springboot-权限控制shiro
1. 场景描述
(1)权限控制是IT项目特别是企业项目,绕不开的重要模块,接下来结合springboot介绍下权限控制框架shiro。
(2)springboot集成shiro的东西有点多,一篇博客完全介绍清楚有点费劲,拟分成3篇吧,第一篇介绍概念、原理;第二篇介绍搭建代码,详细介绍shiro框架;第三篇结合mybatis,搭建可运行项目。
2. 解决方案
2.1 简介
目前的权限控制,很多公司或者企业采用的都是基于角色进行访问控制的。
百度百科介绍,RBAC(英文缩写)

2.2 角色控制原理
通过数据库表结构进行介绍
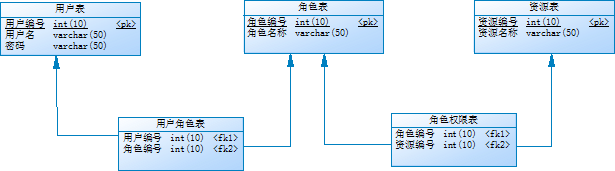
说明:
基于角色的权限控制,基本都是基于这五张表来的。
这五张表分别是:
(1)用户表,存储用户信息。
(2)角色表,存储角色信息,这里的角色类似于我们生活中的角色,企业中角色一般是:财务录单员、财务审核人、财务经理、采购员、采购经理等等。
(3)资源表,一般是系统菜单或者其他资源。
(4)用户角色表,多对多关系。
(5)角色资源表,多对多关系。
流程:
(1)用户登录,校验用户名与密码是否正确;
(2)通过用户名获取用户对应的角色;
(3)通过角色获取对应的资源,返回给前端。
2.3 常用框架
基于上面的权限控制原理,项目组可以通过代码来实现权限控制,也可以通过框架来实现,以前常用的或者好多企业在用的是spring security权限控制框架,一般会基于spring security做一套统一登录系统(单点登录),由一个系统统一控制企业用户权限,其他系统通过接口方式获取用户权限信息。
以前项目中也一直使用spring security,但是security的过滤链还是小多的,配置起来还是稍微有点麻烦,后来听别人说起shiro,看了下官网,又查了相关资料,shiro也是apache下的子项目,使用者也蛮多的,好评不少,发现比securiy简洁很多,效果也差不多,后续的项目就改用shiro了。
2.4 shiro介绍
2.4.1 官网
2.4.2 使用方式
通过maven的gav获取jar使用(目前官网最新版本1.4.1)
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-spring</artifactId>
<version>1.4.0</version>
</dependency>
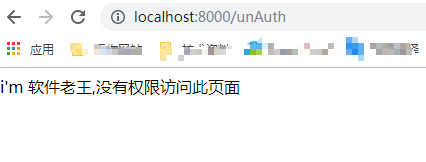
2.4.3 shiro介绍
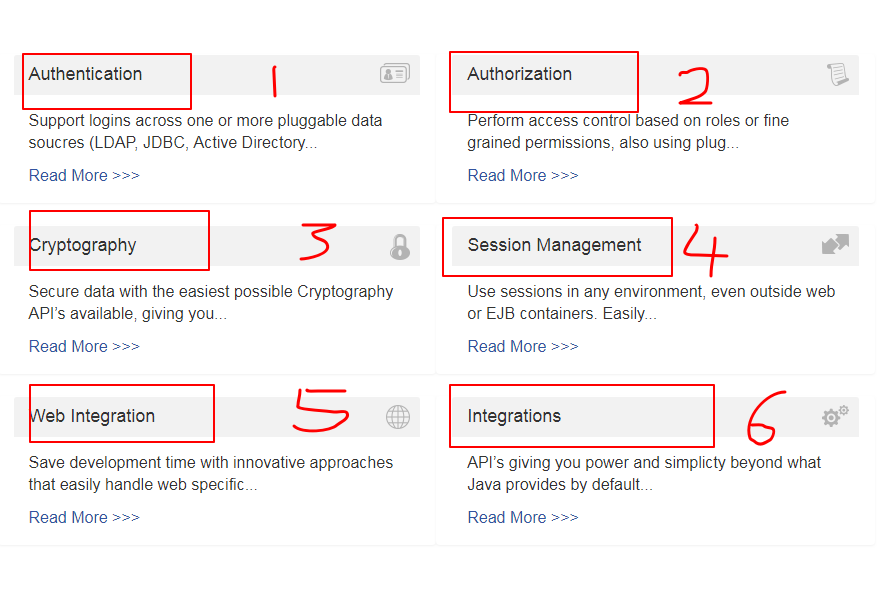
shiro主要包含六大模块
(1)认证;(2)授权;(3)密码;(4)回话管理;(5)web集成;(6)集成模块
说明:
常用的把(1)和(2)用好就可以了,3-6可以暂时不用管。
其中(1)是登录校验,就是校验用户名和密码是否正确用的模块;(2)是权限控制模块,校验登录用户是否有资源权限。
好了,先到这里,下节开始全程撸码与详细shiro权限控制框架介绍。
1. 场景描述
(1)最近有点小忙,公司真实项目内容有点小多以及不想只介绍理论,就使用springboot单独部署了个shiro的demo项目,还是理论和实际项结合比较好理解,介绍起来和修改也方便。
(2)接下来介绍springboot集成shrio,springboot-权限控制shiro(二),本节先不连数据库,先介绍springboot下shiro框架如何使用。(springboot-权限控制shiro(一))
2. 解决方案
2.1 整体介绍
2.1.1 项目图
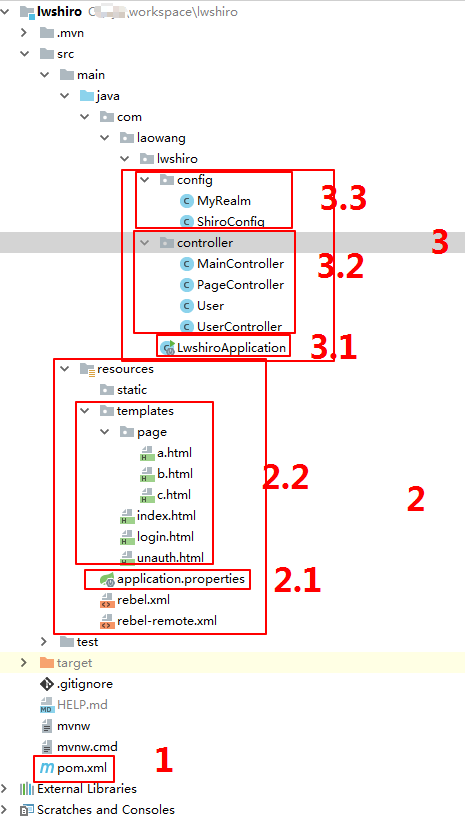
2.1.2 整体说明
shiro的demo项目主要包含三块内容:
(1)1是pom文件,获取相关jar包;
(2)2是资源(resources),一个配置文件以及6个演示页面;
(3)3是主类,包含启动类、控制类、shiro配置类。
2.1.3 shiro 过滤器说明
(1)认证过滤器
anon:用户不需要认证也可以访问
authc: 用户必须认证才可以访问
user:用户只要rememberMe,就可以访问
(2)授权过滤器
perms: 基于资源的授权过滤器
roles : 基于角色的授权过滤器
本节只使用了anon、authc认证过滤与perms资源授权过滤器,简单说shiro就是通过这些过滤器实现的权限控制。
2.2 pom文件
<?xml version="1.0" encoding="UTF-8"?>
<project xmlns="http://maven.apache.org/POM/4.0.0" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd">
<modelVersion>4.0.0</modelVersion>
<parent>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-parent</artifactId>
<version>2.1.6.RELEASE</version>
<relativePath/> <!-- lookup parent from repository -->
</parent>
<groupId>com.laowang</groupId>
<artifactId>lwshiro</artifactId>
<version>0.0.1-SNAPSHOT</version>
<name>lwshiro</name>
<description>Demo project for Spring Boot</description>
<properties>
<java.version>1.8</java.version>
</properties>
<dependencies>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-test</artifactId>
<scope>test</scope>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-thymeleaf</artifactId>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-spring</artifactId>
<version>1.4.0</version>
</dependency>
</dependencies>
<build>
<plugins>
<plugin>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-maven-plugin</artifactId>
</plugin>
</plugins>
</build>
</project>
说明:
重点是两个gav
1. spring-boot-starter-thymeleaf ---结合页面使用(2.2)
2. shiro-spring -----shiro核心包
2.3 resource(页面及配置类)
2.3.1 application.properties
server.port=8000
spring.thymeleaf.cache=false
说明:启动端口号改成了8000;cache=false是为了更改页面后不用重启服务,可忽略。
2.3.2 六个页面
(1)index.html
<!DOCTYPE html>
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
