Lab 3-2
Analyze the malware found in the file Lab03-02.dll using basic dynamic analysis tools.
Questions and Short Answers
-
How can you get this malware to install itself?
A: To install the malware as a service, run the malware’s exported installA function via rundll32.exe with rundll32.exe Lab03-02.dll,installA.
-
How would you get this malware to run after installation?
A: To run the malware, start the service it installs using the net command net start IPRIP.
-
How can you find the process under which this malware is running?
A: Use Process Explorer to determine which process is running the service. Since the malware will be running within one of the svchost.exe files on the system, hover over each one until you see the service name, or search for Lab03-02.dll using the Find DLL feature of Process Explorer.
-
Which filters could you set in order to use procmon to glean information?
A: In procmon you can filter on the PID you found using Process Explorer.

-
What are the malware’s host-based indicators?
A: By default, the malware installs as the service IPRIP with a display name of Intranet Network Awareness (INA+) and description of “Depends INA+, Collects and stores network configuration and location information, and notifies applications when this information changes.” It installs itself for persistence in the registry at HKLM\SYSTEM\CurrentControlSet\Services\IPRIP\ Parameters\ServiceDll: %CurrentDirectory%\Lab03-02.dll. If you rename Lab03-02.dll to something else, such as malware.dll, then it writes malware.dll into the registry key, instead of using the name Lab03-02.dll.
-
Are there any useful network-based signatures for this malware?
A: The malware resolves the domain name practicalmalwareanalysis.com and connects to that host over port 80 using what appears to be HTTP. It does a GET request for serve.html and uses the User-Agent %ComputerName% Windows XP 6.11.
