们补充
2.1.2 查看靶机开放的端口
使用nmap -A -sV -T4 -p- 靶机ip查看靶机开放的端口
⬢ snakeoil nmap -A -sV -T4 -p- 192.168.9.55
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-28 14:32 CST
Nmap scan report for bogon (192.168.9.55)
Host is up (0.00032s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 73:a4:8f:94:a2:20:68:50:5a:ae:e1:d3:60:8d:ff:55 (RSA)
| 256 f3:1b:d8:c3:0c:3f:5e:6b:ac:99:52:80:7b:d6:b6:e7 (ECDSA)
|_ 256 ea:61:64:b6:3b:d3:84:01:50:d8:1a:ab:38:29:12:e1 (ED25519)
80/tcp open http nginx 1.14.2
|_http-title: Welcome to SNAKEOIL!
|_http-server-header: nginx/1.14.2
8080/tcp open http nginx 1.14.2
|_http-title: Welcome to Good Tech Inc.'s Snake Oil Project
|_http-open-proxy: Proxy might be redirecting requests
|_http-server-header: nginx/1.14.2
MAC Address: 08:00:27:BE:C3:35 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.6
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.32 ms bogon (192.168.9.55)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 9.67 seconds
22---ssh---OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
80---http---nginx 1.14.2
8080---http---nginx 1.14.2
2.2枚举漏洞
2.2.1 80 端口分析
扫描一下目录:gobuster dir -u http://192.168.9.55/ -x html,zip,bak,txt,php --wordlist=/usr/share/wordlists/dirb/common.txt -f
⬢ snakeoil gobuster dir -u http://192.168.9.55/ -x html,zip,bak,txt,php --wordlist=/usr/share/wordlists/dirb/common.txt -f
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.9.55/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Extensions: bak,txt,php,html,zip