<title>软件老王主页</title>
</head>
<body>
<h3>软件老王主页</h3>
当前用户名:<span th:text="${session.userName}"></span>,<a href="/user/logout">注销</a>
<hr/>
<span>
<a href="/page/toa">页面1</a><br/>
</span>
<span >
<a href="/page/tob">页面2</a><br/>
</span>
<span >
<a href="/page/toc">页面3</a><br/>
</span>
</body>
</html>
(2)login.html
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
<title>登录页面</title>
</head>
<body>
<h3>登录</h3>
<font color="red" th:text="${msg}"></font>
<form method="post" action="/user/login">
用户名:<input type="text" name="name"/><br/>
密码:<input type="password" name="password"/><br/>
<input type="submit" value="登录">
</form>
</body>
</html>
(3)unauth.html
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
<title>未授权提示页面</title>
</head>
<body>
i'm 软件老王,没有权限访问此页面
</body>
</html>
(4)a.html、 b.html、 c.html
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
<title>i'm 软件老王,页面a</title>
</head>
<body>
i'm 软件老王,页面a
</body>
</html>
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
<title>i'm 软件老王,页面b</title>
</head>
<body>
i'm 软件老王,页面b
</body>
</html>
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
<title>i'm 软件老王,页面c</title>
</head>
<body>
i'm 软件老王,页面c
</body>
</html>
说明: 几个页面就不多说,仅仅为了说明问题新建的,有个标签可以关注下 th,这个是thymeleaf里面的,结合页面使用。
2.4 java类
2.4.1 启动类(LwshiroApplication)
package com.laowang.lwshiro;
import org.springframework.boot.SpringApplication;
import org.springframework.boot.autoconfigure.SpringBootApplication;
@SpringBootApplication
public class LwshiroApplication {
public static void main(String[] args) {
SpringApplication.run(LwshiroApplication.class, args);
}
}
说明: springboot项目启动类。
2.4.2 用户登录类(UserController)
package com.laowang.lwshiro.controller;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authc.IncorrectCredentialsException;
import org.apache.shiro.authc.UnknownAccountException;
import org.apache.shiro.authc.UsernamePasswordToken;
import org.apache.shiro.subject.Subject;
import org.springframework.stereotype.Controller;
import org.springframework.ui.Model;
import org.springframework.web.bind.annotation.RequestMapping;
import javax.servlet.http.HttpServletRequest;
/**
* 用户登录类
* @auther: 软件老王
* @date: 2019/7/30
*/
@Controller
@RequestMapping("/user")
public class UserController {
@RequestMapping("/login")
public String login(User user, HttpServletRequest request,
Model model) {
Subject subject = SecurityUtils.getSubject();
AuthenticationToken token = new UsernamePasswordToken(user.getName(),
user.getPassword());
try {
subject.login(token);
User tuser = (User)subject.getPrincipal();
request.getSession().setAttribute("userName",tuser.getName());
return "redirect:/index";
} catch (UnknownAccountException e) {
model.addAttribute("msg", "i'm 软件老王,用户名不存在");
return "login";
} catch (IncorrectCredentialsException e) {
model.addAttribute("msg", "i'm 软件老王,密码错误");
return "login";
}
}
/**
* i'm 软件老王,注销方法
*/
@RequestMapping("/logout")
public String logout(){
Subject subject = SecurityUtils.getSubject();
subject.logout(); //shiro底层删除session的会话信息
return "redirect:/toLogin";
}
}
说明:
重点就以下3行代码
Subject subject = SecurityUtils.getSubject(); -----------#1
AuthenticationToken token = new UsernamePasswordToken(user.getName(),
user.getPassword()); ---------#2
try {
subject.login(token); ----------#3
(1)第一行是从工厂中获取subject,登录用户操作类;