Detailed Analysis
We begin with basic static analysis by looking at the PE file structure and strings. Figure 3-5L shows that this DLL has five exports, as listed from \({\color{red}1}\) and below. The export ServiceMain suggests that this malware needs to be installed as a service in order to run properly.

The following listing shows the malware’s interesting imported functions in bold.

These include service-manipulation functions, such as CreateService, and registry-manipulation functions, such as RegSetValueEx. Imported networking functions, such as HttpSendRequest, suggest that the malware uses HTTP.
Next, we examine the strings, as shown in the following listing.
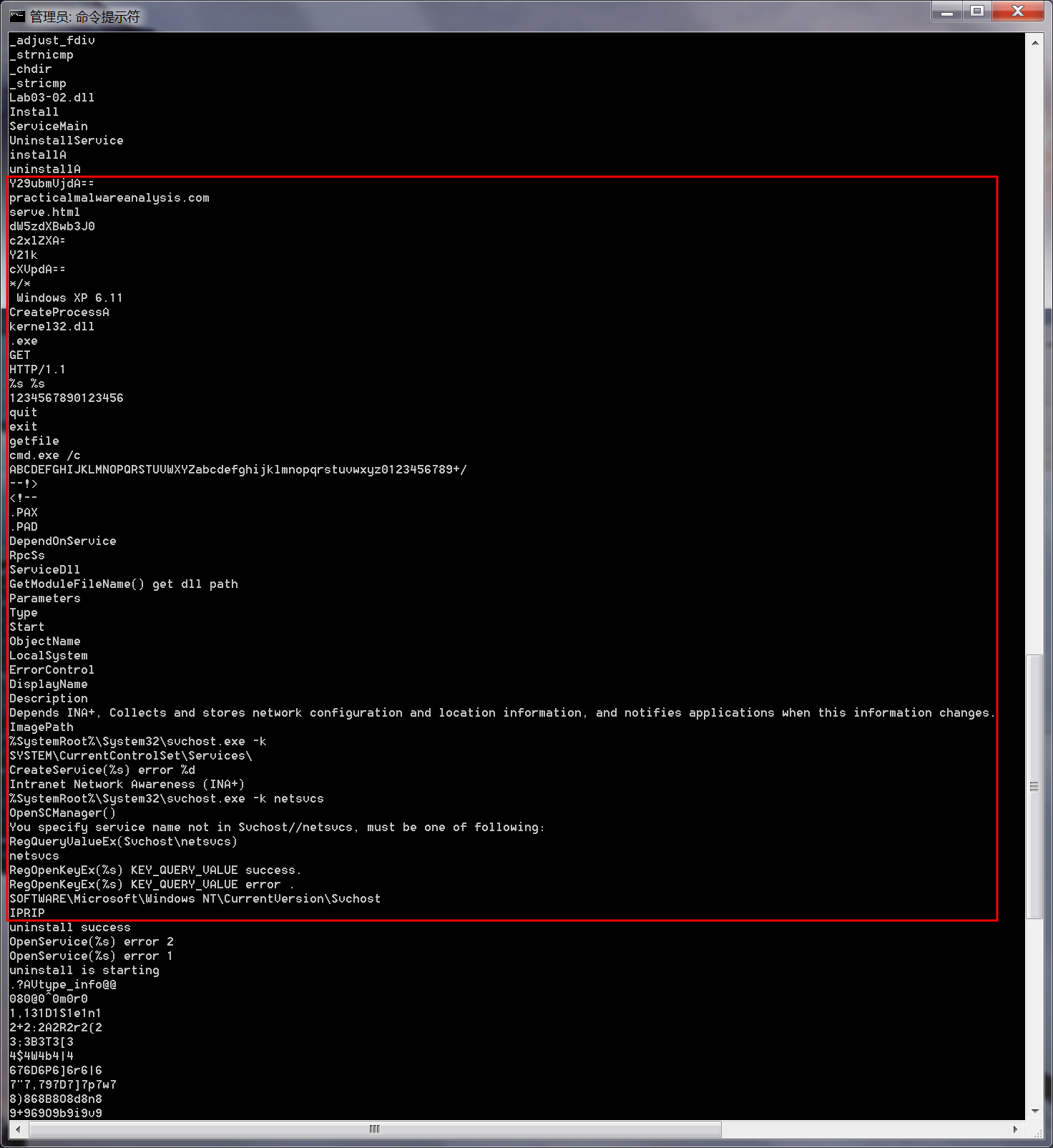
We see several interesting strings, including registry locations, a domain name, unique strings like IPRIP and serve.html, and a variety of encoded strings. Basic dynamic techniques may show us how these strings and imports are used.
The results of our basic static analysis techniques lead us to believe that this malware needs to be installed as a service using the exported function installA. We’ll use that function to attempt to install this malware, but before we do that, we’ll launch Regshot to take a baseline snapshot of the registry and use Process Explorer to monitor the processes running on the system. After setting up Regshot and Process Explorer, we install the malware using rundll32.exe, as follows:
C:\>rundll32.exe Lab03-02.dll,installA

注:win7中无法复现,使用Windows XP可成功复现。
After installing the malware, we use Process Explorer to confirm that it has terminated by making sure that rundll32.exe is no longer in the process listing. Next, we take a second snapshot with Regshot to see if the malware installed itself in the registry.