[+] Add Slash: true
[+] Timeout: 10s
===============================================================
2022/03/28 14:55:40 Starting gobuster in directory enumeration mode
===============================================================
===============================================================
2022/03/28 14:55:42 Finished
===============================================================
⬢ snakeoil
dirsearch -u http://192.168.9.55
⬢ snakeoil dirsearch -u http://192.168.9.55
_|. _ _ _ _ _ _|_ v0.4.2
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 30 | Wordlist size: 10927
Output File: /root/.dirsearch/reports/192.168.9.55/_22-03-28_14-54-41.txt
Error Log: /root/.dirsearch/logs/errors-22-03-28_14-54-41.log
Target: http://192.168.9.55/
[14:54:41] Starting:
Task Completed
换字典换工具均无果
2.2.2 8080端口分析
JWT基础分析
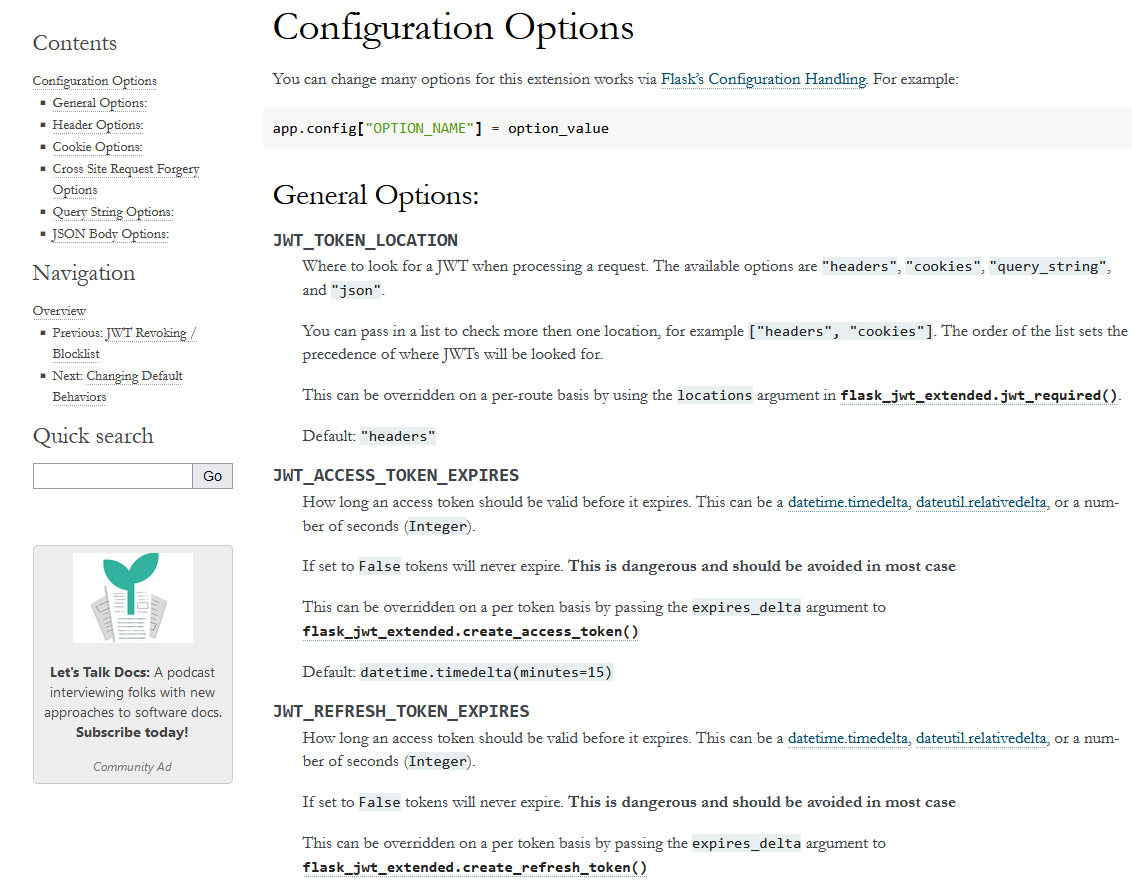
在Useful Links 发现JWTs以及https://flask-jwt-extended.readthedocs.io/en/stable/options/
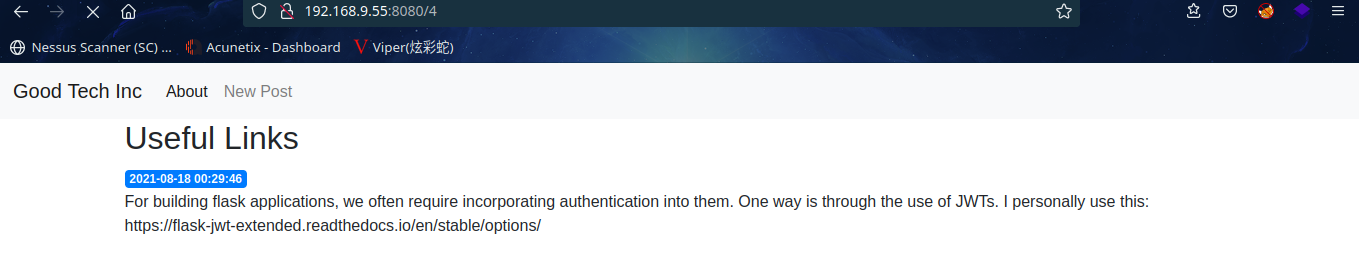
访问其链接发现是一些JWT的配置信息
扫描一下目录: dirsearch -u http://192.168.9.55:8080
⬢ snakeoil dirsearch -u http://192.168.9.55:8080
_|. _ _ _ _ _ _|_ v0.4.2
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 30 | Wordlist size: 10927
Output File: /root/.dirsearch/reports/192.168.9.55-8080/_22-03-28_15-04-27.txt
Error Log: /root/.dirsearch/logs/errors-22-03-28_15-04-27.log
Target: http://192.168.9.55:8080/