(2)将从页面获取的用户名和密码设置到一个token中;
(3)调用登录有用户操作类的login方法;
(4)会在MyRealm类的doGetAuthenticationInfo方法中获取到登录的token与数据库中(目前写的固定值)进行认证过滤比对。
2.4.3 接收参数类(User)
package com.laowang.lwshiro.controller;
import java.io.Serializable;
/**
* 接收参数类
* @auther: 软件老王
* @date: 2019/7/30
*/
public class User implements Serializable{
private Integer id;
private String name;
private String password;
public Integer getId() {
return id;
}
public void setId(Integer id) {
this.id = id;
}
public String getName() {
return name;
}
public void setName(String name) {
this.name = name;
}
public String getPassword() {
return password;
}
public void setPassword(String password) {
this.password = password;
}
@Override
public String toString() {
return "User [id=" + id + ", name=" + name + ", password=" + password + "]";
}
}
说明: 接收参数类
2.4.4 页面跳转(PageController)
package com.laowang.lwshiro.controller;
import org.springframework.stereotype.Controller;
import org.springframework.web.bind.annotation.RequestMapping;
/**
* 页面跳转
* @auther: 软件老王
* @date: 2019/7/30
*/
@Controller
@RequestMapping("/page")
public class PageController {
/**
* i'm 软件老王
*/
@RequestMapping("/toa")
public String toAdd(){
return "page/a";
}
/**
* i'm 软件老王
*/
@RequestMapping("/tob")
public String toList(){
return "page/b";
}
/**
* i'm 软件老王
*/
@RequestMapping("/toc")
public String toUpdate(){
return "page/c";
}
}
说明: 控制跳转类,没啥值的说的。
2.4.5 主控制类(MainController)
package com.laowang.lwshiro.controller;
import org.springframework.stereotype.Controller;
import org.springframework.web.bind.annotation.RequestMapping;
/**
* 主控制类
* @auther: 软件老王
* @date: 2019/7/30
*/
@Controller
@RequestMapping("/")
public class MainController {
/**
* i'm 软件老王
*/
@RequestMapping("/index")
public String index(){
return "index";
}
/**
* i'm 软件老王
*/
@RequestMapping("/toLogin")
public String toLogin(){
return "login";
}
/**
* i'm 软件老王
*/
@RequestMapping("/unAuth")
public String unAuth(){
return "unauth";
}
}
**说明: **主控制类,也没啥值的说的。
2.4.6 shiro主配置类(ShiroConfig)
package com.laowang.lwshiro.config;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.LinkedHashMap;
import java.util.Map;
/**
* shiro主配置类
* @auther: 软件老王
* @date: 2019/7/30
*/
@Configuration
public class ShiroConfig {
/**
* i'm 软件老王
*/
@Bean
public ShiroFilterFactoryBean getShiroFilterFactoryBean(DefaultWebSecurityManager securityManager) {
ShiroFilterFactoryBean shiroFilterFactoryBean = new ShiroFilterFactoryBean();
shiroFilterFactoryBean.setSecurityManager(securityManager);
Map<String, String> filterMap = new LinkedHashMap<>();
//登录
filterMap.put("/page/toa", "anon");
filterMap.put("/user/login", "anon");
//授权过滤器
// filterMap.put("/page/toa", "perms[toa]");
filterMap.put("/page/tob", "perms[tob]");
filterMap.put("/page/toc", "perms[toc]");
filterMap.put("/**", "authc");
shiroFilterFactoryBean.setFilterChainDefinitionMap(filterMap);
shiroFilterFactoryBean.setLoginUrl("/toLogin");
shiroFilterFactoryBean.setUnauthorizedUrl("/unAuth");
return shiroFilterFactoryBean;
}
/**
* i'm 软件老王
*/
@Bean
public DefaultWebSecurityManager getSecurityManager(MyRealm myRealm) {
DefaultWebSecurityManager defaultWebSecurityManager = new DefaultWebSecurityManager();
defaultWebSecurityManager.setRealm(myRealm);
return defaultWebSecurityManager;
}
/**
* i'm 软件老王
*/
@Bean
public MyRealm getMyReal() {
MyRealm myReal = new MyRealm();
return myReal;
