360CTF Re wp
这比赛唯一的一道Re😊
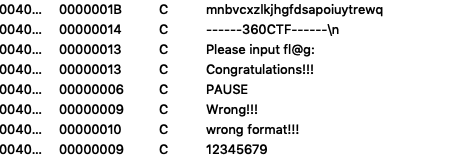
exe,看字符串
找到主函数
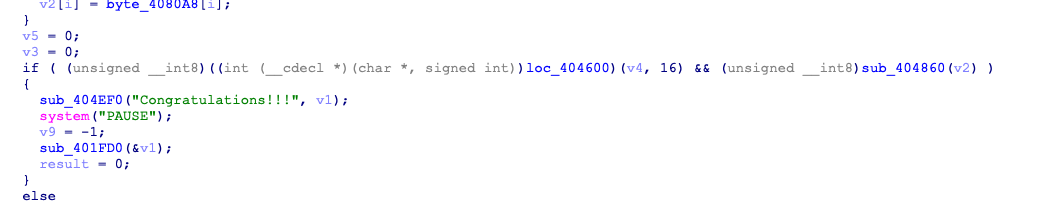
看到判断的地方为loc_404600,去看一下
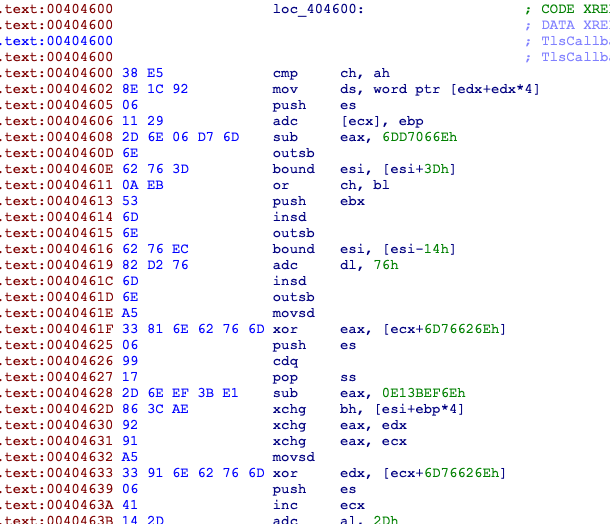
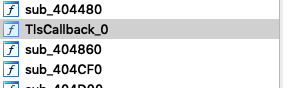
像是SMC,找修改404600处的函数
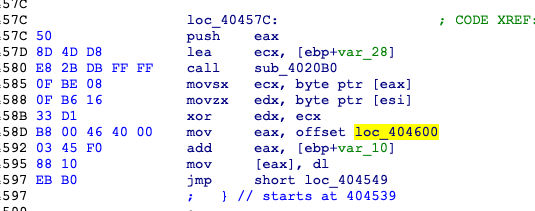
此处用到了loc_404600,找到这个函数为
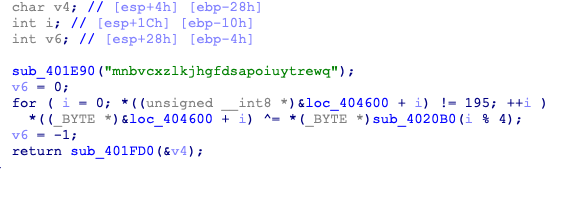
这里将loc_404600与mnbv循环的异或
写个脚本处理下
#include <idc.idc>
static decrypt(from, size) {
auto i, x,key1,key2,key3,key4;
key1 = 0x6D;
key2 = 0x6E;
key3 = 0x62;
key4 = 0x76;
for ( i=0; i != size; i=i+1 ) {
if(i%4==0){
x = Byte(from);
x = (x^key1);
PatchByte(from,x);
}
if(i%4==1){
x = Byte(from);
x = (x^key2);
PatchByte(from,x);
}
if(i%4==2){
x = Byte(from);
x = (x^key3);
PatchByte(from,x);
}
if(i%4==3){
x = Byte(from);
x = (x^key4);
PatchByte(from,x);
}
from = from + 1;
}
Message("\n" + "Decrypt Complete\n");
}
decrypt(0x00404600,0x260);
修改后重新分析创建函数得到
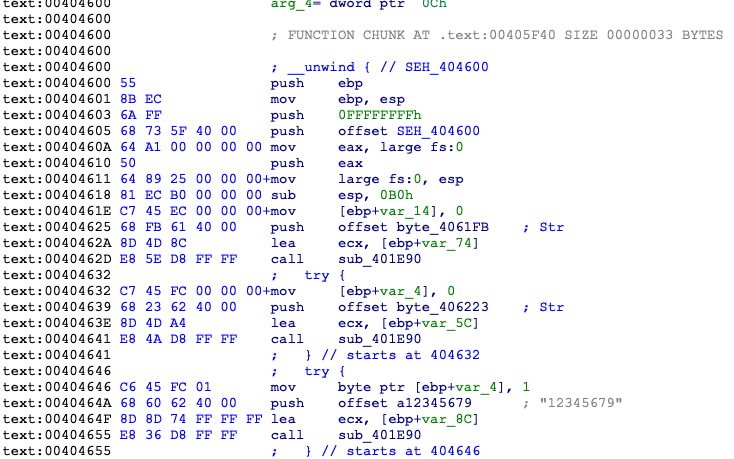
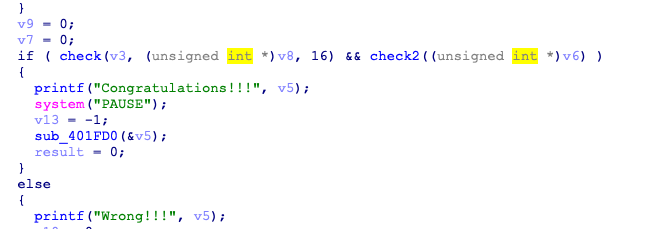
看check
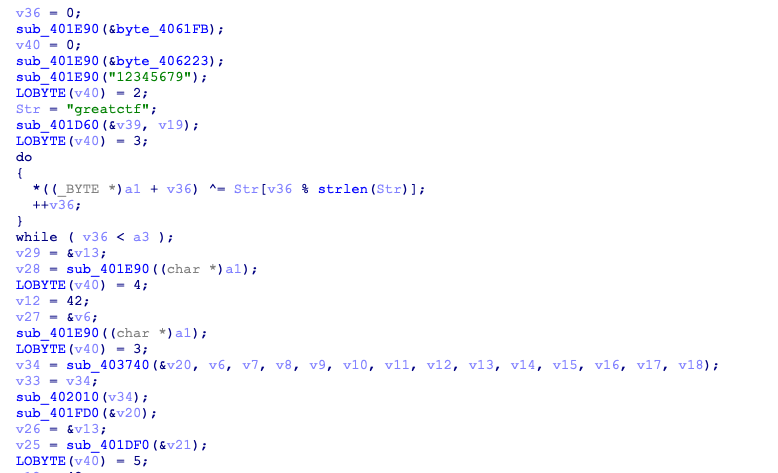
对输入的前16位进行转换使之等于“66733~6775”
光看ida分析这段实在是太难了,结合ollydbg分析,逻辑是将前十六个输入循环的与greatctf异或后平方再乘12345679