The edited Regshot results are shown in the following listing.
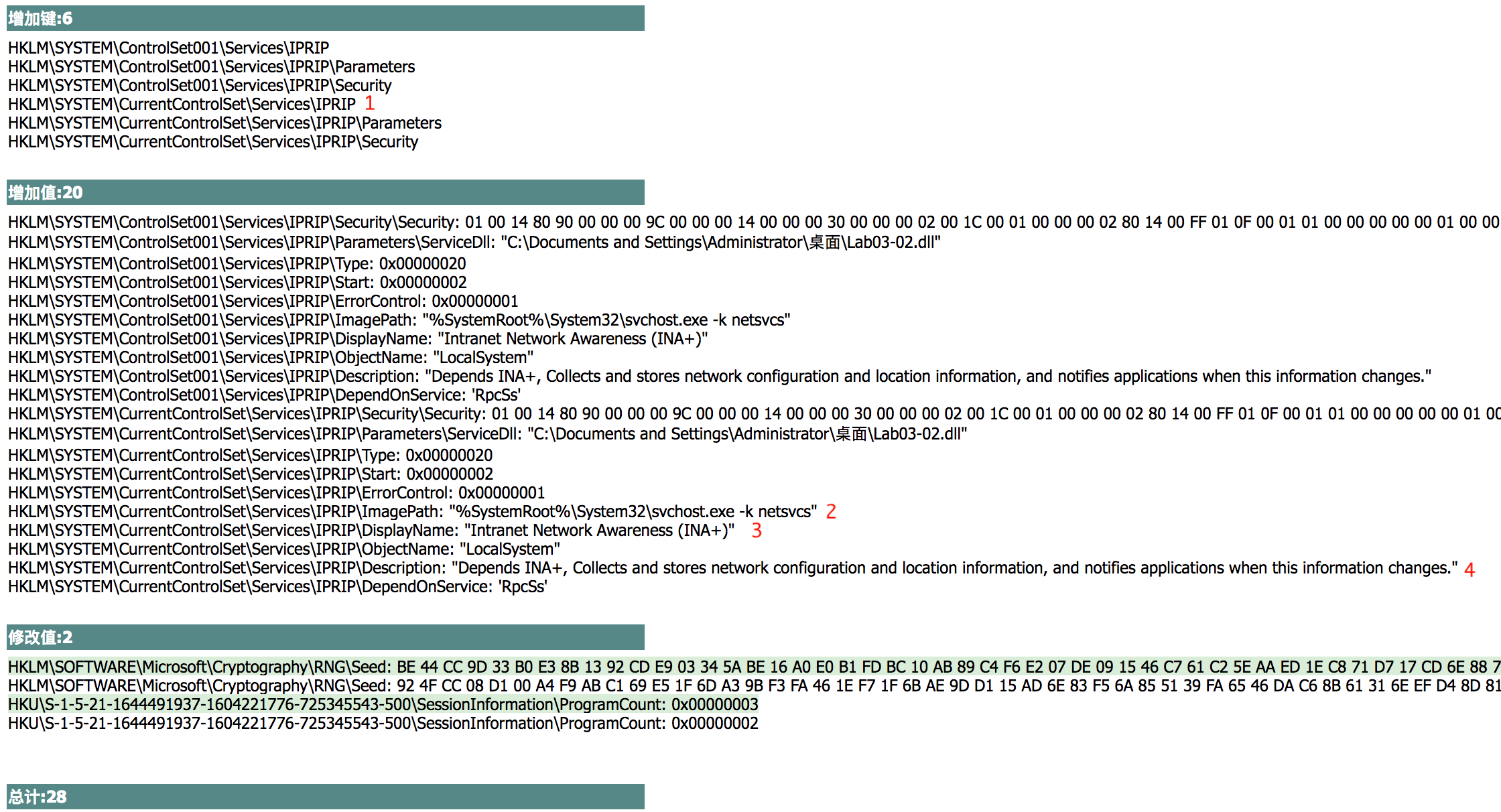

The Keys added section shows that the malware installed itself as the service IPRIP at \({\color{red}1}\). Since the malware is a DLL, it depends on an executable to launch it. In fact, we see at \({\color{red}2}\) that the ImagePath is set to svchost.exe, which means that the malware will be launched inside an svchost.exe process. The rest of the information, such as the DisplayName and Description at \({\color{red}3}\) and \({\color{red}4}\), creates a unique fingerprint that can be used to identify the malicious service.
If we examine the strings closely, we see SOFTWARE\Microsoft\Windows NT\ CurrentVersion\SvcHost and a message "You specify service name not in Svchost// netsvcs, must be one of following". If we follow our hunch and examine the \SvcHost\netsvcs registry key, we can see other potential service names we might use, like 6to4 AppMgmt. Running Lab03-02.dll,installA 6to4 will install this malware under the 6to4 service instead of the IPRIP service, as in the previous listing.
After installing the malware as a service, we could launch it, but first we’ll set up the rest of our basic dynamic tools. We run procmon (after clearing out all events); start Process Explorer; and set up a virtual network, including ApateDNS and Netcat listening on port 80 (since we see HTTP in the strings listing).
Since this malware is installed as the IPRIP service, we can start it using the net command in Windows, as follows:
C:\>net start IPRIP
The Intranet Network Awareness (INA+) service is starting.
The Intranet Network Awareness (INA+) service was started successfully.
The fact that the display name (INA+) matches the information found in the registry tells us that our malicious service has started.