}
}
说明:
这个是shiro的主配置类,重点说一下,这个类中包含了三个bean,分别为:
(1)getShiroFilterFactoryBean这个bean是关键,用于设定过滤器,本节的授权写的固定的,下节将从数据库中获取,在这个bean中设置认证过滤、授权过滤、登录页及无权限页,非常重要。
(2)getSecurityManager这个类是跟前面的 Subject subject = SecurityUtils.getSubject()有关系的,通过这里配置MyRealm,将登录控制与shiro关联起来;
(3)getMyReal 这个bean是为了注入MyRealm类;
2.4.7 shiro配置类(MyRealm)
package com.laowang.lwshiro.config;
import com.laowang.lwshiro.controller.User;
import org.apache.shiro.authc.*;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.authz.SimpleAuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
/**
* shiro配置类
* @auther: 软件老王
* @date: 2019/7/30
*/
public class MyRealm extends AuthorizingRealm {
/**
* i'm 软件老王
*/
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
info.addStringPermission("toa");
info.addStringPermission("toc");
return info;
}
/**
* i'm 软件老王
*/
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authenticationToken) throws AuthenticationException {
UsernamePasswordToken token = (UsernamePasswordToken)authenticationToken;
String name ="laowang";
String password="123";
if (!token.getUsername().equalsIgnoreCase(name)) {
return null;
}
User tuser = new User();
tuser.setName(name);
tuser.setPassword(password);
return new SimpleAuthenticationInfo(tuser,tuser.getPassword(),"");
}
}
说明
这个类是项目的具体配置类,每个项目都可能会不一样。
(1) doGetAuthorizationInfo这个是授权方法,结合登录用户使用,从数据库中查询出登录人具有的权限信息,有权限的话,放行;没有权限的转到unauth页面;
(2)doGetAuthenticationInfo这个是认证方法,在登录控制处调用subject.login方法后,就会跳转到这里进行认证操作,用户名直接跟从数据库中查询比对,密码赋值到SimpleAuthenticationInfo类在shiro中进行比对,根据返回情况在登录控制处进行提示。
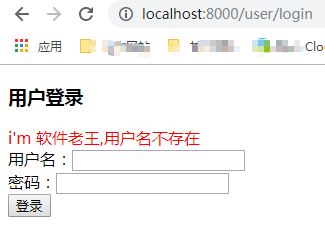
2.5 效果
2.5.1 登录页

2.5.2 首页
登录账户:laowang,密码:123
(1)登录成功

(2)登录失败
2.5.3 访问页面
在myrealm中设置了所有用户对a页面和c页面有操作权限,对b页面没有,这一块本节写的固定的,下一节会从数据库中根据用户名查询登录人拥有的权限。
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
info.addStringPermission("toa");
info.addStringPermission("toc");
return info;
}
(1)访问页面a
(2)访问页面b
Spring Boot 极简集成 Shiro
1. 前言
Apache Shiro是一个功能强大且易于使用的Java安全框架,提供了认证,授权,加密,和会话管理。
Shiro有三大核心组件:
Subject:即当前用户,在权限管理的应用程序里往往需要知道谁能够操作什么,谁拥有操作该程序的权利,shiro中则需要通过Subject来提供基础的当前用户信息,Subject 不仅仅代表某个用户,与当前应用交互的任何东西都是Subject,如网络爬虫等。所有的Subject都要绑定到SecurityManager上,与Subject的交互实际上是被转换为与SecurityManager的交互。
SecurityManager:即所有Subject的管理者,这是Shiro框架的核心组件,可以把他看做是一个Shiro框架的全局管理组件,用于调度各种Shiro框架的服务。作用类似于SpringMVC中的DispatcherServlet,用于拦截所有请求并进行处理。
Realm:Realm是用户的信息认证器和用户的权限人证器,我们需要自己来实现Realm来自定义的管理我们自己系统内部的权限规则。SecurityManager要验证用户,需要从Realm中获取用户。可以把Realm看做是数据源。
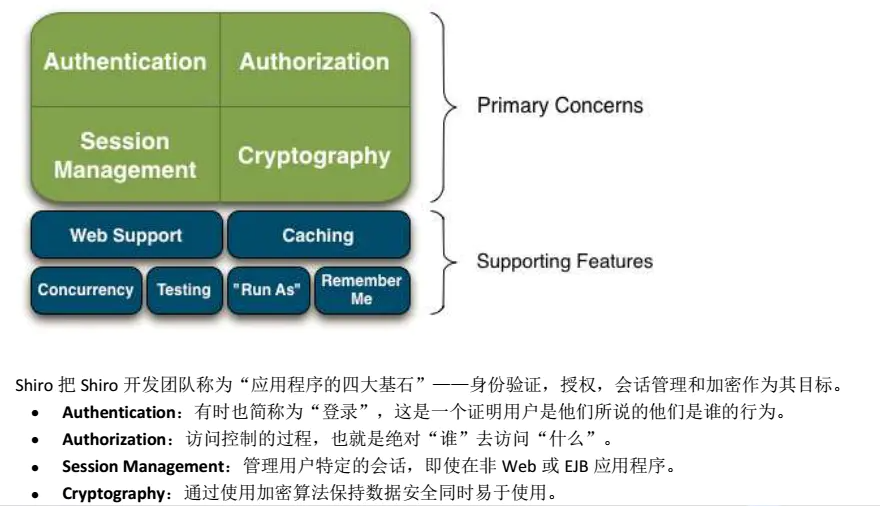
2. 数据库设计
2.1 User(用户)
SET NAMES utf8mb4; SET FOREIGN_KEY_CHECKS = 0; -- ---------------------------- -- Table structure for user -- ---------------------------- DROP TABLE IF EXISTS `user`; CREATE TABLE `user` ( `id` bigint(20) NOT NULL AUTO_INCREMENT, `password` varchar(255) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL, `username` varchar(255) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL, `account` varchar(255) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL, PRIMARY KEY (`id`) USING BTREE ) ENGINE = MyISAM AUTO_INCREMENT = 4 CHARACTER SET = utf8 COLLATE = utf8_general_ci ROW_FORMAT = Dynamic; -- ---------------------------- -- Records of user -- ---------------------------- INSERT INTO `user` VALUES (1, 'root', '超级用户', 'root'); INSERT INTO `user` VALUES (2, 'user', '普通用户', 'user'); INSERT INTO `user` VALUES (3, 'vip', 'VIP用户', 'vip'); SET FOREIGN_KEY_CHECKS = 1;
