集群身份认证与用户鉴权,集群内部安全通信,集群与外部间的安全通信
一台主机,ip:192.168.80.10,运行一个es,一个kibana
实现的效果
- es集群内部开启证书验证才能加入集群
- kibana与es集群通信使用https方式
- 访问es集群节点使用https方式
- 使用浏览器访问kibana使用https方式
后期考虑把logstash也加入进来,官方地址如下:
https://www.elastic.co/guide/en/logstash/current/monitoring-logstash.html
https://www.elastic.co/guide/en/logstash/current/logstash-centralized-pipeline-management.html
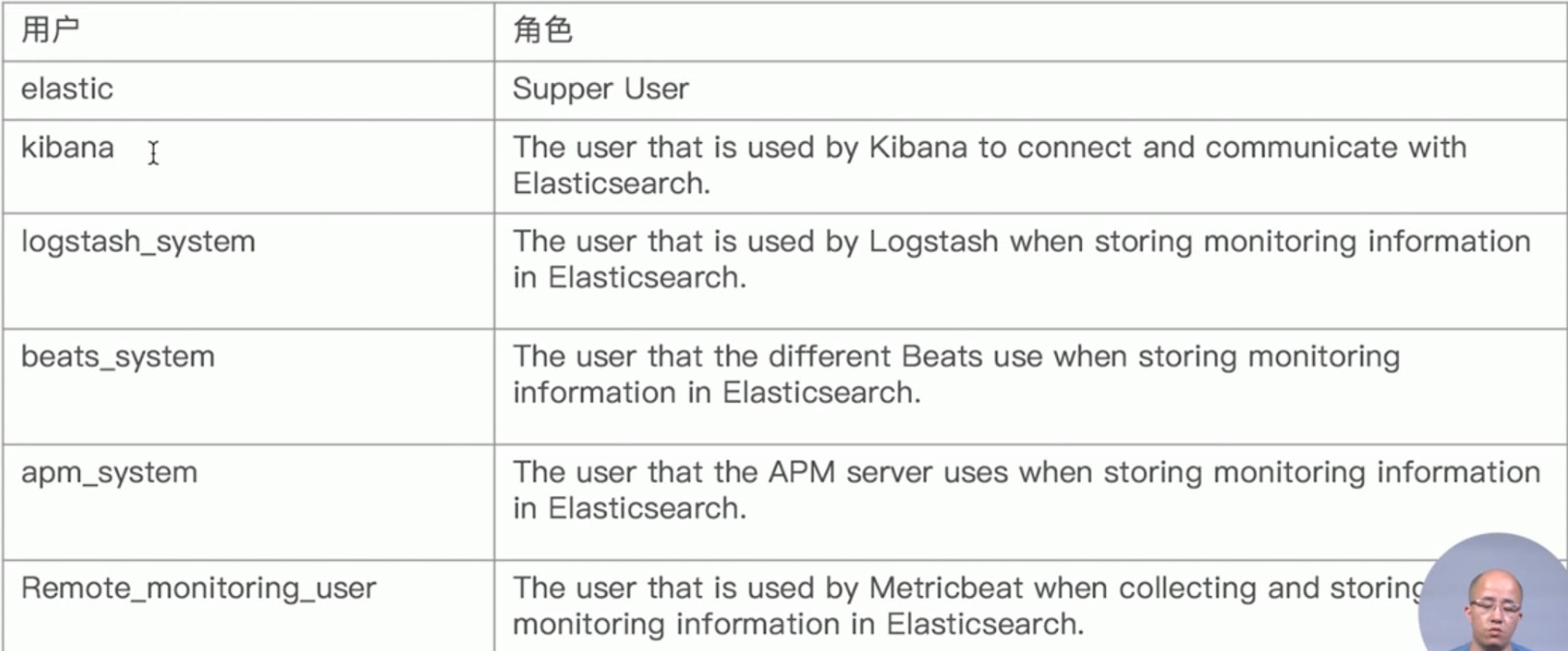
默认用户,角色
- ES操作
# 先在配置文件中开启这两个
xpack.security.enabled: true
# xpack.security.transport.ssl.enabled: true # 这个先不开启的
# 然后重启es集群
# 设置默认的角色密码
bin/elasticsearch-setup-passwords interactive
# 创建keystore文件
# bin/elasticsearch-keystore create # config文件夹下有的话这一步就不用再执行了
# 生成CA证书,一直回车
bin/elasticsearch-certutil ca (CA证书:elastic-stack-ca.p12)
# 生成节点使用的证书,一直回车
bin/elasticsearch-certutil cert --ca elastic-stack-ca.p12 (节点证书:elastic-certificates.p12)
# 创建证书保存目录,并移动到config文件下
mkdir -p config/certs
mv elastic-certificates.p12 config/certs
# 集群身份认证与用户鉴权
xpack.security.enabled: true # 若设置过则不用再设置了
# 集群内部安全通信
xpack.security.transport.ssl.enabled: true # 若设置过则不用再设置了
xpack.security.transport.ssl.verification_mode: certificate # 证书验证级别
xpack.security.transport.ssl.keystore.path: certs/elastic-certificates.p12 # 节点证书路径
xpack.security.transport.ssl.truststore.path: certs/elastic-certificates.p12
# 集群与外部间的安全通信
xpack.security.http.ssl.enabled: true
xpack.security.http.ssl.keystore.path: certs/elastic-certificates.p12
xpack.security.http.ssl.truststore.path: certs/elastic-certificates.p12
# 重启es集群
# 注意查看日志,留意节点访问证书权限
- kibana操作
# es上操作
# 从es节点拷贝节点证书到kibana根目录下
cp /usr/local/elasticsearch-7.5.0/config/certs/elastic-certificates.p12 /usr/local/kibana-7.5.0-linux-x86_64/
# kibana上操作
# 生成连接es的https的证书
# elastic-certificates.p12为上一步节点证书(注意这个证书权限),elastic-ca.pem为生成的供kibana使用的证书
openssl pkcs12 -in elastic-certificates.p12 -cacerts -nokeys -out elastic-ca.pem
# 创建证书保存目录,并移动到config文件下
mkdir -p config/certs
mv elastic-certificates.p12 elastic-ca.pem config/certs