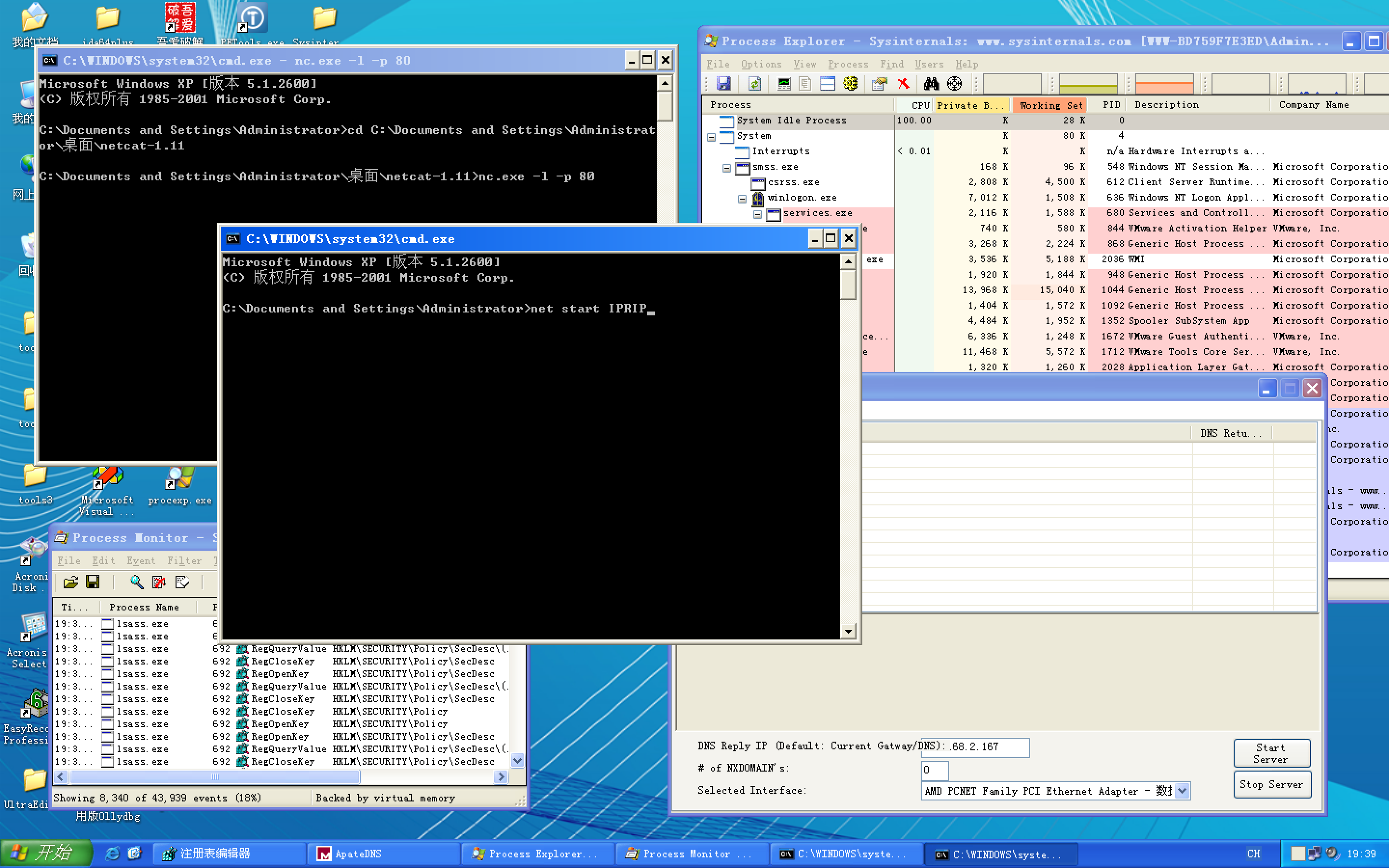
注:上图按 Enter 键前,记得ApateDNS软件点击Start Server。

Next, we open Process Explorer and attempt to find the process in which the malware is running by selecting Find -> Find Handle or DLL to open the dialog shown in Figure 3-6L. We enter Lab03-02.dll and click Search. As shown in the figure, the result tells us that Lab03-02.dll is loaded by svchost.exe with the PID 1044. (The specific PID may differ on your system.)