2.2 Role(角色)

SET NAMES utf8mb4; SET FOREIGN_KEY_CHECKS = 0; -- ---------------------------- -- Table structure for role -- ---------------------------- DROP TABLE IF EXISTS `role`; CREATE TABLE `role` ( `id` int(11) NOT NULL AUTO_INCREMENT, `role` varchar(255) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL, `desc` varchar(255) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL, PRIMARY KEY (`id`) USING BTREE ) ENGINE = MyISAM AUTO_INCREMENT = 4 CHARACTER SET = utf8 COLLATE = utf8_general_ci ROW_FORMAT = Dynamic; -- ---------------------------- -- Records of role -- ---------------------------- INSERT INTO `role` VALUES (1, 'admin', '超级管理员'); INSERT INTO `role` VALUES (2, 'user', '普通用户'); INSERT INTO `role` VALUES (3, 'vip_user', 'VIP用户'); SET FOREIGN_KEY_CHECKS = 1;
2.3 Permission(权限)
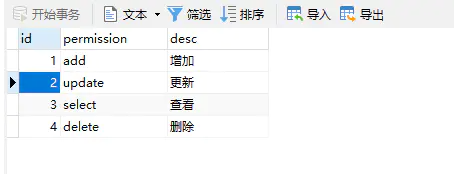
SET NAMES utf8mb4; SET FOREIGN_KEY_CHECKS = 0; -- ---------------------------- -- Table structure for permission -- ---------------------------- DROP TABLE IF EXISTS `permission`; CREATE TABLE `permission` ( `id` int(11) NOT NULL AUTO_INCREMENT, `permission` varchar(255) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '权限名称', `desc` varchar(255) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '权限描述', PRIMARY KEY (`id`) USING BTREE ) ENGINE = MyISAM AUTO_INCREMENT = 5 CHARACTER SET = utf8 COLLATE = utf8_general_ci ROW_FORMAT = Dynamic; -- ---------------------------- -- Records of permission -- ---------------------------- INSERT INTO `permission` VALUES (1, 'add', '增加'); INSERT INTO `permission` VALUES (2, 'update', '更新'); INSERT INTO `permission` VALUES (3, 'select', '查看'); INSERT INTO `permission` VALUES (4, 'delete', '删除'); SET FOREIGN_KEY_CHECKS = 1;
2.4 User_Role(用户-角色)
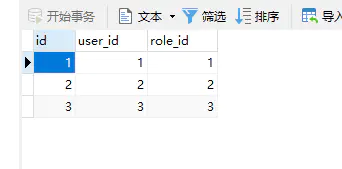
SET NAMES utf8mb4; SET FOREIGN_KEY_CHECKS = 0; -- ---------------------------- -- Table structure for user_role -- ---------------------------- DROP TABLE IF EXISTS `user_role`; CREATE TABLE `user_role` ( `id` int(11) NOT NULL AUTO_INCREMENT, `user_id` int(11) NULL DEFAULT NULL, `role_id` int(11) NULL DEFAULT NULL, PRIMARY KEY (`id`) USING BTREE ) ENGINE = MyISAM AUTO_INCREMENT = 4 CHARACTER SET = utf8 COLLATE = utf8_general_ci ROW_FORMAT = Fixed; -- ---------------------------- -- Records of user_role -- ---------------------------- INSERT INTO `user_role` VALUES (1, 1, 1); INSERT INTO `user_role` VALUES (2, 2, 2); INSERT INTO `user_role` VALUES (3, 3, 3); SET FOREIGN_KEY_CHECKS = 1;
2.5 Role_Permission(角色-权限)
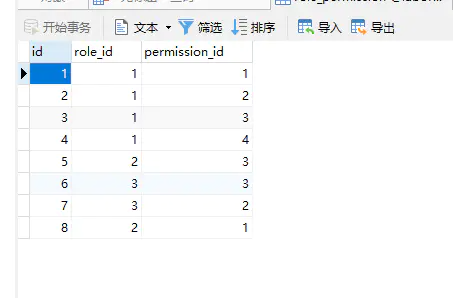
SET NAMES utf8mb4; SET FOREIGN_KEY_CHECKS = 0; -- ---------------------------- -- Table structure for role_permission -- ---------------------------- DROP TABLE IF EXISTS `role_permission`; CREATE TABLE `role_permission` ( `id` int(11) NOT NULL AUTO_INCREMENT, `role_id` int(11) NULL DEFAULT NULL, `permission_id` int(255) NULL DEFAULT NULL, PRIMARY KEY (`id`) USING BTREE ) ENGINE = MyISAM AUTO_INCREMENT = 9 CHARACTER SET = utf8 COLLATE = utf8_general_ci ROW_FORMAT = Fixed; -- ---------------------------- -- Records of role_permission -- ---------------------------- INSERT INTO `role_permission` VALUES (1, 1, 1); INSERT INTO `role_permission` VALUES (2, 1, 2); INSERT INTO `role_permission` VALUES (3, 1, 3); INSERT INTO `role_permission` VALUES (4, 1, 4); INSERT INTO `role_permission` VALUES (5, 2, 3); INSERT INTO `role_permission` VALUES (6, 3, 3); INSERT INTO `role_permission` VALUES (7, 3, 2); INSERT INTO `role_permission` VALUES (8, 2, 1); SET FOREIGN_KEY_CHECKS = 1;
