BUUCTF CRYPTO部分题目wp
对密码学了解不多,做一下熟悉熟悉
1,看我回旋踢
给的密文synt{5pq1004q-86n5-46q8-o720-oro5on0417r1}
简单的凯撒密码,用http://www.zjslove.com/3.decode/kaisa/index.html
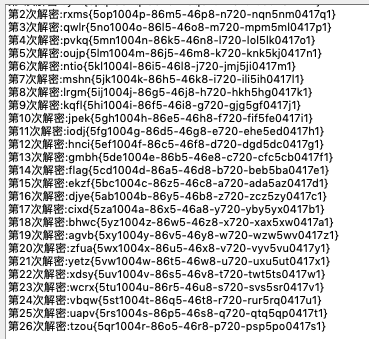
得到flag
2,md5
密文:e00cf25ad42683b3df678c61f42c6bda
md5解密:https://www.cmd5.com
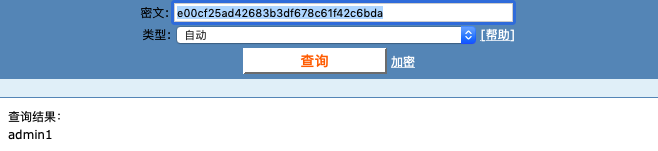
得到flag
3,url编码
密文:%66%6c%61%67%7b%61%6e%64%20%31%3d%31%7d
用http://tool.chinaz.com/tools/urlencode.aspx
得到flag
4,摩丝
密文:.. .-.. --- ...- . -.-- --- ..-
大写得到flag
5,变异凯撒
密文:afZ_r9VYfScOeO_UL^RWUc
格式:flag{}
根据格式,密文前五位ascii与格式相差为5,6,7,8,9,写脚本
m='afZ_r9VYfScOeO_UL^RWUc'
a=5
for i in range(0,len(m)):
print(chr(ord(m[i])+a),end='')
a+=1
6,Quoted-printable
密文:=E9=82=A3=E4=BD=A0=E4=B9=9F=E5=BE=88=E6=A3=92=E5=93=A6
用http://web.chacuo.net/charsetquotedprintable
解密得flag
7,password
打开文件
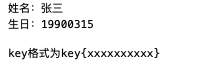
flag{zs19900315}
8,一眼就解密
密文:ZmxhZ3tUSEVfRkxBR19PRl9USElTX1NUUklOR30=
base64:http://tool.chinaz.com/Tools/Base64.aspx
解密得flag
9,丢失的MD5
送分题,给了一段python
import hashlib
for i in range(32,127):
for j in range(32,127):
for k in range(32,127):
m=hashlib.md5()
m.update('TASC'+chr(i)+'O3RJMV'+chr(j)+'WDJKX'+chr(k)+'ZM')
des=m.hexdigest()
if 'e9032' in des and 'da' in des and '911513' in des:
print des
跑一遍得flag,大概是展示md5爆破
10,rabbit
密文:U2FsdGVkX1/+ydnDPowGbjjJXhZxm2MP2AgI
rabbit密码:http://tool.chinaz.com/Tools/TextEncrypt.aspx
解密得flag
11,还原大师
md5爆破,写脚本
import hashlib
c='ABCDEFGHIJKLMNOPQRSTUVWXYZ'
a='e903???4dab????08?????51?80??8a?'
flag=0
def f(mds):
for i in range(0,len(a)):
if a[i]=='?':
continue
elif a[i]!=mds[i]:
return 0
return 1
for i in range(0,len(c)):
if flag==1:
break
for j in range(0,len(c)):
for k in range(0,len(c)):
b='TASC'+c[i]+'O3RJMV'+c[j]+'WDJKX'+c[k]+'ZM'
md=hashlib.md5(b.encode('utf8'))
mds=md.hexdigest()
flag=f(mds)
if flag==1:
print(mds)
得到flag
12,权限获得第一步
给的文件:Administrator:500:806EDC27AA52E314AAD3B435B51404EE:F4AD50F57683D4260DFD48AA351A17A8:::
这好像是Linux的shadow文件,密码是F4AD50F57683D4260DFD48AA351A17A8
得到flag
13,异性相吸
异或,给了两个文件,写脚本
with open('密文.txt' )as a:
a=a.read()
with open('key.txt' )as b:
b=b.read()
d=''
for i in range(0,len(b)):
c=chr(ord(a[i])^ord(b[i]))
d+=c
print(d)
得到flag
14,window系统密码
给文件:
Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
ctf:1002:06af9108f2e1fecf144e2e8adef09efd:a7fcb22a88038f35a8f39d503e7f0062:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
SUPPORT_388945a0:1001:aad3b435b51404eeaad3b435b51404ee:bef14eee40dffbc345eeb3f58e290d56:::
和上面权限那题一样,密码:a7fcb22a88038f35a8f39d503e7f0062
解密得flag


 浙公网安备 33010602011771号
浙公网安备 33010602011771号