[15:04:27] Starting:
[15:04:29] 200 - 2KB - /01
[15:04:29] 200 - 2KB - /02
[15:04:29] 200 - 2KB - /04
[15:04:29] 200 - 2KB - /1
[15:04:29] 200 - 2KB - /2
[15:04:29] 200 - 2KB - /4
[15:04:43] 405 - 64B - /login
[15:04:48] 200 - 29B - /registration
[15:04:48] 500 - 37B - /secret
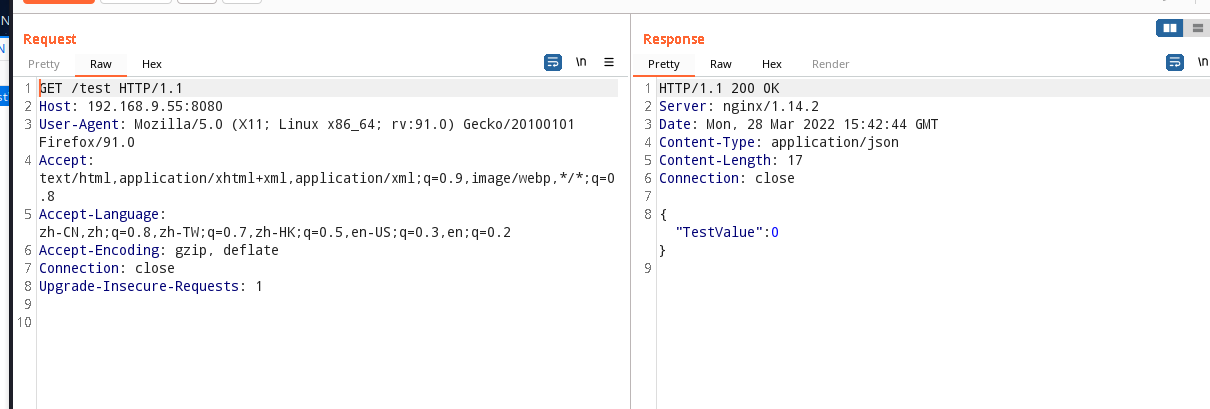
[15:04:50] 200 - 17B - /test
[15:04:52] 200 - 140B - /users
Task Completed
⬢ snakeoil
挨个访问一下,
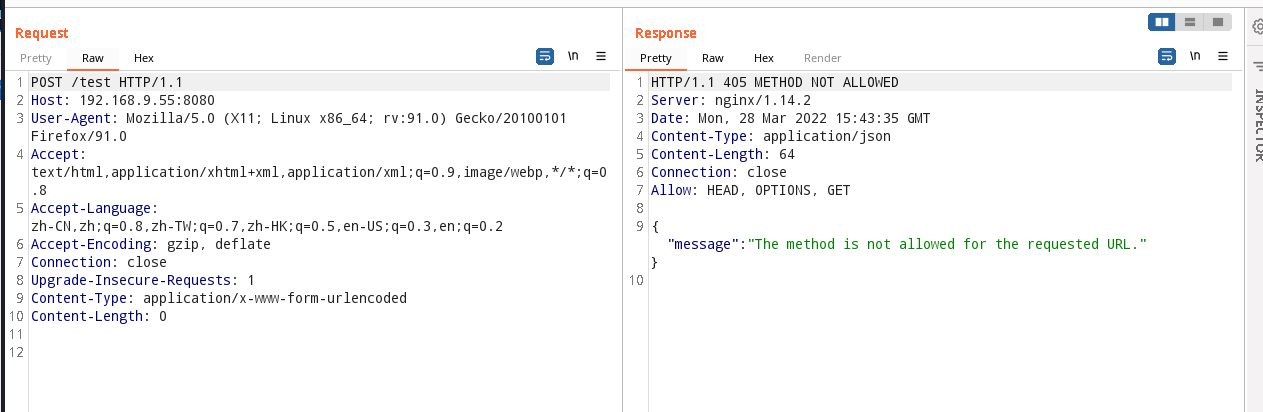
http://192.168.9.55:8080/login
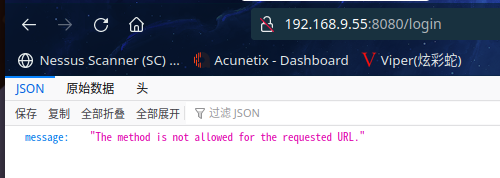
请求的url不允许使用该方法
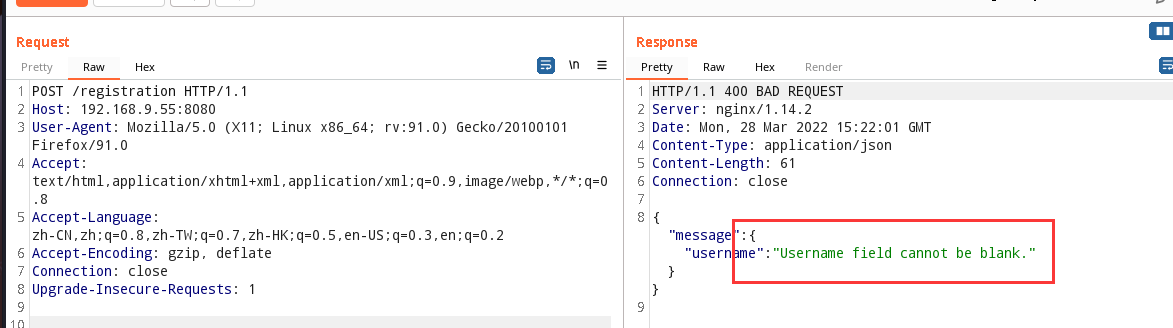
抓包修改一下方法
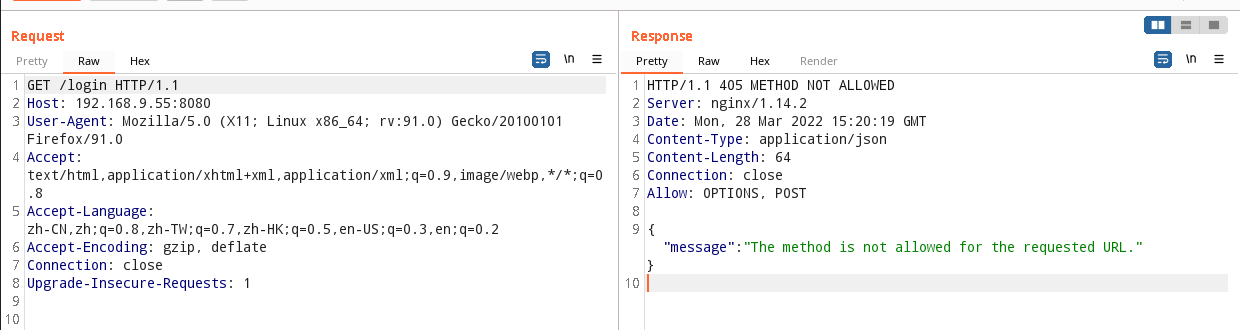
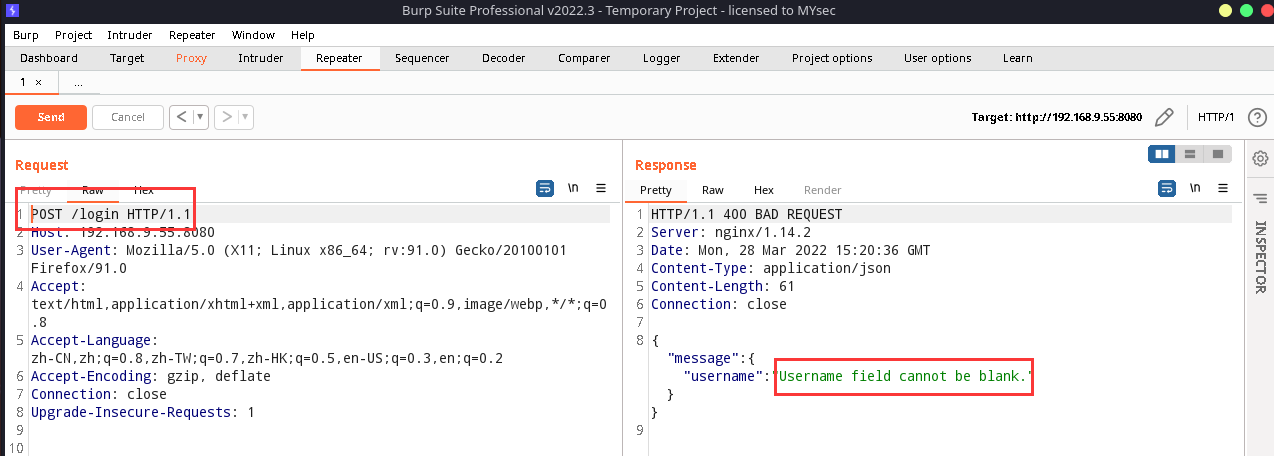
username 字段不能为空,先放一边
http://192.168.9.55:8080/registration