3. 项目结构
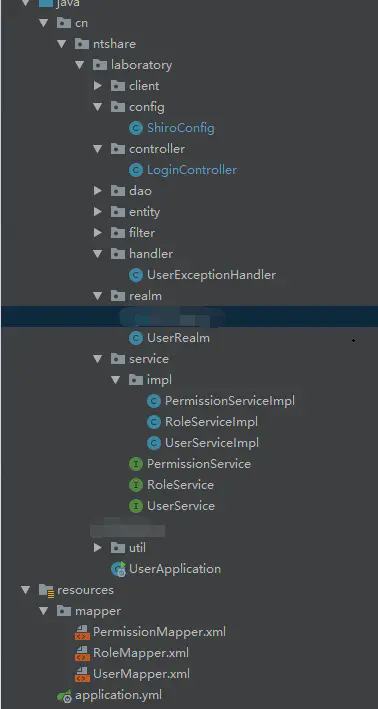
4. 前期准备
4.1 导入Pom
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
</dependency>
<dependency>
<groupId>org.mybatis.spring.boot</groupId>
<artifactId>mybatis-spring-boot-starter</artifactId>
<version>1.3.2</version>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-spring</artifactId>
<version>1.4.0</version>
</dependency>
4.2 application.yml
server:
port: 8903
spring:
application:
name: lab-user
datasource:
driver-class-name: com.mysql.jdbc.Driver
url: jdbc:mysql://127.0.0.1:3306/laboratory?charset=utf8
username: root
password: root
mybatis:
type-aliases-package: cn.ntshare.laboratory.entity
mapper-locations: classpath:mapper/*.xml
configuration:
map-underscore-to-camel-case: true
4.3 实体类
4.3.1 User.java
@Data
@ToString
public class User implements Serializable {
private static final long serialVersionUID = -6056125703075132981L;
private Integer id;
private String account;
private String password;
private String username;
}
4.3.2 Role.java
@Data
@ToString
public class Role implements Serializable {
private static final long serialVersionUID = -1767327914553823741L;
private Integer id;
private String role;
private String desc;
}
4.4 Dao层
4.4.1 PermissionMapper.java
@Mapper
@Repository
public interface PermissionMapper {
List<String> findByRoleId(@Param("roleIds") List<Integer> roleIds);
}
4.4.2 PermissionMapper.xml
<mapper namespace="cn.ntshare.laboratory.dao.PermissionMapper">
<sql id="base_column_list">
id, permission, desc
</sql>
<select id="findByRoleId" parameterType="List" resultType="String">
select permission
from permission, role_permission rp
where rp.permission_id = permission.id and rp.role_id in
<foreach collection="roleIds" item="id" open="(" close=")" separator=",">
#{id}
</foreach>
</select>
</mapper>
4.4.3 RoleMapper.java
@Mapper
@Repository
public interface RoleMapper {
List<Role> findRoleByUserId(@Param("userId") Integer userId);
}
4.4.4 RoleMapper.xml
<mapper namespace="cn.ntshare.laboratory.dao.RoleMapper">
<sql id="base_column_list">
id, user_id, role_id
</sql>
<select id="findRoleByUserId" parameterType="Integer" resultType="Role">
select role.id, role
from role, user, user_role ur
where role.id = ur.role_id and ur.user_id = user.id and user.id = #{userId}
</select>
</mapper>
4.4.5 UserMapper.java
@Mapper
@Repository
public interface UserMapper {
User findByAccount(@Param("account") String account);
}
4.4.6 UserMapper.xml
<mapper namespace="cn.ntshare.laboratory.dao.UserMapper">
<sql id="base_column_list">
id, account, password, username
</sql>
<select id="findByAccount" parameterType="Map" resultType="User">
select
<include refid="base_column_list"/>
from user
where account = #{account}
</select>
</mapper>
4.5 Service层
4.5.1 PermissionServiceImpl.java
@Service
public class PermissionServiceImpl implements PermissionService {
@Autowired
private PermissionMapper permissionMapper;
@Override
public List<String> findByRoleId(List<Integer> roleIds) {
return permissionMapper.findByRoleId(roleIds);
}
}
4.5.2 RoleServiceImpl.java