# kibana配置连接ES的https
elasticsearch.hosts: ["https://192.168.80.10:9200"]
elasticsearch.ssl.certificateAuthorities: ["/usr/local/kibana-7.5.0-linux-x86_64/config/certs/elastic-ca.pem"]
elasticsearch.ssl.verificationMode: certificate # 证书验证级别
# kibana配置连接ES,使用用户名和密码
elasticsearch.username: "kibana"
elasticsearch.password: "changeme"
# 使用https方式访问kibana
# es上操作
bin/elasticsearch-certutil ca --pem (elastic-stack-ca.zip)
unzip elastic-stack-ca.zip
# 得到ca.crt和ca.key
creating: ca/
inflating: ca/ca.crt
inflating: ca/ca.key
# 从es节点拷贝上一步生成的证书到kibana证书目录下
cp /usr/local/elasticsearch-7.5.0/ca/* /usr/local/kibana-7.5.0-linux-x86_64/config/certs/
# 非必须:修改证书权限
# kibana上操作
# 开启,并设置证书(注意证书路径写法)
server.ssl.enabled: true
server.ssl.certificate: config/certs/ca.crt
server.ssl.key: config/certs/ca.key
es配置文件
cluster.name: my-application
node.name: node0
path.data: node0_data
network.host: 192.168.80.10
http.port: 9200
discovery.seed_hosts: ["192.168.80.10"]
cluster.initial_master_nodes: ["192.168.80.10"]
xpack.security.enabled: true
xpack.security.http.ssl.enabled: true
xpack.security.http.ssl.keystore.path: certs/elastic-certificates.p12
xpack.security.http.ssl.truststore.path: certs/elastic-certificates.p12
xpack.security.transport.ssl.enabled: true
xpack.security.transport.ssl.verification_mode: certificate
xpack.security.transport.ssl.keystore.path: certs/elastic-certificates.p12
xpack.security.transport.ssl.truststore.path: certs/elastic-certificates.p12
kibana配置文件
server.port: 5601
server.host: "192.168.80.10"
elasticsearch.hosts: ["https://192.168.80.10:9200"]
elasticsearch.username: "kibana"
elasticsearch.password: "changeme"
server.ssl.enabled: true
server.ssl.certificate: config/certs/ca.crt
server.ssl.key: config/certs/ca.key
elasticsearch.ssl.certificateAuthorities: ["/usr/local/kibana-7.5.0-linux-x86_64/config/certs/elastic-ca.pem"]
elasticsearch.ssl.verificationMode: certificate