flag=''
a=667339003789000121539302795007135856775//12345679
b=pow(a,0.5)
c=str(b)
key='greatctf'
for i in range(16):
flag+=chr(ord(c[i])^ord(key[i%8]))
print(flag)
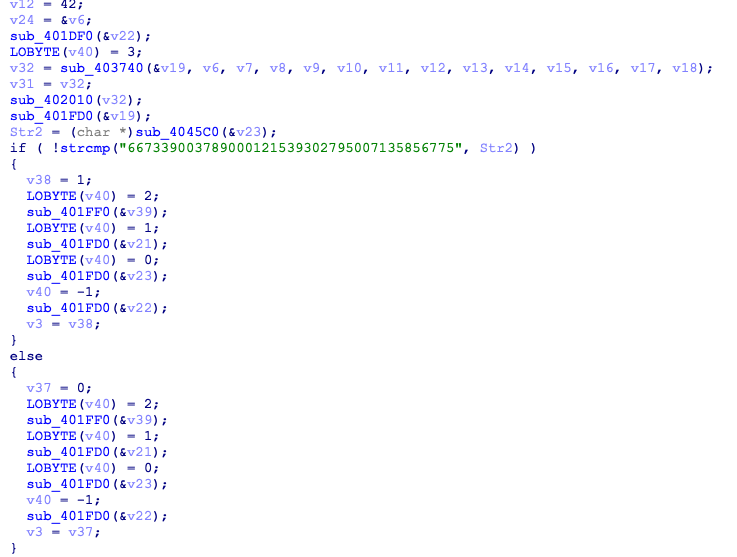
再看check2
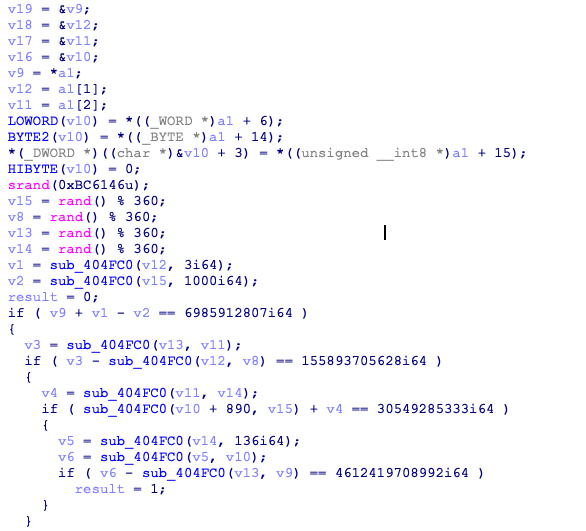
先搞随机数,在解四元一次方程
#include<stdlib.h>
#include<stdio.h>
int main(){
int v15,v8,v14,v13;
srand(0xbc6146);
v15 = rand() % 360;
v8 = rand() % 360;
v13 = rand() % 360;
v14 = rand() % 360;
printf("v5=%x,v8=%x,V13=%x,v14=%x\n",v15,v8,v13,v14);
return 0;
}
在这我出了个小错误,我最开始是在Linux里跑的,结果随机数与程序里不一样(🍑
from z3 import*
def hex_str(x):
temp=''
for i in range(len(x)//2):
temp+=chr(int(x[2*i:2*i+2],16))
return temp
f=Solver()
x=[Int('x%d'%i) for i in range(4)]
f.add(x[0]+3*x[3]-1000*2 == 0x1A06491E7)
f.add(x[2]*0xc0-x[3]*0xb == 0x244BFD2B9C)
f.add(2*(x[1]+0x37a)+x[2]*0x1f == 0x71CE119D5)
f.add(x[1]*0x1f*136-0xc0*x[0] == 0x431E9A36840)
if f.check() == sat:
for i in range(4):
print(hex_str(hex(f.model()[x[i]].as_long())[2:])[::-1])
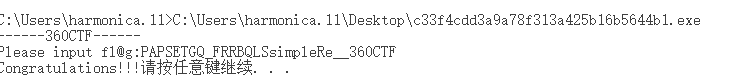
输出
simp
0CTF
__36
leRe
顺序修改一下就可以了


 浙公网安备 33010602011771号
浙公网安备 33010602011771号