@Service
public class RoleServiceImpl implements RoleService {
@Autowired
private RoleMapper roleMapper;
@Override
public List<Role> findRoleByUserId(Integer id) {
return roleMapper.findRoleByUserId(id);
}
}
4.5.3 UserServiceImpl.java
@Service
public class UserServiceImpl implements UserService {
@Autowired
private UserMapper userMapper;
@Override
public User findByAccount(String account) {
return userMapper.findByAccount(account);
}
}
4.6. 系统返回状态枚举与包装函数
4.6.1 ServerResponseEnum.java
@AllArgsConstructor
@Getter
public enum ServerResponseEnum {
SUCCESS(0, "成功"),
ERROR(10, "失败"),
ACCOUNT_NOT_EXIST(11, "账号不存在"),
DUPLICATE_ACCOUNT(12, "账号重复"),
ACCOUNT_IS_DISABLED(13, "账号被禁用"),
INCORRECT_CREDENTIALS(14, "账号或密码错误"),
NOT_LOGIN_IN(15, "账号未登录"),
UNAUTHORIZED(16, "没有权限")
;
Integer code;
String message;
}
4.6.2 ServerResponseVO.java
@Getter
@Setter
@NoArgsConstructor
public class ServerResponseVO<T> implements Serializable {
private static final long serialVersionUID = -1005863670741860901L;
// 响应码
private Integer code;
// 描述信息
private String message;
// 响应内容
private T data;
private ServerResponseVO(ServerResponseEnum responseCode) {
this.code = responseCode.getCode();
this.message = responseCode.getMessage();
}
private ServerResponseVO(ServerResponseEnum responseCode, T data) {
this.code = responseCode.getCode();
this.message = responseCode.getMessage();
this.data = data;
}
private ServerResponseVO(Integer code, String message) {
this.code = code;
this.message = message;
}
/**
* 返回成功信息
* @param data 信息内容
* @param <T>
* @return
*/
public static<T> ServerResponseVO success(T data) {
return new ServerResponseVO<>(ServerResponseEnum.SUCCESS, data);
}
/**
* 返回成功信息
* @return
*/
public static ServerResponseVO success() {
return new ServerResponseVO(ServerResponseEnum.SUCCESS);
}
/**
* 返回错误信息
* @param responseCode 响应码
* @return
*/
public static ServerResponseVO error(ServerResponseEnum responseCode) {
return new ServerResponseVO(responseCode);
}
}
4.7 统一异常处理
当用户身份认证失败时,会抛出UnauthorizedException,我们可以通过统一异常处理来处理该异常
@RestControllerAdvice
public class UserExceptionHandler {
@ExceptionHandler(UnauthorizedException.class)
@ResponseStatus(HttpStatus.UNAUTHORIZED)
public ServerResponseVO UnAuthorizedExceptionHandler(UnauthorizedException e) {
return ServerResponseVO.error(ServerResponseEnum.UNAUTHORIZED);
}
}
5. 集成Shiro
5.1 UserRealm.java
/**
* 负责认证用户身份和对用户进行授权
*/
public class UserRealm extends AuthorizingRealm {
@Autowired
private UserService userService;
@Autowired
private RoleService roleService;
@Autowired
private PermissionService permissionService;
// 用户授权
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
User user = (User) principalCollection.getPrimaryPrincipal();
SimpleAuthorizationInfo authorizationInfo = new SimpleAuthorizationInfo();
List<Role> roleList = roleService.findRoleByUserId(user.getId());
Set<String> roleSet = new HashSet<>();
List<Integer> roleIds = new ArrayList<>();
for (Role role : roleList) {
roleSet.add(role.getRole());
roleIds.add(role.getId());
}
// 放入角色信息
authorizationInfo.setRoles(roleSet);
// 放入权限信息
List<String> permissionList = permissionService.findByRoleId(roleIds);
authorizationInfo.setStringPermissions(new HashSet<>(permissionList));
return authorizationInfo;
}
// 用户认证
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authToken) throws AuthenticationException {