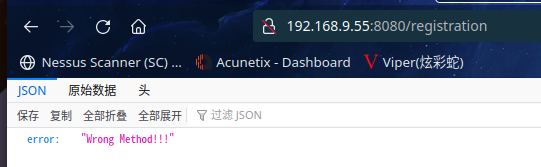
同样的抓包更改一下方法
直接访问http://192.168.9.55:8080/users
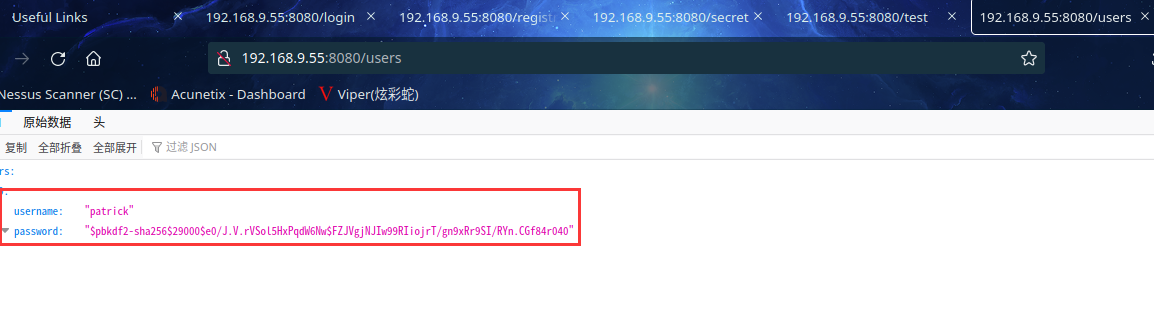
发现用户名和加密过的密码,说明有两个字段,也就是说,POST请求有两个字段,分别是username和password
重新发包给注册界面,尝试注册用户test
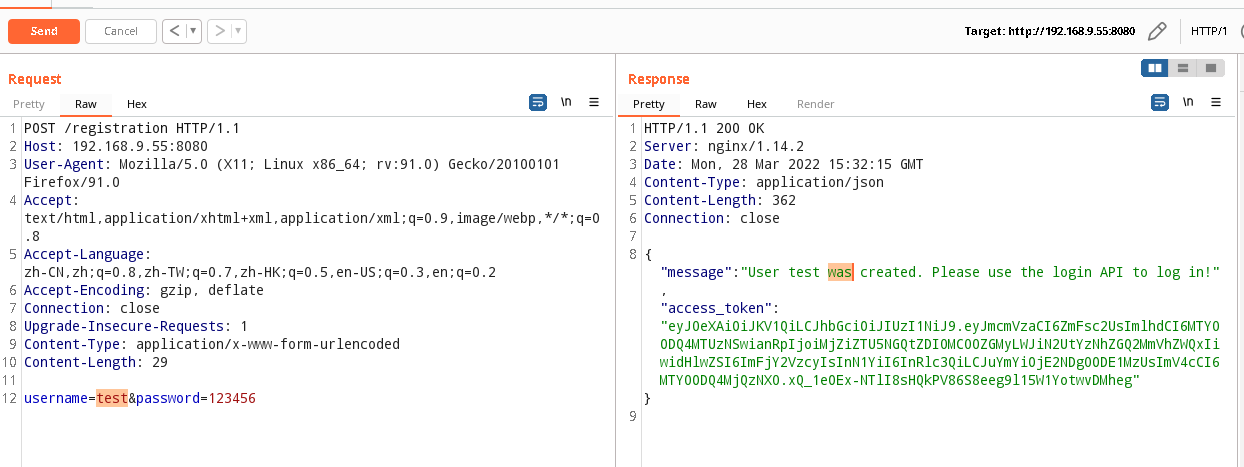
成功注册,回到登录页面登陆一下,用刚创建的用户进行登录:
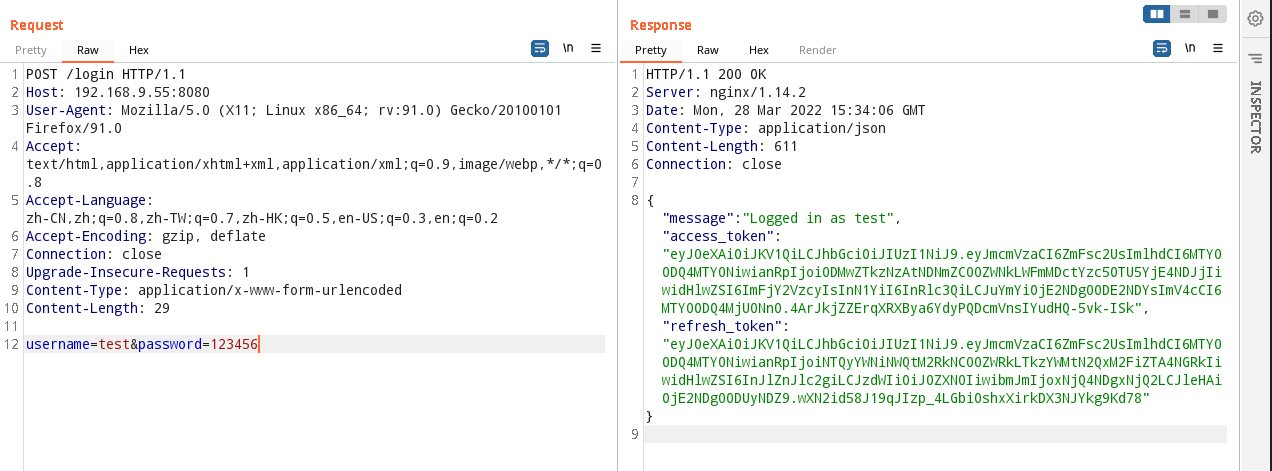
成功登录,并发现access_token及refresh_token
登录后,咱们访问扫描出的其他页面
/create 页面
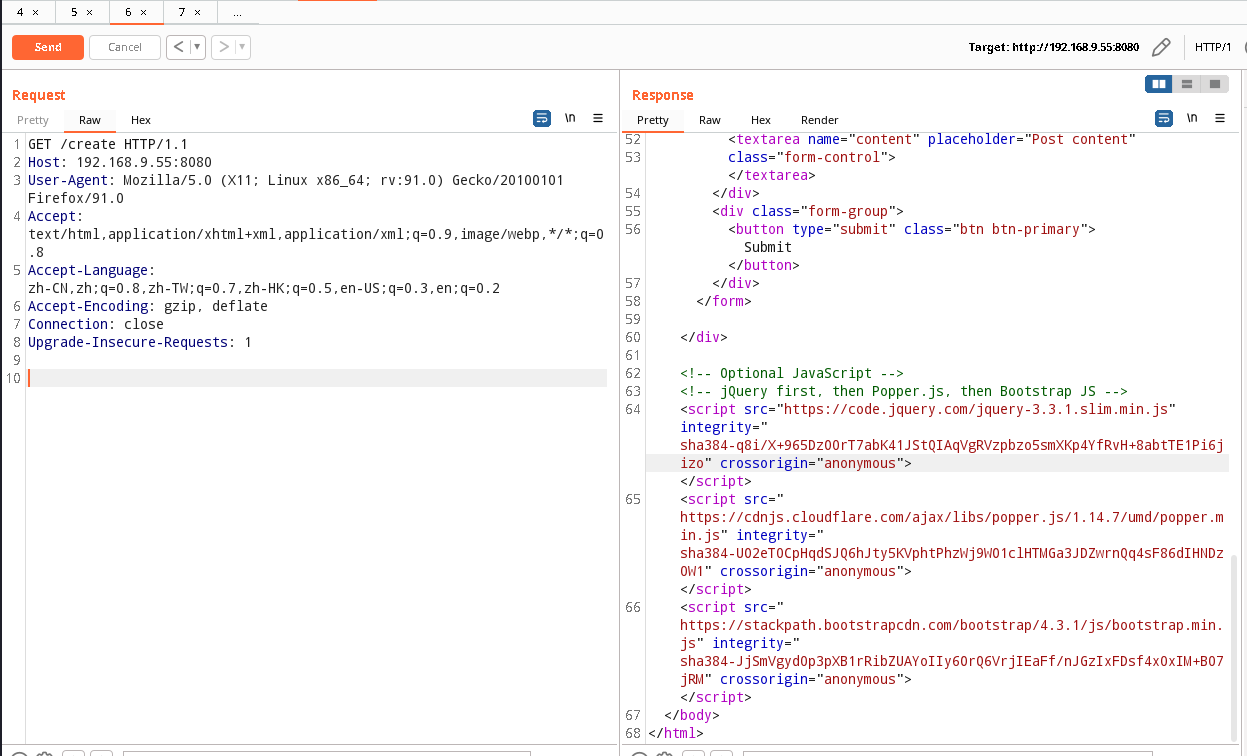
浏览器(或代理)发送了此服务器无法理解的请求。
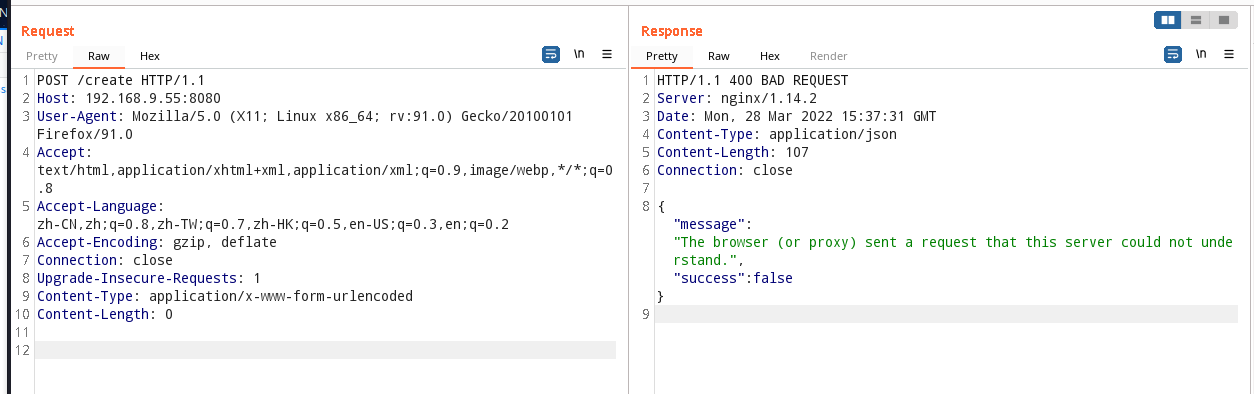
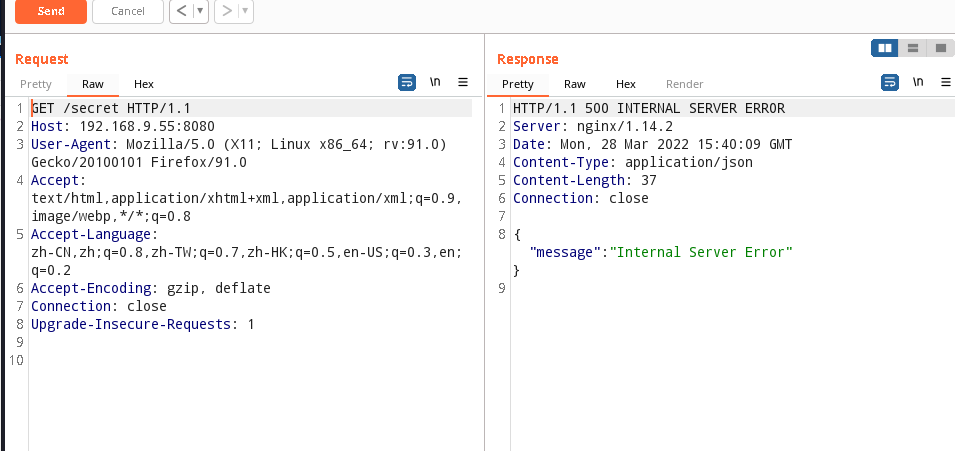
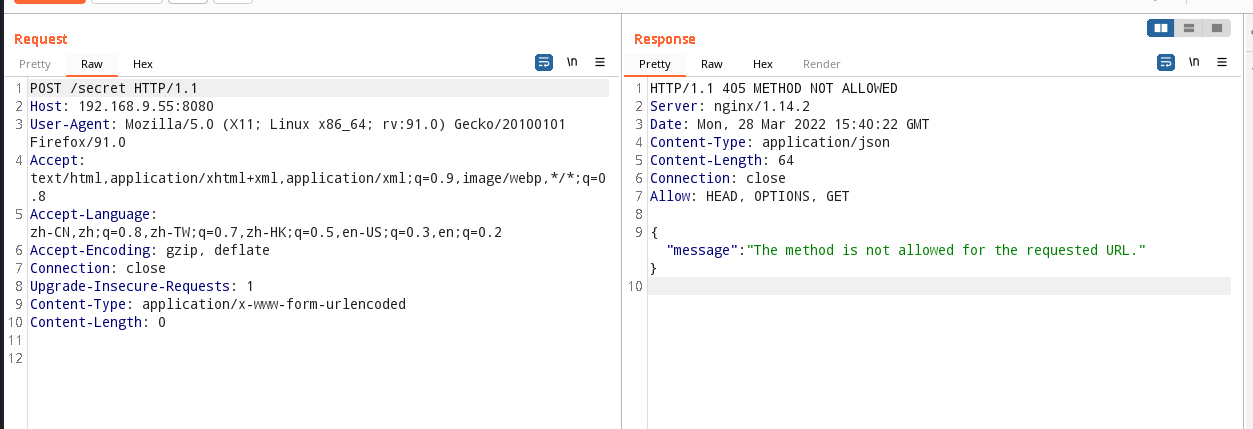
/secret 页面
/test页面
线索到这里就断了,感觉像是少了什么页面,换个工具扫一下目录:
gobuster dir -u http://192.168.9.55:8080/ -x html,zip,bak,txt,php --wordlist=/usr/share/wordlists/dirb/common.txt