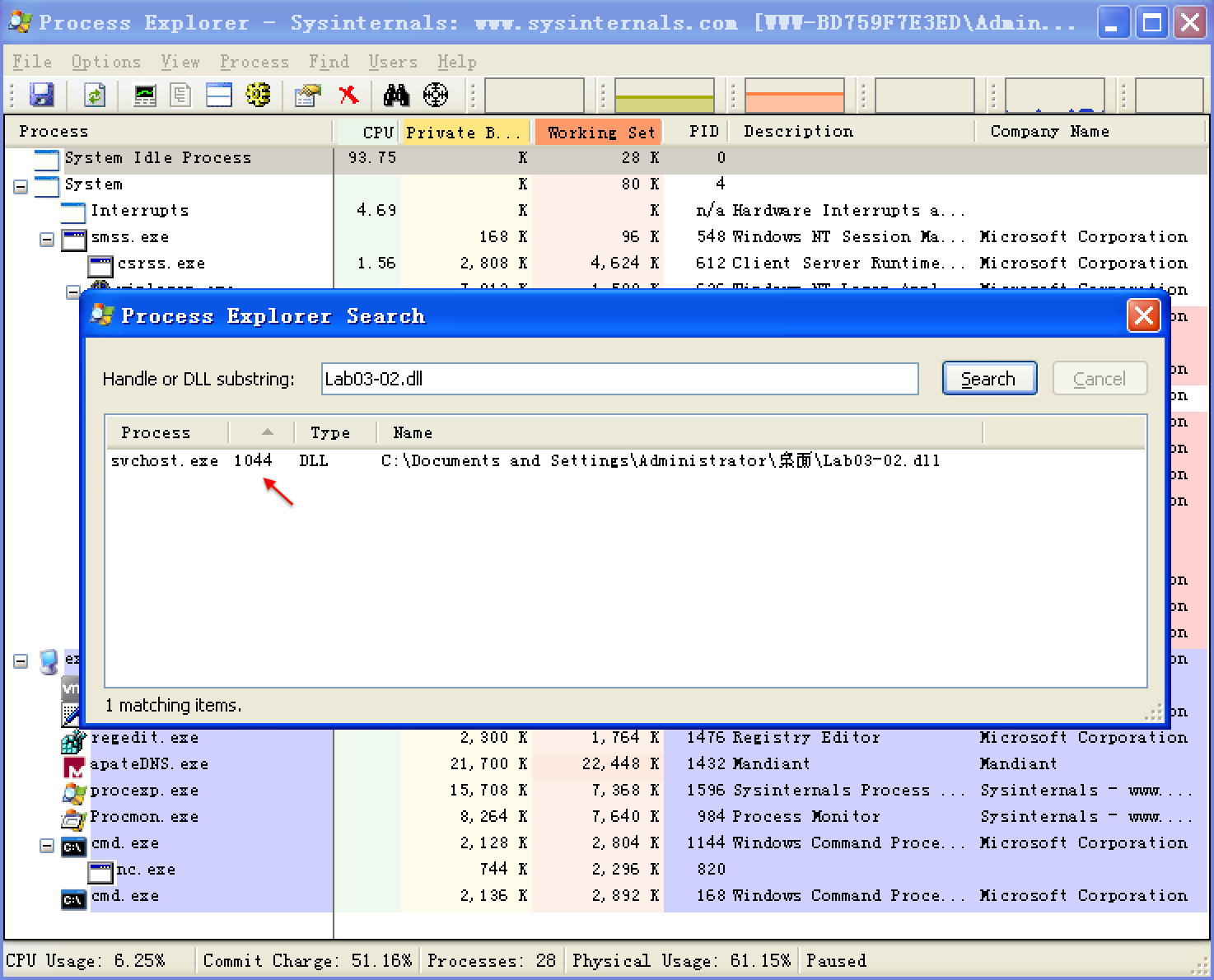
In Process Explorer, we select View -> Lower Pane View -> DLLs and choose the svchost.exe running with PID 1044. Figure 3-7L shows the result. The display name Intranet Network Awareness (INA+) shown at \({\color{red}1}\) confirms that the malware is running in svchost.exe, which is further confirmed when we see at \({\color{red}2}\) that Lab03-02.dll is loaded.

Next, we turn our attention to our network analysis tools. First, we check ApateDNS to see if the malware performed any DNS requests. The output shows a request for practicalmalwareanalysis.com, which matches the strings listing shown earlier.
NOTE
It takes 60 seconds after starting the service to see any network traffic (the program does a Sleep(60000) before attempting network access). If the networking connection fails for any reason (for example, you forgot to set up ApateDNS), it waits 10 minutes before attempting to connect again.