UsernamePasswordToken token = (UsernamePasswordToken) authToken;
User user = userService.findByAccount(token.getUsername());
if (user == null) {
return null;
}
return new SimpleAuthenticationInfo(user, user.getPassword(), getName());
}
}
5.2 ShiroConfig.java
@Configuration
public class ShiroConfig {
@Bean
public UserRealm userRealm() {
return new UserRealm();
}
@Bean
public DefaultWebSecurityManager securityManager() {
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
securityManager.setRealm(userRealm());
return securityManager;
}
/**
* 路径过滤规则
* @return
*/
@Bean
public ShiroFilterFactoryBean shiroFilter(DefaultWebSecurityManager securityManager) {
ShiroFilterFactoryBean shiroFilterFactoryBean = new ShiroFilterFactoryBean();
shiroFilterFactoryBean.setSecurityManager(securityManager);
shiroFilterFactoryBean.setLoginUrl("/login");
shiroFilterFactoryBean.setSuccessUrl("/");
Map<String, String> map = new LinkedHashMap<>();
// 有先后顺序
map.put("/login", "anon"); // 允许匿名访问
map.put("/**", "authc"); // 进行身份认证后才能访问
shiroFilterFactoryBean.setFilterChainDefinitionMap(map);
return shiroFilterFactoryBean;
}
/**
* 开启Shiro注解模式,可以在Controller中的方法上添加注解
* @param securityManager
* @return
*/
@Bean
public AuthorizationAttributeSourceAdvisor authorizationAttributeSourceAdvisor(@Qualifier("securityManager") DefaultSecurityManager securityManager) {
AuthorizationAttributeSourceAdvisor authorizationAttributeSourceAdvisor = new AuthorizationAttributeSourceAdvisor();
authorizationAttributeSourceAdvisor.setSecurityManager(securityManager);
return authorizationAttributeSourceAdvisor;
}
5.3 LoginController.java
@RestController
@RequestMapping("")
public class LoginController {
@PostMapping("/login")
public ServerResponseVO login(@RequestParam(value = "account") String account,
@RequestParam(value = "password") String password) {
Subject userSubject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken(account, password);
try {
// 登录验证
userSubject.login(token);
return ServerResponseVO.success();
} catch (UnknownAccountException e) {
return ServerResponseVO.error(ServerResponseEnum.ACCOUNT_NOT_EXIST);
} catch (DisabledAccountException e) {
return ServerResponseVO.error(ServerResponseEnum.ACCOUNT_IS_DISABLED);
} catch (IncorrectCredentialsException e) {
return ServerResponseVO.error(ServerResponseEnum.INCORRECT_CREDENTIALS);
} catch (Throwable e) {
e.printStackTrace();
return ServerResponseVO.error(ServerResponseEnum.ERROR);
}
}
@GetMapping("/login")
public ServerResponseVO login() {
return ServerResponseVO.error(ServerResponseEnum.NOT_LOGIN_IN);
}
@GetMapping("/auth")
public String auth() {
return "已成功登录";
}
@GetMapping("/role")
@RequiresRoles("vip")
public String role() {
return "测试Vip角色";
}
@GetMapping("/permission")
@RequiresPermissions(value = {"add", "update"}, logical = Logical.AND)
public String permission() {
return "测试Add和Update权限";
}
}
6. 测试
6.1 用root用户登录
6.1.1 登录
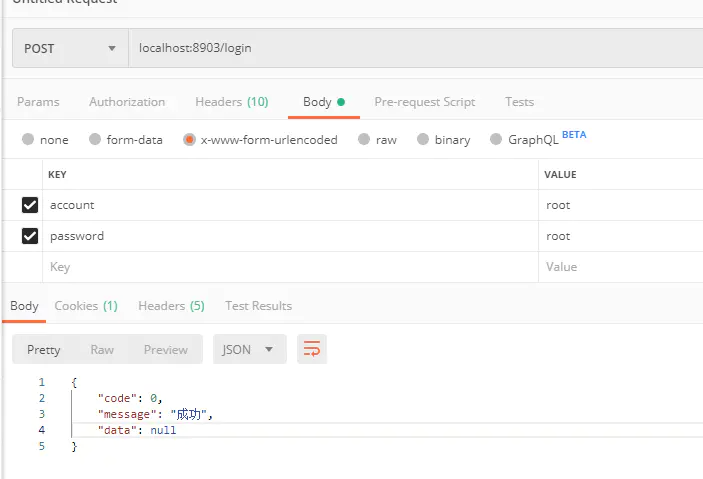
6.1.2 验证是否登录
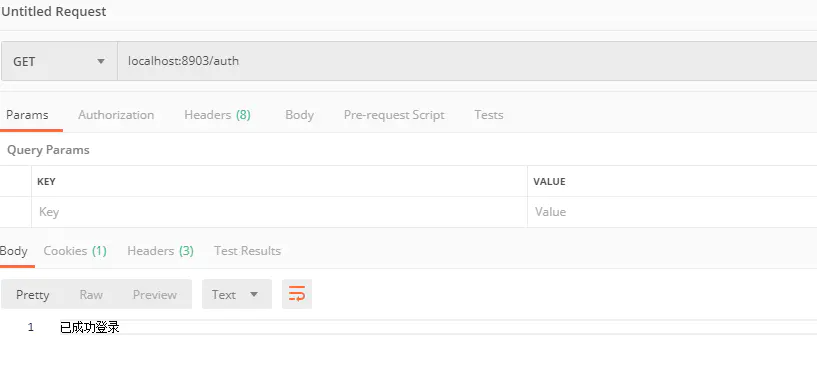 6.1.3 测试角色权限
6.1.3 测试角色权限 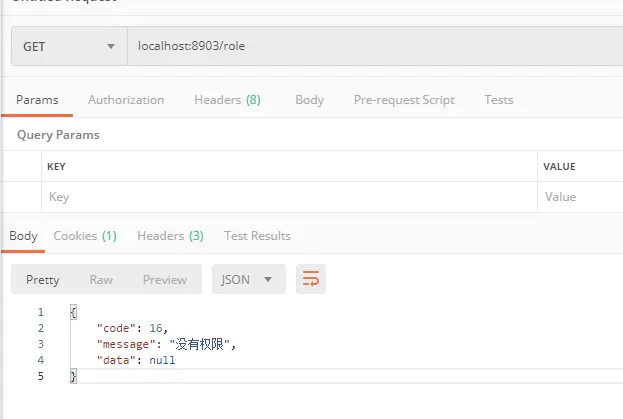
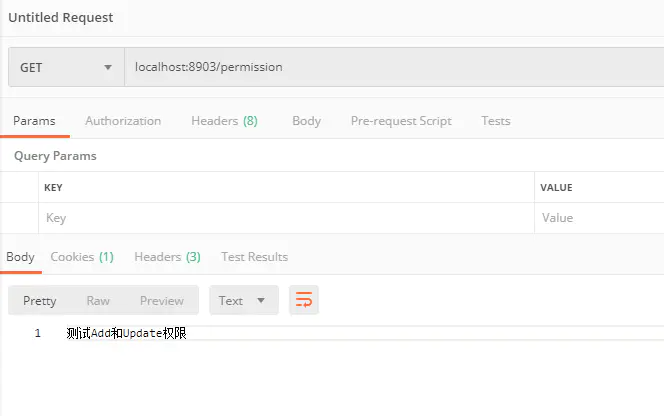
6.1.4 测试用户操作权限
7. 总结
本文演示了 Spring Boot 极简集成 Shiro 框架,实现了基础的身份认证和授权功能
后续可扩展的功能点有:
1. 集成 Redis 实现 Shiro 的分布式会话
2. 集成 JWT 实现单点登录功能


 浙公网安备 33010602011771号
浙公网安备 33010602011771号