⬢ snakeoil gobuster dir -u http://192.168.9.55:8080/ -x html,zip,bak,txt,php --wordlist=/usr/share/wordlists/dirb/common.txt
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.9.55:8080/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Extensions: txt,php,html,zip,bak
[+] Timeout: 10s
===============================================================
2022/03/28 15:44:58 Starting gobuster in directory enumeration mode
===============================================================
/01 (Status: 200) [Size: 2193]
/02 (Status: 200) [Size: 2356]
/04 (Status: 200) [Size: 2324]
/1 (Status: 200) [Size: 2193]
/2 (Status: 200) [Size: 2356]
/4 (Status: 200) [Size: 2324]
/create (Status: 200) [Size: 2596]
/login (Status: 405) [Size: 64]
/registration (Status: 200) [Size: 29]
/run (Status: 405) [Size: 178]
/secret (Status: 500) [Size: 37]
/test (Status: 200) [Size: 17]
/users (Status: 200) [Size: 265]
===============================================================
2022/03/28 15:45:17 Finished
===============================================================
⬢ snakeoil
发现新页面/run
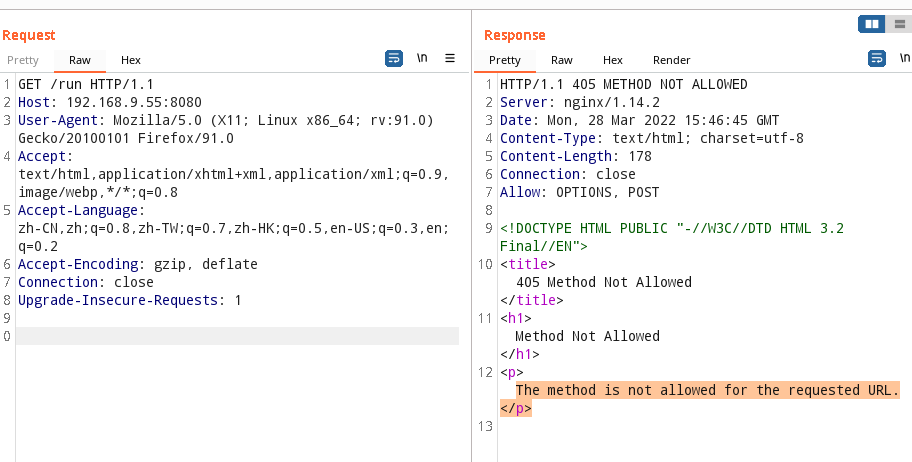
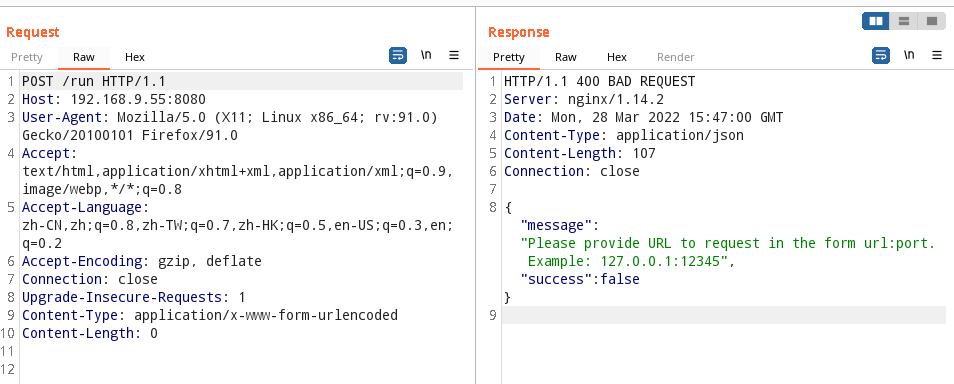
请以 url:port 格式提供请求的 URL。 示例:127.0.0.1:12345
修改请求包如下
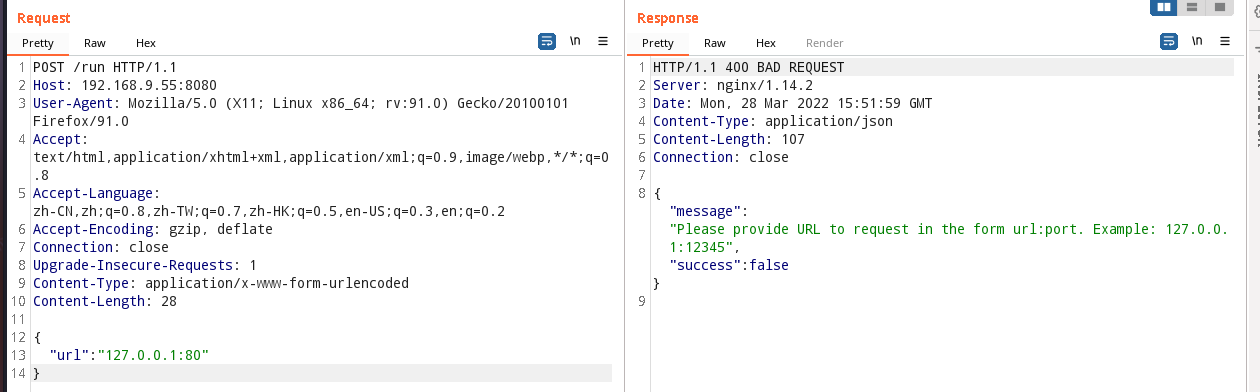
发包没反应,后百度一下发现需要更改 Content-Type
四种常见的 POST 提交数据方式
application/x-www-form-urlencoded
这应该是最常见的 POST 提交数据的方式了。浏览器的原生


 浙公网安备 33010602011771号
浙公网安备 33010602011771号