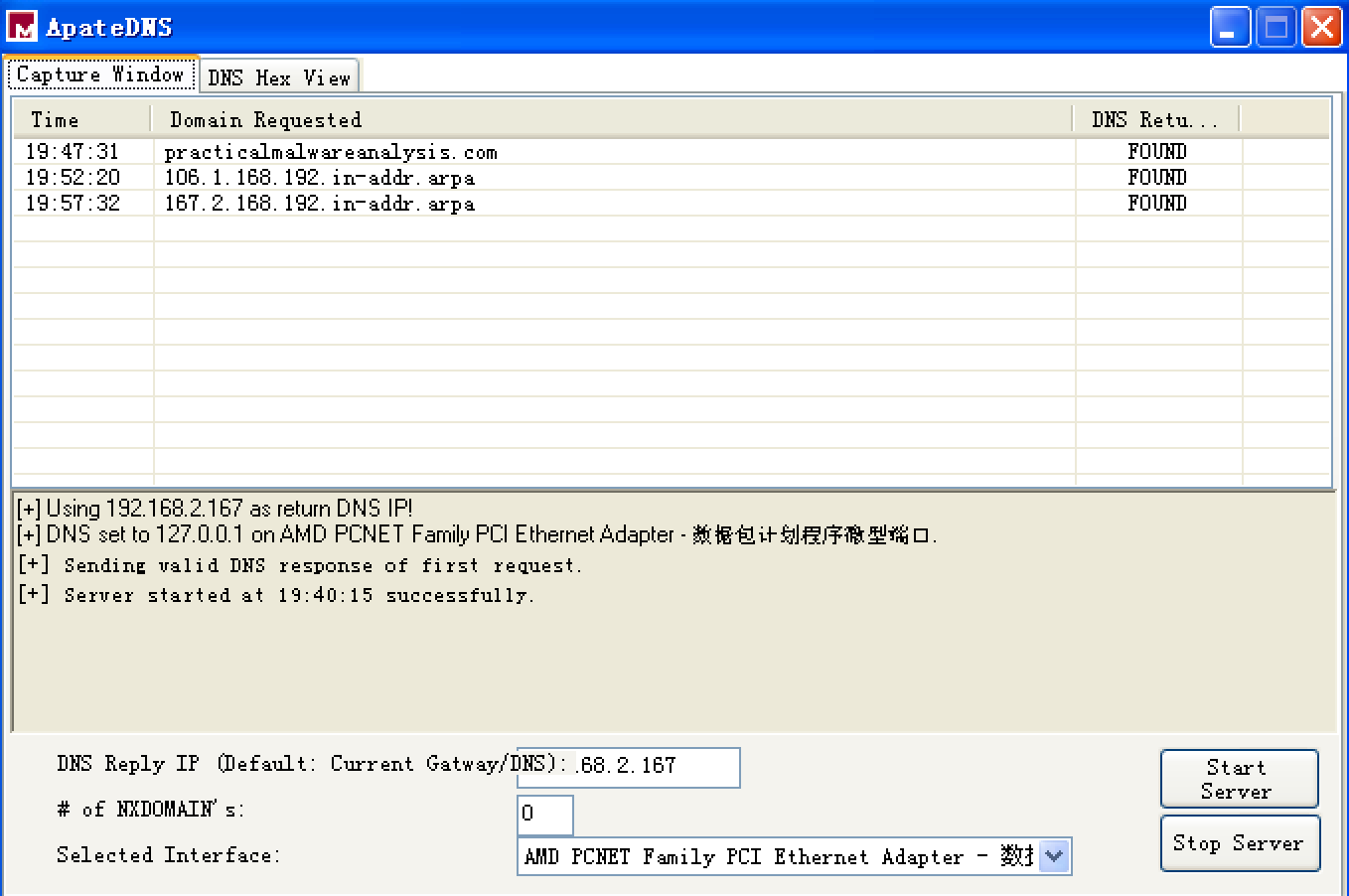
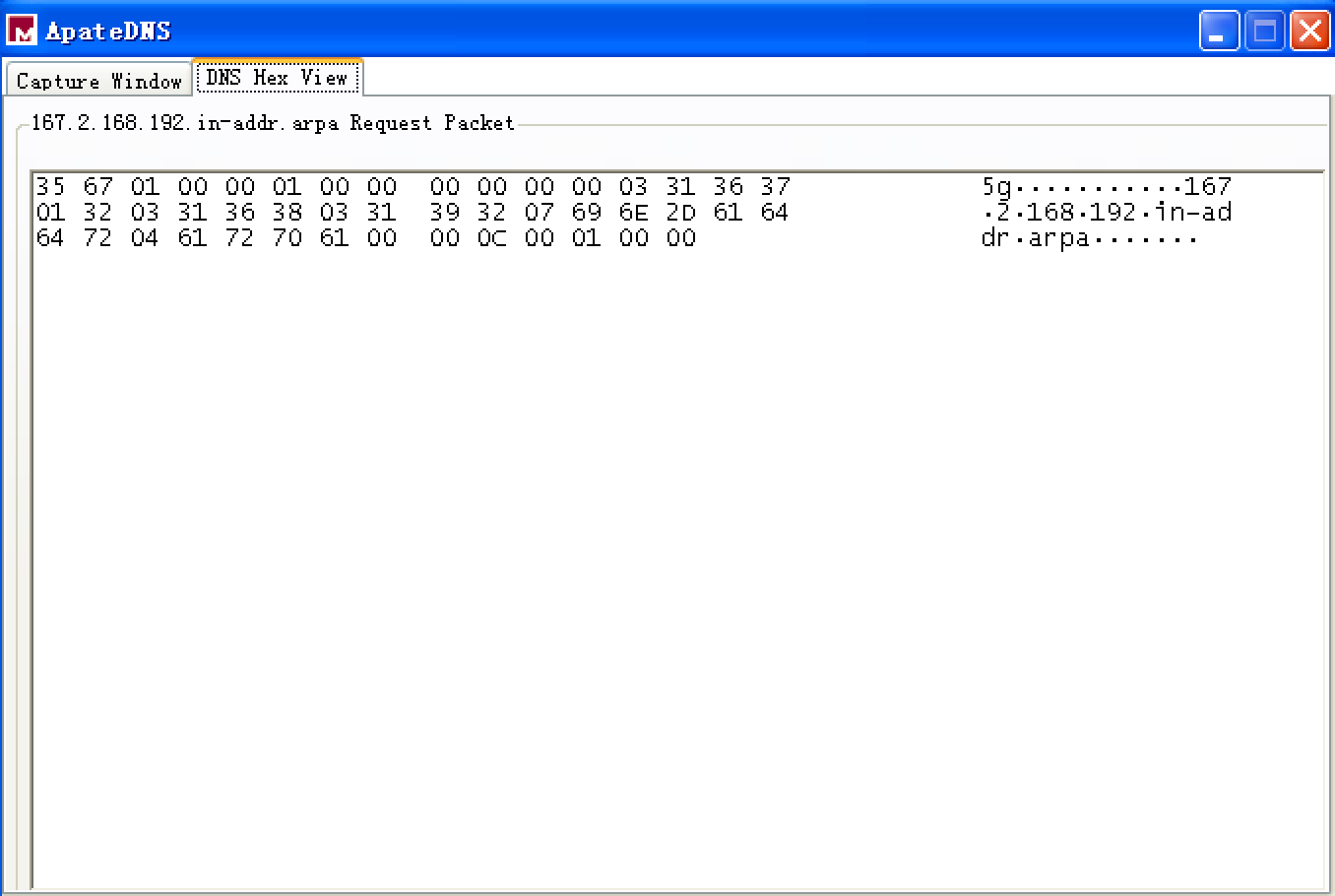
双击 ApateDNS 的 Capture Window 窗口的 Domain Requested 相应条目,显示 DNS Hex View,如下:
最后 ApateDNS 点击 Stop Server,在服务器端,快捷键 control + c 结束服务器,查看生成的日志文件 report.3385.txt 如下:

We complete our network analysis by examining the Netcat results, as follows:

书中的结果是如下:

We see that the malware performs an HTTP GET request over port 80 (we were listening over port 80 with Netcat since we saw HTTP in the string listing). We run this test several times, and the data appears to be consistent across runs.
We can create a couple of network signatures from this data. Because the malware consistently does a GET request for serve.html, we can use that GET request as a network signature. The malware also uses the User-Agent MalwareAnalysis2 Windows XP 6.11. MalwareAnalysis2 is our malware analysis virtual machine’s name (so this portion of the User-Agent will be different on your machine). The second part of the User-Agent (Windows XP 6.11) is consistent and can be used as a network signature.


 浙公网安备 33010602011771号
浙公网安备 33010602011771号